TEAM SWOT ANALYSIS
This comprehensive presentation template guides individuals or small groups through conducting a SWOT analysis to identify strengths, weaknesses, opportunities, and threats for a business. It includes questions to assess strengths, weaknesses, opportunities, and threats, a discussion section to dete
1 views • 8 slides
Active Directory Self Service Password Reset Tool, cionsystems
It provides the feature of delegated web access administration, self-registration, self-service and password management. \/\/rb.gy\/1tjfv5
2 views • 2 slides
Digital Wellness and Password Security Lesson for Students
This lesson focuses on promoting digital wellness and teaching students about password security. It covers topics such as creating strong passwords, safeguarding personal information, and the importance of balancing online and offline interactions. Through activities and discussions, students learn
0 views • 13 slides
Unlocking Solutions: Addressing QuickBooks Company File Incorrect Password Issue
Unlocking Solutions: Addressing QuickBooks Company File Incorrect Password Issues\nQuickBooks, a vital tool for businesses, can encounter password-related hurdles, disrupting workflow. This guide explores causes and solutions to incorrect password issues. Forgotten passwords, user permission errors,
1 views • 5 slides
Cybersecurity Best Practices for Password Protection and Incident Response
Enhance your cybersecurity knowledge with insights on password management, cybercriminal tactics, creating strong passwords, and password complexity. Learn how to safeguard your data and prevent cyber threats by implementing strong password rules, multi-factor authentication, and incident response s
2 views • 24 slides
Understanding Device Settings and Strong Passwords for Digital Citizenship
This lesson focuses on understanding device settings and the importance of creating strong passwords for digital citizenship. It covers topics such as changing backgrounds, locking screens, creating strong passwords, common password mistakes to avoid, and tips for password safety. The lesson also in
1 views • 11 slides
Strengthen Your Digital Literacy with Strong Password Strategies
Enhance your digital literacy by learning about the importance of strong passwords, strategies for creating secure passwords, and the role of password managers. Explore various resources, videos, and tools to improve your password security and protect your online accounts effectively.
0 views • 5 slides
Promote Feature Adoption with Self-Service Password Reset Posters
Enhance feature adoption of self-service password reset among your employees with these ready-to-use posters. Simply customize and print them to encourage password security awareness in your workplace. Don't risk productivity downtime due to forgotten passwords – empower your team to reset their p
0 views • 13 slides
Evolution of Password Security in Modern Computing
Delve into the historical origins of passwords, their significance in cybersecurity, and the current methods employed to safeguard digital assets. Explore the challenges posed by fast computing systems and discover innovative solutions and tools like LastPass, Keeper, and Dashlane in the realm of pa
0 views • 15 slides
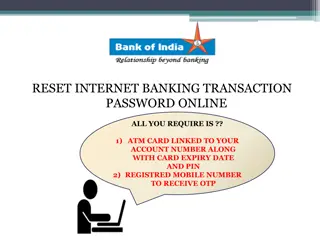
Reset Internet Banking Transaction Password Online Guide
Complete your internet banking transaction password reset online using your ATM card details and registered mobile number for OTP verification. Follow the step-by-step instructions provided with images for a successful reset process and confirmation.
0 views • 8 slides
Enhancing Security with Windows Hello for Business
Windows Hello for Business provides a more secure non-password credential for Windows 10/11 devices, implementing 2FA/MFA to combat password-related vulnerabilities. This article explores the benefits, security measures, and implementation steps of Windows Hello for Business, addressing the challeng
8 views • 24 slides
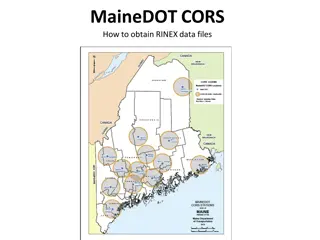
Obtaining RINEX Data Files from MaineDOT CORS
Obtain RINEX data files from MaineDOT CORS by following a few simple steps. Login and password are required, and guest login is no longer an option. The data is collected at one-second intervals and is available for Real-Time-Kinematic (RTK) users. To access the files, visit the provided link, selec
0 views • 17 slides
Understanding Scrypt: Maximally Memory-Hard Functions
Scrypt is a memory-hard function designed for password hashing and key derivation, aiming to thwart brute-force attacks by making evaluation moderately hard. It emphasizes the need for memory intensity over computation, hindering the advantages of special-purpose hardware, parallelism, and amortizat
0 views • 59 slides
Understanding Software Weaknesses and Exploits
Discover the vulnerabilities present in software such as buffer overflows and format string vulnerabilities, and how these weaknesses can be exploited to cause security issues. Learn about the technical aspects of weaknesses, stack frames, memory organization, and the potential consequences of stack
0 views • 57 slides
Recovering Console Password for Cisco ASR5000/5500 - Step-by-Step Guide
Learn how to recover the console password for Cisco ASR5000/5500 devices using a simple step-by-step process. Follow pre-requisites, problem reproduction steps, and the solution overview to regain access to your console interface.
2 views • 14 slides
Laptop Roll-Out Information and Schedule for Students at HPK
Information and guidelines for the upcoming laptop roll-out event at HPK including distributing password cards, password training, roll-out locations, times by grade, and instructions on global protection software. Students must follow the specified steps to receive their laptops successfully.
0 views • 14 slides
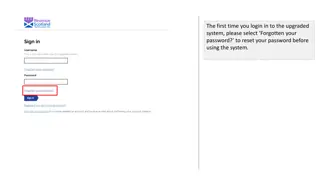
Step-by-Step Guide to Password Recovery and Account Activation
Detailed instructions on how to recover your password, activate your account, and securely log in for the first time following the system upgrade. Follow each step carefully to ensure a smooth transition into the upgraded system.
0 views • 9 slides
Safely Logging Password-Derived Measurements for Web Login Systems
Design a secure measurement framework called Gossamer to assess risks associated with password-based measurements for web login systems. Explore ways to differentiate between benign and malicious traffic, and consider adding instrumentation to enhance security. Learn how attackers exploit password-d
0 views • 12 slides
How to Login to BridgeIT & Create MAPFRE Password
Learn how to login to BridgeIT on August 6th at bridgeit.mapfre.com:4430 and create or reset your MAPFRE password. Follow the step-by-step instructions provided using your MAPFRE username. A dedicated support helpline is available for any login difficulties.
0 views • 5 slides
Guide to Logging in to SIRA UW with MAPFRE Credentials
Learn how to access SIRA UW platform using your MAPFRE credentials starting August 6th. Follow the steps for creating and resetting your password, ensuring a smooth login process. Utilize your MAPFRE username and be prepared to wait 10 minutes post password reset. Reach out to the dedicated support
0 views • 5 slides
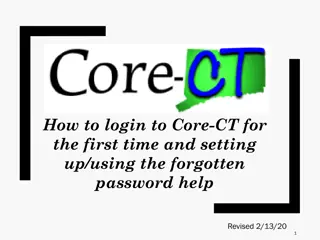
Guide to Logging in and Setting Up Core-CT for the First Time
Accessing Core-CT for the first time involves using your State of Connecticut Employee ID and temporary password. Follow the steps to log in, set up a new password, and establish a forgotten password help feature. This guide provides clear instructions and visuals for each step.
0 views • 19 slides
Step-by-Step Guide to Creating a Wikipedia Account
Follow these detailed steps to create your own Wikipedia account easily, including selecting a language, inputting a username and password, and entering your email address. Ensure a secure and unique username and password for a successful account setup.
0 views • 13 slides
Energy Management Software Comparison: Strengths and Weaknesses
This analysis compares the strengths and weaknesses of various Energy Management Software (EMS) options like EnergyCAP, Ameresco, EEMS, Lucid, Entech Gold, FacilityDude, UtilityTrac, and NUS Direct. Strengths include cost avoidance, real-time data monitoring, bill management, and more. However, weak
0 views • 8 slides
Password Cracking Techniques and Remote Desktop Access Setup
Explore various password cracking methods such as offline and online techniques using tools like Hydra, alongside setting up remote desktop access on Windows VMs to gain remote control over services. Learn about preparing Windows VMs, disabling firewalls, and enabling remote desktop assistance for e
0 views • 12 slides
Best Practices for Securing Linux Systems
This resource covers essential security practices for Linux systems, including the CIA Triad (Confidentiality, Integrity, Availability), recommended partitions, encryption at rest and in transit, SSH and user login configurations, and password best practices. Learn about securing user directories, p
0 views • 27 slides
Mastering Strong Passwords: A Practical Guide
Understanding how passwords work is crucial for online security. Passwords act like combination locks, preventing unauthorized access to your accounts. Creating a strong password involves using random words and characters, as well as combining three random words for added security. Learn how to craf
0 views • 5 slides
Interactive Password Security Activity for Children
This presentation recaps the importance of strong passwords, techniques for creating them, and the significance of two-factor authentication. The lesson notes guide discussions on creating secure passwords using the "three random words" method and avoiding personal details. The interactive game "Gue
0 views • 4 slides
Weaknesses of the Weimar Constitution and Key Questions 1919-23
The Weimar Constitution had strengths such as democratic PR but weaknesses like Article 48 leading to dictatorship vulnerability. Additional weaknesses included a right-wing bias and a Republic dominated by anti-Republican personnel. The period also saw a revolution in 1918 due to military defeat. T
0 views • 12 slides
Best Practices for Secure Password Storage - OWASP Foundation Guidelines
Learn about secure password storage techniques recommended by OWASP Foundation, including adding salt, slowing down hashing functions, using HMAC isolation, and imposing difficult verification processes on attackers. Remember to use proper encoding, avoid limiting password types or lengths unreasona
0 views • 10 slides
Techniques and Tools for Offline Password Cracking
Explore the world of offline password cracking techniques using tools like John the Ripper. Learn about the motivation behind cracking user account passwords, gaining root privilege, and compromising vulnerable systems to obtain password hashes for further exploitation. Enhance your understanding of
0 views • 15 slides
Understanding Fine-Grained Password Policies in Active Directory
Explore the intricacies of Fine-Grained Password Policies (FGPP) in Active Directory, covering topics such as domain account policies, policy recovery methods, interpreting pwdProperties attribute, and implementing PSOs for granular password settings. Delve into the nuances of password complexity, h
0 views • 11 slides
Comprehensive Guide to SWOT Analysis in Business
SWOT analysis is a strategic planning tool used to evaluate the Strengths, Weaknesses, Opportunities, and Threats of an organization or a business. It helps in identifying key issues, building on strengths, minimizing weaknesses, seizing opportunities, and counteracting threats. By focusing on turni
0 views • 18 slides
Enhancing Performance Through GCSE PE Coursework Evaluation
In the GCSE PE coursework analysis and evaluation task at Cirencester Kingshill School, students are required to assess mark allocation, identify strengths and weaknesses, devise sessions to combat weaknesses, and create evaluation plans focusing on training methods like circuit training. The emphas
0 views • 26 slides
Understanding Password Security: Techniques and Best Practices
Delve into the world of password security with this comprehensive guide, covering topics such as password gathering, cracking strategies, tools, types of passwords, hashes, salting, better hashes, and hash identification. Learn how to enhance security measures and protect against malicious attacks.
0 views • 20 slides
Protecting Password Identifiers in IEEE 802.11-21
This submission addresses the need for safeguarding password identifiers in SAE to ensure privacy and prevent attackers from constructing personally identifiable information. The document presents two potential solutions, ultimately recommending the use of symmetric cryptography for efficient protec
0 views • 11 slides
Understanding Password Guessability Metrics in Real-World Security
Delve into the realm of password guessability metrics to enhance password security. Explore how measuring guessability aids in eliminating weak passwords, aiding users in creating stronger ones, and assessing security against various cracking algorithms. Uncover the significance of statistical and p
0 views • 27 slides
Self-Service Password Reset Instructions for Staff Members
Staff members can easily reset or change their password through self-service options using Multi-Factor Authentication. They can visit the provided links, verify their identity through email and phone number, and reset their password securely. Follow the step-by-step guide for a hassle-free password
0 views • 4 slides
Guide to Logging into Your Chromebook
This step-by-step guide provides instructions on how to log into your Chromebook using either your student ID and password or a QR code. Simply open the lid, press the power button, select "Next," and then proceed to log in with your credentials. For password login, enter your student ID and the def
0 views • 6 slides
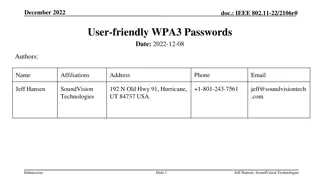
Enhancing Wi-Fi Security with User-Friendly WPA3 Passwords
Proposal to enhance Wi-Fi security by incorporating password and password identifier hashes in the SAE commit exchange, enabling devices to hint to access points which password will be used. This approach aims to improve network efficiency and user experience while addressing privacy concerns associ
0 views • 8 slides
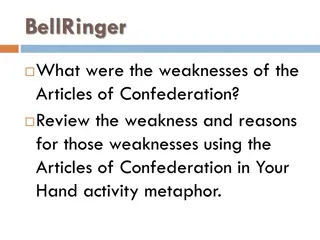
Weaknesses of the Articles of Confederation and Land Policies Explained
The weaknesses of the Articles of Confederation, including the lack of provision for adding new states, the Land Ordinance of 1785, and the Northwest Ordinance of 1787, are explored. The reasons behind these weaknesses are discussed, shedding light on the challenges faced by the early American gover
0 views • 8 slides