Airport Security Market to be Worth $25.27 Billion by 2031
\u00ae, the airport security market is projected to reach $25.27 billion by 2031, at a CAGR of 8.6% from 2024 to 2031. Some of the major factors driving the growth of this market are stringent government regulations for airport security and the growing number of air passengers. In addition, increasi
6 views • 5 slides
KEERTHI SECURITY - Best Security Agencies In Bangalore
Keerthi Security is a security and facility management services provider in Bangalore. We are committed to offering top-notch security services for commercial and residential places. We aim to offer very secure and reliable security services to everyone. Our best-trained security guards are very sha
9 views • 11 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
0 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Understanding the Role of Security Champions in Organizations
Security Champions play a vital role in decision-making concerning security engagement, acting as a core element in security assurance processes within a team. They foster a security culture, reduce dependency on the CISO, and promote responsible autonomy and continuous security education in the org
3 views • 13 slides
Digital Wellness and Password Security Lesson for Students
This lesson focuses on promoting digital wellness and teaching students about password security. It covers topics such as creating strong passwords, safeguarding personal information, and the importance of balancing online and offline interactions. Through activities and discussions, students learn
0 views • 13 slides
Unlocking Solutions: Addressing QuickBooks Company File Incorrect Password Issue
Unlocking Solutions: Addressing QuickBooks Company File Incorrect Password Issues\nQuickBooks, a vital tool for businesses, can encounter password-related hurdles, disrupting workflow. This guide explores causes and solutions to incorrect password issues. Forgotten passwords, user permission errors,
1 views • 5 slides
Cybersecurity Best Practices for Password Protection and Incident Response
Enhance your cybersecurity knowledge with insights on password management, cybercriminal tactics, creating strong passwords, and password complexity. Learn how to safeguard your data and prevent cyber threats by implementing strong password rules, multi-factor authentication, and incident response s
2 views • 24 slides
Understanding Device Settings and Strong Passwords for Digital Citizenship
This lesson focuses on understanding device settings and the importance of creating strong passwords for digital citizenship. It covers topics such as changing backgrounds, locking screens, creating strong passwords, common password mistakes to avoid, and tips for password safety. The lesson also in
1 views • 11 slides
Understanding the Roles of a Security Partner
Learn about the roles and responsibilities of a Security Partner, including requesting changes to security roles, approving security requests, and initiating access requests. Explore the overview of Workday Security, the security access request process, and the pre-request process flow. Discover how
1 views • 17 slides
Strengthen Your Digital Literacy with Strong Password Strategies
Enhance your digital literacy by learning about the importance of strong passwords, strategies for creating secure passwords, and the role of password managers. Explore various resources, videos, and tools to improve your password security and protect your online accounts effectively.
0 views • 5 slides
Promote Feature Adoption with Self-Service Password Reset Posters
Enhance feature adoption of self-service password reset among your employees with these ready-to-use posters. Simply customize and print them to encourage password security awareness in your workplace. Don't risk productivity downtime due to forgotten passwords – empower your team to reset their p
0 views • 13 slides
Evolution of Password Security in Modern Computing
Delve into the historical origins of passwords, their significance in cybersecurity, and the current methods employed to safeguard digital assets. Explore the challenges posed by fast computing systems and discover innovative solutions and tools like LastPass, Keeper, and Dashlane in the realm of pa
0 views • 15 slides
Enhancing Security with Windows Hello for Business
Windows Hello for Business provides a more secure non-password credential for Windows 10/11 devices, implementing 2FA/MFA to combat password-related vulnerabilities. This article explores the benefits, security measures, and implementation steps of Windows Hello for Business, addressing the challeng
8 views • 24 slides
OAuth Service for Issuing Certificates to Science Gateways
This project aims to provide an OAuth service for issuing certificates to Science Gateways for TeraGrid users Jim Basney and Jeff Gaynor from the University of Illinois. The effort is supported by the National Science Foundation to enhance security, independent gateway access, and better resource ut
0 views • 14 slides
Safely Logging Password-Derived Measurements for Web Login Systems
Design a secure measurement framework called Gossamer to assess risks associated with password-based measurements for web login systems. Explore ways to differentiate between benign and malicious traffic, and consider adding instrumentation to enhance security. Learn how attackers exploit password-d
0 views • 12 slides
Guide to Logging in and Setting Up Core-CT for the First Time
Accessing Core-CT for the first time involves using your State of Connecticut Employee ID and temporary password. Follow the steps to log in, set up a new password, and establish a forgotten password help feature. This guide provides clear instructions and visuals for each step.
0 views • 19 slides
Modern Solution for Enhanced Security - Face Lock Technology
Addressing common security issues faced by users, this project proposal introduces a cutting-edge fingerprint door lock system with face recognition technology. Offering multiple verification methods and user management levels, this innovative solution ensures a high level of security and convenienc
0 views • 16 slides
Best Practices for Securing Linux Systems
This resource covers essential security practices for Linux systems, including the CIA Triad (Confidentiality, Integrity, Availability), recommended partitions, encryption at rest and in transit, SSH and user login configurations, and password best practices. Learn about securing user directories, p
0 views • 27 slides
Mastering Strong Passwords: A Practical Guide
Understanding how passwords work is crucial for online security. Passwords act like combination locks, preventing unauthorized access to your accounts. Creating a strong password involves using random words and characters, as well as combining three random words for added security. Learn how to craf
0 views • 5 slides
Accessing NC Fast Subsidized Child Care Data in Data Warehouse
Learn how to log in and access NC Fast Subsidized Child Care data through the Data Warehouse portal. Access to the data warehouse requires a login and password, which can be obtained by contacting your LME or Institution Security Officer. The metadata available includes descriptions, table names, pr
0 views • 15 slides
Interactive Password Security Activity for Children
This presentation recaps the importance of strong passwords, techniques for creating them, and the significance of two-factor authentication. The lesson notes guide discussions on creating secure passwords using the "three random words" method and avoiding personal details. The interactive game "Gue
0 views • 4 slides
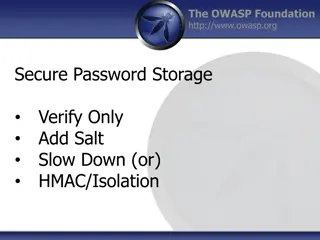
Best Practices for Secure Password Storage - OWASP Foundation Guidelines
Learn about secure password storage techniques recommended by OWASP Foundation, including adding salt, slowing down hashing functions, using HMAC isolation, and imposing difficult verification processes on attackers. Remember to use proper encoding, avoid limiting password types or lengths unreasona
0 views • 10 slides
Techniques and Tools for Offline Password Cracking
Explore the world of offline password cracking techniques using tools like John the Ripper. Learn about the motivation behind cracking user account passwords, gaining root privilege, and compromising vulnerable systems to obtain password hashes for further exploitation. Enhance your understanding of
0 views • 15 slides
Understanding Fine-Grained Password Policies in Active Directory
Explore the intricacies of Fine-Grained Password Policies (FGPP) in Active Directory, covering topics such as domain account policies, policy recovery methods, interpreting pwdProperties attribute, and implementing PSOs for granular password settings. Delve into the nuances of password complexity, h
0 views • 11 slides
Best Practices for Protecting Sensitive Data
Learn about password and credit card data security, storing passwords securely, data in transit vs. data at rest, and the importance of using salts to protect password hashes from offline attacks. Discover how to securely store passwords using encryption, hashing, and more to minimize exposure of se
0 views • 30 slides
Windows Security Overview and Best Practices
Windows operating system security overview focusing on preventing unauthorized access, privilege escalation, and password vulnerabilities. Includes countermeasures such as setting proper permissions, implementing strong passwords, and detecting vulnerabilities. Covering topics like remote password g
0 views • 6 slides
Enhancing Web Security with U2F Authentication
Explore the innovative FIDO U2F technology, a robust authentication solution for the web that addresses common password vulnerabilities. Learn how U2F works, its benefits for users, service providers, and device vendors, and its user-friendly implementation across various devices. Discover why U2F o
0 views • 18 slides
Enhancing WiFi Security and Password Protection for IoT Devices
Explore the importance of securing WiFi networks and IoT devices to mitigate privacy and security risks. Learn about encryption, hashing, salting, and ways to strengthen passwords to prevent unauthorized access. Discover common password attack methods and how to safeguard against them.
0 views • 13 slides
Understanding Password Security: Techniques and Best Practices
Delve into the world of password security with this comprehensive guide, covering topics such as password gathering, cracking strategies, tools, types of passwords, hashes, salting, better hashes, and hash identification. Learn how to enhance security measures and protect against malicious attacks.
0 views • 20 slides
Tools and Techniques for Extracting Password Hashes and Credentials from Windows Systems
Explore various tools and scripts such as ESEDBXTRACT, GPPPFinder, and PowerShell scripts for extracting password hashes and credentials from Windows systems, including NTDS.dit and SYSTEM files, Group Policy Preferences, and more. Learn how to handle different Windows versions and access encrypted
0 views • 19 slides
Comprehensive DevOps Security Training Overview
This Certified DevOps Security Practitioner course provides a deep dive into implementing DevSecOps, integrating security into the DevOps processes. Covering topics like security testing, Docker security, automation, and more, the training aims to equip participants with the necessary skills to embe
0 views • 5 slides
Protecting Password Identifiers in IEEE 802.11-21
This submission addresses the need for safeguarding password identifiers in SAE to ensure privacy and prevent attackers from constructing personally identifiable information. The document presents two potential solutions, ultimately recommending the use of symmetric cryptography for efficient protec
0 views • 11 slides
Best Practices for Password Security and User Authentication
Password security is crucial for protecting sensitive information. Passwords should not be shared and should be changed regularly to prevent unauthorized access. Implementing strong passwords, two-factor authentication, and biometric security measures can greatly enhance security. Additionally, main
0 views • 16 slides
Understanding Password-Protected Secret Sharing for Enhanced Data Security
Exploring the concept of password-protected secret sharing, this content delves into Shamir's Secret Sharing, ElGamal Public Key Encryption, and the importance of securing sensitive information with robust schemes. It highlights the challenges of offline attacks, properties of secret sharing, and th
0 views • 22 slides
Understanding Password Guessability Metrics in Real-World Security
Delve into the realm of password guessability metrics to enhance password security. Explore how measuring guessability aids in eliminating weak passwords, aiding users in creating stronger ones, and assessing security against various cracking algorithms. Uncover the significance of statistical and p
0 views • 27 slides
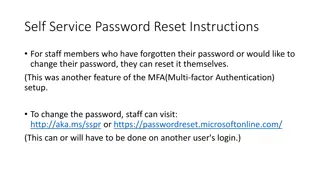
Self-Service Password Reset Instructions for Staff Members
Staff members can easily reset or change their password through self-service options using Multi-Factor Authentication. They can visit the provided links, verify their identity through email and phone number, and reset their password securely. Follow the step-by-step guide for a hassle-free password
0 views • 4 slides
Guide to Logging into Your Chromebook
This step-by-step guide provides instructions on how to log into your Chromebook using either your student ID and password or a QR code. Simply open the lid, press the power button, select "Next," and then proceed to log in with your credentials. For password login, enter your student ID and the def
0 views • 6 slides
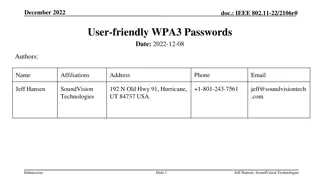
Enhancing Wi-Fi Security with User-Friendly WPA3 Passwords
Proposal to enhance Wi-Fi security by incorporating password and password identifier hashes in the SAE commit exchange, enabling devices to hint to access points which password will be used. This approach aims to improve network efficiency and user experience while addressing privacy concerns associ
0 views • 8 slides
Office 365 Email & Security Workshop Highlights
Office 365 Email & Security workshop was held with presenters Jason Hetterle, Steve Garcia, and Joseph Andreason covering topics like security awareness, self-service password reset, Office 365 webmail features, and more. The agenda included discussions on security measures, a case study on an anato
0 views • 9 slides