2 Factor Authentication, cionsystems
Reduce the chance of your data and accounts of being hacked with 2 Factor Authentication. https:\/\/rb.gy\/tvtkan
4 views • 7 slides
Enhancing Security with Two-Factor Authentication in Funding & Tenders Portal
Increase in cybersecurity threats necessitates the use of two-factor authentication in the Funding & Tenders Portal to safeguard valuable information. Users are encouraged to adopt this secure login method, which will soon become mandatory. Methods such as mobile devices, SMS, and security keys are
1 views • 31 slides
Enhancing Security with Multi-Factor Authentication for NHS Mail Users
Multi-Factor Authentication (MFA) is being enforced for all NHSmail accounts to safeguard patient data and prevent cyber-attacks. Understand the benefits, importance, and steps to enroll in MFA to enhance security measures. Protecting sensitive information is crucial in the digital age to ensure pat
2 views • 10 slides
Theories of Intelligence: Monarchie vs. Spearman's Two-Factor Theory
The Monarchie Theory of Intelligence posits a single factor of intelligence, while Spearman's Two-Factor Theory divides intelligence into a general ability (G-factor) and specific abilities (S-factors). The implications of these theories on educational practices are discussed, shedding light on the
11 views • 25 slides
Understanding Blood Clotting Factors in the Human Body
Blood clotting factors play a crucial role in the coagulation process to prevent excessive bleeding. Factors such as Fibrinogen (Factor-I), Prothrombin (Factor-II), Thromboplastin (Factor-III), Calcium Ions (Factor-IV), Labile Factor (Factor-V), and Stable Factor (Factor-VII) are essential for the c
7 views • 14 slides
Two Factor Authentication, cionsysytems
Reduce the chance of your data and accounts of being hacked with 2 Factor Authentication. \/\/rb.gy\/6nndve
5 views • 2 slides
IGX Orientation 2023: Logging In, Two-Factor Authentication, Dashboard Setup
Step-by-step guide for logging into IGX for the first time, resetting forgotten credentials, setting up two-factor authentication, and customizing the dashboard with panels. Learn how to access your account, ensure security, and personalize your user experience effortlessly.
0 views • 9 slides
The Fitz Factor: Your Ultimate Fitness Guide
Discover the power of personalized fitness with The Fitz Factor, where expert advice meets real-life results. Our brand is dedicated to providing you with top-notch fitness tips, innovative workout strategies, and comprehensive wellness guidance. Whether you're looking to kickstart your fitness jour
2 views • 4 slides
The Fitz Factor: Your Ultimate Fitness Guide
Discover the power of personalized fitness with The Fitz Factor, where expert advice meets real-life results. Our brand is dedicated to providing you with top-notch fitness tips, innovative workout strategies, and comprehensive wellness guidance. Whether you're looking to kickstart your fitness jour
0 views • 4 slides
The Fitz Factor: Your Ultimate Fitness Guide
Discover the power of personalized fitness with The Fitz Factor, where expert advice meets real-life results. Our brand is dedicated to providing you with top-notch fitness tips, innovative workout strategies, and comprehensive wellness guidance. Whether you're looking to kickstart your fitness jour
0 views • 4 slides
The Fitz Factor: Your Ultimate Fitness Guide
Discover the power of personalized fitness with The Fitz Factor, where expert advice meets real-life results. Our brand is dedicated to providing you with top-notch fitness tips, innovative workout strategies, and comprehensive wellness guidance. Whether you're looking to kickstart your fitness jour
0 views • 4 slides
The Fitz Factor: Your Ultimate Fitness Guide
Discover the power of personalized fitness with The Fitz Factor, where expert advice meets real-life results. Our brand is dedicated to providing you with top-notch fitness tips, innovative workout strategies, and comprehensive wellness guidance. Whether you're looking to kickstart your fitness jour
0 views • 4 slides
Understanding the Concept of Return to Factor in Production Economics
Return to Factor is a key concept in production economics that explains the relationship between variable inputs like labor and total production output. The concept is based on the three stages of production - increasing returns, diminishing returns, and negative returns. By analyzing the behavior o
0 views • 7 slides
Guide to Setting Up EU Login and Two-Factor Authentication
Learn how to create your EU Login account and add two-factor authentication for accessing Europass and other EU services. Follow step-by-step instructions to register, verify your email, and set up a secure password. Ensure a seamless process by understanding the difference between Europass and EU L
3 views • 18 slides
Enhancing Security with Multi-Factor Authentication in IAM
Multi-Factor Authentication (MFA) is crucial for protecting sensitive accounts, online infrastructure, and research data within Identity and Access Management (IAM) systems. MFA adds an extra layer of security by requiring additional verification factors like one-time passcodes and recovery codes. U
0 views • 11 slides
Understanding Spearman's Two-Factor Theory
Spearman's Two-Factor Theory posits a general mental energy factor (g) and specific abilities factors (s), determining individual intelligence. The g factor is innate and crucial in various activities, while the s factor is acquired and varies per task. Despite criticisms regarding the oversimplific
0 views • 9 slides
Importance of Multi-Factor Authentication in Ensuring Data Security
Multi-Factor Authentication (MFA) is crucial for safeguarding sensitive information from cyber threats. Learn about the significance of MFA, its implementation process, and the benefits it offers in protecting accounts from unauthorized access. Find out why it is essential for companies to adopt MFA
2 views • 12 slides
UTORMFA: Enhancing Security with Multi-Factor Authentication at University of Toronto
In November and December 2020, the University of Toronto is introducing UTORMFA, a multi-factor authentication service for staff, faculty, and librarians. This additional layer of security, using Duo Mobile MFA, requires two credentials for account access. Learn how to self-enroll, supported platfor
0 views • 20 slides
Implementing 2FA for UW Azure AD: Best Practices and Options
Explore the implementation of two-factor authentication (2FA) for UW Azure Active Directory (AD) based on key decisions and options outlined in the provided slides. Understand the strategies for enforcing MFA, handling legacy authentication, and transitioning to cloud-based authentication. Discover
0 views • 19 slides
Security and Authentication in Electronic Filing Systems: Arkansas Subcommittee Report
Explore the subcommittee report on security and authentication in electronic filing systems for campaign and finance reports in Arkansas. Learn about user authentication, risks, mitigation strategies, and approaches used in other states. Discover the filing processes in both paper and electronic for
0 views • 24 slides
Enhancing Security with Multi-Factor Authentication Webinar
Join us for a comprehensive webinar on Multi-Factor Authentication (MFA) where we discuss the importance of MFA in today's evolving threat landscape, how to implement MFA in your organization, and the benefits it offers in safeguarding your business and data. This webinar is aimed at providing valua
0 views • 21 slides
DAVA Drugs Authentication & Verification Application by National Informatics Centre
The DAVA Drugs Authentication & Verification Application, developed by the National Informatics Centre of the Government of India, enables authentication, tracking, and tracing of Indian drugs at different packaging levels. Manufacturers maintain Unique Serial Numbers for primary and secondary packa
2 views • 42 slides
Setting Up Two-Factor Authentication for HRMS Access
Learn how to enhance HR system security by setting up two-factor authentication for off-campus access. This tutorial covers the importance of two-factor authentication, using your phone as a second layer of security, initial setup procedures through Wyoweb, requesting permission for HR self-service
0 views • 9 slides
Understanding Analytic Rotation in Factor Analysis
Factor analysis involves rotation of the factor loading matrix to enhance interpretability. This process was originally done manually but is now performed analytically with computers. Factors can be orthogonal or oblique, impacting the interpretation of factor loadings. Understanding rotation simpli
0 views • 42 slides
Analyzing Experimental Design with One-Factor and Two-Factor GLMs
Comparing the experimental designs of one-factor (1-way ANOVA) and two-factor GLMs, this content explores biological questions that can be answered through the analysis of multiple factors simultaneously in experiments. It discusses sample sizes, drug treatments, factor levels, and concentration var
0 views • 13 slides
Mastering SAS for Data Analytics - Factor Analysis Essentials
Factor analysis is a dimension reduction technique used to identify latent variables from observed data. Exploratory factor analysis involves steps like computing correlations, extracting factors, rotating factors for interpretation, and computing factor scores. SAS PROC FACTOR is commonly used for
1 views • 34 slides
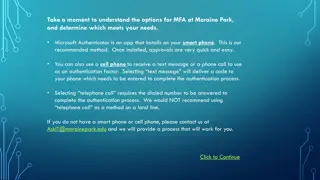
Setting Up Multi-Factor Authentication at Moraine Park
Explore the options for setting up Multi-Factor Authentication (MFA) at Moraine Park, with Microsoft Authenticator as the recommended method. You can choose between using the Microsoft Authenticator app on a smartphone, receiving a text message, or a phone call for authentication. Detailed steps for
1 views • 16 slides
Understanding Authentication Mechanisms and Security Vulnerabilities
Authentication lies at the core of application security, serving as the primary defense against malicious attacks. This article explores various authentication technologies, including HTML forms-based authentication, multi-factor mechanisms, client SSL certificates, and more. It delves into common d
0 views • 70 slides
Treatment Strategies for Recurrent Venous Thromboembolism in Factor V Leiden Patients
This presentation discusses the treatment options for recurrent venous thromboembolism in patients with Factor V Leiden mutation. It explores the pathophysiology, epidemiology, and diagnosis criteria for Factor V Leiden, reviews failed anticoagulation history, and suggests outpatient anticoagulation
0 views • 31 slides
An Introduction to Factor Analysis: Course Logistics for PSY544
This course in PSY544 introduces students to factor analysis with a focus on understanding the statistical theory behind the model. Taught in English, the course covers lecture times, prerequisites, math requirements, and grading criteria. Emphasizing the inner workings of factor analysis, it aims t
0 views • 16 slides
Evolution of User Authentication Practices: Moving Beyond IP Filtering
The article explores the obsolescence of IP filtering in user authentication, highlighting the challenges posed by evolving technology and the limitations of IP-based authentication methods. It discusses the shift towards improving user experience and addressing security concerns by focusing on user
0 views • 22 slides
Understanding Kerberos Authentication in Network Security
Kerberos is a trusted authentication service for establishing secure communication between clients and servers in a distributed environment. Developed at MIT, it addresses threats like user impersonation and eavesdropping by providing centralized authentication. Kerberos relies on symmetric encrypti
0 views • 13 slides
Understanding Strong Customer Authentication (SCA) for Online Payments in Ireland
The Irish Retail Payments Forum at the Central Bank of Ireland discusses the implementation of Strong Customer Authentication (SCA) under PSD2 regulations. SCA aims to enhance security by validating user identity through two-factor authentication. The deadline for full SCA migration is set for Decem
0 views • 13 slides
Secure Authentication Using ISO 15693 RFID Tags
The authentication process with ISO 15693 tags involves generating a signature using a hash of the tag UID and a private key. This signature, programmed during manufacturing, must match with the one generated by the reader for successful authentication. Advantages include enhanced security with priv
0 views • 7 slides
Understanding Authentication and Authorization in Information Assurance
Explore the concepts of authentication and authorization in information assurance through a series of visuals and explanations provided by Adam Doup from Arizona State University. Learn about authentication terms, mechanisms, password systems, and UNIX standard hash functions. Gain insights into how
0 views • 26 slides
Integrating HID Prox Card II with Multi-Factor Authentication Systems
Boost security by integrating HID Prox Card II with multi-factor authentication for enhanced protection.\n
1 views • 6 slides
Understanding Authentication and Message Authentication in Network Security
Authentication is crucial in establishing identity in the digital world to access rights, products, and services. It involves validating credentials to prove identity and ensure security. Message authentication confirms the integrity and origin of transmitted data, preventing alteration or unauthori
0 views • 24 slides
Understanding Two-Factor Authentication for Enhanced Security
Two-factor authentication adds an extra layer of security by requiring two verification steps to access an account. This process helps prevent unauthorized access even if passwords are compromised. Explore different types of two-factor authentication methods such as text message, fingerprint scanner
0 views • 8 slides
Proximity-Proof: Secure and Usable Mobile Two-Factor Authentication
Explore the implementation of secure and user-friendly mobile two-factor authentication solutions, adding an extra layer of security to online accounts. Learn about the motivation behind commercial 2FA solutions and the importance of user involvement in enhancing security measures.
0 views • 46 slides
Understanding Authentication in Networking Environments
Authentication is a crucial process in computer networks where clients prove their identity to servers. This article covers the concept of authentication, its importance, and specific guidance on network authentication, particularly focusing on Windows and Linux VMs. Key topics include the use of pa
0 views • 30 slides