Enhancing Security with Two-Factor Authentication in Funding & Tenders Portal
Increase in cybersecurity threats necessitates the use of two-factor authentication in the Funding & Tenders Portal to safeguard valuable information. Users are encouraged to adopt this secure login method, which will soon become mandatory. Methods such as mobile devices, SMS, and security keys are
1 views • 31 slides
Customer and Business Support (CABS) - Enhancing Customer Experience
CABS plays a crucial role in the council service supply chain by managing customer inquiries efficiently. They handle a wide range of services including switchboard operations, housing queries, leisure services, and more. Additionally, CABS works closely with partner services, administers various fu
1 views • 15 slides
How to Delete a Customer in QuickBooks
Deleting a customer in QuickBooks involves a few simple steps. First, navigate to the \"Customers\" menu and select \"Customer Center.\" Find the customer you want to delete, right-click on their name, and choose \"Delete Customer.\" QuickBooks will prompt you to confirm the deletion; ensure you're
4 views • 4 slides
Understanding Federal Customer Experience Initiative
Federal customer experience initiative focuses on improving customer satisfaction with federal services. Services play a crucial role in shaping customer perception and satisfaction, impacting the overall reputation of an organization or brand. By prioritizing customer experience, agencies aim to en
0 views • 6 slides
Understanding Customer Interactions Through Journey Mapping
Customer journey mapping and empathy mapping are essential tools for businesses to comprehend typical customer interactions, decisions, and emotions throughout the product acquisition cycle. By creating representative personas and empathy maps, teams can gain deeper insights into customer needs and
1 views • 12 slides
Understanding Critical to Customer (CTC) and Critical to Quality (CTQ)
Quality is determined by meeting customer needs. Critical to Customer (CTC) Flowdown translates these needs into Critical to Quality (CTQ) aspects. This tool helps organizations identify what is critical to meet customer expectations, serving as a communication tool and guiding improvement projects.
2 views • 10 slides
Importance of Respecting Customer Needs in Customer Service
Respect is fundamental in customer service as it fosters good relationships, loyalty, and satisfaction. Understanding and addressing customer needs, whether product functionality or empathy, are key to delivering effective service. Showing respect through easy access, acknowledging mistakes, prompt
0 views • 9 slides
Guide to Setting Up EU Login and Two-Factor Authentication
Learn how to create your EU Login account and add two-factor authentication for accessing Europass and other EU services. Follow step-by-step instructions to register, verify your email, and set up a secure password. Ensure a seamless process by understanding the difference between Europass and EU L
3 views • 18 slides
Two-Step Authentication Implementation for Enhanced Security
Learn about the implementation of two-step authentication at a university to combat phishing attacks and enhance security. Discover how Duo Security was used to provide a seamless two-step authentication solution, the challenges faced during the enrollment tool setup, and the successful implementati
0 views • 10 slides
Importance of Good Customer Service in Organizations
Understanding the benefits of good customer service is essential for any organization. Customer service involves meeting customers' needs professionally and efficiently. Good customer service leads to increased sales, customer loyalty, enhanced public image, and a more effective workforce. On the ot
1 views • 7 slides
Implementing 2FA for UW Azure AD: Best Practices and Options
Explore the implementation of two-factor authentication (2FA) for UW Azure Active Directory (AD) based on key decisions and options outlined in the provided slides. Understand the strategies for enforcing MFA, handling legacy authentication, and transitioning to cloud-based authentication. Discover
0 views • 19 slides
Security and Authentication in Electronic Filing Systems: Arkansas Subcommittee Report
Explore the subcommittee report on security and authentication in electronic filing systems for campaign and finance reports in Arkansas. Learn about user authentication, risks, mitigation strategies, and approaches used in other states. Discover the filing processes in both paper and electronic for
0 views • 24 slides
Electronic Customer Relationship Management (E-CRM) in E-Commerce
In this presentation by Prof. Pampa Jana, the focus is on E-CRM for organization interaction strategies. E-CRM involves managing online customer relations and building long-term customer relationships through technology. Key aspects include assessing customer actions, integrated databases, automated
0 views • 11 slides
Understanding Customer Relationship Management (CRM) for Business Success
Customer Relationship Management (CRM) is a vital business strategy that focuses on shifting goals from traditional seller-oriented approaches to customer-centric models. It aligns business strategies with customer information and technology to foster mutually beneficial relationships. CRM enables b
1 views • 21 slides
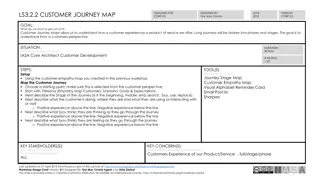
Customer Journey Mapping Workshop Guide for Understanding Customer Experiences
This guide outlines a structured approach for conducting a Customer Journey Mapping workshop to understand how customers interact with products or services. It provides detailed steps, tools, key stakeholders, and goals for mapping the customer journey effectively. The workshop aims to gain insights
0 views • 5 slides
DAVA Drugs Authentication & Verification Application by National Informatics Centre
The DAVA Drugs Authentication & Verification Application, developed by the National Informatics Centre of the Government of India, enables authentication, tracking, and tracing of Indian drugs at different packaging levels. Manufacturers maintain Unique Serial Numbers for primary and secondary packa
2 views • 42 slides
Setting Up Two-Factor Authentication for HRMS Access
Learn how to enhance HR system security by setting up two-factor authentication for off-campus access. This tutorial covers the importance of two-factor authentication, using your phone as a second layer of security, initial setup procedures through Wyoweb, requesting permission for HR self-service
0 views • 9 slides
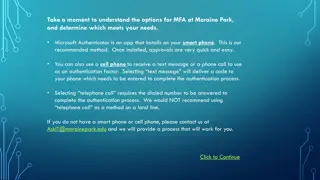
Setting Up Multi-Factor Authentication at Moraine Park
Explore the options for setting up Multi-Factor Authentication (MFA) at Moraine Park, with Microsoft Authenticator as the recommended method. You can choose between using the Microsoft Authenticator app on a smartphone, receiving a text message, or a phone call for authentication. Detailed steps for
1 views • 16 slides
Understanding Authentication Mechanisms and Security Vulnerabilities
Authentication lies at the core of application security, serving as the primary defense against malicious attacks. This article explores various authentication technologies, including HTML forms-based authentication, multi-factor mechanisms, client SSL certificates, and more. It delves into common d
0 views • 70 slides
An Open-Source SPDM Implementation for Secure Device Communication
This article introduces an open-source SPDM (Secure Protocol and Data Model) implementation for secure device communication, developed by Jiewen Yao and Xiaoyu Ruan, Principal Engineers at Intel. SPDM aims to enhance device security through protocols for device authentication, session key establishm
0 views • 29 slides
Authentication and Authorization in Astronomy: A Deep Dive into ASTERICS
Explore the world of authentication and authorization in the field of astronomy through the lens of the ASTERICS project. Learn about the importance of verifying identities and granting access rights, the Virtual Observatory Approach, Single Sign-On standards, and Credential Delegation protocols. Di
0 views • 9 slides
Evolution of User Authentication Practices: Moving Beyond IP Filtering
The article explores the obsolescence of IP filtering in user authentication, highlighting the challenges posed by evolving technology and the limitations of IP-based authentication methods. It discusses the shift towards improving user experience and addressing security concerns by focusing on user
0 views • 22 slides
Effective Customer Relationship Management Strategies
Implementing Customer Relationship Management (CRM) can increase customer loyalty, minimize customer defection, and identify target customers. Learn how to enhance customer satisfaction, gain loyalty, and address reasons for customer loss through innovative strategies.
0 views • 7 slides
Cashier Training for Resolving Customer Problems
This training covers essential aspects of cashier and CSR roles, such as answering customer queries, resolving issues, involving managers when necessary, and handling customer feedback effectively. It includes topics like special terms, common customer questions, handling customer problems, manager
0 views • 8 slides
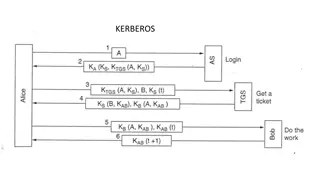
Understanding Kerberos Authentication in Network Security
Kerberos is a trusted authentication service for establishing secure communication between clients and servers in a distributed environment. Developed at MIT, it addresses threats like user impersonation and eavesdropping by providing centralized authentication. Kerberos relies on symmetric encrypti
0 views • 13 slides
Understanding Kerberos Authentication Protocol
Kerberos is a secure authentication protocol developed at M.I.T. to allow workstation users to access network resources securely. It involves three servers: Authentication Server (AS), Ticket-Granting Server (TGS), and the server performing the requested tasks. The AS verifies users, TGS issues tick
0 views • 12 slides
Creating Customers for Life: The Golden Customer Rule and Emotional Loyalty
Learn how to create customers for life by implementing the Golden Customer Rule, understanding customer emotions that drive buying and loyalty, and focusing on customer service management best practices. Discover the importance of building strong relationships, being responsive and rewarding, and of
0 views • 43 slides
Understanding Strong Customer Authentication (SCA) for Online Payments in Ireland
The Irish Retail Payments Forum at the Central Bank of Ireland discusses the implementation of Strong Customer Authentication (SCA) under PSD2 regulations. SCA aims to enhance security by validating user identity through two-factor authentication. The deadline for full SCA migration is set for Decem
0 views • 13 slides
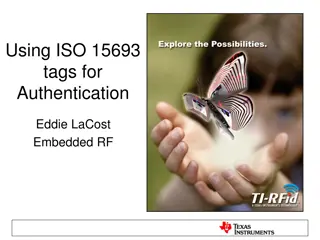
Secure Authentication Using ISO 15693 RFID Tags
The authentication process with ISO 15693 tags involves generating a signature using a hash of the tag UID and a private key. This signature, programmed during manufacturing, must match with the one generated by the reader for successful authentication. Advantages include enhanced security with priv
0 views • 7 slides
Uncovering Flaws in Authentication Solutions: A Privacy Concern
Delve into the potential privacy risks posed by design flaws in authentication solutions, as discussed by security consultant David Johansson. Explore scenarios where digital identities can be compromised, the implications of exposed electronic IDs, and the urgent need for software updates to safegu
0 views • 34 slides
Understanding Authentication and Authorization in Information Assurance
Explore the concepts of authentication and authorization in information assurance through a series of visuals and explanations provided by Adam Doup from Arizona State University. Learn about authentication terms, mechanisms, password systems, and UNIX standard hash functions. Gain insights into how
1 views • 26 slides
Understanding Customer Satisfaction and Its Impact
Customer satisfaction is crucial for businesses to thrive. Different types of customers, such as current, indirect, potential, and lost customers, play a significant role in shaping the success of an organization. Neglecting to measure customer satisfaction can lead to lower sales, reduced profits,
0 views • 13 slides
ASP.NET Web API Security and Authentication Overview
Explore the essential elements of ASP.NET Web API security, including HTTPS transport security, authentication filters, access to client identities, and OWIN middleware. Learn about securing your Web API with integrity protection, replay protection, and encryption for confidentiality. Dive into the
0 views • 29 slides
Modular Security Analysis for Key Exchange and Authentication Protocols
Explore the modular security analysis approach used to examine the security of key exchange and authentication protocols, focusing on the universally composable authentication with a global Public Key Infrastructure. The analysis involves splitting the system into smaller components, separately anal
0 views • 15 slides
Understanding Authentication and Message Authentication in Network Security
Authentication is crucial in establishing identity in the digital world to access rights, products, and services. It involves validating credentials to prove identity and ensure security. Message authentication confirms the integrity and origin of transmitted data, preventing alteration or unauthori
0 views • 24 slides
Understanding Two-Factor Authentication for Enhanced Security
Two-factor authentication adds an extra layer of security by requiring two verification steps to access an account. This process helps prevent unauthorized access even if passwords are compromised. Explore different types of two-factor authentication methods such as text message, fingerprint scanner
0 views • 8 slides
Understanding Authentication in Networking Environments
Authentication is a crucial process in computer networks where clients prove their identity to servers. This article covers the concept of authentication, its importance, and specific guidance on network authentication, particularly focusing on Windows and Linux VMs. Key topics include the use of pa
0 views • 30 slides
Best Practices for Password Security and User Authentication
Password security is crucial for protecting sensitive information. Passwords should not be shared and should be changed regularly to prevent unauthorized access. Implementing strong passwords, two-factor authentication, and biometric security measures can greatly enhance security. Additionally, main
0 views • 16 slides
Understanding Electronic Mail Security: PGP and S/MIME
Explore the world of Electronic Mail Security through the lenses of two prominent systems - PGP and S/MIME. Learn about the origins of PGP encryption, the authentication and confidentiality problems it addresses, and the utilization of S/MIME in business and personal electronic mail. Discover the ke
0 views • 10 slides
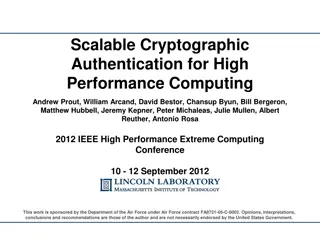
Scalable Cryptographic Authentication for High Performance Computing
This work discusses the scalable cryptographic authentication approach developed by Andrew Prout and team for high-performance computing. The LLGrid system architecture, challenges with interactive supercomputing, and utilization of LLGrid for various computing tasks are explored, highlighting the i
0 views • 34 slides