Computer Networks CMSC 417 : Spring 2022
Exploring the concepts of Classless Interdomain Routing (CIDR) and Dynamic Host Configuration Protocol (DHCP) in the context of internetworking. CIDR simplifies subnetting by allowing for classless addressing, hiding network hierarchies, and enabling supernetting. Lessons learned from subnetting inc
0 views • 57 slides
Modeling and Generation of Realistic Network Activity Using Non-Negative Matrix Factorization
The GHOST project focuses on the challenges of modeling, analyzing, and generating patterns of network activity. By utilizing Non-Negative Matrix Factorization (NMF), realistic network activity patterns can be created and injected into live wireless networks. Understanding and predicting user behavi
4 views • 28 slides
Network Function Abstraction A delicate question of (CPU) affinity?
Exploring the delicate balance of CPU affinity in network function abstraction, including challenges, benefits, and solutions like CPU pinning for network workloads. Learn about the impact on performance and scalability, as well as the importance of proper configuration in virtual and physical envir
3 views • 40 slides
WHONET Training Course: Laboratory Configuration and Setup
Understanding the laboratory configuration process in WHONET is crucial for effective data entry and analysis. This module guides users on setting up a new laboratory, entering country and lab details, defining antibiotics, sample locations, and data fields, creating microbiological alerts, and savi
3 views • 57 slides
Proposal for Location Configuration Information (LCI) in IEEE 802.11 Beacons and Probe Responses
This document proposes the inclusion of Location Configuration Information (LCI) data in a standard information element broadcast in Beacons and Probe Responses within IEEE 802.11 networks. By enhancing the accessibility of infrastructure location to non-AP STAs, this proposal aims to simplify locat
1 views • 5 slides
Revolutionizing Network Management with Intent-Based Networking
Explore the concept and benefits of Intent-Based Networking (IBN) in simplifying network configuration and enhancing efficiency. Learn how IBN automates network operations, aligns with business objectives, improves security, and ensures scalability and reliability. Discover the potential of IBN tool
0 views • 14 slides
R7 Network Slicing Model Proposal and Structure Overview
Explore the modeling requirements for R7 network slicing, focusing on slice subnet domain combinations within the NST model. The proposal delves into CST, NSST, slice profiles, NF configuration, and more to enhance the understanding of network slicing. Learn about the modeling structure, CST-DT rela
1 views • 23 slides
Network Compression Techniques: Overview and Practical Issues
Various network compression techniques such as network pruning, knowledge distillation, and parameter quantization are discussed in this content. The importance of pruning redundant weights and neurons in over-parameterized networks is highlighted. Practical issues like weight pruning and neuron pru
0 views • 37 slides
Introduction to Network Slicing in 5G Workshop
Explore the world of network slicing in the context of 5G technology through the Fall 2021 OpenAirInterface Workshop. Understand the concept of creating multiple logical networks on a shared physical infrastructure, with different slices catering to distinct user groups or services. Dive into the de
1 views • 6 slides
Network Slicing with OAI 5G CN Workshop Overview
Overview of Network Slicing with OAI 5G CN workshop focusing on the crucial role of network slicing in realizing the service-oriented 5G vision. This workshop covers topics like multiple logical networks creation on shared infrastructure, different types of network slices, preparation and instantiat
1 views • 6 slides
Enhancing EPS Authorization and Configuration Options in 5G Networks
The proposal focuses on enhancing authorization and configuration options in EPS using protocol configuration options. It discusses the attach procedure, ePCO checking, and the importance of ePCO support in the network architecture. The solution presented emphasizes the role of MME, SGW, and PGW-C+S
0 views • 8 slides
Personal IoT Network (PIN) Terminology Discussion for 3GPP TSG-SA WG1 Meeting
In this discussion, the concept of Personal IoT Network (PIN) and its elements are explored, including the roles of PIN Elements, Configuration PIN Capability, and Gateway Capability. The necessity of gateways to the 3GPP network, device examples, and the distinction of licensed spectrum are also ad
2 views • 10 slides
Understanding 5G RAN Network Slicing and Architecture
Explore the intricate world of 5G Radio Access Network (RAN) and Network Slicing, delving into concepts such as SO Service Orchestrator, SDN-C Service Design, and Core Network Elements. Discover the significance of managing and designing mobile slice services, including eMBB, Massive IoT, and Missio
0 views • 26 slides
Understanding Snort: An Open-Source Network Intrusion Detection System
Snort is an open-source Network Intrusion Detection System (NIDS) developed by Cisco, capable of analyzing network packets to identify suspicious activities. It can function as a packet sniffer, packet logger, or a full-fledged intrusion prevention system. By monitoring and matching network activity
0 views • 23 slides
5G Use Case Proposal for Dublin Ericsson
This proposal outlines the use of NETCONF for configuration management in 5G networks, focusing on Dublin. It covers topics like Configuration with NETCONF, NETCONF Overview, NETCONF Security, YANG Overview, and Proposed Use Cases and Requirements for Dublin. The proposal emphasizes the importance o
7 views • 20 slides
Understanding Devices and Network Security Implementation
This content discusses the installation and configuration of network components to enhance organizational security. It covers topics such as intrusion detection systems (IDS), different types of IDS approaches, passive and active responses to intrusions, and using hubs to attach network-based IDS. T
0 views • 13 slides
Understanding Native VLAN 1 in Mesh Ethernet Bridging
Mesh Ethernet bridging utilizes native VLAN 1 for the initial configuration, ensuring the RAP connects to the native VLAN ID 1 on a switch. This setup affects the communication between the RAP and the Map devices, as well as their connection to the controller. Misconfigurations related to VLAN taggi
0 views • 9 slides
Configuration Examples for IP SLA with Object Tracking
Learn how to configure and troubleshoot IP SLA with Object Tracking using detailed examples for Static Routing, HSRP, and Policy Based Routing. Find out where Object Tracking can be implemented and when not to use it in various network scenarios. Understand the configuration components, including de
2 views • 17 slides
Understanding Static Routing in Network Infrastructure Workshops
Explore the concepts of static routing in networking workshops, covering Unix and Cisco network interface configurations, static routes, default routes, and advantages and disadvantages of static routing. Learn about IP routing configuration, assignment of IPv4 addresses, and FreeBSD network interfa
4 views • 37 slides
Transportation Network Modeling and Analysis with C.Coupled SE Platform
This content outlines the features and functionalities of the C.Coupled SE Platform (CSET Platform) developed by the Connetics Transportation Group. It covers aspects such as interface design, inputs merging, purposes, platform development using Cube, TAZs merging, and network attributes. The platfo
0 views • 11 slides
Evolution of Configuration Management in Software Engineering
Explore the evolution of configuration management in software engineering, highlighting key practices like cloud-based IDE, shared repositories, and unobtrusive configuration management. Understand the importance of modern best practices in software development, traditional vs. optimistic approaches
0 views • 20 slides
Understanding BGP Protocol and Configuration for Routing Policy Filtering
Explore the terminology, reasons, and methods behind routing policy filtering in the context of BGP protocol configuration. Learn how to control traffic routing preferences, filter routes based on AS or prefix, and use regular expressions for complex filtering rules. Discover the importance of AS-Pa
0 views • 29 slides
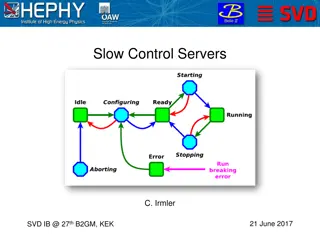
Slow Control Servers and Network Configuration for SVD Management
The documentation discusses the setup and requirements for slow control servers, network configuration, FADC server status, ENV server status, and general SC server status for SVD management. It outlines the need for backup servers, minimum server requirements, server specifications, procurement det
0 views • 11 slides
LArDPS to eFEX Test Configuration for FOX Demonstrator
Configuration details and diagrams for testing the direct path from the LArDPS to eFEX in the FOX Demonstrator, including optical insertion loss measurements, offset calibration using different setups, and diagrams without splitters. The setup matches the planned configuration for the test.
0 views • 34 slides
Meridian: An SDN Platform for Cloud Network Services
Meridian is an SDN platform developed by Mohammad Banikazemi, David Olshefski, Anees Shaikh, John Tracey, and GuohuiWang at IBM T. J. Watson Research Center. The platform focuses on providing cloud network services efficiently. It encompasses an architecture that enables faster and more convenient n
0 views • 21 slides
Updates on iKAGRA Installation and Configuration Changes
The report discusses changes in the iKAGRA configuration from Fabry-Perot Michelson Interferometer to Michelson Interferometer due to schedule constraints and budget limitations. The document outlines the revised schedule for installation tasks, shift applications, and the impact on the KAGRA projec
0 views • 16 slides
Android Network Access Configuration Guide for Eduroam Network
Learn how to configure Android devices for network access on the Eduroam network. Follow step-by-step instructions to connect your device seamlessly. From accessing Wi-Fi settings to logging in with your university email, this guide ensures a smooth setup process. Complete with visuals for each step
0 views • 6 slides
Specific Parameters for DL Interruptions in 5G Network Testing
Detailed discussion and guidelines for verifying symbol-level DL interruptions in 5G network testing scenarios such as switching between LTE and NR carriers, inter-band ENDC TDD configuration, and FDD-TDD CA (SA) TDD configuration. The document covers specific parameters, test options, and symbol ve
0 views • 6 slides
Understanding Network Analysis: Whole Networks vs. Ego Networks
Explore the differences between Whole Networks and Ego Networks in social network analysis. Whole Networks provide comprehensive information about all nodes and links, enabling the computation of network-level statistics. On the other hand, Ego Networks focus on a sample of nodes, limiting the abili
0 views • 31 slides
Insights into Operating Experience and Configuration Management in Nuclear Power Plants
Explore the significance of Operating Experience (OE) in refining machine and human performance, reinforcing desired behaviors, solving problems timely, and sharing industry-wide knowledge in nuclear power. Learn from examples highlighting the importance of configuration management in mature nuclear
0 views • 11 slides
Advanced Neutronics Parameters for Fusion Chamber Configuration with Magnetic Intervention
Detailed analysis and design considerations for a fusion chamber configuration utilizing magnetic intervention to optimize neutronics parameters. The discussion includes blanket configuration, neutron wall loading distribution, blanket design options, nuclear design requirements, and dimensions meet
0 views • 12 slides
Recap of eZeeKonfigurator Notice Configuration and Zeek Week Oct 2019
A summary of events involving a talk at Zeek Week, issues with notice configuration, experiences with Zeek/Bro, and the introduction of eZeeKonfigurator for configuring Zeek clusters. The content includes descriptions of individuals involved, challenges faced, support for cluster configurations, and
0 views • 20 slides
Network Function Virtualization (NFV) Overview
Network Function Virtualization (NFV) focuses on virtualizing network functions to improve efficiency and reduce costs in network infrastructure. The lecture discusses key readings, devices that compose a network, specialization of devices, benefits of one-device-does-anything approach, and the goal
0 views • 21 slides
Enhancing Network Stability with Network Monitoring Systems
Network monitoring is crucial for efficient management and proactive issue detection in a network environment. Factors influencing an effective network system include choosing the best OEM, SLA agreements, and selecting a reliable System Integrator. Reactive monitoring can lead to financial losses a
0 views • 12 slides
Efficient Skyline Batch Workflow Tool for Processing Multiple Files
Utilize Skyline Batch, a user-friendly tool developed by Ali Marsh, to run simple Skyline workflows on multiple files efficiently. This tool is ideal for overnight processing, reprocessing data easily, and sharing workflows across different computers. Quickly transform Skyline templates into report
0 views • 4 slides
Comprehensive Guide to Nexus vPC: Definitions, Benefits, Terminology, Operation, Consistency Check, Configuration
This comprehensive guide covers everything you need to know about Nexus vPC (Virtual Port Channel) including definitions, benefits, terminology, operation, consistency checks, and detailed configuration steps. Explore the virtual port channel concept and its impact on network topology, spanning tree
0 views • 12 slides
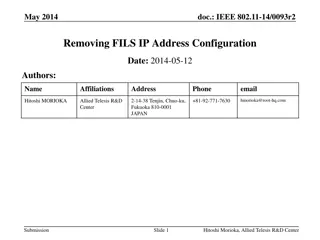
Removal of FILS IP Address Configuration in IEEE 802.11-14/0093r2
This document details the rationale behind the proposal to remove FILS IP Address Configuration in IEEE 802.11-14/0093r2. The author, Hitoshi Morioka, explains that the need for this configuration is redundant due to the HLP encapsulation's ability to support all required functions. By eliminating c
0 views • 18 slides
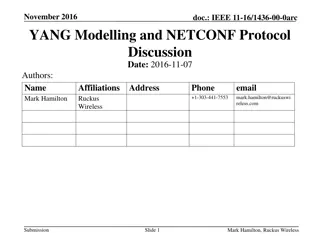
Introduction to YANG Modelling and NETCONF Protocol
This presentation from November 2016 provides a brief introduction to YANG modelling and the NETCONF protocol for managing system configuration. It discusses the purpose and benefits of YANG, highlighting its role as a data modeling language for the NETCONF protocol and detailing its features such a
0 views • 6 slides
Accelerating Systemic Change Network Inaugural Workshop Summary
The Accelerating Systemic Change Network held its inaugural workshop at Howard Hughes Medical Institute in July 2016 to address the lack of coordination in improving higher education. With a vision to become a professional hub for change researchers in STEM education, the network aims to enhance ind
0 views • 5 slides
University Network Section Overview July 2015 - March 2016
The presentation covers the network team structure, team members, objectives, goals, report outline, network statistics, accomplishments, and future plans of the university network section from July 2015 to March 2016. It highlights efforts to provide stable internet and intranet services, restructu
0 views • 16 slides