E-commerce Market
E-commerce Market by Business Model, Browsing Medium, Payment Mode (Card Payments, Digital Wallets, Bank Transfer), Operational Channel, Offering (Beauty & Fashion, Food & Beverage, Electronic, Household) - Global Forecast to 2030
1 views • 4 slides
Asia-Pacific E-commerce Market to Be Worth $22.7 Billion by 2030
Asia-Pacific E-commerce Market by Business Model (Horizontal E-commerce and Vertical E-commerce), Browsing Medium, Payment Mode (Card Payments, Digital Wallets, Bank Transfers, Cash Payments), Operating Channel, and Offering - Forecast to 2030\n
1 views • 4 slides
Sparkle and Style: Explore Top Jewelry Shop in Dallas | Gillespie Fine Jewelers
blished in 1974, Gillespie Fine Jewelers is a reputable retailer that offers high-quality gold jewelry in Dallas. The variety of an exquisite showroom gives guests stunning works of art handpicked with the finest detail to depict luxury and sophistication. While browsing through their range of produ
4 views • 3 slides
Are You Looking For The Best Used Commercial Refrigerator
Browsing for refrigeration repair services? Axxonservices.com is a refrigeration repair company providing installation, maintenance, and repair of HVAC, refrigeration, and ice machines. Please visit our website for more details.\n\n\/\/ \/
2 views • 1 slides
EnCase Forensics: Official Study Guide Overview
Explore the key features of EnCase Forensics including the EnCase Environment, home screen navigation, browsing evidence, layout details, and case creation processes. Gain insights into working with evidence, templates, and custom options in a detailed manner to enhance your knowledge in computer fo
1 views • 32 slides
Performers and Programs Database Webinar - Overview and Features
Learn about the Performers and Programs Database Webinar happening on October 22, 2021. This webinar, presented by Peter Kowalski and introduced by Sharon B. Phillips, offers valuable information about the database's features, including how performers advertise programs, categorization, virtual prog
0 views • 25 slides
Essential Cybersecurity Practices for Safe Online Activities
Phishing attacks come in various forms such as common phishing, spear phishing, whaling, smishing, and vishing. It's crucial to be cautious when connecting to Wi-Fi networks, secure your passwords, and follow safe web browsing practices to protect your personal information online.
4 views • 5 slides
Browsing the best natural stabilizers? Nexusingredient.com is a leading
Browsing the best natural stabilizers? Nexusingredient.com is a leading supplier of natural stabilizers for a variety of industries. We provide high-quality and reliable natural stabilizers that are designed to meet the needs of our customers. Our na
2 views • 1 slides
Mapping Methodology for Establishing ESCO Relations
Learn how to set up teams, collect resources, compare classifications, and establish mapping relations for ESCO implementation projects. Get insights on using computer-assisted suggestions, updating mapping tables, and selecting mapping projects. Explore techniques for navigating classifications, br
1 views • 21 slides
Understanding Malware: Types, Usage, and Protection
Malware, short for malicious software, encompasses various forms of hostile software designed to disrupt computer operation, steal sensitive information, or gain unauthorized access. It includes viruses, trojan horses, worms, spyware, phishing, ransomware, and more. Malware is often used to steal pe
1 views • 49 slides
Instagram Like App | Socialmediamarketplace.com
Browsing for the Instagram Like App? Socialmediamarketplace.com is a well-known platform for Instagram likes. Likes are a social media marketing indicator that has long been used to determine the performance of Instagram content. For more data, visit
2 views • 1 slides
Impact of Carrier-Grade NAT on Web Browsing: A Comprehensive Analysis
The research delves into the effects of Carrier-Grade NAT on web browsing, discussing traditional NAT mechanisms, deployment implications of Carrier Grade NAT, and investigation goals. Methodologies for large-scale passive measurement in real ISP deployments are outlined, focusing on monitoring web
0 views • 25 slides
Natural Green Tea | Threespoons.ie
Browsing for a delicious and healthy way to enjoy green tea? Threespoons.ie offers a variety of natural green tea blends that are perfect for any occasion. Visit our shop or explore our selection online.
3 views • 1 slides
Understanding Graphical User Interfaces in Java
Learn about designing graphical user interfaces in Java, including layout management, common components like radio buttons and menus, browsing Java documentation effectively, and utilizing inheritance for complex frames. Explore topics such as using layout managers to organize UI components, creatin
0 views • 74 slides
Search Google or Type a URL , which is a better approach
Wondering if you should search or type URL? Explore the benefits of both methods and find out which is better for your browsing habits.
1 views • 9 slides
Introduction to Internet Basics and Web Browsing
Exploring the fundamental concepts of networks and the internet, this overview covers key elements like IP addresses, DNS, protocols, web browsers, and more. Understanding these basics is essential for navigating the online world effectively.
0 views • 24 slides
Add New Renault Certification Authorities to Internet Explorer
Learn how to add the new Renault Certification Authorities to your Microsoft Internet Explorer browser to ensure secure website browsing. Follow the step-by-step instructions provided to install the necessary certificates for a trusted browsing experience.
0 views • 11 slides
YHI Account Locking: Reasons and Resolutions
Your YHI account could get locked due to multiple failed login attempts, inactivity, or accumulation of browsing data. Learn the common causes of locked accounts and their resolutions, including steps to reset your password or username, reactivate a dormant account, and clear browsing data. Contact
0 views • 7 slides
Mastering Chromebooks: Tips and Tricks for Ultimate Productivity
Unleash the full potential of your Chromebook with this comprehensive guide. Learn essential care tips, keyboard shortcuts, touchpad techniques, and how your settings follow you across devices. Enhance your browsing experience and productivity with these invaluable insights.
0 views • 22 slides
Free Indian VPN for Tiktok
Access effortlessly with our Free Indian VPN for Tiktok, designed for fast speeds and secure browsing. Ideal for overcoming geo-restrictions and enjoying unrestricted content from India.
0 views • 5 slides
Faculty Success Survey Fall 2022 for New Hires at VSU: Insights and Feedback
Detailed insights and feedback from faculty members at VSU on their employment experience, including tenure, rank/position, how they found the open position, what attracted them to VSU, issues faced during the application process, response time from the university, and browsing experience on the VSU
0 views • 31 slides
Free Indian VPN for Tiktok
Access effortlessly with our Free Indian VPN for Tiktok, designed for fast speeds and secure browsing. Ideal for overcoming geo-restrictions and enjoying unrestricted content from India.
0 views • 5 slides
Understanding Web Browsers and Internet Explorer
Web browsers are essential software applications that allow users to navigate the internet by interpreting HTML files, handling multimedia content, managing history, and more. Learn about the features of web browsers, their support for web standards like HTML and JavaScript, and how to open Internet
0 views • 17 slides
Guide to Clearing Browser Cache for Better Online Experience
Learn how to clear cache on Internet Explorer, Firefox, and Chrome to avoid distorted data and inaccurate information during a weekend release. Follow simple steps provided for each browser to ensure smooth browsing experience on BT Wholesale Online. Access the user guide via My BT Wholesale.
0 views • 8 slides
Understanding the Tor Network: An In-Depth Overview
The Tor Network, developed in the mid-1990s, is a volunteer-based network that prioritizes privacy and security for Internet users through encryption and random pathways. By utilizing Onion Routing, Tor preserves anonymity but has limitations such as lack of application-level security and plugin usa
0 views • 13 slides
Exploring Data Ethics: Questions, Uses, Benefits, and Risks
Panelists discuss the ethical use of data, sources like pre-enrollment browsing and healthcare records, current and near-future predictive analytics uses, potential benefits and risks, and the FIPPs approach to privacy protection. Privacy violations, algorithmic bias, and data ownership pose risks,
0 views • 10 slides
Understanding Malware: Types, Symptoms, and Countermeasures
Malware is malicious software that can alter computer settings, behavior, files, services, ports, and speed. Sources of malware include insufficient security, honeypot websites, free downloads, torrents, pop-ups, emails, and infected media. Symptoms of malware include unusual computer behavior, slow
0 views • 9 slides
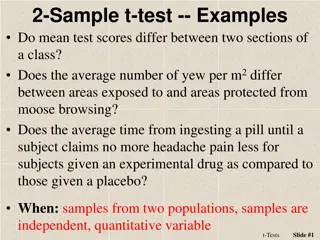
Understanding 2-Sample t-Test Examples
The 2-sample t-test is used to determine if mean scores differ between two groups in various scenarios, such as comparing test scores in different sections, yew density in moose browsing areas, or headache pain relief with different treatments. Key steps include formulating hypotheses, calculating t
0 views • 13 slides
How to Discover Books Using Destiny in Guilford County Schools
Guilford County School students can access a wide range of books, including eBooks, through Destiny, the Media Center catalog. Browsing is currently not allowed, but students can put books on hold and manage checkouts online. Students can log in using their ID number and birthday, search for books b
0 views • 16 slides
Enhancing Library Services with Book Display Widgets
Explore how Wheaton Public Library utilizes innovative book display widgets to enhance user experience and promote library collections. From dynamic grid carousels to easy setup/update features, discover the benefits of incorporating these widgets for a seamless browsing experience. Additionally, le
0 views • 16 slides
Step-by-Step Guide to Creating a Piestar RFx Account for Livestock Innovation
Learn how to create a Piestar RFx account for the Feed the Future Innovation Lab for Livestock Systems in a detailed step-by-step guide. From signing up to browsing funding opportunities and submitting your application, follow this guide to access resources for your livestock projects.
0 views • 10 slides
Investigating the Privacy Risks of Private Browsing
Private browsing, a feature available in major browsers, is used by approximately 450 million users. However, this study reveals potential security vulnerabilities, such as leftover artifacts in memory and issues with SQLite databases, that may compromise users' sensitive information even after clos
0 views • 19 slides
Understanding Web Browsers: Features and Functions
Web browsers are essential software applications used for accessing and navigating information resources on the internet. They enable users to visit websites, search for specific content, and perform various tasks such as tabbed browsing, bookmarking, and refreshing pages. Different web browsers lik
0 views • 20 slides
Practical Guide to Drawing Long-Term Yield Curve at Krugersdrift Dam
Learn how to draw a long-term yield curve at Krugersdrift Dam step-by-step, including setting up the study, browsing for data, importing hydrology files, manipulating the curve for accuracy, and achieving the final result.
0 views • 7 slides
Search Google or Type a URL - Harvee designs
Wondering if you should search or type URL? Explore the benefits of both methods and find out which is better for your browsing habits.
1 views • 8 slides
Web Security Fundamentals: Understanding the Same Origin Policy
Explore the basic principles of web security focusing on the Same Origin Policy, operating system analogies, isolation of content sources, browser sandboxing, and setting cookies securely by servers. Learn how these concepts help ensure a safe browsing experience and prevent common vulnerabilities l
0 views • 37 slides
Internet Safety Guide for Children
In this animated presentation, children are introduced to the Internet, its uses, and safety measures. The content explains the concept of the Internet, its purpose, and highlights the importance of adult supervision while browsing. Tips on safe Internet usage and what to do when encountering unfami
0 views • 14 slides
Enhancing Browser Experience with Safe Chrome Extensions for All
Explore the world of Chrome extensions for users with disabilities, presented in a webinar by Adaptech Research Network Student Panel. Learn about the safety measures, installation steps, and key features of these extensions. Discover how these tools can improve productivity, reading, writing, and m
0 views • 14 slides
Clearing Browser Cache and Cookies: Google Chrome Edition
In this guide, you will learn how to clear the browser cache and cookies in Google Chrome. Follow the easy steps to ensure smooth browsing experience. From accessing your browser settings to selecting the right options, this tutorial covers it all. Keep your browser running efficiently by regularly
0 views • 6 slides
Understanding Web Security: Threats and Protections
Exploring the landscape of web security through discussions on historical vulnerabilities, top web threats, browser security models, and the goals of web security. Delve into the world of web programming, security threat models, and learn about the goals and importance of maintaining a secure web br
0 views • 74 slides