Top Crypto Launchpads To Watch In 2024
At BlockchainX tech, we help startups, medium-sized enterprises, and large-sized businesses by providing end-to-end blockchain development services such as token creation, token sale distribution, landing page design, whitepaper writing, and smart contract creation. \nhttps:\/\/www.blockchainx.tech\
4 views • 7 slides
Enhancing Security with Two-Factor Authentication in Funding & Tenders Portal
Increase in cybersecurity threats necessitates the use of two-factor authentication in the Funding & Tenders Portal to safeguard valuable information. Users are encouraged to adopt this secure login method, which will soon become mandatory. Methods such as mobile devices, SMS, and security keys are
1 views • 31 slides
DOWNLOAD/PDF The Love Token : A delightful story of a love that defies time (Gr
11 minutes ago - COPY LINK TO DOWNLOAD = http:\/\/cupangbalapmope.blogspot.com\/?cread=B0B6XY4WZK | PDF\/READ The Love Token : A delightful story of a love that defies time (GraceTown Book 2) | Alexis Spencer thinks she has it all figured out. Even when life gets her down, she’s never too far
0 views • 4 slides
Understanding Ethereum Token Standards: ERC-20, ERC-721, and ERC-1155
Delve into the world of blockchain, cryptocurrencies, and decentralized technologies with a focus on Ethereum token standards ERC-20, ERC-721, and ERC-1155. Learn about the differences between fungible and non-fungible tokens, smart contracts, and examples of popular tokens in the space. Explore how
0 views • 9 slides
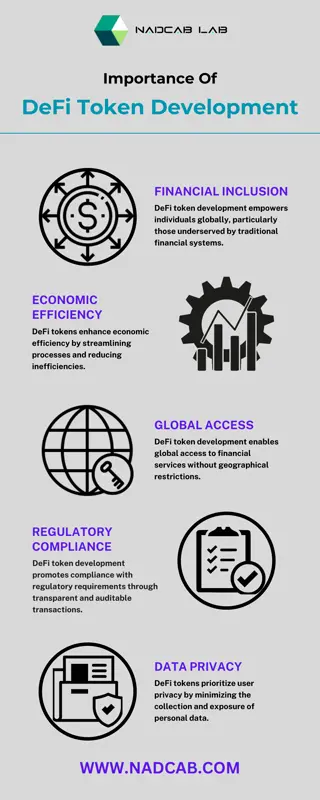
DeFi Token Development
As demand for DeFi Token Development services continues to grow, Nadcab Labs remains committed to innovative solutions that not only meet current market needs but also anticipate future trends.\n
5 views • 1 slides
BEP20-Token-Development-Company
Ready to launch your own custom BEP-20 token? Look no further! With Bitdeal's expert BEP-20 token development services, you can create your own digital asset on the Binance Smart Chain. Whether you're a startup looking to tokenize assets or an established business seeking to leverage blockchain te
1 views • 8 slides
BTR: Binary Token Representations for Efficient Retrieval Augmented Language Models
Retrieval-augmented language models like BTR address issues such as hallucination by providing efficient solutions for encoding input passages and queries. By utilizing cacheable binary token representations, BTR offers a unique approach to decomposing and binarizing passage encoding to improve runt
0 views • 9 slides
The Role of a Blockchain Development Company
At BlockchainX tech, we help startups, medium-sized enterprises, and large-sized businesses by providing end-to-end blockchain development services such as token creation, token sale distribution, landing page design, whitepaper writing, and smart contract creation. https:\/\/www.blockchainx.tech\/
1 views • 8 slides
Layer 2 Token Marketing Services
Layer-2 token marketing promotes tokens built on scalable layer-2 solutions, highlighting benefits like faster transactions and lower fees. Get connected with our experts today and launch a lucrative \ntoken platform.
0 views • 3 slides
Ethereum Token Development Company
Ethereum token development leverages the Ethereum blockchain to create and manage digital assets through smart contracts. Our Ethereum developers provide end-to-end Ethereum token development services in standards such as ERC-20, ERC-721, and ERC-115
0 views • 3 slides
Guide to Setting Up EU Login and Two-Factor Authentication
Learn how to create your EU Login account and add two-factor authentication for accessing Europass and other EU services. Follow step-by-step instructions to register, verify your email, and set up a secure password. Ensure a seamless process by understanding the difference between Europass and EU L
3 views • 18 slides
SkyHub.App Walkthrough: Getting Started, Login, Home Page, Notifications, Devices, Expo Token, Settings
Explore the SkyHub.App with a comprehensive walkthrough covering how to get started, login, navigate the home page, manage notifications, access devices, view the Expo Token, and adjust settings. From downloading the APK file to utilizing various features, this guide provides step-by-step instructio
2 views • 16 slides
Two-Step Authentication Implementation for Enhanced Security
Learn about the implementation of two-step authentication at a university to combat phishing attacks and enhance security. Discover how Duo Security was used to provide a seamless two-step authentication solution, the challenges faced during the enrollment tool setup, and the successful implementati
0 views • 10 slides
Token Economies and Behaviour Modification in Custody: Evaluating Efficacy
This article explores the application of token economies in prisons as a behaviour modification technique based on operant conditioning. Token economies involve exchanging tokens for desired behaviours, aiming to replace undesirable actions with positive reinforcement. The use of increments, consist
0 views • 19 slides
Understanding JSON Web Tokens (JWT) in Web Development
JSON Web Tokens (JWT) are a simple and commonly used type of token that is self-contained, meaning the data is stored within the token itself. They consist of three parts: Header, Payload, and Signature. JWTs are signed by the server using a secret key, allowing clients to read the data without bein
3 views • 6 slides
Implementing 2FA for UW Azure AD: Best Practices and Options
Explore the implementation of two-factor authentication (2FA) for UW Azure Active Directory (AD) based on key decisions and options outlined in the provided slides. Understand the strategies for enforcing MFA, handling legacy authentication, and transitioning to cloud-based authentication. Discover
0 views • 19 slides
Security and Authentication in Electronic Filing Systems: Arkansas Subcommittee Report
Explore the subcommittee report on security and authentication in electronic filing systems for campaign and finance reports in Arkansas. Learn about user authentication, risks, mitigation strategies, and approaches used in other states. Discover the filing processes in both paper and electronic for
0 views • 24 slides
Understanding Token Ring Technology in Computer Networks
Token Ring, developed by IBM, is a networking technology that uses a token passing scheme for data transmission. Devices on the network take turns transmitting data by holding a token and releasing it after data transfer. Unlike Ethernet, Token Ring offers unique benefits and operates efficiently in
2 views • 17 slides
DAVA Drugs Authentication & Verification Application by National Informatics Centre
The DAVA Drugs Authentication & Verification Application, developed by the National Informatics Centre of the Government of India, enables authentication, tracking, and tracing of Indian drugs at different packaging levels. Manufacturers maintain Unique Serial Numbers for primary and secondary packa
2 views • 42 slides
Setting Up Two-Factor Authentication for HRMS Access
Learn how to enhance HR system security by setting up two-factor authentication for off-campus access. This tutorial covers the importance of two-factor authentication, using your phone as a second layer of security, initial setup procedures through Wyoweb, requesting permission for HR self-service
0 views • 9 slides
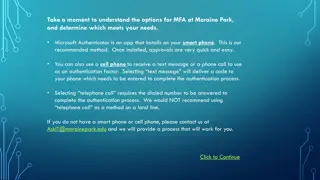
Setting Up Multi-Factor Authentication at Moraine Park
Explore the options for setting up Multi-Factor Authentication (MFA) at Moraine Park, with Microsoft Authenticator as the recommended method. You can choose between using the Microsoft Authenticator app on a smartphone, receiving a text message, or a phone call for authentication. Detailed steps for
1 views • 16 slides
Understanding Authentication Mechanisms and Security Vulnerabilities
Authentication lies at the core of application security, serving as the primary defense against malicious attacks. This article explores various authentication technologies, including HTML forms-based authentication, multi-factor mechanisms, client SSL certificates, and more. It delves into common d
0 views • 70 slides
An Open-Source SPDM Implementation for Secure Device Communication
This article introduces an open-source SPDM (Secure Protocol and Data Model) implementation for secure device communication, developed by Jiewen Yao and Xiaoyu Ruan, Principal Engineers at Intel. SPDM aims to enhance device security through protocols for device authentication, session key establishm
0 views • 29 slides
Authentication and Authorization in Astronomy: A Deep Dive into ASTERICS
Explore the world of authentication and authorization in the field of astronomy through the lens of the ASTERICS project. Learn about the importance of verifying identities and granting access rights, the Virtual Observatory Approach, Single Sign-On standards, and Credential Delegation protocols. Di
0 views • 9 slides
Evolution of User Authentication Practices: Moving Beyond IP Filtering
The article explores the obsolescence of IP filtering in user authentication, highlighting the challenges posed by evolving technology and the limitations of IP-based authentication methods. It discusses the shift towards improving user experience and addressing security concerns by focusing on user
0 views • 22 slides
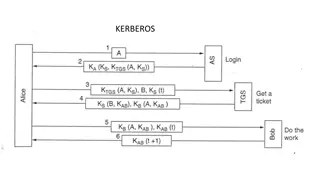
Understanding Kerberos Authentication in Network Security
Kerberos is a trusted authentication service for establishing secure communication between clients and servers in a distributed environment. Developed at MIT, it addresses threats like user impersonation and eavesdropping by providing centralized authentication. Kerberos relies on symmetric encrypti
0 views • 13 slides
Understanding Kerberos Authentication Protocol
Kerberos is a secure authentication protocol developed at M.I.T. to allow workstation users to access network resources securely. It involves three servers: Authentication Server (AS), Ticket-Granting Server (TGS), and the server performing the requested tasks. The AS verifies users, TGS issues tick
0 views • 12 slides
Enhancing Name and Address Parsing for Data Standardization
Explore the project focused on improving the quality of name and address parsing using active learning methods at the University of Arkansas. Learn about the importance of parsing, entity resolution, and the token pattern approach in standardizing and processing unstructured addresses. Discover the
0 views • 11 slides
Understanding Strong Customer Authentication (SCA) for Online Payments in Ireland
The Irish Retail Payments Forum at the Central Bank of Ireland discusses the implementation of Strong Customer Authentication (SCA) under PSD2 regulations. SCA aims to enhance security by validating user identity through two-factor authentication. The deadline for full SCA migration is set for Decem
0 views • 13 slides
Secure Authentication Using ISO 15693 RFID Tags
The authentication process with ISO 15693 tags involves generating a signature using a hash of the tag UID and a private key. This signature, programmed during manufacturing, must match with the one generated by the reader for successful authentication. Advantages include enhanced security with priv
0 views • 7 slides
Uncovering Flaws in Authentication Solutions: A Privacy Concern
Delve into the potential privacy risks posed by design flaws in authentication solutions, as discussed by security consultant David Johansson. Explore scenarios where digital identities can be compromised, the implications of exposed electronic IDs, and the urgent need for software updates to safegu
0 views • 34 slides
Understanding Authentication and Authorization in Information Assurance
Explore the concepts of authentication and authorization in information assurance through a series of visuals and explanations provided by Adam Doup from Arizona State University. Learn about authentication terms, mechanisms, password systems, and UNIX standard hash functions. Gain insights into how
1 views • 26 slides
ASP.NET Web API Security and Authentication Overview
Explore the essential elements of ASP.NET Web API security, including HTTPS transport security, authentication filters, access to client identities, and OWIN middleware. Learn about securing your Web API with integrity protection, replay protection, and encryption for confidentiality. Dive into the
0 views • 29 slides
Integrating Hashicorp Vault with HTCondor for Secure Oauth Credential Management
Exploring the use of token-based authentication over X.509 certificates for improved security in HTCondor workflows. The transition to tokens offers enhanced control and flexibility, with a focus on utilizing JWTs and Scitokens. Leveraging Hashicorp Vault alongside HTCondor streamlines the managemen
0 views • 18 slides
Modular Security Analysis for Key Exchange and Authentication Protocols
Explore the modular security analysis approach used to examine the security of key exchange and authentication protocols, focusing on the universally composable authentication with a global Public Key Infrastructure. The analysis involves splitting the system into smaller components, separately anal
0 views • 15 slides
Understanding Authentication and Message Authentication in Network Security
Authentication is crucial in establishing identity in the digital world to access rights, products, and services. It involves validating credentials to prove identity and ensure security. Message authentication confirms the integrity and origin of transmitted data, preventing alteration or unauthori
0 views • 24 slides
Understanding Two-Factor Authentication for Enhanced Security
Two-factor authentication adds an extra layer of security by requiring two verification steps to access an account. This process helps prevent unauthorized access even if passwords are compromised. Explore different types of two-factor authentication methods such as text message, fingerprint scanner
0 views • 8 slides
Understanding Authentication in Networking Environments
Authentication is a crucial process in computer networks where clients prove their identity to servers. This article covers the concept of authentication, its importance, and specific guidance on network authentication, particularly focusing on Windows and Linux VMs. Key topics include the use of pa
0 views • 30 slides
Understanding Electronic Mail Security: PGP and S/MIME
Explore the world of Electronic Mail Security through the lenses of two prominent systems - PGP and S/MIME. Learn about the origins of PGP encryption, the authentication and confidentiality problems it addresses, and the utilization of S/MIME in business and personal electronic mail. Discover the ke
0 views • 10 slides
Scalable Cryptographic Authentication for High Performance Computing
This work discusses the scalable cryptographic authentication approach developed by Andrew Prout and team for high-performance computing. The LLGrid system architecture, challenges with interactive supercomputing, and utilization of LLGrid for various computing tasks are explored, highlighting the i
0 views • 34 slides