Public key encryption, Digital signature and authentication
Understand the concept of public key encryption, asymmetric encryption, and the widely used RSA algorithm. Explore how public key cryptography revolutionized the field of encryption and its applications in confidentiality, authentication, and key distribution.
4 views • 12 slides
2 Factor Authentication, cionsystems
Reduce the chance of your data and accounts of being hacked with 2 Factor Authentication. https:\/\/rb.gy\/tvtkan
4 views • 7 slides
Enhancing Security with Two-Factor Authentication in Funding & Tenders Portal
Increase in cybersecurity threats necessitates the use of two-factor authentication in the Funding & Tenders Portal to safeguard valuable information. Users are encouraged to adopt this secure login method, which will soon become mandatory. Methods such as mobile devices, SMS, and security keys are
1 views • 31 slides
Overcoming the UX Challenges Faced by FIDO Credentials in the Faced by FIDO Credentials in the Consumer Space
Many websites are vulnerable to phishing attacks due to traditional authentication methods. To address this, the utilization of cryptographic authentication, such as key pairs, is recommended to enhance security and prevent MITM attacks.
0 views • 17 slides
Enhancing Security with Multi-Factor Authentication for NHS Mail Users
Multi-Factor Authentication (MFA) is being enforced for all NHSmail accounts to safeguard patient data and prevent cyber-attacks. Understand the benefits, importance, and steps to enroll in MFA to enhance security measures. Protecting sensitive information is crucial in the digital age to ensure pat
2 views • 10 slides
Two Factor Authentication, cionsysytems
Reduce the chance of your data and accounts of being hacked with 2 Factor Authentication. \/\/rb.gy\/6nndve
6 views • 2 slides
IGX Orientation 2023: Logging In, Two-Factor Authentication, Dashboard Setup
Step-by-step guide for logging into IGX for the first time, resetting forgotten credentials, setting up two-factor authentication, and customizing the dashboard with panels. Learn how to access your account, ensure security, and personalize your user experience effortlessly.
0 views • 9 slides
3D Secure Authentication Market 2022 Growth, Progress Insight by Forecast to 202
Adroit Market Research has included the Global 3D Secure Authentication Market\u00a0research to its database in order to provide a thorough analysis of the variables driving a general market growth trend. The study contains a lot of information and is a useful tool for professionals in the field.
0 views • 5 slides
WFDSS Login Changes and New authentication Process Overview
The changes in the WFDSS login process starting November 2023 involve transitioning to a new two-factor authentication process through e-Authenticate and Login.gov called FAMAuth. Federal users will use e-Authenticate with their PIV cards, while non-federal users will validate credentials through Lo
3 views • 11 slides
Guide to Setting Up EU Login and Two-Factor Authentication
Learn how to create your EU Login account and add two-factor authentication for accessing Europass and other EU services. Follow step-by-step instructions to register, verify your email, and set up a secure password. Ensure a seamless process by understanding the difference between Europass and EU L
3 views • 18 slides
Enhancing Security with Multi-Factor Authentication in IAM
Multi-Factor Authentication (MFA) is crucial for protecting sensitive accounts, online infrastructure, and research data within Identity and Access Management (IAM) systems. MFA adds an extra layer of security by requiring additional verification factors like one-time passcodes and recovery codes. U
0 views • 11 slides
Understanding Sender, Message, Receiver Correspondence in Communication Process
Communication process involves sender, message, and receiver elements. The sender initiates communication, generates a message, and conveys it to the receiver. The message is encoded, transmitted through a channel, and decoded by the receiver. Noise can hinder the communication process by interferin
1 views • 13 slides
Two-Step Authentication Implementation for Enhanced Security
Learn about the implementation of two-step authentication at a university to combat phishing attacks and enhance security. Discover how Duo Security was used to provide a seamless two-step authentication solution, the challenges faced during the enrollment tool setup, and the successful implementati
0 views • 10 slides
Understanding Internet Mail Architecture Components
The Internet mail architecture consists of key components including Message User Agents (MUA), Mail Submission Agent (MSA), Message Transfer Agent (MTA), Mail Delivery Agent (MDA), and Message Store (MS). These components work together to facilitate the sending, receiving, and storing of email messa
6 views • 4 slides
Implementing 2FA for UW Azure AD: Best Practices and Options
Explore the implementation of two-factor authentication (2FA) for UW Azure Active Directory (AD) based on key decisions and options outlined in the provided slides. Understand the strategies for enforcing MFA, handling legacy authentication, and transitioning to cloud-based authentication. Discover
0 views • 19 slides
Security and Authentication in Electronic Filing Systems: Arkansas Subcommittee Report
Explore the subcommittee report on security and authentication in electronic filing systems for campaign and finance reports in Arkansas. Learn about user authentication, risks, mitigation strategies, and approaches used in other states. Discover the filing processes in both paper and electronic for
0 views • 24 slides
Understanding the Impact of Message Creation on Communication Processes
The process of communication begins with creating a message, which can significantly influence how it is received. Messages, conveyed through words, signs, or sounds, are interpreted by receivers based on the sender's delivery. Littlejohn (2018) emphasizes the importance of how senders initiate comm
1 views • 9 slides
DAVA Drugs Authentication & Verification Application by National Informatics Centre
The DAVA Drugs Authentication & Verification Application, developed by the National Informatics Centre of the Government of India, enables authentication, tracking, and tracing of Indian drugs at different packaging levels. Manufacturers maintain Unique Serial Numbers for primary and secondary packa
2 views • 42 slides
Setting Up Two-Factor Authentication for HRMS Access
Learn how to enhance HR system security by setting up two-factor authentication for off-campus access. This tutorial covers the importance of two-factor authentication, using your phone as a second layer of security, initial setup procedures through Wyoweb, requesting permission for HR self-service
0 views • 9 slides
Setting Up Multi-Factor Authentication at Moraine Park
Explore the options for setting up Multi-Factor Authentication (MFA) at Moraine Park, with Microsoft Authenticator as the recommended method. You can choose between using the Microsoft Authenticator app on a smartphone, receiving a text message, or a phone call for authentication. Detailed steps for
1 views • 16 slides
Understanding Authentication Mechanisms and Security Vulnerabilities
Authentication lies at the core of application security, serving as the primary defense against malicious attacks. This article explores various authentication technologies, including HTML forms-based authentication, multi-factor mechanisms, client SSL certificates, and more. It delves into common d
0 views • 70 slides
An Open-Source SPDM Implementation for Secure Device Communication
This article introduces an open-source SPDM (Secure Protocol and Data Model) implementation for secure device communication, developed by Jiewen Yao and Xiaoyu Ruan, Principal Engineers at Intel. SPDM aims to enhance device security through protocols for device authentication, session key establishm
0 views • 29 slides
Authentication and Authorization in Astronomy: A Deep Dive into ASTERICS
Explore the world of authentication and authorization in the field of astronomy through the lens of the ASTERICS project. Learn about the importance of verifying identities and granting access rights, the Virtual Observatory Approach, Single Sign-On standards, and Credential Delegation protocols. Di
0 views • 9 slides
Evolution of User Authentication Practices: Moving Beyond IP Filtering
The article explores the obsolescence of IP filtering in user authentication, highlighting the challenges posed by evolving technology and the limitations of IP-based authentication methods. It discusses the shift towards improving user experience and addressing security concerns by focusing on user
0 views • 22 slides
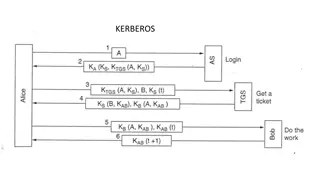
Understanding Kerberos Authentication in Network Security
Kerberos is a trusted authentication service for establishing secure communication between clients and servers in a distributed environment. Developed at MIT, it addresses threats like user impersonation and eavesdropping by providing centralized authentication. Kerberos relies on symmetric encrypti
0 views • 13 slides
Understanding Kerberos Authentication Protocol
Kerberos is a secure authentication protocol developed at M.I.T. to allow workstation users to access network resources securely. It involves three servers: Authentication Server (AS), Ticket-Granting Server (TGS), and the server performing the requested tasks. The AS verifies users, TGS issues tick
0 views • 12 slides
Practical Aspects of Modern Cryptography: November 2016
Exploring session-based protocols, SSL/TLS, certificates, and public key infrastructure, this presentation delves into the motivation behind secure online interactions, discussing the importance of verifying identities, ensuring data confidentiality, maintaining message integrity, and authenticating
0 views • 137 slides
IPC Lab 2 MessageQ Client/Server Example
This MessageQ example demonstrates the client/server pattern using SYS/BIOS heap for message pool, anonymous message queue, and return address implementation. The example involves two processors - HOST and DSP, where the DSP processor acts as the server creating a named message queue, and the HOST p
0 views • 12 slides
Understanding Strong Customer Authentication (SCA) for Online Payments in Ireland
The Irish Retail Payments Forum at the Central Bank of Ireland discusses the implementation of Strong Customer Authentication (SCA) under PSD2 regulations. SCA aims to enhance security by validating user identity through two-factor authentication. The deadline for full SCA migration is set for Decem
0 views • 13 slides
Secure Authentication Using ISO 15693 RFID Tags
The authentication process with ISO 15693 tags involves generating a signature using a hash of the tag UID and a private key. This signature, programmed during manufacturing, must match with the one generated by the reader for successful authentication. Advantages include enhanced security with priv
0 views • 7 slides
Uncovering Flaws in Authentication Solutions: A Privacy Concern
Delve into the potential privacy risks posed by design flaws in authentication solutions, as discussed by security consultant David Johansson. Explore scenarios where digital identities can be compromised, the implications of exposed electronic IDs, and the urgent need for software updates to safegu
0 views • 34 slides
Understanding Authentication and Authorization in Information Assurance
Explore the concepts of authentication and authorization in information assurance through a series of visuals and explanations provided by Adam Doup from Arizona State University. Learn about authentication terms, mechanisms, password systems, and UNIX standard hash functions. Gain insights into how
1 views • 26 slides
ASP.NET Web API Security and Authentication Overview
Explore the essential elements of ASP.NET Web API security, including HTTPS transport security, authentication filters, access to client identities, and OWIN middleware. Learn about securing your Web API with integrity protection, replay protection, and encryption for confidentiality. Dive into the
0 views • 29 slides
Modular Security Analysis for Key Exchange and Authentication Protocols
Explore the modular security analysis approach used to examine the security of key exchange and authentication protocols, focusing on the universally composable authentication with a global Public Key Infrastructure. The analysis involves splitting the system into smaller components, separately anal
0 views • 15 slides
Understanding Authentication and Message Authentication in Network Security
Authentication is crucial in establishing identity in the digital world to access rights, products, and services. It involves validating credentials to prove identity and ensure security. Message authentication confirms the integrity and origin of transmitted data, preventing alteration or unauthori
0 views • 24 slides
Understanding Two-Factor Authentication for Enhanced Security
Two-factor authentication adds an extra layer of security by requiring two verification steps to access an account. This process helps prevent unauthorized access even if passwords are compromised. Explore different types of two-factor authentication methods such as text message, fingerprint scanner
0 views • 8 slides
Understanding Authentication in Networking Environments
Authentication is a crucial process in computer networks where clients prove their identity to servers. This article covers the concept of authentication, its importance, and specific guidance on network authentication, particularly focusing on Windows and Linux VMs. Key topics include the use of pa
0 views • 30 slides
Network Security: A Top-Down Approach Overview
This content delves into the fundamental principles of network security, covering topics such as cryptography, authentication, message integrity, and security measures at different network layers. It explores the concepts of confidentiality, authentication, message integrity, access, and availabilit
0 views • 66 slides
Understanding Electronic Mail Security: PGP and S/MIME
Explore the world of Electronic Mail Security through the lenses of two prominent systems - PGP and S/MIME. Learn about the origins of PGP encryption, the authentication and confidentiality problems it addresses, and the utilization of S/MIME in business and personal electronic mail. Discover the ke
0 views • 10 slides
Scalable Cryptographic Authentication for High Performance Computing
This work discusses the scalable cryptographic authentication approach developed by Andrew Prout and team for high-performance computing. The LLGrid system architecture, challenges with interactive supercomputing, and utilization of LLGrid for various computing tasks are explored, highlighting the i
0 views • 34 slides