Water Quality Testing Market: Test Type and Industry Sector
Meticulous Research\u00ae\u2014a leading global market research company, published a research report titled, \u2018Water Quality Testing Market by Offering, Test Type (Physical Test, Chemical Test), Device Type, Product Type (pH Meter, TOC Analyzer), Sector (Laboratory, Government, Environmental Ins
4 views • 3 slides
Apache MINA: High-performance Network Applications Framework
Apache MINA is a robust framework for building high-performance network applications. With features like non-blocking I/O, event-driven architecture, and enhanced scalability, MINA provides a reliable platform for developing multipurpose infrastructure and networked applications. Its strengths lie i
3 views • 13 slides
Modeling and Generation of Realistic Network Activity Using Non-Negative Matrix Factorization
The GHOST project focuses on the challenges of modeling, analyzing, and generating patterns of network activity. By utilizing Non-Negative Matrix Factorization (NMF), realistic network activity patterns can be created and injected into live wireless networks. Understanding and predicting user behavi
4 views • 28 slides
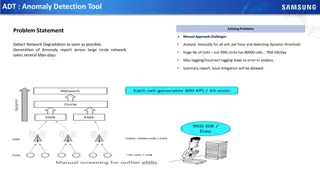
Automated Anomaly Detection Tool for Network Performance Optimization
Anomaly Detection Tool (ADT) aims to automate the detection of network degradation in a mobile communications network, reducing the time and effort required significantly. By utilizing statistical and machine learning models, ADT can generate anomaly reports efficiently across a large circle network
8 views • 7 slides
Revolutionizing Network Management with Intent-Based Networking
Explore the concept and benefits of Intent-Based Networking (IBN) in simplifying network configuration and enhancing efficiency. Learn how IBN automates network operations, aligns with business objectives, improves security, and ensures scalability and reliability. Discover the potential of IBN tool
0 views • 14 slides
Step-by-Step Guide for Using Kruss Goniometer Contact Angle Analyzer
Detailed instructions on how to operate a Kruss goniometer contact angle analyzer. Learn how to set up the equipment, prepare the sample, adjust camera focus, measure contact angle, and analyze the results. Follow each step carefully to achieve accurate measurements.
1 views • 10 slides
Understanding the Clang Static Analyzer by Vince Bridgers
Explore the benefits of tools like Static Analysis, discover different types of program analysis such as linting checks and Compiler diagnostics, and learn about finding flaws in source code through symbolic and dynamic analysis approaches. The tutorial covers the importance of early bug detection,
1 views • 34 slides
Understanding Voice Stress Analysis for Deception Detection
Voice Stress Analysis (VSA) employs technology to detect micro-tremors in the vocal muscles that indicate stress, potentially linked to deception. Developed based on Dr. Lippold's work, VSA systems measure changes in speech characteristics caused by mental stress, aiming to assess the truthfulness o
0 views • 11 slides
Network Compression Techniques: Overview and Practical Issues
Various network compression techniques such as network pruning, knowledge distillation, and parameter quantization are discussed in this content. The importance of pruning redundant weights and neurons in over-parameterized networks is highlighted. Practical issues like weight pruning and neuron pru
0 views • 37 slides
Network Slicing with OAI 5G CN Workshop Overview
Overview of Network Slicing with OAI 5G CN workshop focusing on the crucial role of network slicing in realizing the service-oriented 5G vision. This workshop covers topics like multiple logical networks creation on shared infrastructure, different types of network slices, preparation and instantiat
1 views • 6 slides
Network Design Challenges and Solutions in Business Data Communications
Issues in designing a Local Area Network (LAN) include needs analysis, technological design, and cost assessment. The traditional approach involves structured systems analysis, but faces challenges due to rapidly changing technology and increasing network traffic. The Building Blocks Approach recomm
1 views • 20 slides
Digital Differential Analyzer (DDA) Algorithm in Computer Graphics
In computer graphics, the Digital Differential Analyzer (DDA) Algorithm is utilized as the basic line drawing algorithm. This method involves interpolation of variables between two endpoints to rasterize lines, triangles, and polygons efficiently. The algorithm requires inputting coordinates of two
0 views • 9 slides
Laboratory Equipment E-Catalog 2019
Explore the E-Catalog featuring various laboratory equipment such as the Analyticon Biolyzer 100 Chemistry Analyzer, Boeco Centrifuge C28A, and Eschweiler Blood Gas Analyzer. View specifications, prices, education materials, and procedures for these advanced laboratory tools. The catalog includes es
2 views • 7 slides
Marine Corps Expeditionary Fluid Analysis System (EFAS) Overview
The USMC Expeditionary Fluid Analysis System (EFAS) led by Mr. Anton Schager is a deployable, real-time fluid analysis system supporting Condition-Based Maintenance for Marine Corps ground equipment. It consists of two tiers - a ruggedized portable analyzer for tactical units and a benchtop analyzer
4 views • 12 slides
Understanding S-Parameter Measurements in Microwave Engineering
S-Parameter measurements in microwave engineering are typically conducted using a Vector Network Analyzer (VNA) to analyze the behavior of devices under test (DUT) at microwave frequencies. These measurements involve the use of error boxes, calibration techniques, and de-embedding processes to extra
0 views • 20 slides
Understanding Radiation Safety for XL2 Analyzers
The Niton Model XL2 analyzer uses an X-ray tube that emits radiation when turned on, requiring adherence to the ALARA principle to minimize exposure. Factors like time, distance, and shielding play crucial roles in managing radiation exposure. Learn how to stay safe while using the XL2 analyzer to e
0 views • 11 slides
Understanding 5G RAN Network Slicing and Architecture
Explore the intricate world of 5G Radio Access Network (RAN) and Network Slicing, delving into concepts such as SO Service Orchestrator, SDN-C Service Design, and Core Network Elements. Discover the significance of managing and designing mobile slice services, including eMBB, Massive IoT, and Missio
0 views • 26 slides
Understanding Snort: An Open-Source Network Intrusion Detection System
Snort is an open-source Network Intrusion Detection System (NIDS) developed by Cisco, capable of analyzing network packets to identify suspicious activities. It can function as a packet sniffer, packet logger, or a full-fledged intrusion prevention system. By monitoring and matching network activity
0 views • 23 slides
Data Flows and Network Challenges in Particle Physics Infrastructure
This overview delves into the data flows and network challenges faced in particle physics infrastructure, focusing on the JUNO project. It discusses the process of data reception, storage, and replication across various data centers, highlighting the bidirectional nature of data flows. Additionally,
0 views • 24 slides
Understanding Symmetrical DDA and Bresenham's Line Drawing Algorithm
The content discusses the Symmetrical DDA (Digital Differential Analyzer) and Bresenham's Algorithm for line drawing in computer graphics. Symmetrical DDA generates lines from differential equations, while Bresenham's Algorithm iteratively changes coordinate values to draw lines effectively. The pro
0 views • 11 slides
Progress of Network Architecture Work in FG IMT-2020
In the Network Architecture Group led by Namseok Ko, significant progress has been made in defining the IMT-2020 architecture. The work has involved gap analysis, draft recommendations, and setting framework and requirements. Phase 1 focused on identifying 19 architectural gaps, such as demands for
1 views • 11 slides
Understanding Interconnection Networks Topology
Exploring the topology of interconnection networks helps determine the arrangement of channels and nodes, impacting network cost, performance, latency, energy consumption, and complexity of implementation. Abstract metrics such as degree, hop count, and network diameter play crucial roles in evaluat
1 views • 56 slides
Transportation Network Modeling and Analysis with C.Coupled SE Platform
This content outlines the features and functionalities of the C.Coupled SE Platform (CSET Platform) developed by the Connetics Transportation Group. It covers aspects such as interface design, inputs merging, purposes, platform development using Cube, TAZs merging, and network attributes. The platfo
0 views • 11 slides
Human Disease Symptom Network: Understanding Disease Relationships Through Symptoms and Genes
The Human Disease Symptom Network (HSDN) is constructed using a large-scale medical bibliographic records database to form a network of human diseases based on symptom similarities. By integrating disease-gene associations and protein-protein interaction data, correlations between symptom similarity
0 views • 37 slides
Update on ROOT I/O Workshop Efforts and Recent Additions
Efforts dedicated to improving ROOT software include memory management enhancements, caching advancements, and a new post-compile analyzer. Recent additions focus on memory leaks, TTree optimizations, and performance improvements for ROOT-based projects. Progress has been made towards zero-copy I/O
0 views • 11 slides
Introduction to Network Analysis Using .NET
This presentation introduces the concept of network analysis using .NET in the humanities classroom. It provides a template for teaching and adapting network analysis tools for educational purposes. The guide explains the relevance of networks in processing and visualizing data, emphasizing the coll
0 views • 20 slides
Meridian: An SDN Platform for Cloud Network Services
Meridian is an SDN platform developed by Mohammad Banikazemi, David Olshefski, Anees Shaikh, John Tracey, and GuohuiWang at IBM T. J. Watson Research Center. The platform focuses on providing cloud network services efficiently. It encompasses an architecture that enables faster and more convenient n
0 views • 21 slides
Introduction to Lex and Yacc: Compiler Design Essentials
Lex and Yacc are essential tools in compiler design. Lex serves as a lexical analyzer, converting source code to tokens, while Yacc is a parser generator that implements parsing based on BNF grammars. Through these tools, strings are processed, and code is generated for efficient compilation. This i
0 views • 10 slides
Innovative Wireless Guitar Multi-Functional Design Project Overview
This capstone design project focuses on developing a multi-functional wireless guitar adapter that integrates digital signal processing, Bluetooth interfacing, live-streaming technology, and power amplifier capabilities. The team's progress includes testing guitar signals, designing DSP architecture
0 views • 16 slides
Enhancing Network Security with Software-Defined Snort and OpenFlow
Explore the implementation of Snort, Barnyard, and PulledPork within a Software-Defined Network framework using OpenFlow technology. Learn how these tools enhance network security through intrusion detection engines, rule management, and network traffic control mechanisms. Dive into the architecture
0 views • 15 slides
Woodland Public Schools Facilities and Safety Report April 2022
Woodland Public Schools provided an update on facility improvements and safety measures in their April 2022 report. Highlights include the installation of a new chlorine analyzer at Yale Elementary, delivery of a HAAS VF2 vertical milling machine for the AJAC program at WMS, LED sign installations,
0 views • 6 slides
Understanding Network Analysis: Whole Networks vs. Ego Networks
Explore the differences between Whole Networks and Ego Networks in social network analysis. Whole Networks provide comprehensive information about all nodes and links, enabling the computation of network-level statistics. On the other hand, Ego Networks focus on a sample of nodes, limiting the abili
0 views • 31 slides
Standard G6PD Test Quality Assurance Guide
This comprehensive guide covers the quality assurance features of the SD Biosensor STANDARD G6PD Test, including instructions on checking the strip, code chip, and control reagents. Learn how to use the check strip, change the code chip, and utilize quality control reagents for accurate testing resu
0 views • 14 slides
Knowledge-Based Approach to Winograd Schema Challenge
Method proposed to resolve anaphoric pronouns in the Winograd Schema Challenge using a knowledge-based semantic analyzer called SemETAP. The study challenges the Turing Test's effectiveness and explores the structure of Winograd schemas for better evaluation. Presented by Ivan Rygaev in Dialogue 201
0 views • 37 slides
Network Function Virtualization (NFV) Overview
Network Function Virtualization (NFV) focuses on virtualizing network functions to improve efficiency and reduce costs in network infrastructure. The lecture discusses key readings, devices that compose a network, specialization of devices, benefits of one-device-does-anything approach, and the goal
0 views • 21 slides
Enhancing Network Stability with Network Monitoring Systems
Network monitoring is crucial for efficient management and proactive issue detection in a network environment. Factors influencing an effective network system include choosing the best OEM, SLA agreements, and selecting a reliable System Integrator. Reactive monitoring can lead to financial losses a
0 views • 12 slides
Environmental Contaminant Analysis Workshop by ANFEC at Royal University of Phnom Penh
Join the 1st ANFEC Training Workshop on Environmental Contaminant Analysis at Royal University of Phnom Penh from 18-20 December 2012. Explore the SMS 100 Mercury Analyzer for precise determination of total mercury in solid and liquid samples, featuring a decomposition furnace, auto sampler, spectro
0 views • 9 slides
Understanding Complete Blood Count (CBC) Testing
Complete Blood Count (CBC) is a crucial test that provides information about the composition of a patient's blood, including red blood cells, white blood cells, and platelets. This test helps in diagnosing conditions such as anemia, infections, and more. CBC involves analyzing parameters like RBC co
0 views • 20 slides
Accelerating Systemic Change Network Inaugural Workshop Summary
The Accelerating Systemic Change Network held its inaugural workshop at Howard Hughes Medical Institute in July 2016 to address the lack of coordination in improving higher education. With a vision to become a professional hub for change researchers in STEM education, the network aims to enhance ind
0 views • 5 slides
University Network Section Overview July 2015 - March 2016
The presentation covers the network team structure, team members, objectives, goals, report outline, network statistics, accomplishments, and future plans of the university network section from July 2015 to March 2016. It highlights efforts to provide stable internet and intranet services, restructu
0 views • 16 slides