Enhancing Security with Two-Factor Authentication in Funding & Tenders Portal
Increase in cybersecurity threats necessitates the use of two-factor authentication in the Funding & Tenders Portal to safeguard valuable information. Users are encouraged to adopt this secure login method, which will soon become mandatory. Methods such as mobile devices, SMS, and security keys are
1 views • 31 slides
Guide to Setting Up EU Login and Two-Factor Authentication
Learn how to create your EU Login account and add two-factor authentication for accessing Europass and other EU services. Follow step-by-step instructions to register, verify your email, and set up a secure password. Ensure a seamless process by understanding the difference between Europass and EU L
3 views • 18 slides
Understanding Computer Networks and Servers
Computer networks are groups of connected computers that allow communication and resource sharing. They utilize network media, adapters, operating systems, and protocols. Servers are specialized network computers that provide centralized access to resources like applications, files, and email servic
1 views • 53 slides
Understanding Mail Server Basics from a Linux Operating System Perspective
Dive into the essentials of mail servers, exploring the key components of an email system, such as email clients and servers. Learn how email clients work, the functions they offer, and the role of email servers in managing and routing messages to ensure delivery over the Internet.
0 views • 25 slides
Post-COVID-19 Operational Guide for PCR Inc.
The operational guide outlines safety protocols for PCR Inc. post-COVID-19, emphasizing a 50% capacity limit, presence of a certified food manager on-site, adherence to social distancing guidelines, frequent sanitation of high-touch surfaces, and mandatory mask-wearing. Employees are required to wea
2 views • 7 slides
Understanding Concurrent Processing in Client-Server Software
Concurrency in client-server software allows for simultaneous computing, involving multi-user systems, time-sharing, and multiprocessing. This concept is vital in distributed computing, occurring among clients and servers, as well as within networks. Developers design client programs without conside
3 views • 26 slides
Two-Step Authentication Implementation for Enhanced Security
Learn about the implementation of two-step authentication at a university to combat phishing attacks and enhance security. Discover how Duo Security was used to provide a seamless two-step authentication solution, the challenges faced during the enrollment tool setup, and the successful implementati
0 views • 10 slides
Implementing 2FA for UW Azure AD: Best Practices and Options
Explore the implementation of two-factor authentication (2FA) for UW Azure Active Directory (AD) based on key decisions and options outlined in the provided slides. Understand the strategies for enforcing MFA, handling legacy authentication, and transitioning to cloud-based authentication. Discover
0 views • 19 slides
Security and Authentication in Electronic Filing Systems: Arkansas Subcommittee Report
Explore the subcommittee report on security and authentication in electronic filing systems for campaign and finance reports in Arkansas. Learn about user authentication, risks, mitigation strategies, and approaches used in other states. Discover the filing processes in both paper and electronic for
0 views • 24 slides
Why the Best Dedicated Servers Run on Linux
In the realm of web hosting, dedicated servers stand as the pinnacle of performance, control, and reliability. When it comes to choosing an operating system for these servers, Linux consistently emerges as the top choice for businesses, developers, a
1 views • 11 slides
Server Design Alternatives - A Comprehensive Overview
Exploring various server design alternatives such as preforked servers, threaded servers, prethreaded servers, sequential servers, and multiplexed servers. Discussing their implementations, efficiency, limitations, and potential combinations for optimal performance.
1 views • 12 slides
Discussion on Provisioning Servers Addressing Information in 3GPP TS 23.501
Background CT4 LS in S2-2200200 issue 2 discussed the interpretation and intention of the addressing information for Provisioning Servers (PVS) as stated in 3GPP TS 23.501. The focus was on whether the provided PVS IP addresses and/or FQDNs are for a single PVS server or multiple servers and how the
0 views • 4 slides
DAVA Drugs Authentication & Verification Application by National Informatics Centre
The DAVA Drugs Authentication & Verification Application, developed by the National Informatics Centre of the Government of India, enables authentication, tracking, and tracing of Indian drugs at different packaging levels. Manufacturers maintain Unique Serial Numbers for primary and secondary packa
2 views • 42 slides
Setting Up Two-Factor Authentication for HRMS Access
Learn how to enhance HR system security by setting up two-factor authentication for off-campus access. This tutorial covers the importance of two-factor authentication, using your phone as a second layer of security, initial setup procedures through Wyoweb, requesting permission for HR self-service
0 views • 9 slides
Fault-tolerant and Load-balanced VuFind Project Overview
Project Background: Part of the National Digital Library initiative, the VuFind project aims to provide a discovery interface for Finnish archives, libraries, and museums. It started development in 2012 due to the insufficiency of existing commercial products. The focus is on enhancing fault toleran
1 views • 19 slides
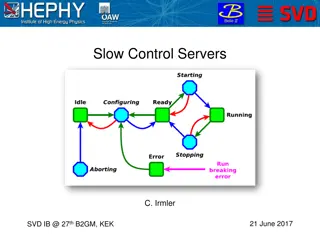
Slow Control Servers and Network Configuration for SVD Management
The documentation discusses the setup and requirements for slow control servers, network configuration, FADC server status, ENV server status, and general SC server status for SVD management. It outlines the need for backup servers, minimum server requirements, server specifications, procurement det
0 views • 11 slides
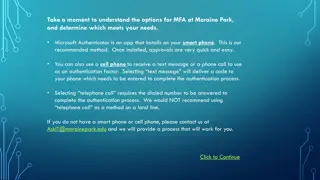
Setting Up Multi-Factor Authentication at Moraine Park
Explore the options for setting up Multi-Factor Authentication (MFA) at Moraine Park, with Microsoft Authenticator as the recommended method. You can choose between using the Microsoft Authenticator app on a smartphone, receiving a text message, or a phone call for authentication. Detailed steps for
1 views • 16 slides
Understanding Authentication Mechanisms and Security Vulnerabilities
Authentication lies at the core of application security, serving as the primary defense against malicious attacks. This article explores various authentication technologies, including HTML forms-based authentication, multi-factor mechanisms, client SSL certificates, and more. It delves into common d
0 views • 70 slides
An Open-Source SPDM Implementation for Secure Device Communication
This article introduces an open-source SPDM (Secure Protocol and Data Model) implementation for secure device communication, developed by Jiewen Yao and Xiaoyu Ruan, Principal Engineers at Intel. SPDM aims to enhance device security through protocols for device authentication, session key establishm
0 views • 29 slides
Authentication and Authorization in Astronomy: A Deep Dive into ASTERICS
Explore the world of authentication and authorization in the field of astronomy through the lens of the ASTERICS project. Learn about the importance of verifying identities and granting access rights, the Virtual Observatory Approach, Single Sign-On standards, and Credential Delegation protocols. Di
0 views • 9 slides
Evolution of User Authentication Practices: Moving Beyond IP Filtering
The article explores the obsolescence of IP filtering in user authentication, highlighting the challenges posed by evolving technology and the limitations of IP-based authentication methods. It discusses the shift towards improving user experience and addressing security concerns by focusing on user
0 views • 22 slides
Understanding Identity and Owin in .NET Applications
Explore the concept of Identity and Owin in .NET development, covering authorization attributes, Owin pipeline, claim types, authentication middleware, and more. Learn how Owin defines a standard interface for web servers and applications, and how it integrates with Microsoft servers and frameworks.
0 views • 11 slides
Understanding Client-Server Paradigm in Distributed Systems
Client-server paradigm in distributed systems involves structuring systems as collaborating processes where clients request services from servers. The model follows a request/reply protocol, with servers providing centralized control of shared resources. Advantages include security and simplicity, w
1 views • 30 slides
Understanding Domain Names for Authoritative DNS Servers
Researchers need to accurately define the types of authoritative DNS servers they sample when measuring server properties. This study focuses on collecting domain names used for web servers to assess typical domain name characteristics, highlighting the importance of accurate data for research purpo
0 views • 7 slides
Understanding Client-Server Computing in Distributed Systems
Client-server interaction forms the foundation of distributed computing, where clients rely on servers to perform operations. Clients can be various applications like browsers, email clients, and office software, while servers manage network resources and serve specific functions such as file storag
0 views • 17 slides
Minimum Direct Connections to Achieve Simultaneous Access
In a computer science laboratory with 15 workstations and 10 servers, the minimum number of direct connections needed to ensure that any set of 10 or fewer workstations can simultaneously access different servers is determined using the Generalized Pigeonhole Principle. By strategically connecting w
0 views • 5 slides
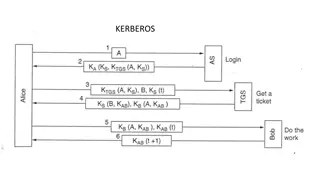
Understanding Kerberos Authentication in Network Security
Kerberos is a trusted authentication service for establishing secure communication between clients and servers in a distributed environment. Developed at MIT, it addresses threats like user impersonation and eavesdropping by providing centralized authentication. Kerberos relies on symmetric encrypti
0 views • 13 slides
Understanding Kerberos Authentication Protocol
Kerberos is a secure authentication protocol developed at M.I.T. to allow workstation users to access network resources securely. It involves three servers: Authentication Server (AS), Ticket-Granting Server (TGS), and the server performing the requested tasks. The AS verifies users, TGS issues tick
0 views • 12 slides
Understanding Email Technologies and Infrastructure
Explore the intricacies of email technologies, infrastructure, and architecture, including the format of HTTP messages, the role of proxy servers, creating web servers, and key components of email systems like user agents, mail servers, and SMTP protocol. Delve into email protocols like SMTP, POP3,
0 views • 38 slides
Understanding Client/Server Computing Architecture
Client/Server Computing architecture separates clients and servers over a network, allowing for file sharing, resource allocation, and service requests. Clients initiate services from servers, with transparent server locations and message-passing transactions. Systems with C/S architecture include f
0 views • 18 slides
Understanding Strong Customer Authentication (SCA) for Online Payments in Ireland
The Irish Retail Payments Forum at the Central Bank of Ireland discusses the implementation of Strong Customer Authentication (SCA) under PSD2 regulations. SCA aims to enhance security by validating user identity through two-factor authentication. The deadline for full SCA migration is set for Decem
0 views • 13 slides
Secure Authentication Using ISO 15693 RFID Tags
The authentication process with ISO 15693 tags involves generating a signature using a hash of the tag UID and a private key. This signature, programmed during manufacturing, must match with the one generated by the reader for successful authentication. Advantages include enhanced security with priv
0 views • 7 slides
Uncovering Flaws in Authentication Solutions: A Privacy Concern
Delve into the potential privacy risks posed by design flaws in authentication solutions, as discussed by security consultant David Johansson. Explore scenarios where digital identities can be compromised, the implications of exposed electronic IDs, and the urgent need for software updates to safegu
0 views • 34 slides
Understanding Authentication and Authorization in Information Assurance
Explore the concepts of authentication and authorization in information assurance through a series of visuals and explanations provided by Adam Doup from Arizona State University. Learn about authentication terms, mechanisms, password systems, and UNIX standard hash functions. Gain insights into how
1 views • 26 slides
ASP.NET Web API Security and Authentication Overview
Explore the essential elements of ASP.NET Web API security, including HTTPS transport security, authentication filters, access to client identities, and OWIN middleware. Learn about securing your Web API with integrity protection, replay protection, and encryption for confidentiality. Dive into the
0 views • 29 slides
Understanding the Architecture of the World Wide Web
The World Wide Web (WWW) is a vast repository of information accessible through a distributed client-server system. Users interact with web pages hosted on servers through browsers, utilizing URLs to navigate between different sites. This system consists of clients (browsers) and servers, where clie
0 views • 44 slides
Analyzing Break-In Attempts Across Multiple Servers using Apache Spark
Exploring cyber attacks on West Chester University's servers by analyzing security logs from five online servers using Apache Spark for large-scale data analysis. Uncovering attack types, frequency patterns, and sources to enhance security measures. Discover insights on break-in attempts and potenti
0 views • 19 slides
Modular Security Analysis for Key Exchange and Authentication Protocols
Explore the modular security analysis approach used to examine the security of key exchange and authentication protocols, focusing on the universally composable authentication with a global Public Key Infrastructure. The analysis involves splitting the system into smaller components, separately anal
0 views • 15 slides
Understanding Authentication and Message Authentication in Network Security
Authentication is crucial in establishing identity in the digital world to access rights, products, and services. It involves validating credentials to prove identity and ensure security. Message authentication confirms the integrity and origin of transmitted data, preventing alteration or unauthori
0 views • 24 slides
Understanding Authentication in Networking Environments
Authentication is a crucial process in computer networks where clients prove their identity to servers. This article covers the concept of authentication, its importance, and specific guidance on network authentication, particularly focusing on Windows and Linux VMs. Key topics include the use of pa
0 views • 30 slides