Airport Security Market to be Worth $25.27 Billion by 2031
\u00ae, the airport security market is projected to reach $25.27 billion by 2031, at a CAGR of 8.6% from 2024 to 2031. Some of the major factors driving the growth of this market are stringent government regulations for airport security and the growing number of air passengers. In addition, increasi
8 views • 5 slides
KEERTHI SECURITY - Best Security Agencies In Bangalore
Keerthi Security is a security and facility management services provider in Bangalore. We are committed to offering top-notch security services for commercial and residential places. We aim to offer very secure and reliable security services to everyone. Our best-trained security guards are very sha
10 views • 11 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Role of Security Champions in Organizations
Security Champions play a vital role in decision-making concerning security engagement, acting as a core element in security assurance processes within a team. They foster a security culture, reduce dependency on the CISO, and promote responsible autonomy and continuous security education in the org
3 views • 13 slides
Developing with Docker Containers in Visual Studio Code Workshop
Learn how to use Docker containers as a development environment in Visual Studio Code. The workshop will cover prerequisites, learning objectives, agenda, and hands-on exercises to prepare projects, customize settings, and add software to container environments.
0 views • 40 slides
Guide to Self-built Moodle Docker Testing Environments by Alexander Dominicus
Dive into the world of self-built Moodle Docker testing environments with insights shared by Alexander Dominicus. Understand the significance of Docker containers in ensuring software portability, encapsulating dependencies, and resolving bugs. Explore the choice between pre-built and self-built set
2 views • 24 slides
Roles of a Security Partner
Learn about the roles and responsibilities of a Security Partner, including requesting changes to security roles, approving security requests, and initiating access requests. Explore the overview of Workday Security, the security access request process, and the pre-request process flow. Discover how
2 views • 17 slides
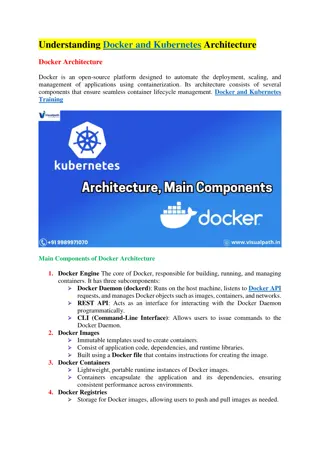
Docker Architecture in Advanced Operating Systems
Delve into the intricacies of Docker architecture as covered in CSE 522S Advanced Operating Systems course at Washington University in St. Louis. Explore the fundamental mechanisms, client-server interactions, container creation automation, and monitoring provided by Docker. Gain insights into names
5 views • 13 slides
Container Security: What Could Possibly Go Wrong?
This presentation explores the fundamentals of container technology, focusing primarily on Docker. It delves into the differences between containers and virtual machines, discusses the threat landscape in container security, and emphasizes best practices, especially in vulnerability and patch manage
0 views • 33 slides
Comprehensive Online Tutorial for Component Databases Management
Explore a detailed online tutorial covering various aspects of managing component databases, including finding information, setting up in a Docker environment, data definition interface, editing components and modules, and generating server/client web applications. Access documentation, docker setup
0 views • 33 slides
Enhancing Learning Environments with Vagrant and Docker
Explore the integration of Vagrant and Docker in educational settings to empower students with practical IT skills. Addressing challenges faced by archivists and librarians, these tools open new possibilities for hands-on learning through virtualization systems and portable labs. Discover how Vagran
0 views • 28 slides
Introduction to Docker and HTCondor in High-Performance Computing
Explore the evolution from HTCondor's use of chroot for job isolation to the adoption of Docker containers for managing Linux containers in high-performance computing environments. Understand the benefits and challenges of utilizing Docker with HTCondor, highlighting the shift towards more efficient
0 views • 49 slides
Docker: A Comprehensive Overview
Docker is a versatile system that enables running programs in lightweight containers, simplifying processes and enhancing rigor. Despite objections, Docker offers benefits such as ease of use, improved efficiency, and image sharing through registries. This presentation by Richard Schneider at Hardin
0 views • 23 slides
Cornell University - Docker, Drupal, and Persistence with Bill Juda
Learn about Docker, Drupal, and local development setup from Bill Juda at Cornell University. Discover the advantages of Docker containerization, set-up with docker-compose, and explore Drupal as a Content Management System. Get insights into optimizing your development environment and find useful d
0 views • 22 slides
Cybersecurity Work Updates: Week 10/30
Overview of the week's work includes setting up a basic grid, SYN flood attempts, dss-python progress, and fixing Docker issues. Specific updates from team members Tyler, Zach, Justin, and Kaya on their tasks and explorations related to cybersecurity. Highlighted activities such as experimenting wit
1 views • 14 slides
Developing Standardized Tango Environment with Docker for SKA Telescope Project
SKA project required a standardized Tango environment for development, testing, and continuous integration resulting in reference Docker images for Tango v9.3.3. Developed on Debian stable, these images include dependencies and follow best practices. The project, known as ska-docker, provides core i
0 views • 13 slides
Comprehensive DevOps Security Training Overview
This Certified DevOps Security Practitioner course provides a deep dive into implementing DevSecOps, integrating security into the DevOps processes. Covering topics like security testing, Docker security, automation, and more, the training aims to equip participants with the necessary skills to embe
1 views • 5 slides
The Best Docker and Kubernetes Course - Docker Online Training
Visualpath offers premier Docker Online Training led by industry experts. Our program includes hands-on projects, Docker and Kubernetes Courses, and interview preparation. Accessible globally, including India, the USA, the UK, Canada, Dubai, and Aust
0 views • 3 slides
Docker and Kubernetes Training in Hyderabad - Visualpath
Visualpath delivers top-notch Docker and Kubernetes Courses led by real-time experts. For more information, call 91-9989971070 today\nVisit: \/\/ \/online-docker-and-kubernetes-training.html
1 views • 3 slides
Docker and Kubernetes Training - Kubernetes Online Training
Visualpath Institute in Hyderabad provides outstanding Kubernetes Online Training, delivered by industry experts emphasizing hands-on learning. Their Docker Online Training is accessible worldwide, including in the USA, UK, Canada, Dubai, and Austral
1 views • 5 slides
Kubernetes Online Training - Docker Kubernetes Online Course
Visualpath provides premier Docker and Kubernetes Training, delivered by industry experts to ensure hands-on learning. Our courses are accessible worldwide, catering to students in the USA, UK, Canada, Dubai, and Australia. For more information, call
1 views • 5 slides
Docker Online Training - Kubernetes Online Training
Visualpath Institute in Hyderabad offers top-notch Kubernetes Online Training and Docker Online Training led by industry experts. Available globally, including the USA, UK, Canada, Dubai, and Australia, the courses focus on hands-on learning. Key top
0 views • 4 slides
Docker and Kubernetes Training in Hyderabad
Visualpath offers expert-led Docker and Kubernetes Online Training with real-time instructors and hands-on projects. Available globally, including the USA, UK, Canada, Dubai, and Australia, our Kubernetes Certification Training prepares you for caree
0 views • 4 slides
Docker and Kubernetes Training in Hyderabad
Visualpath offers expert-led Docker and Kubernetes Online Training with real-time instructors and hands-on projects. Available globally, including the USA, UK, Canada, Dubai, and Australia, our Kubernetes Certification Training prepares you for caree
0 views • 4 slides
Docker and Kubernetes Training in Hyderabad
Visualpath offers expert-led Docker and Kubernetes Online Training with real-time instructors and hands-on projects. Available globally, including the USA, UK, Canada, Dubai, and Australia, our Kubernetes Certification Training prepares you for caree
0 views • 4 slides
Docker and Kubernetes Training in Hyderabad
Visualpath offers expert-led Docker and Kubernetes Online Training with real-time instructors and hands-on projects. Available globally, including the USA, UK, Canada, Dubai, and Australia, our Kubernetes Certification Training prepares you for caree
0 views • 4 slides
Docker Kubernetes Online Course - Docker & Kubernetes Training
VisualPath in Hyderabad offers an outstanding Docker Kubernetes Online Course, featuring hands-on learning with real-world projects. Our Docker & Kubernetes Training provides expert guidance, in-depth coverage, and career support. The program is avai
1 views • 4 slides
Docker and Kubernetes Training - Visualpath
VisualPath in Hyderabad delivers an exceptional Docker Kubernetes Online Course with hands-on learning and real-world projects. The program offers expert guidance, comprehensive coverage, and career support. Accessible worldwide, it caters to learner
1 views • 4 slides
Docker Kubernetes Online - Docker and Kubernetes Course
VisualPath provides expert-led Docker & Kubernetes Training in Hyderabad, focusing on hands-on practice to develop real-world skills. Our Docker Online Training includes daily recordings, detailed presentations, and global accessibility for flexible
1 views • 4 slides
Best Docker Kubernetes Training - Docker Kubernetes Online
VisualPath offers expert-led Docker and Kubernetes Online Training, covering key topics like Lightweight, Portability, and Multi-Cloud. Available globally, including the USA, UK, Canada, Dubai, and Australia, our course enhances your containerization
1 views • 5 slides
Docker and Kubernetes Training - Docker and Kubernetes Online
VisualPath offers the best Docker and Kubernetes Training to enhance your containerization skills. Our expert-led Docker and Kubernetes Online courses cover key concepts like lightweight architecture, portability, and multi-cloud management. With han
3 views • 3 slides
Best Docker Kubernetes - Docker Kubernetes Course
VisualPath provides top-notch Docker and Kubernetes courses to enhance your containerization skills. Our expert-led online training covers lightweight architecture, portability, and multi-cloud management. Gain hands-on experience with real-world pro
1 views • 4 slides
Best Docker Kubernetes - Docker Kubernetes Training in Chennai
VisualPath offers expert-led Docker and Kubernetes courses to elevate your containerization skills. Our Kubernetes Certification Training Course covers lightweight architecture, portability, and multi-cloud management. Gain hands-on experience throug
1 views • 4 slides
Top Docker and Kubernetes Training in Bangalore - India
VisualPath offers expert-led Docker and Kubernetes Training in Bangalore with hands-on projects and real-time examples. Get Daily Recorded Sessions for Reference and 24\/7 Access to Recorded Sessions for flexible learning. Our Docker and Kubernetes o
1 views • 5 slides
What's New in HTCondor: Updates and Enhancements
In HTCondor, the latest version v8.9.0 is focusing on new features and enhancements. Previous versions like v8.8.x introduced stability improvements, Docker Job Universe, IPv6 support, and more. The integration of Singularity offers Docker-like capabilities without a root-owned daemon process. Featu
0 views • 25 slides
What's New in HTCondor: Updates and Enhancements
HTCondor, a powerful distributed computing software, is constantly evolving with new features and improvements. The latest developments include enhanced scalability, Docker job universe support, IPv6 compatibility, and more. Version 8.6 introduced significant enhancements, such as simplified task ma
0 views • 26 slides
Exploring Docker Security
In-depth review of Docker security, hardware virtualization, and VMs. Explore pros and cons of hardware virtualization, Docker architecture, and the Container approach. Learn about Docker's history, ease of application packaging, and its role in the DevOps movement.
0 views • 43 slides
Docker Course - Kubernetes Online Training in India
VisualPath provides Docker and Kubernetes Training in Bangalore with expert-led sessions, hands-on projects, and real-time examples. Enjoy daily recorded sessions and 24\/7 access to flexible learning. Our Docker and Kubernetes Online Courses are ava
1 views • 4 slides
Top Docker and Kubernetes Online Training in India Visualpath
VisualPath offers Docker and Kubernetes Online Training in India with expert-led sessions, real-time examples, and hands-on projects. Our Docker and Kubernetes Courses include job-oriented training and resume preparation to boost your career. Get dai
1 views • 4 slides