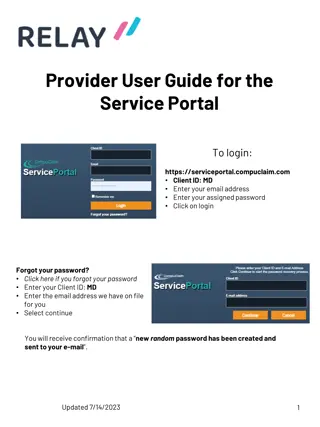
Service Portal User Guide for Providers
Learn how to login to the service portal, navigate the site, manage your caseload, and create caseload groups effectively. Access important features like the service log, supervision log, reports, and resources to streamline your service provision process. Follow step-by-step instructions and utiliz
2 views • 15 slides
Resolving QuickBooks Event ID Log Error 4
Learn how to resolve QuickBooks Event ID Log Error 4 with our comprehensive guide. This detailed resource provides step-by-step solutions to address this common issue, ensuring your QuickBooks functions smoothly. Discover how to identify the root causes of Event ID Log Error 4, from file corruption
1 views • 4 slides
How to Restore deleted Invoice in Quickbooks Online?
How to Restore deleted Invoices in Quickbooks Online?\nRestoring a deleted invoice in QuickBooks Online involves using the Audit Log to track and recreate it. First, access the Audit Log via the Gear icon under \"Tools\" and identify the deleted invoice details. Then, manually recreate the invoice b
1 views • 7 slides
Efficient Log Analysis and Data Reduction Using AWK
Learn how AWK and regex can streamline log analysis and data reduction tasks, saving you time and effort compared to manual methods like Excel. Discover how these tools excel at parsing columns of data, enabling advanced lexical analysis and efficient comparison of log files.
0 views • 15 slides
Understanding Log-structured File Systems in Operating Systems
Log-structured file systems (LFS) address performance issues by transforming updates into sequential writes to disk. This process improves efficiency by buffering updates in memory before writing them to disk. The strategy includes determining buffer size to optimize write effectiveness and utilizin
0 views • 17 slides
Mastering Color in Film: A Comprehensive Guide to Using Color Grading Techniques
Explore the intricate world of color in filmmaking through understanding color grading, log explained, Log rec.709, color correction, and grading techniques without LUTs. Enhance your storytelling by harnessing the power of color to evoke emotions and create visual impact in your films.
1 views • 6 slides
Workforce Ready (New Kronos) Log-in Instructions & Resources for Assistance
Comprehensive log-in instructions for Workforce Ready (New Kronos), including steps for web and mobile access, as well as resources for further assistance and training materials. Users can log in using their regular Doane credentials and follow the provided guidance. For additional help, resources,
0 views • 5 slides
Comprehensive RAID Log Presentation and Management Overview
This comprehensive presentation template provides a detailed overview of a RAID log, including risks, issues, threats, assumptions, dependencies, and reliance factors. It offers insights on tracking and managing different aspects of project planning and execution, categorized by risk levels. The bre
0 views • 6 slides
Understanding Tracer Studies and Disinfection in Water Treatment
Tracer studies play a crucial role in determining hydraulic efficiencies and disinfectant exposure times in water treatment processes. This presentation by Guy Schott covers the purpose of tracer studies, water age distribution, disinfection exposure time, CT disinfection, log inactivation, and more
0 views • 34 slides
Understanding VetraSpec VFW Basic Training: Key Topics and Features
Explore the essential topics covered in the VetraSpec VFW Basic Training of September 2021, including the VetraSpec ID, General Contact Log, and more. Learn about the importance of the VetraSpec ID as a unique identification number for veterans and the purpose of the General Contact Log in recording
0 views • 17 slides
Registration and Login Instructions for WBG Edcast Courses on Grow Learn Connect Platform
Learn how to register and log in to the WBG Edcast platform to access Grow Learn Connect courses. Follow step-by-step instructions from creating an account to enrolling in courses. Discover a variety of learning opportunities and start your educational journey with ease.
0 views • 7 slides
Daymap Login and App: How to Access and Navigate Efficiently
For first-time users of Daymap, it is essential to follow the steps outlined to log in successfully. Contact KP Daymap Support for assistance in setting up your account. Accessing Daymap on mobile can be done through the website or the Daymap app, with clear instructions provided for both methods. E
0 views • 5 slides
Firewood Log Store Convenient and Neat Firewood Storage
The robust Firewood Log Store is available from timeoutgardens.co.uk and is perfect for storing and organizing your firewood. An ideal companion for warm winter evenings spent together around the fireplace. Buy today!\n\n\/\/timeoutgardens.co.uk\/col
4 views • 1 slides
Event Log Alignment for Conformance Checking
Approach based on ILP for aligning event logs and process models, ensuring multi-perspective conformance checking. Examples illustrate trace executions with and without problems, utilizing Petri Nets with data. Alignments between log and process traces are analyzed, showing the existence of multiple
0 views • 21 slides
Raft Consensus Algorithm Overview for Replicated State Machines
Raft is a consensus algorithm designed for replicated state machines to ensure fault tolerance and reliable service in distributed systems. It provides leader election, log replication, safety mechanisms, and client interactions for maintaining consistency among servers. The approach simplifies oper
0 views • 32 slides
Introduction to Programming and Computer Instructions
Programming is the process of creating instructions for computers to follow and accomplish tasks. It involves turning human language instructions into detailed binary machine language. Before learning programming, individuals may have different levels of experience, ranging from no experience to pro
0 views • 16 slides
Understanding Git Commit History Options
Explore various options to view Git commit history using $git log command, such as -p to show differences, --stat for file stats, --pretty for different output formats, and --graph for branch history visualization. Customize log output using --pretty=format to display specific commit information.
0 views • 9 slides
Additive Combinatorics Approach to Log-Rank Conjecture in Communication Complexity
This research explores an additive combinatorics approach to the log-rank conjecture in communication complexity, addressing the maximum total bits sent on worst-case inputs and known bounds. It discusses the Polynomial Freiman-Ruzsa Conjecture and Approximate Duality, highlighting technical contrib
0 views • 9 slides
Raft Consensus Algorithm Overview
Raft is a consensus algorithm designed for fault-tolerant replication of logs in distributed systems. It ensures that multiple servers maintain identical states for fault tolerance in various services like file systems, databases, and key-value stores. Raft employs a leader-based approach where one
0 views • 34 slides
Advanced Techniques for Heavy Hitters Detection in Insertion Streams
Beating CountSketch algorithms, like those presented by David P. Woodruff and team, offer innovative solutions for identifying heavy hitters in insertion streams with minimal space complexity. Guarantees such as L1 and L2 outputs and the CountSketch approach are explored to achieve efficient heavy h
0 views • 18 slides
Professional Experience Portfolio (PEP) Requirements for Student Recruitment Manager
Professional Experience Portfolio (PEP) outlines the requirements for Tana Forrest, a Student Recruitment Manager, to log a minimum of 400 days of workplace experience, engage in evidenced activities, and document overall learning and development. The PEP includes a detailed work experience summary
0 views • 21 slides
Comprehensive RAID Log Presentation Template
This comprehensive presentation template includes a RAID log with risks, assumptions, issues, and dependencies structured in a professional layout. Utilize this template to effectively manage project risks and dependencies. The template also features a simple RAID log slide template for a clear over
0 views • 7 slides
Central Log Service & IT Policies Overview
Central Log Service (CLS) is a university service for storing and analyzing log information, operated by the Division of IT Network Infrastructure and Services Monitoring team. The service provides a centralized location for log storage, analysis tools, and real-time indexing capabilities. IT Loggin
1 views • 7 slides
Satchel.One Pupil Guide: Log in via the App at Knightswood Secondary School
A step-by-step guide for pupils to log in to Satchel.One (formerly Show My Homework) app at Knightswood Secondary School. Learn how to download the app, search for the school, log in via RM Unify, and enter your Glow username and password with helpful images.
0 views • 6 slides
Learning to Interpret Natural Language Navigation Instructions from Observation
This research focuses on developing a system that can interpret natural language navigation instructions by observing humans' actions in a virtual environment. The goal is to create virtual agents capable of understanding and following instructions in video games and educational software, all based
0 views • 51 slides
Ordering of Pseudo Dispatch Instructions for QBOA
This document outlines the specific order in which Pseudo Dispatch Instructions (DIs) are to be arranged for QBOA in scenarios where multiple instructions are issued simultaneously. The order prioritizes certain instructions to maintain consistency and alignment with system implementation rules.
0 views • 11 slides
Understanding Branching and Machine Control Instructions
This content delves into the intricate details of branching and machine control instructions in programming. It explains the three main types of instructions - JUMP (JMP), CALL, and RETURN - along with their subtypes and functionalities. The unconditional and conditional aspects of JUMP, CALL, and R
0 views • 18 slides
Understanding Arithmetic and Logic Computing in CdM-8
Explore the fundamental concepts of arithmetic and logic computing, including conditions, branches, arithmetic instructions, logic instructions, shift and move instructions, and the practical applications of shift operations. Delve into CdM-8 flags semantics, C and unsigned subtraction/comparison, b
0 views • 14 slides
Versatile Tests for Comparing Survival Curves Based on Weighted Log-Rank Statistics
Overview of various statistical tests for comparing survival curves beyond the traditional log-rank test. The focus is on weighted log-rank statistics sensitive to non-proportional hazards scenarios, with examples and methodologies discussed. These tests aim to provide more nuanced insights into dif
0 views • 31 slides
How to Synchronize EPPO Data with Log Shipping
EPPO provides multiple files in XML format, and it is challenging to update data in a SQLite database. Log shipping is a technique for replicating a database to another instance by copying transaction log files. Follow steps to set up log shipping on the EPPO Data services portal for efficient data
0 views • 8 slides
Guide to Logging into Your Chromebook
This step-by-step guide provides instructions on how to log into your Chromebook using either your student ID and password or a QR code. Simply open the lid, press the power button, select "Next," and then proceed to log in with your credentials. For password login, enter your student ID and the def
0 views • 6 slides
Understanding 4-Log Virus Treatment and Groundwater Rule Compliance
This collection of images and information delves into the importance of 4-log virus treatment under the Groundwater Rule, regulatory requirements for groundwater systems, the basics of Ct calculations for disinfection, types of disinfectants used, and understanding log inactivation of viruses. The c
0 views • 24 slides
Detailed Instructions for Accessing Naviance and Single Sign-On Tutorial
Comprehensive guide with screenshots on how to log into Naviance, access it via Office 365 portal using single sign-on, and troubleshoot technical issues. Includes step-by-step instructions for both staff and students, along with links and visuals for easy navigation.
0 views • 8 slides
Development of Log Data Management System for Monitoring Fusion Research Operations
This project focuses on creating a Log Data Management System for monitoring operations related to MDSplus database in fusion research. The system architecture is built on Big Data Technology, incorporating components such as Flume, HDFS, Mapreduce, Kafka, and Spark Streaming. Real-time and offline
0 views • 6 slides
Utilizing Topic Modeling for Identifying Critical Log Lines in Research
By employing Topic Modeling, Vithor Bertalan, Robin Moine, and Prof. Daniel Aloise from Polytechnique Montréal's DORSAL Laboratory aim to extract essential log lines from a log parsing research. The process involves building a log parser, identifying important log lines and symptoms, and establishi
0 views • 18 slides
Importance of Logging and Auditing in Cybersecurity
Discussing the significance of logging and auditing in cybersecurity, emphasizing the need for both a priori and a posteriori techniques to prevent security violations. Logging helps record events for system analysis, while auditing involves analyzing log records to provide understandable system inf
0 views • 32 slides
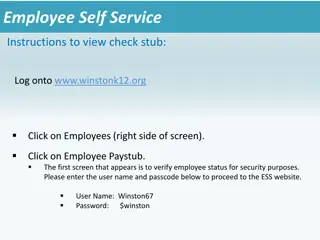
Employee Self-Service Instructions for Viewing Pay Stubs at Winston K12
Employee Self-Service (ESS) at Winston K12 allows employees to easily access and view their pay stubs online. By following the instructions provided, employees can log in to the ESS website, verify their status, and proceed to view their pay information. Registration is required for all users, and t
0 views • 6 slides
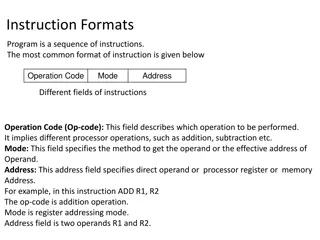
Understanding Different Instruction Formats in Computing
Instruction formats in computing include one-address, two-address, three-address, and zero-address instructions, each with specific ways of specifying operations and operands. One-address instructions utilize an implied accumulator register, while two-address and three-address instructions allow for
0 views • 18 slides
Quantum Space-Bounded Complexity in Logarithmic Space: A Comprehensive Overview
Quantum space-bounded complexity explores the memory requirements for solving problems in log space. Examples include matrix multiplication, undirected graph connectivity, and problems like inverting matrices and determining connectivity. The significance of deterministic log space (NL) and nondeter
0 views • 49 slides
Raft: A Consensus Algorithm for Replicated Logs Overview
Raft is a consensus algorithm developed by Diego Ongaro and John Ousterhout at Stanford University. It aims to ensure replicated log clients and consensus modules maintain proper log replication and state machine execution across servers. Raft utilizes leader election, normal operation for log repli
0 views • 31 slides