Efficient Online Course Management Guide
Streamline your online course setup with steps on adding due dates, editing syllabus, and ensuring student engagement. Also includes browser settings for optimal performance. Learn how to add due dates for assignments, discussions, and quizzes, and customize your syllabus to include essential inform
0 views • 14 slides
Understanding Secure Act 2.0 Key Provisions
In a detailed report by Dee Spivey and Angie Zouhar, key provisions of SECURE Act 2.0 are outlined, including changes in retirement plans like RMD age increase, employee certification of hardship withdrawals, and more. Secure 1.0 and Secure 2.0 differences, effective dates, and necessary actions for
5 views • 12 slides
QuickBooks Online Running Slow
If QuickBooks Online is running slowly, there are several actions you can take to improve its performance. First, make sure your internet connection is stable. Then, clear your browser's cache and cookies to remove unnecessary data. Another option is to close unused tabs and programs to free up reso
1 views • 3 slides
Introduction to SFTP & PGP Encryption for Secure Data Transfer
Discover how to ensure reliable data transfer, make informed decisions, and gain a strategic advantage through the use of Secure File Transfer Protocol (SFTP) and Pretty Good Privacy (PGP) encryption. The session includes demonstrations on PGP encryption and SFTP access, along with insights on setti
1 views • 22 slides
Ensuring Secure Testing Environments in Oregon Education System
Oregon's Statewide Assessment System (OSAS) emphasizes the critical need for secure testing environments to maintain the validity and accuracy of assessment data. This includes handling secure printed test materials, identifying and preventing improprieties, and reporting any irregularities. From ma
2 views • 20 slides
User Manual for Certificate Courses Login and System Requirements
Access the online platform for certificate courses provided by ICSI with login instructions including password setup and system requirements for optimal user experience. Ensure proper internet connectivity, browser compatibility, screen resolution, and browser maintenance for seamless learning. Than
1 views • 6 slides
Troubleshooting Invalid Login Credential Issue on e-Way Bill Portal
Some users are encountering an "Invalid Login Credentials" error while trying to access the Maharashtra GST Department's e-Way Bill Helpdesk portal at ewaybillgst.gov.in. To resolve this issue, it is recommended to clear browser cache and cookies. Additionally, ensure you are using a recommended bro
0 views • 13 slides
Exploring Blazor: An Experimental .NET Framework for the Browser
Blazor is an experimental .NET framework that enables C# and Razor developers to build web applications that run directly in the browser. Utilizing WebAssembly for client-side execution, Blazor provides a unique approach to web development, allowing for seamless integration of C# code with the brows
0 views • 39 slides
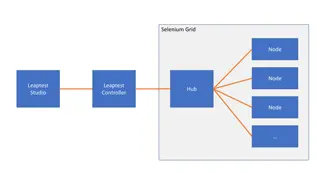
Comprehensive Overview of Selenium Grid, Leaptest Studio, and Browser Automation
This content provides images and descriptions of various components in the Selenium Grid, Leaptest Studio, and browser automation setup. It covers nodes, hubs, controllers, environments, and test cases in the context of Selenium and Leaptest tools. The images showcase different configurations and se
1 views • 8 slides
Understanding Geolocation: What You Need to Know
Geolocation is a built-in browser functionality that allows web applications to be location-aware. It uses geographic latitude/longitude and is supported by all modern browsers, making it an integral part of the HTML5/W3C JavaScript API. With geolocation, you can show users their position on a map,
0 views • 16 slides
Enhancing Online Exams Security with AI Proctoring Solutions
Revolutionize your online examination process with AI-powered proctoring solutions ensuring secure and efficient monitoring of exams. Benefit from features like live monitoring, suspect video detection, and AI-generated reports, leading to wider reach, cost savings, and enhanced security. Simple ste
0 views • 17 slides
Tamper-Evident Pairing (TEP) Protocol for Secure Wireless Pairing Without Passwords
This article discusses the challenges of traditional secure wireless pairing methods that rely on password validation and proposes the Tamper-Evident Pairing (TEP) protocol as a secure in-band solution to protect against Man-in-the-Middle (MITM) attacks. TEP eliminates the need for out-of-band chann
1 views • 40 slides
Browser Extensions as Assistive Technology: Enhancing Accessibility
Explore the potential of browser extensions as assistive technology in a presentation from the 37th Annual CSUN Assistive Technology Conference. Learn how Chrome extensions can support students with disabilities, providing safe downloads, alternative AT options, and unique functions, all while enhan
0 views • 32 slides
Techniques and Tools for Secure Web Browser Extension Development
Explore the world of web browser extensions with Rezwana Karim's research at Rutgers University, focusing on secure development techniques, extensible platforms, and the implications of vulnerable extensions on platform security. Discover the popularity and impact of browser extensions in today's di
1 views • 66 slides
Analysis of file:// Vulnerabilities in Android Browser Apps
The study delves into file:// vulnerabilities in Android browser apps, uncovering risks posed by the file:// URI scheme. It highlights how file:// requests can breach app data isolation, potentially compromising sensitive files. The research presents a unified attack model, FileCross automated testi
0 views • 22 slides
Exploring Secure Cooperative Sharing of Resources in Web Applications
This series of visual representations delves into the concept of secure cooperative sharing of JavaScript, browser capabilities, and physical resources in web applications. The images and descriptions cover topics such as web application security, browser functionality, and the principles of sharing
0 views • 22 slides
Automating Your Browser and Desktop Apps Using Python
Explore the world of automation with Python programming language through Al Sweigart's book "Automate the Boring Stuff". Learn web scraping techniques and use Selenium to automate tasks on your browser and desktop applications effortlessly.
0 views • 30 slides
Enhancing Browser Security for Mobile Devices Using Smart CDNs
Explore the realm of improving browser security for mobile devices through the utilization of Smart Content Delivery Networks (CDNs). Delve into research directions, challenges in adoption, and innovative security services to safeguard against potential threats. Discover how the rise of Smart CDNs i
0 views • 14 slides
Efficient ACME Workflow Automation for Browser-based Team Collaboration
Visualize the streamlined ACME workflow process led by Sterling Baldwin and smoothly executed by the dedicated team. Each step, from running models to analyzing output data, flows seamlessly, enhancing collaboration and efficiency in a browser environment.
0 views • 16 slides
Setting Up Browser for Approving Purchase Requests in E-Procurement Project
Explore step-by-step instructions for setting up your browser - Internet Explorer for PC users and Safari for Mac users - to efficiently approve purchase requests in the E-Procurement Project at SU. Ensure smooth access to WebNow and avoid potential issues with Java updates.
0 views • 15 slides
Step-by-Step Guide to Using secure.colostate.edu NetConnect
Accessing secure.colostate.edu NetConnect is crucial for connecting securely to Colostate's network. Follow these steps: Use your web browser to login, allow Juniper Network installation, access Secure.Colostate.edu, connect behind the firewall, and utilize Pangea for file access. Obtain the Pangea
0 views • 8 slides
The Rise of Chrome: A Technical Comparison with Competing Browsers
Since 2009, Google Chrome has become the dominant desktop browser, outpacing competitors like Internet Explorer and Firefox. This study delves into the technical aspects that have contributed to Chrome's rise, including performance benchmarks, features, and adherence to industry standards. The metho
0 views • 40 slides
Browser News and Root Inclusion Process Updates
The Browser news reveals new policies and strategies to enhance user experience, including the clarification of inclusion processes and removal of certain roots. Additionally, updates on the Root inclusion process for CAs are mentioned, with scheduled quarterly updates starting in October 2018. Sugg
0 views • 6 slides
Guide to Clearing Browser Cache for Better Online Experience
Learn how to clear cache on Internet Explorer, Firefox, and Chrome to avoid distorted data and inaccurate information during a weekend release. Follow simple steps provided for each browser to ensure smooth browsing experience on BT Wholesale Online. Access the user guide via My BT Wholesale.
0 views • 8 slides
Investigating the Privacy Risks of Private Browsing
Private browsing, a feature available in major browsers, is used by approximately 450 million users. However, this study reveals potential security vulnerabilities, such as leftover artifacts in memory and issues with SQLite databases, that may compromise users' sensitive information even after clos
0 views • 19 slides
Understanding How Browser Engines Work
Browser engines play a crucial role in how web browsers retrieve, present, and traverse information resources on the World Wide Web. This process involves fetching a page, interpreting URLs, rendering content with layout engines, and utilizing components like the host application. Popular layout eng
0 views • 10 slides
University of Waterloo Browser Support Guidelines
The University of Waterloo has introduced a graded browser support system, emphasizing that support does not mean identical experiences for all users. The purpose is to ensure accessibility and prioritize content consumption based on browser capabilities. The guidelines introduce grades of support a
0 views • 21 slides
CSS Rule Sets and Cross-Browser Compatibility in ASP.NET Applications
Learn how to code CSS rule sets and ensure cross-browser compatibility in ASP.NET applications. Explore Visual Studio features for working with HTML and CSS, along with guidelines for testing web pages on different browsers and utilizing HTML5 features effectively.
0 views • 20 slides
Introduction to BED Files: An Overview of Browser Extensible Data Format
BED (Browser Extensible Data) files are commonly used for annotating genomic sequences by specifying ranges on chromosomes. They consist of required fields like chromosome name, start and end positions, and optional fields for additional information such as name, score, strand, and color representat
0 views • 11 slides
Advanced Programming of Web Applications with Browser APIs
Explore advanced programming techniques for web applications using Browser APIs like navigation, history, web pages visibility, multiple windows/tabs, mouse and pointer interaction, and text selection. Learn how to leverage these APIs to create dynamic and interactive web experiences.
0 views • 22 slides
Understanding JavaScript Core API and Browser Object Model (BOM)
Explore the fundamentals of JavaScript Core API and the Browser Object Model (BOM) in this informative content. Learn about native objects, host environment elements, global objects like window, BOM hierarchy, object extension in JavaScript, and essential window methods and attributes for interactiv
0 views • 27 slides
Enhancing JavaScript Security with ConScript Approach
Explore how ConScript enables specifying and enforcing fine-grained security policies for JavaScript in the browser. Learn about the approach to protect benign users by giving control to the hosting site, the contributions of ConScript, and its impact on browser security and policy correctness.
0 views • 41 slides
Insight into Browser Instrumentation for Exploit Analysis
Explore the complex world of browser instrumentation and exploit analysis through the lens of Mihai Neagu's research at Bitdefender. Delve into the intricacies of exploit kits, malware delivery services, behavior analysis, and hidden aspects of exploit execution processes.
0 views • 19 slides
Exploring the Use of Browser Extensions for Assistive Technology
The presentation discusses the use of browser extensions as alternative assistive technology for students with disabilities who may prefer not to use traditional AT tools. It covers topics such as the benefits of Chrome extensions, safety tips for downloading and using them, and a curated list of re
0 views • 32 slides
Clearing Browser Cache and Cookies: Google Chrome Edition
In this guide, you will learn how to clear the browser cache and cookies in Google Chrome. Follow the easy steps to ensure smooth browsing experience. From accessing your browser settings to selecting the right options, this tutorial covers it all. Keep your browser running efficiently by regularly
0 views • 6 slides
Mastering Internet Research for Managers: Browser Tools and Search Techniques
Enhance your managerial skills by delving into Internet research techniques, focusing on web browser basics, search strategies, and browser tools. Learn about popular browsers like Google Chrome, Mozilla Firefox, Apple Safari, and Microsoft Edge, along with tips for efficient web searching using Chr
0 views • 13 slides
Evolution of Mozilla: From Browser Wars to Open-Source Development
The evolution of Mozilla from the Browser Wars era to becoming a pioneer in open-source community development is highlighted. Starting with Mosaic and Netscape Navigator, Mozilla transformed into the popular Firefox browser and expanded into various projects under the Mozilla Foundation and Corporat
0 views • 22 slides
Enhancing Online Exam Integrity with Respondus Monitor and Lockdown Browser
Discover how Respondus Monitor and Lockdown Browser provide enhanced security features for online exams, including webcam and microphone monitoring, controls blocking, and post-exam recording review. Best practices and resources for implementing these tools effectively in Moodle are also highlighted
0 views • 8 slides
Comprehensive Guide to Identifying Carbapenem-Resistant Isolates Without Common Acquired Carbapenem Resistance Genes
Utilize the Isolates Browser on NCBI Pathogen Detection platform to search for carbapenem-resistant isolates without common acquired resistance genes. Follow steps such as using AST phenotypes and AMR genotypes, cross-browser selection, and filters to isolate relevant results. Detailed instructions
0 views • 6 slides
Secure Exam Monitoring with LockDown Browser and Respondus Monitor
Enhance exam security with the combination of LockDown Browser and Respondus Monitor. Students must download and install LockDown Browser, ensuring webcam usage for monitoring. The process involves launching the desktop app, confirming technology requirements, and accessing various resources for a s
0 views • 7 slides