Exploring micro:bit - The Next Gen Technocamps Partnership
Discover the collaboration between Technocamps and the micro:bit Foundation in Wales, bringing the new phase of micro:bit projects to students. Dive into what micro:bit can do, explore coding with Makecode, engage in fun activities like Emotion Badge coding, and learn how to use button events to con
0 views • 30 slides
Understanding 4-Bit Parallel Adder/Subtractor IC7483
Explore the concept of 4-bit parallel adder/subtractor using IC7483, which is a digital circuit capable of performing arithmetic operations on binary numbers greater than one bit in length. Learn about the structure, operation, and implementation of parallel adders with cascaded full adders. Discove
6 views • 11 slides
Discrete Mathematics
Explore the foundations of logic and proofs in discrete mathematics, focusing on compound propositions, bit operations, and applications of propositional logic. Learn about how computers use bits for information representation and manipulation, and delve into translating English sentences into logic
5 views • 15 slides
Daily current affairs 2024(presentation)
\u25ba Check this page for wide range of online courses: http:\/\/bit.ly\/kd-courses\n\nDo you want to get a Government job online course? Here are best govt job preparation courses :\n\n\ud83d\udc49 SSC Courses - \/\/bit.ly\/3Ft9FrY\n\n\ud83d\udc49 UPSC Courses - \/\/bit.ly\/3Diszjr\n\n\ud83d\udc49
2 views • 22 slides
SSC CHSL CPO 2024 (presentation)
\u25ba Check this page for wide range of online courses: http:\/\/bit.ly\/kd-courses\n\nDo you want to get a Government job online course? Here are best govt job preparation courses :\n\n\ud83d\udc49 SSC Courses - \/\/bit.ly\/3Ft9FrY\n\n\ud83d\udc49 UPSC Courses - \/\/bit.ly\/3Diszjr\n\n\ud83d\udc49
1 views • 9 slides
Why Simplified Data Manipulation is the Future of BI Dashboard Software
Discover why simplified data manipulation is revolutionizing BI dashboard software. As businesses strive for real-time insights and data-driven decisions, the need for intuitive and efficient BI tools becomes paramount.
1 views • 6 slides
Simplified Data Manipulation and Cleaning Without Coding
To fully experience and leverage the potential of your data, complex coding is not always the best bet. Business users and analysts can increase their productivity by leaving everyday challenges at bay. Our latest blog explores how no-code Business Intelligence tools are revolutionizing data manipul
3 views • 6 slides
Understanding Character Sets in Computer Science
Alphanumeric characters, special symbols, and control characters play crucial roles in representing data through character sets like ASCII and Unicode in computer science. ASCII, with its 7-bit binary codes, represents 128 characters, while Extended ASCII allows for 256 characters. Unicode covers a
1 views • 12 slides
Create a Flood Warning System with Micro:bit and Moisture Sensor
A design brief for constructing a flood warning system using micro:bit to detect rising water levels and alert homeowners, aiming to mitigate damage caused by flooding. The project involves selecting suitable input sensors, such as a moisture sensor, and programming the micro:bit to trigger a warnin
3 views • 9 slides
Evolution of Microprocessors: A Historical Overview
The history of microprocessors traces back to Fairchild Semiconductors in 1959, leading to the founding of Intel in 1968. The evolution from 4-bit to 64-bit microprocessors by Intel revolutionized computing. Key milestones include the Intel 4004 and 4040 (4-bit), 8008, 8080, and 8085 (8-bit), and th
2 views • 44 slides
Memory Design Overview: SRAM Cell and Bit Slice Organization
This content provides an overview of SRAM (Static Random Access Memory) cell and bit slice organization, explaining the design elements such as SRAM cell augment, D latch tristated output, multiple enable signals, row and bit selection, data input and output, addressing, and memory expansion with mu
0 views • 25 slides
IEEE 802.11-19/0468r0 RSTA Requires ISTA-to-RSTA LMR Bit
This document proposes adding a bit in the Extended Capabilities element to indicate if ISTA needs information from RSTA for 11az negotiation initiation. It suggests RSTA advertise its expectation for ISTA to share the Location Measurement Report. By setting the RSTA requires ISTA-to-RSTA LMR bit, R
2 views • 11 slides
The Life and Personality of Two-Bit Matthews in "The Outsiders
Two-Bit Matthews, a key character in "The Outsiders," is described as the wisecracker of the gang with a humorous and loyal personality. Standing at six feet tall, with gray eyes and a wide grin, he is known for his optimistic nature, love for jokes, and loyalty to his Greaser friends. Despite his s
0 views • 5 slides
Genetic Manipulation in Environmental Biotechnology
Genetic manipulation strategies in environmental biotechnology involve techniques like gene splicing and molecular cloning to modify genes directly. These methods have various applications such as isolating genes, producing specific molecules, improving biochemical production, creating organisms wit
0 views • 20 slides
Micro:bit Robot Entry Tutorial - Lesson on Tracking with YahBoom
Explore the world of robotics with this comprehensive tutorial series focused on tracking using YahBoom in micro:bit. Learn about black line tracking, infrared sensor principles, hardware setup, and block programming to enhance your robotics skills. Follow step-by-step instructions to create a fun a
0 views • 12 slides
Understanding Ethical Considerations in Manipulated Photography for Media
Ethical control in photojournalism involves capturing non-fiction events without manipulation, but some control over the image is acceptable within ethical bounds. However, moving into manipulated images for non-news events requires a different approach, involving subject and scene manipulation for
0 views • 28 slides
Micro:bit Robot Entry Tutorial with YahBoom - Buzzer Singing Lesson
In this engaging tutorial series, you will learn how to program a micro:bit robot to sing "Happy Birthday" using a buzzer. Follow step-by-step instructions to set up your micro:bit, connect it to your computer, search for coding blocks, and combine them to create a musical robot. Powered by YahBoom,
2 views • 8 slides
How Advanced Algorithms Are Reshaping Data Manipulation
Explore the transformative impact of advanced algorithms on data manipulation in our latest feature. This insightful exploration delves into the sophisticated technologies revolutionizing business analytics and understanding what is data manipulation
0 views • 7 slides
Basin Manipulation Simulation Analysis Tool Overview
Basin Manipulation Simulation Analysis Tool provides a comprehensive solution for managing and analyzing basin data, including tasks like basin manipulation, simulation analysis, case management, and defining simulation time steps. The tool allows for easy data entry, visualization of simulation res
2 views • 17 slides
Improved Encryption Technique for Phase Change Memory (PCM)
Bit flips in Phase Change Memory (PCM) can adversely impact performance, power consumption, and system lifespan. To address this, a write-efficient encryption scheme called DEUCE was developed, which reduced bit flips by 50% and improved speed by 27%. By re-encrypting only modified data, the scheme
0 views • 41 slides
Analysis of Lady Macbeth's Manipulation in Shakespeare's Macbeth
In a pivotal moment in Macbeth, Lady Macbeth's manipulation of her husband is showcased when she calls upon supernatural forces to overcome his kindness and convince him to kill Duncan. This extract is crucial in introducing Lady Macbeth's character and power dynamics within the play, particularly h
0 views • 49 slides
Micro:bit Quiz Counter Prototype Development
Developing a score counter prototype using micro:bit for quiz participants. The product aims to accurately track and display team scores, catering to young adults with a durable and portable design. Pre-written programs in JavaScript and Python editors are provided for easy implementation on BBC mic
0 views • 5 slides
Developing an Automatic Lighting System with micro:bit
Explore how to save lighting energy with the micro:bit by developing a programmable system for automatic lighting in homes. The project involves using sensors to detect motion, LED lights for illumination, and programming the micro:bit to control the lighting based on occupancy in the room. Get hand
0 views • 8 slides
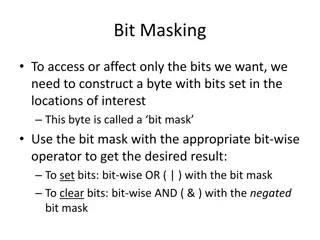
Understanding Bit Masking and Bitwise Operations for Efficient Bit Manipulation
Bit masking is a powerful technique in programming to selectively access or modify specific bits without affecting others. By creating a byte with bits set at desired positions using a bit mask, bitwise operators like OR (|) and AND (&) can be leveraged to efficiently set or clear specific bits. Thi
0 views • 11 slides
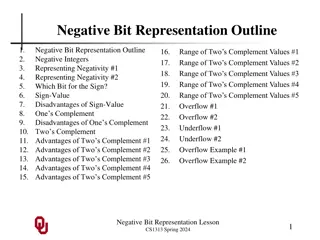
Understanding Negative Bit Representation in Computer Science
Dive into the world of negative bit representation in computer science, exploring the need for representing negativity in integers, methods like Two's Complement, disadvantages of Sign-Value and One's Complement, range of Two's Complement values, overflow, underflow, and more. Discover the significa
0 views • 26 slides
Storage and Manipulation of Liquefied Gases with Dewars and Cryostats
Storage and manipulation of liquefied gases involve using specialized equipment like Dewars and Cryostats to minimize heat transfer and maintain low temperatures. Dewars, invented by James Dewar, are double-walled vacuum vessels designed to store liquefied gases with minimal losses. The use of vacuu
0 views • 11 slides
Understanding Carry Bit Calculation in Digital Systems
Explore the concepts of carry bit calculation in digital systems through re-examination of addition operations, generating carries, propagating carries, and scenarios where Cout must be zero. Discover how different combinations of Ak and Bk values influence the carry bit and learn about situations w
0 views • 12 slides
Understanding Direct Manipulation in HCI
In this lecture, learn about the concept of direct manipulation in Human-Computer Interaction (HCI), including its benefits, drawbacks, and related terms such as engagement, distance, semantic, and articulatory distances. Explore the evolution of GUIs and interaction styles, and compare edge maps an
0 views • 24 slides
Understanding Non-Optimal Routing and 32-Bit ASN Compatibility
Explore the challenges caused by the incompatibility of 32-bit ASN with old router software, leading to non-optimal routing issues. Learn about Autonomous Systems, AS Numbers, BGP asymmetric routing, and the importance of routing software supporting 32-bit ASN. Discover how outdated software replace
0 views • 8 slides
Micro:bit Robot Entry Tutorial - Advanced Lesson on Breathing Lamp with YahBoom (80 characters)
In this tutorial, learn how to create an advanced breathing lamp effect using a micro:bit robot with YahBoom. Follow the steps to program the colorful lights on the dot matrix, change colors of the seven-color lamp, and connect the micro:bit to a computer for programming. This comprehensive guide in
0 views • 13 slides
Understanding MIPS Arithmetic Logic Unit (ALU)
The MIPS ALU is the heart of computer calculations, performing functions like add, and, or, and sub. This article delves into designing a full ALU, starting from a 1-bit full adder to a 32-bit ALU. It explores how operations like and, or, and addition are carried out within the ALU, and how to imple
0 views • 28 slides
Understanding Narcissistic Abuse: The Insidious Manipulation of Victims
Narcissistic abuse is a form of severe psychological and emotional manipulation that targets a victim's spirit and identity. The abuser employs tactics such as lying, manipulation, denial of reality, and control. This abuse is often invisible and devastating, characterized by a lack of empathy and a
0 views • 15 slides
Emerging Variable Precision Formats in Compiler Flow
Many applications rely on floating point numbers, but deciding on the right precision is crucial to avoid performance and energy waste. This work explores the impact of precision choices, including overkill and insufficient precision, on applications such as CNNs and GPU algorithms. It introduces a
0 views • 25 slides
Privacy Address Requirements for Wireless Personal Area Networks
This document discusses the privacy address requirements for IEEE P802.15 Working Group's TG4ab standard for Wireless Personal Area Networks (WPANs). It covers the need for 48-bit addresses with collision resistance, the use of different privacy addresses for each frame, and the adequacy of 12-bit c
0 views • 8 slides
Creating a Musical Instrument Using BBC Micro:bit
Design and program a device using the BBC Micro:bit to be used as a musical instrument in a class performance. The project involves creating different parts of a piece of music such as rhythm, harmony, and melody, and includes criteria for the device's functionalities like producing drumbeats, playi
0 views • 14 slides
Micro:bit Robot Ultrasonic Obstacle Avoidance Tutorial
Learn how to set up and program a micro:bit robot for ultrasonic obstacle avoidance. Follow the step-by-step guide to prepare hardware, connect the micro:bit to the computer, search for programming blocks, and test the ultrasonic sensor. Children can understand the concepts and experiment with obsta
0 views • 10 slides
Ethical Analysis of Manipulation in Organ Allocation System
This resource tackles the issue of manipulation in organ transplant waitlist priority through unnecessary medical interventions. It highlights the ethical concerns, potential harms, and ways to mitigate this manipulation, urging adherence to systemic safeguards and ethical clinical practice.
0 views • 9 slides
Programming the micro:bit Robot Buggy for Maze Navigation
In this project, teams work together to program a micro:bit-powered robot buggy to successfully navigate a maze layout. The program development involves testing at different intervals before the final attempt. Participants need to meet the design brief and criteria by programming the BBC micro:bit u
0 views • 5 slides
Innovative Multicellular Computing Circuits for Genetic Manipulation
Cells are utilized as computational devices in a innovative approach for genetic manipulation. Various logic gates and promoters are combined to achieve complex circuit behavior without the need for genetic manipulation. Advantages include a wide dynamic range and low variability, but with the drawb
0 views • 10 slides
Illustrated Design of a Simplified CPU with 16-bit RAM
Demonstrates the design of a basic CPU with 11 instructions and 4096 16-bit RAM, showcasing the assembly of a general-purpose computer using gates and registers. The CPU comprises 8 key registers for various functions, employing a sequential circuit for instruction execution. The machine language pr
0 views • 31 slides