Enhancing Security with Two-Factor Authentication in Funding & Tenders Portal
Increase in cybersecurity threats necessitates the use of two-factor authentication in the Funding & Tenders Portal to safeguard valuable information. Users are encouraged to adopt this secure login method, which will soon become mandatory. Methods such as mobile devices, SMS, and security keys are
1 views • 31 slides
Vi-CELL.BLU - Advanced Cell Counting Instrument
Vi-CELL.BLU is a cutting-edge cell counting instrument that offers faster analysis, increased resolution, and improved optical sensor technology for enhanced cell concentration and viability assessments. The device features a user-friendly interface, Trypan blue method for live cell detection, and a
1 views • 19 slides
Understanding Cell Viability Assays in Laboratory Testing
Cell viability assays play a crucial role in determining the health and status of cells, measuring their ability to survive and proliferate. These assays involve various techniques such as dye exclusion, colorimetric, fluorometric, luminometric, and flow cytometric assays. By assessing factors like
6 views • 16 slides
Bacterial Cell Structure and Composition Overview
Bacterial cells exhibit variations in size, typically ranging from 0.75 to 1.5 micrometers. The cell envelope, comprising glycocalyx, cell wall, and cell membrane, plays crucial roles in protection and cell function. The cell membrane, a thin barrier rich in phospholipids and proteins, is integral t
1 views • 28 slides
Guide to Setting Up EU Login and Two-Factor Authentication
Learn how to create your EU Login account and add two-factor authentication for accessing Europass and other EU services. Follow step-by-step instructions to register, verify your email, and set up a secure password. Ensure a seamless process by understanding the difference between Europass and EU L
3 views • 18 slides
Overview of Cell Culture Methods and Importance in Research
Introduction to the principles of cell culture, including tissue culture, organ culture, and cell culture methods. Discusses the advantages and disadvantages of each technique and highlights the need for cell culture in research for studying cellular behavior and large-scale production of cell mater
3 views • 45 slides
Two-Step Authentication Implementation for Enhanced Security
Learn about the implementation of two-step authentication at a university to combat phishing attacks and enhance security. Discover how Duo Security was used to provide a seamless two-step authentication solution, the challenges faced during the enrollment tool setup, and the successful implementati
0 views • 10 slides
Implementing 2FA for UW Azure AD: Best Practices and Options
Explore the implementation of two-factor authentication (2FA) for UW Azure Active Directory (AD) based on key decisions and options outlined in the provided slides. Understand the strategies for enforcing MFA, handling legacy authentication, and transitioning to cloud-based authentication. Discover
0 views • 19 slides
Security and Authentication in Electronic Filing Systems: Arkansas Subcommittee Report
Explore the subcommittee report on security and authentication in electronic filing systems for campaign and finance reports in Arkansas. Learn about user authentication, risks, mitigation strategies, and approaches used in other states. Discover the filing processes in both paper and electronic for
0 views • 24 slides
Regulation of the Cell Cycle: A Comprehensive Overview
Variation in cell cycle length in humans, controlled by internal and external mechanisms, with special proteins and checkpoint systems ensuring proper progression. External events trigger initiation and inhibition of cell division, while internal checkpoints maintain genetic integrity and chromosome
4 views • 14 slides
DAVA Drugs Authentication & Verification Application by National Informatics Centre
The DAVA Drugs Authentication & Verification Application, developed by the National Informatics Centre of the Government of India, enables authentication, tracking, and tracing of Indian drugs at different packaging levels. Manufacturers maintain Unique Serial Numbers for primary and secondary packa
2 views • 42 slides
Setting Up Two-Factor Authentication for HRMS Access
Learn how to enhance HR system security by setting up two-factor authentication for off-campus access. This tutorial covers the importance of two-factor authentication, using your phone as a second layer of security, initial setup procedures through Wyoweb, requesting permission for HR self-service
0 views • 9 slides
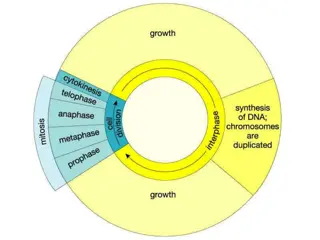
Understanding the Cell Cycle and Mitosis Process
The cell cycle consists of two main periods: Interphase and Mitosis. During Interphase, the cell prepares for division by growing in size and copying chromosomes. Mitosis, the division of the nucleus, results in the formation of two daughter cells with identical chromosome copies. Centrioles and cen
0 views • 26 slides
Understanding Cell Division: Processes and Types
Cell division is a vital process in living cells for growth and reproduction. This article explores the basics of cell division, including the cell cycle, types of cell division (such as mitosis and meiosis), and the initiation of cell division. It also covers key phases like interphase and provides
0 views • 20 slides
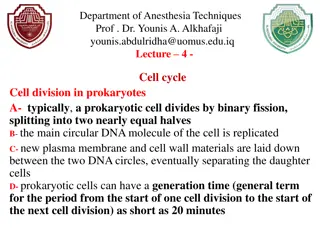
Overview of Cell Division in Prokaryotes and Eukaryotic Cells
Cell division plays a crucial role in the growth and reproduction of all organisms. In prokaryotic cells, binary fission is the primary mode of division, while eukaryotic cells undergo a more complex process involving cell growth, DNA replication, chromosome distribution, and cytokinesis. The cell c
0 views • 10 slides
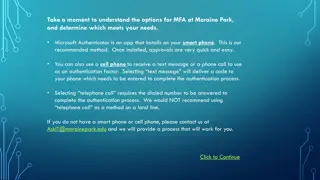
Setting Up Multi-Factor Authentication at Moraine Park
Explore the options for setting up Multi-Factor Authentication (MFA) at Moraine Park, with Microsoft Authenticator as the recommended method. You can choose between using the Microsoft Authenticator app on a smartphone, receiving a text message, or a phone call for authentication. Detailed steps for
1 views • 16 slides
Understanding Authentication Mechanisms and Security Vulnerabilities
Authentication lies at the core of application security, serving as the primary defense against malicious attacks. This article explores various authentication technologies, including HTML forms-based authentication, multi-factor mechanisms, client SSL certificates, and more. It delves into common d
0 views • 70 slides
An Open-Source SPDM Implementation for Secure Device Communication
This article introduces an open-source SPDM (Secure Protocol and Data Model) implementation for secure device communication, developed by Jiewen Yao and Xiaoyu Ruan, Principal Engineers at Intel. SPDM aims to enhance device security through protocols for device authentication, session key establishm
0 views • 29 slides
Authentication and Authorization in Astronomy: A Deep Dive into ASTERICS
Explore the world of authentication and authorization in the field of astronomy through the lens of the ASTERICS project. Learn about the importance of verifying identities and granting access rights, the Virtual Observatory Approach, Single Sign-On standards, and Credential Delegation protocols. Di
0 views • 9 slides
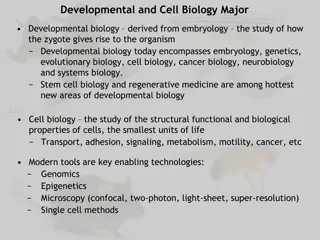
Explore the World of Developmental and Cell Biology
Developmental biology, stemming from embryology, investigates how organisms evolve from a zygote. It merges various fields like genetics, cell biology, and cancer biology. Cell biology focuses on cell properties and behaviors, using tools like genomics and microscopy. Research areas include cancer c
0 views • 8 slides
Evolution of User Authentication Practices: Moving Beyond IP Filtering
The article explores the obsolescence of IP filtering in user authentication, highlighting the challenges posed by evolving technology and the limitations of IP-based authentication methods. It discusses the shift towards improving user experience and addressing security concerns by focusing on user
0 views • 22 slides
Role of Cell Cycle in Nanoparticle Uptake and Dilution in Cell Population
The cell cycle plays a crucial role in the cellular uptake and dilution of nanoparticles within a cell population. This process involves different phases such as G1, S, G2, and M, each with specific functions related to cell growth, DNA synthesis, protein synthesis, and cell division. Understanding
0 views • 20 slides
Methods of Non-Human Cell Line Authentication and Identification
Techniques such as chromosomal karyotyping, DNA barcoding, and STR genotyping are used for authenticating and identifying non-human cell lines to ensure accurate research outcomes. Species-level identification, karyotyping, and commercial services for mouse and rat cell lines are discussed, highligh
0 views • 16 slides
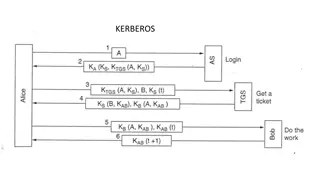
Understanding Kerberos Authentication in Network Security
Kerberos is a trusted authentication service for establishing secure communication between clients and servers in a distributed environment. Developed at MIT, it addresses threats like user impersonation and eavesdropping by providing centralized authentication. Kerberos relies on symmetric encrypti
0 views • 13 slides
Understanding Kerberos Authentication Protocol
Kerberos is a secure authentication protocol developed at M.I.T. to allow workstation users to access network resources securely. It involves three servers: Authentication Server (AS), Ticket-Granting Server (TGS), and the server performing the requested tasks. The AS verifies users, TGS issues tick
0 views • 12 slides
Exploring Cell Structure and Function in Developmental Biology
Discover the intricate world of cell structure and function in the context of developmental biology. Delve into the inner workings of organelles, their functions, and how they contribute to cellular activities. Engage in interactive activities like building cell models and playing Cell Detective to
0 views • 14 slides
Optimizing Line Coding for PM-PHY: A Detailed Analysis
Enabling line coding and channel equalization methods for PM-PHY, the IEEE 802.15.13 standard introduces overhead while enhancing channel adaptation. This contribution proposes 64b67b and Uniform Line Coding as alternative transmission modes, aiming to reduce line coding overhead while maintaining a
0 views • 26 slides
Understanding Strong Customer Authentication (SCA) for Online Payments in Ireland
The Irish Retail Payments Forum at the Central Bank of Ireland discusses the implementation of Strong Customer Authentication (SCA) under PSD2 regulations. SCA aims to enhance security by validating user identity through two-factor authentication. The deadline for full SCA migration is set for Decem
0 views • 13 slides
Understanding Cell Cycle Control in Biology
Maintaining control of the cell cycle is crucial to producing healthy daughter cells and preventing mutations that can lead to degenerative diseases like Parkinson's or cancer. Cell cycle checkpoints at G1, G2, and Metaphase ensure the cell meets specific requirements before progressing to the next
0 views • 11 slides
Understanding Cell Structure and Function
Explore the intricate world of cell biology through this comprehensive guide covering the definition of a cell, the characteristics of animal cells, the role of the nucleus, ribosomes, cell structure, organelles, cell membrane, and cell wall. Discover the fascinating details of eukaryotic cells and
0 views • 61 slides
Understanding the Functions of Cell Organelles
Explore the vital functions of different cell organelles such as the cell membrane, nucleus, endoplasmic reticulum, lysosomes, Golgi apparatus, mitochondria, cytoplasm, ribosomes, vacuole, cell wall, chloroplasts, and chlorophyll in a cell. Learn how each organelle plays a unique role in maintaining
0 views • 38 slides
Basics of Mammalian Cell Culture
Mammalian cell culture involves the removal of cells from an organism for growth in a controlled environment. Primary cell cultures can be sub-cultured, leading to the generation of cell lines. Sub-culturing involves transferring cells to fresh growth media for further growth. Different methods and
0 views • 29 slides
Secure Authentication Using ISO 15693 RFID Tags
The authentication process with ISO 15693 tags involves generating a signature using a hash of the tag UID and a private key. This signature, programmed during manufacturing, must match with the one generated by the reader for successful authentication. Advantages include enhanced security with priv
0 views • 7 slides
Uncovering Flaws in Authentication Solutions: A Privacy Concern
Delve into the potential privacy risks posed by design flaws in authentication solutions, as discussed by security consultant David Johansson. Explore scenarios where digital identities can be compromised, the implications of exposed electronic IDs, and the urgent need for software updates to safegu
0 views • 34 slides
Understanding Authentication and Authorization in Information Assurance
Explore the concepts of authentication and authorization in information assurance through a series of visuals and explanations provided by Adam Doup from Arizona State University. Learn about authentication terms, mechanisms, password systems, and UNIX standard hash functions. Gain insights into how
1 views • 26 slides
ASP.NET Web API Security and Authentication Overview
Explore the essential elements of ASP.NET Web API security, including HTTPS transport security, authentication filters, access to client identities, and OWIN middleware. Learn about securing your Web API with integrity protection, replay protection, and encryption for confidentiality. Dive into the
0 views • 29 slides
Understanding Animal Tissue Culture and Cell Line Production
Animal tissue culture involves growing tissues separate from the animal in a laboratory setting. To achieve exponential cell growth, cells are converted into immortal cell lines. The production of a cell line involves steps like breaking cell adhesion, incubation, and transferring cells to fresh med
0 views • 22 slides
Modular Security Analysis for Key Exchange and Authentication Protocols
Explore the modular security analysis approach used to examine the security of key exchange and authentication protocols, focusing on the universally composable authentication with a global Public Key Infrastructure. The analysis involves splitting the system into smaller components, separately anal
0 views • 15 slides
Understanding Authentication and Message Authentication in Network Security
Authentication is crucial in establishing identity in the digital world to access rights, products, and services. It involves validating credentials to prove identity and ensure security. Message authentication confirms the integrity and origin of transmitted data, preventing alteration or unauthori
0 views • 24 slides
Understanding Authentication in Networking Environments
Authentication is a crucial process in computer networks where clients prove their identity to servers. This article covers the concept of authentication, its importance, and specific guidance on network authentication, particularly focusing on Windows and Linux VMs. Key topics include the use of pa
0 views • 30 slides