Protection Analysis using the PAF
In this session, participants will learn how to utilize the Protection Analysis Framework (PAF) and its tools to conduct effective protection analysis. The session covers an overview of PAF, understanding its pillars, and analyzing data to comprehend essential protection concepts. Key points include
5 views • 48 slides
The Digital Personal Data Protection Act 2023
The Digital Personal Data Protection Act of 2023 aims to regulate the processing of digital personal data while balancing individuals' right to data protection and lawful data processing. It covers various aspects such as obligations of data fiduciaries, rights of data principals, and the establishm
3 views • 28 slides
Active Directory Self Service Password Reset Tool, cionsystems
It provides the feature of delegated web access administration, self-registration, self-service and password management. \/\/rb.gy\/1tjfv5
2 views • 2 slides
Digital Wellness and Password Security Lesson for Students
This lesson focuses on promoting digital wellness and teaching students about password security. It covers topics such as creating strong passwords, safeguarding personal information, and the importance of balancing online and offline interactions. Through activities and discussions, students learn
0 views • 13 slides
Governance and Managerial Leadership of Formal Social Protection in Africa: Insights from Cameroon's National Social Insurance Fund (CNPS)
This presentation delves into the governance and managerial leadership of formal social protection in Africa, focusing on Cameroon's CNPS system. It discusses the institutional evolution of social protection, the challenges faced by bureaucratic and political stakeholders, and the roles of various s
0 views • 8 slides
Unlocking Solutions: Addressing QuickBooks Company File Incorrect Password Issue
Unlocking Solutions: Addressing QuickBooks Company File Incorrect Password Issues\nQuickBooks, a vital tool for businesses, can encounter password-related hurdles, disrupting workflow. This guide explores causes and solutions to incorrect password issues. Forgotten passwords, user permission errors,
1 views • 5 slides
Eye Protection Training for Workplace Safety
Understand the importance of proper eye protection at work, including identifying at-risk job functions, selecting the right PPE, and knowing responsibilities for employees and employers. Training covers when PPE is necessary, how to use, maintain, and dispose of it properly, and the need for retrai
2 views • 28 slides
Cybersecurity Best Practices for Password Protection and Incident Response
Enhance your cybersecurity knowledge with insights on password management, cybercriminal tactics, creating strong passwords, and password complexity. Learn how to safeguard your data and prevent cyber threats by implementing strong password rules, multi-factor authentication, and incident response s
2 views • 24 slides
Understanding Device Settings and Strong Passwords for Digital Citizenship
This lesson focuses on understanding device settings and the importance of creating strong passwords for digital citizenship. It covers topics such as changing backgrounds, locking screens, creating strong passwords, common password mistakes to avoid, and tips for password safety. The lesson also in
1 views • 11 slides
Strengthen Your Digital Literacy with Strong Password Strategies
Enhance your digital literacy by learning about the importance of strong passwords, strategies for creating secure passwords, and the role of password managers. Explore various resources, videos, and tools to improve your password security and protect your online accounts effectively.
0 views • 5 slides
Promote Feature Adoption with Self-Service Password Reset Posters
Enhance feature adoption of self-service password reset among your employees with these ready-to-use posters. Simply customize and print them to encourage password security awareness in your workplace. Don't risk productivity downtime due to forgotten passwords – empower your team to reset their p
0 views • 13 slides
Evolution of Password Security in Modern Computing
Delve into the historical origins of passwords, their significance in cybersecurity, and the current methods employed to safeguard digital assets. Explore the challenges posed by fast computing systems and discover innovative solutions and tools like LastPass, Keeper, and Dashlane in the realm of pa
0 views • 15 slides
Understanding the General Data Protection Regulation (GDPR) and Data Protection Bill
The General Data Protection Regulation (GDPR) is a set of rules aimed at safeguarding individuals' personal data and privacy rights, with key changes from the previous Data Protection Act 1998. The GDPR introduces transparency, consent requirements, enhanced individual rights, breach notifications,
3 views • 40 slides
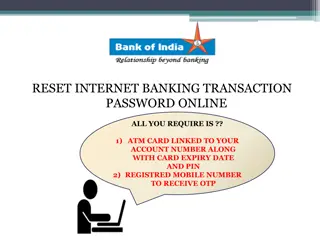
Reset Internet Banking Transaction Password Online Guide
Complete your internet banking transaction password reset online using your ATM card details and registered mobile number for OTP verification. Follow the step-by-step instructions provided with images for a successful reset process and confirmation.
0 views • 8 slides
Enhancing Security with Windows Hello for Business
Windows Hello for Business provides a more secure non-password credential for Windows 10/11 devices, implementing 2FA/MFA to combat password-related vulnerabilities. This article explores the benefits, security measures, and implementation steps of Windows Hello for Business, addressing the challeng
8 views • 24 slides
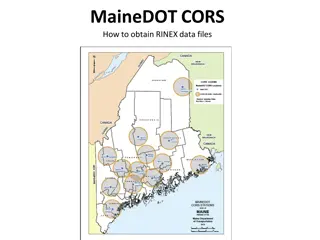
Obtaining RINEX Data Files from MaineDOT CORS
Obtain RINEX data files from MaineDOT CORS by following a few simple steps. Login and password are required, and guest login is no longer an option. The data is collected at one-second intervals and is available for Real-Time-Kinematic (RTK) users. To access the files, visit the provided link, selec
0 views • 17 slides
Groundskeeping Safety and Personal Protective Equipment Training
This presentation covers essential information on groundskeeping safety and the proper use of personal protective equipment (PPE). Topics include head protection, eye/face protection, hearing protection, respiratory protection, hand protection, body protection, foot protection, as well as guidance o
0 views • 35 slides
Rethinking Conditionalities in Social Protection Programs
The images and descriptions provided delve into the concept of conditionalities within social protection programs, highlighting how they can mask poor service quality, create opportunities for coercion, and strip away the protection and safety nets meant to support individuals. The narrative advocat
0 views • 8 slides
Understanding Scrypt: Maximally Memory-Hard Functions
Scrypt is a memory-hard function designed for password hashing and key derivation, aiming to thwart brute-force attacks by making evaluation moderately hard. It emphasizes the need for memory intensity over computation, hindering the advantages of special-purpose hardware, parallelism, and amortizat
0 views • 59 slides
Laptop Roll-Out Information and Schedule for Students at HPK
Information and guidelines for the upcoming laptop roll-out event at HPK including distributing password cards, password training, roll-out locations, times by grade, and instructions on global protection software. Students must follow the specified steps to receive their laptops successfully.
0 views • 14 slides
Safely Logging Password-Derived Measurements for Web Login Systems
Design a secure measurement framework called Gossamer to assess risks associated with password-based measurements for web login systems. Explore ways to differentiate between benign and malicious traffic, and consider adding instrumentation to enhance security. Learn how attackers exploit password-d
0 views • 12 slides
Guide to Logging in and Setting Up Core-CT for the First Time
Accessing Core-CT for the first time involves using your State of Connecticut Employee ID and temporary password. Follow the steps to log in, set up a new password, and establish a forgotten password help feature. This guide provides clear instructions and visuals for each step.
0 views • 19 slides
The Importance of Social Protection and the African Union in Africa
Social protection is recognized as a fundamental human right, and efforts within the African Union have been made to promote social protection programs to combat poverty in Africa. The growth of social protection initiatives since the Ouagadougou declaration of 2004 has led to increased awareness an
0 views • 12 slides
Importance of Fall Protection Systems in Workplace Safety
Fall protection systems play a crucial role in preventing injuries and fatalities caused by falls at the workplace. Understanding the anatomy of a fall, statistics on fall-related incidents, and the various philosophies of fall protection can help companies plan and implement effective fall protecti
0 views • 50 slides
Interactive Password Security Activity for Children
This presentation recaps the importance of strong passwords, techniques for creating them, and the significance of two-factor authentication. The lesson notes guide discussions on creating secure passwords using the "three random words" method and avoiding personal details. The interactive game "Gue
0 views • 4 slides
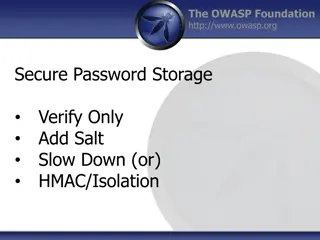
Best Practices for Secure Password Storage - OWASP Foundation Guidelines
Learn about secure password storage techniques recommended by OWASP Foundation, including adding salt, slowing down hashing functions, using HMAC isolation, and imposing difficult verification processes on attackers. Remember to use proper encoding, avoid limiting password types or lengths unreasona
0 views • 10 slides
Techniques and Tools for Offline Password Cracking
Explore the world of offline password cracking techniques using tools like John the Ripper. Learn about the motivation behind cracking user account passwords, gaining root privilege, and compromising vulnerable systems to obtain password hashes for further exploitation. Enhance your understanding of
0 views • 15 slides
Understanding Fine-Grained Password Policies in Active Directory
Explore the intricacies of Fine-Grained Password Policies (FGPP) in Active Directory, covering topics such as domain account policies, policy recovery methods, interpreting pwdProperties attribute, and implementing PSOs for granular password settings. Delve into the nuances of password complexity, h
0 views • 11 slides
Improving Consumer Protection in Ghana: Insights from the Sixth Annual African Dialogue Consumer Protection Conference
The Sixth Annual African Dialogue Consumer Protection Conference held in Lilongwe, Malawi in September 2014 shed light on the challenges faced by Ghana's consumer protection policies. Irene Aborchie-Nyahe, a legal consultant, highlighted the gaps in Ghana's legislative framework, lack of effective i
0 views • 14 slides
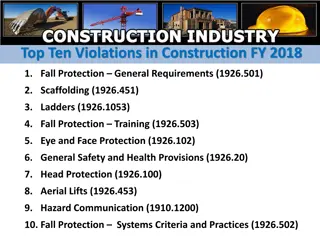
Top Ten Construction Violations FY 2018 Overview
The top ten violations in construction for fiscal year 2018 are related to fall protection, scaffolding, ladders, safety training, eye and face protection, general safety provisions, head protection, aerial lifts, hazard communication, and fall protection systems criteria and practices. The violatio
0 views • 11 slides
Understanding Carnegie Mellon's Protection and Security Concepts
Carnegie Mellon University emphasizes the importance of protection and security in operating systems. Protection involves preventing unauthorized access by users, while security focuses on external threats and authenticating system users. The goals of protection include preventing access violations
0 views • 37 slides
Understanding Data Protection Regulations and Definitions
Learn about the roles of Data Protection Officers (DPOs), the Data Protection Act (DPA) of 2004, key elements of the act, definitions of personal data, examples of personal data categories, and sensitive personal data classifications. Explore how the DPO enforces privacy rights and safeguards person
0 views • 33 slides
Enhancing WiFi Security and Password Protection for IoT Devices
Explore the importance of securing WiFi networks and IoT devices to mitigate privacy and security risks. Learn about encryption, hashing, salting, and ways to strengthen passwords to prevent unauthorized access. Discover common password attack methods and how to safeguard against them.
0 views • 13 slides
Understanding Password Security: Techniques and Best Practices
Delve into the world of password security with this comprehensive guide, covering topics such as password gathering, cracking strategies, tools, types of passwords, hashes, salting, better hashes, and hash identification. Learn how to enhance security measures and protect against malicious attacks.
0 views • 20 slides
Protecting Password Identifiers in IEEE 802.11-21
This submission addresses the need for safeguarding password identifiers in SAE to ensure privacy and prevent attackers from constructing personally identifiable information. The document presents two potential solutions, ultimately recommending the use of symmetric cryptography for efficient protec
0 views • 11 slides
Workshop on Data Protection: Mauritius Police Force Presentation
The workshop on data protection by Mrs. D. Madhub, Data Protection Commissioner, held on May 15, 2019, focused on the Data Protection Act, the Data Protection Office, definitions, functions, powers, and obligations related to data protection, covering areas such as processing of personal data and ri
0 views • 46 slides
Understanding Password Guessability Metrics in Real-World Security
Delve into the realm of password guessability metrics to enhance password security. Explore how measuring guessability aids in eliminating weak passwords, aiding users in creating stronger ones, and assessing security against various cracking algorithms. Uncover the significance of statistical and p
0 views • 27 slides
Self-Service Password Reset Instructions for Staff Members
Staff members can easily reset or change their password through self-service options using Multi-Factor Authentication. They can visit the provided links, verify their identity through email and phone number, and reset their password securely. Follow the step-by-step guide for a hassle-free password
0 views • 4 slides
Guide to Logging into Your Chromebook
This step-by-step guide provides instructions on how to log into your Chromebook using either your student ID and password or a QR code. Simply open the lid, press the power button, select "Next," and then proceed to log in with your credentials. For password login, enter your student ID and the def
0 views • 6 slides
Enhancing Wi-Fi Security with User-Friendly WPA3 Passwords
Proposal to enhance Wi-Fi security by incorporating password and password identifier hashes in the SAE commit exchange, enabling devices to hint to access points which password will be used. This approach aims to improve network efficiency and user experience while addressing privacy concerns associ
0 views • 8 slides