Understanding IRB Review Process for Expedited Research
Learn about the significance of IRB review, levels of review, and categories of expedited review. Discover the criteria for IRB review, including whether the study involves human subjects and contributes to generalizable knowledge. Explore the different levels of IRB review and the specific categori
3 views • 11 slides
Institutional Review Board Application Process
The basics of the IRB, researcher responsibilities, IRB members, and the role of faculty advisors and student investigators in navigating the IRB application process. Understand the importance of ancillary approvals for research projects involving human subjects.
1 views • 19 slides
Understanding IRB Review Process for Research Studies
The content provides an overview of the IRB review process for research studies, including what necessitates IRB review, the levels of IRB review (exempt, expedited, full board), examples of full board research, and criteria for an Investigational New Drug.
1 views • 17 slides
Enhancing Security with Two-Factor Authentication in Funding & Tenders Portal
Increase in cybersecurity threats necessitates the use of two-factor authentication in the Funding & Tenders Portal to safeguard valuable information. Users are encouraged to adopt this secure login method, which will soon become mandatory. Methods such as mobile devices, SMS, and security keys are
1 views • 31 slides
Understanding Responsible Conduct of Research and IRB Overview
Delve into the world of research ethics through an overview of Institutional Review Boards (IRB), regulations governing human subjects research, historical events shaping research ethics, and examples of research controversies. Explore key ethical principles and the role of the IRB in protecting res
3 views • 34 slides
Understanding IRB Review Levels and Exempt Determinations
Explore the levels of IRB review for human participant research, including Exempt, Expedited, and Full Board reviews. Learn about the categories of Exempt Determinations and the criteria for Limited IRB Review. Understand if your study requires IRB review based on research and human subject involvem
1 views • 12 slides
First-Time Researcher's Guide: Navigating the IRB Submission Process at Barry University IRB January 2023
Providing essential guidance for first-time researchers submitting to the Barry University IRB in January 2023. Covers initial steps such as creating an IRBNet account, completing ethics training, determining the review category, and selecting the appropriate protocol form.
0 views • 40 slides
Understanding IRB Reliance Agreements in Research
IRB reliance agreements allow institutions to delegate IRB review responsibilities or collaborate with other institutions for human subjects research. Federalwide assurance (FWA) documents ensure compliance with regulations. Different types of agreements, such as IRB authorization agreements and ind
0 views • 23 slides
Guide to Setting Up EU Login and Two-Factor Authentication
Learn how to create your EU Login account and add two-factor authentication for accessing Europass and other EU services. Follow step-by-step instructions to register, verify your email, and set up a secure password. Ensure a seamless process by understanding the difference between Europass and EU L
3 views • 18 slides
Two-Step Authentication Implementation for Enhanced Security
Learn about the implementation of two-step authentication at a university to combat phishing attacks and enhance security. Discover how Duo Security was used to provide a seamless two-step authentication solution, the challenges faced during the enrollment tool setup, and the successful implementati
0 views • 10 slides
Pathology Department IRB Protocol for Electronic Medical Records Screening
Pathology Department's IRB protocol enables the screening of electronic medical records for research purposes, allowing members to review patient records and pathology slides. By fulfilling specific requirements and obtaining blanket IRB approval, researchers can access and analyze patient data for
0 views • 16 slides
Guidelines for GPS IRB Application Process at Pepperdine University
The GPS IRB at Pepperdine University focuses on protecting the rights and welfare of human research subjects. Applications cover social, behavioral, and educational research, following federal regulations. IRB approval is required before starting any research activities, and different application ty
0 views • 12 slides
Implementing 2FA for UW Azure AD: Best Practices and Options
Explore the implementation of two-factor authentication (2FA) for UW Azure Active Directory (AD) based on key decisions and options outlined in the provided slides. Understand the strategies for enforcing MFA, handling legacy authentication, and transitioning to cloud-based authentication. Discover
0 views • 19 slides
Security and Authentication in Electronic Filing Systems: Arkansas Subcommittee Report
Explore the subcommittee report on security and authentication in electronic filing systems for campaign and finance reports in Arkansas. Learn about user authentication, risks, mitigation strategies, and approaches used in other states. Discover the filing processes in both paper and electronic for
0 views • 24 slides
Understanding the IRB Application Process Overview
This comprehensive overview delves into the IRB application process, covering topics such as human research protections, IRB oversight requirements, different types of reviews, informed consent, response to IRB correspondence, common errors, and the significance of ethics in research. Key historical
0 views • 27 slides
Understanding Institutional Review Board (IRB) Process
Institutional Review Board (IRB) plays a crucial role in ensuring research involving human subjects adheres to ethical standards. This summary provides insights into the IRB process, including determining the need for IRB review, defining human subjects research, and the importance of human subjects
0 views • 20 slides
Institutional Review Board (IRB) and Quality Assurance Overview
Institutional Review Board (IRB) plays a crucial role in protecting the rights and welfare of research participants, ensuring the validity, ethics, and compliance of human research. This content covers the functions of IRB as a Privacy Board, distinguishes Downstate and non-Downstate workforce inves
0 views • 27 slides
Streamlined IRB Application Process Guidelines
Enhance your understanding of the IRB application process with helpful resources, step-by-step instructions, and access to training modules. From CITI certification to Cayuse navigation, this comprehensive guide aims to simplify the protocol submission journey for researchers. Explore hints, example
4 views • 11 slides
Navigating the Institutional Review Board (IRB) Process: A Practical Guide
Understanding the IRB process is crucial for conducting ethical research involving human subjects. This guide outlines federal regulations, protective mechanisms, IRB goals, and the definition of human subjects in research. It also provides insights into the level of intervention, considerations whe
1 views • 26 slides
Guidance on Single IRB (sIRB) Consultation for Multi-Institutional Studies
This resource provides detailed guidance on the requirements and processes for consulting with the Human Subjects Division (HSD) for single Institutional Review Board (IRB) studies involving multiple institutions, federally-funded research, and new NIH funding. It includes information on when a sIRB
0 views • 6 slides
DAVA Drugs Authentication & Verification Application by National Informatics Centre
The DAVA Drugs Authentication & Verification Application, developed by the National Informatics Centre of the Government of India, enables authentication, tracking, and tracing of Indian drugs at different packaging levels. Manufacturers maintain Unique Serial Numbers for primary and secondary packa
2 views • 42 slides
Setting Up Two-Factor Authentication for HRMS Access
Learn how to enhance HR system security by setting up two-factor authentication for off-campus access. This tutorial covers the importance of two-factor authentication, using your phone as a second layer of security, initial setup procedures through Wyoweb, requesting permission for HR self-service
0 views • 9 slides
Navigating IRB Submission Forms & Resources with Dr. Kelly Quesnelle
Explore the essential criteria for human subjects research, the process of applying to the IRB for determinations, understanding regulated research, and common errors in exemption submissions. Delve into expedited vs. full board reviews and different categories of research review, in this detailed g
0 views • 52 slides
Enhancing VHA Policy for Effective IRB and R&D Functions
Explore the potential VHA policy changes that can streamline IRB and R&D committee responsibilities to better serve veterans while upholding the VA's mission. Delve into questions concerning beneficial and challenging policy changes, the need for a single R&D committee model, and considerations on t
0 views • 6 slides
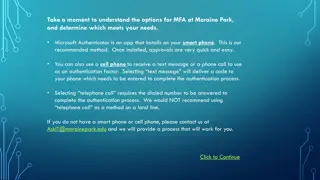
Setting Up Multi-Factor Authentication at Moraine Park
Explore the options for setting up Multi-Factor Authentication (MFA) at Moraine Park, with Microsoft Authenticator as the recommended method. You can choose between using the Microsoft Authenticator app on a smartphone, receiving a text message, or a phone call for authentication. Detailed steps for
1 views • 16 slides
Understanding Authentication Mechanisms and Security Vulnerabilities
Authentication lies at the core of application security, serving as the primary defense against malicious attacks. This article explores various authentication technologies, including HTML forms-based authentication, multi-factor mechanisms, client SSL certificates, and more. It delves into common d
0 views • 70 slides
An Open-Source SPDM Implementation for Secure Device Communication
This article introduces an open-source SPDM (Secure Protocol and Data Model) implementation for secure device communication, developed by Jiewen Yao and Xiaoyu Ruan, Principal Engineers at Intel. SPDM aims to enhance device security through protocols for device authentication, session key establishm
0 views • 29 slides
Authentication and Authorization in Astronomy: A Deep Dive into ASTERICS
Explore the world of authentication and authorization in the field of astronomy through the lens of the ASTERICS project. Learn about the importance of verifying identities and granting access rights, the Virtual Observatory Approach, Single Sign-On standards, and Credential Delegation protocols. Di
0 views • 9 slides
Evolution of User Authentication Practices: Moving Beyond IP Filtering
The article explores the obsolescence of IP filtering in user authentication, highlighting the challenges posed by evolving technology and the limitations of IP-based authentication methods. It discusses the shift towards improving user experience and addressing security concerns by focusing on user
0 views • 22 slides
Guideline for Submitting a New IRB Protocol
This tutorial provides step-by-step instructions for submitting a new IRB protocol in Cayuse IRB. It covers essential preparatory steps, authentication requirements, logging in to Cayuse, navigating the platform, and initiating a new study application. Helpful tips are included for Primary Investiga
0 views • 24 slides
Understanding Saint Leo IRB Process
Discover the Saint Leo IRB review process, its purpose, requirements for research approval, definitions of human subjects and research, and how to apply for IRB approval. Learn about the exclusion criteria for class activities and access useful resources and guidance for conducting research at Saint
0 views • 17 slides
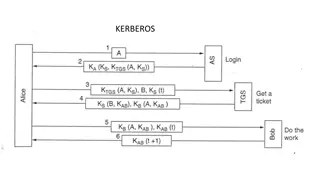
Understanding Kerberos Authentication in Network Security
Kerberos is a trusted authentication service for establishing secure communication between clients and servers in a distributed environment. Developed at MIT, it addresses threats like user impersonation and eavesdropping by providing centralized authentication. Kerberos relies on symmetric encrypti
0 views • 13 slides
Understanding Kerberos Authentication Protocol
Kerberos is a secure authentication protocol developed at M.I.T. to allow workstation users to access network resources securely. It involves three servers: Authentication Server (AS), Ticket-Granting Server (TGS), and the server performing the requested tasks. The AS verifies users, TGS issues tick
0 views • 12 slides
Understanding IRB Reliance: Roles and Responsibilities
This content delves into the roles and responsibilities involved when relying on an external IRB, covering regulatory requirements, the reliance request process, why local context review is essential, and more. It discusses NIH policies, the use of a single IRB for multi-site research, exceptions to
0 views • 40 slides
Understanding the IRB Review Process: A Comprehensive Overview by Dr. Kathryn Greene
Delve into the essential aspects of the IRB review process with Dr. Kathryn Greene, a professor and IRB board member. Explore the historical context, regulations, significance, and procedures involved in navigating the IRB review process. Gain insights into the importance of IRB in protecting human
0 views • 27 slides
Secure Authentication Using ISO 15693 RFID Tags
The authentication process with ISO 15693 tags involves generating a signature using a hash of the tag UID and a private key. This signature, programmed during manufacturing, must match with the one generated by the reader for successful authentication. Advantages include enhanced security with priv
0 views • 7 slides
Understanding Authentication and Authorization in Information Assurance
Explore the concepts of authentication and authorization in information assurance through a series of visuals and explanations provided by Adam Doup from Arizona State University. Learn about authentication terms, mechanisms, password systems, and UNIX standard hash functions. Gain insights into how
0 views • 26 slides
Introduction to Institutional Review Board (IRB): Overview and Application Process
This detailed content provides an introduction and overview of the Institutional Review Board (IRB), covering its history, purpose, application process, and available resources. The IRB ensures that research involving humans adheres to ethical principles and regulatory requirements to protect partic
0 views • 4 slides
Understanding Authentication and Message Authentication in Network Security
Authentication is crucial in establishing identity in the digital world to access rights, products, and services. It involves validating credentials to prove identity and ensure security. Message authentication confirms the integrity and origin of transmitted data, preventing alteration or unauthori
0 views • 24 slides
Understanding Authentication in Networking Environments
Authentication is a crucial process in computer networks where clients prove their identity to servers. This article covers the concept of authentication, its importance, and specific guidance on network authentication, particularly focusing on Windows and Linux VMs. Key topics include the use of pa
0 views • 30 slides