Advanced Pre-Filled Syringes and Parenteral Solutions (Event) 2024
Welcome to MarketsandMarkets NextGen Inject: Conference on Advanced Pre-Filled Syringes and Parenteral Solutions where innovation meets injection.\n\nEnquire More @ https:\/\/events.marketsandmarkets.com\/nextgen-inject-conference-on-advanced-pre-filled-syringes-and-parenteral-solutions\/ \n\nWho Sh
2 views • 5 slides
Master GB0-372 Ace H3C Advanced Routing & Switching Technology 1 Exam
Elevate your career with success in the GB0-372 exam. Master H3C Advanced Routing and Switching Technology 1 with our comprehensive study materials, practice tests, and expert guidance. Prepare effectively for the H3C GB0-372 exam and gain the skills and knowledge necessary to excel in advanced rout
2 views • 8 slides
Introduction to IBM Watson Explorer in Business Intelligence: University of Rome La Sapienza Course
The course at University of Rome La Sapienza introduces students to IBM Watson Explorer for Business Intelligence. It covers practical use cases, advanced BI topics, and familiarization with real software used in organizations. The schedule includes sessions on Watson Explorer features, conducting B
0 views • 34 slides
Enhancing Access to Medicines and Health Products through Innovative Approaches
Global Health Centre experts discuss how building access into innovation can ensure better access to medicines, vaccines, and health products. Key ideas include planting seeds for access early in innovation, exploring alternative innovation models, and rethinking the relationship between innovation
4 views • 20 slides
Dynamics 365 Online Training - Microsoft Dynamics 365 Online Training
Advanced Warehouse Management - VisualPath offers the Best Advanced Warehouse Management Online Training conducted by real-time experts. Our Advanced Warehouse Management is available in Hyderabad and is provided to individuals globally in the USA, UK, Canada, Dubai, and Australia. Contact us at 91
1 views • 10 slides
Dynamics Advanced Warehouse Management - Hyderabad
Advanced Warehouse Management - VisualPath offers the Best Advanced Warehouse Management Online Training conducted by real-time experts. Our Advanced Warehouse Management is available in Hyderabad and is provided to individuals globally in the USA, UK, Canada, Dubai, and Australia. Contact us at 91
1 views • 4 slides
2022 Thales Access Management Index
Thales Access Management Index highlights the current landscape of access security, revealing insights on multi-factor authentication adoption, remote and privileged user access management, VPN usage trends, challenges faced, and preferences towards third-party access management. The report emphasiz
2 views • 9 slides
Advanced Warehouse Management Course - Hyderabad
Advanced Warehouse Management - VisualPath offers the Best Advanced Warehouse Management Online Training conducted by real-time experts. Our Advanced Warehouse Management is available in Hyderabad and is provided to individuals globally in the USA, UK, Canada, Dubai, and Australia. Contact us at 91
9 views • 3 slides
Guidelines for Expanded Access to Investigational Drugs and Devices
Providing guidance on types of Expanded Access for drugs, biologics, and devices, this content explains the concept of Expanded Access and the criteria that must be met. It covers different types of Expanded Access for drugs and devices, emphasizing the importance of patient safety and benefit. The
0 views • 10 slides
Personnel Safety Systems and Access Control at CERN Facilities
Personnel Safety Systems at CERN include ODH detection, fire safety measures, and access control to protect personnel from hazards. Various access control layers are implemented to regulate entry to different parts of the facility, ensuring only trained personnel access underground areas. Biometric
0 views • 19 slides
Understanding Advanced Pedagogy in Education
Advanced Pedagogy involves skillful planning and implementation of activities to engage learners collaboratively. It emphasizes integrating innovative teaching strategies, technology, and diverse learning modes to enhance student motivation and understanding. The principles of advanced pedagogy focu
1 views • 55 slides
Advanced Higher English: Transition and Expectations
Moving from Higher to Advanced Higher English requires a deeper level of literary knowledge and independent critical reading and writing skills. The Advanced Higher English course involves creating a portfolio with creative and discursive writing pieces, as well as a dissertation focusing on literat
0 views • 6 slides
Advanced Clinical Practice Framework and Pillars of Practice
The document discusses the advanced clinical practice framework and the four pillars of practice which include leadership & management, clinical practice, education, and research. It emphasizes the importance of core capabilities and area-specific competence in advanced clinical practice. The role o
2 views • 8 slides
Port of Stockton Restricted Area Access Control and ID Card Policy
Access to restricted areas at the Port of Stockton facilities requires possession of a TWIC (Transportation Worker Identification Credential). Only authorized personnel, such as employees, contractors, and those with regular access, may receive a Port Access Card after approval by the Facility Secur
0 views • 6 slides
Introduction to Database Security and Countermeasures
Database security is essential to protect data integrity, availability, and confidentiality. Countermeasures such as access control, inference control, flow control, and encryption can safeguard databases against threats. Access control restricts user access, inference control manages statistical da
0 views • 26 slides
O3 Access Control Solution Overview
O3 Access Control Solution offers unique selling points like single-seat management software, role-based permissions, customizable user information, and more. The system includes a compact controller with multi-format reader support and BACnet Access objects. It integrates with other O3 modules for
0 views • 10 slides
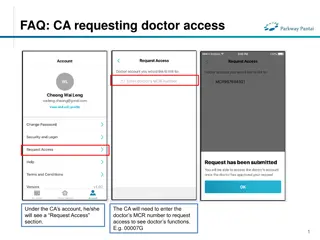
FAQs for Doctor and Clinical Assistant (CA) Account Access Management
Learn how CAs can request access to doctors' functions by entering the MCR number, how doctors can grant or remove CA access, and how CAs can manage access to multiple doctors. The process includes requesting, approving, and unlinking accounts, ensuring efficient and secure access management in a cl
0 views • 4 slides
Intercept X - Early Access Program Overview
Intercept X's Early Access Program offers advanced security solutions to combat active adversaries and advanced malware. The program covers deep learning techniques, false positive mitigations, and credential theft protection. It focuses on protecting against various threats such as credential theft
0 views • 14 slides
EventsHQ Virtual Event Registration: User Access and Setup Guide
This comprehensive guide provides step-by-step instructions on setting up virtual event registration using EventsHQ. It covers how users can access event details, join the event, and includes best practices for sharing access links. Learn how to utilize the Virtual Event Details feature, send remind
1 views • 19 slides
Accessible Voting System for Californians with Disabilities
Learn about the Remote Accessible Vote-by-Mail System in California, designed to empower voters with disabilities to securely access, mark, and return their ballots from any computer with internet access. Find out who is eligible to use the system, how to access and return the ballot, and the steps
0 views • 23 slides
Dell Networking Solutions for BYOD and Guest Access Projects
Dell offers end-to-end solutions for Bring-Your-Own-Device (BYOD) and guest access projects, enabling secure employee access and controlled connectivity for visitors. The framework includes mobility business models, device security, network protection, and scalability. Dell supports customers in imp
0 views • 11 slides
MSc in Advanced Computer Science Program Details
The MSc in Advanced Computer Science program at the University of Strathclyde offers advanced courses focusing on Future Computing Systems, with a blend of theory and practical emphasis. Graduates delve into mobile, reliable, secure, distributed, and autonomous systems. Besides the core curriculum,
0 views • 11 slides
Role-based Access Control Policies and Security Properties Overview
This content provides an overview of Role-based Access Control (RBAC) policies, Administrative RBAC (ARBAC) systems, and security properties in the context of access control in large organizations. It discusses the implementation of RBAC in various software systems, the assignment and revocation of
0 views • 18 slides
Open Access at Charles University: Opportunities and Challenges
Charles University is navigating the landscape of open access following the implementation of the Czech National Open Access Strategy. The university is working towards making all research articles and proceeding papers open access, monitoring article processing charges, and promoting open access as
0 views • 24 slides
Understanding Filesystem Security Principles and Access Control
Learn about filesystem security, general principles, discretionary access control (DAC), closed vs. open policy, closed policy with negative authorizations, and access control entries and lists. Discover how files and folders are managed, the role of access control lists (ACLs), and the different le
1 views • 56 slides
Understanding Ethernet and Multiple Access Protocols in Computer Networks
Exploring the fundamentals of Ethernet and multiple access protocols in computer networks, this content discusses the two primary categories of multiple access protocols - contention access and controlled access. It delves into topics such as CSMA/CD, LANs, performance of multiple access schemes, ad
0 views • 7 slides
Understanding Shared Memory, Distributed Memory, and Hybrid Distributed-Shared Memory
Shared memory systems allow multiple processors to access the same memory resources, with changes made by one processor visible to all others. This concept is categorized into Uniform Memory Access (UMA) and Non-Uniform Memory Access (NUMA) architectures. UMA provides equal access times to memory, w
0 views • 22 slides
Advanced HIV Diagnoses Among Gay and Bisexual Men in Australia: 2007-2016 Study Analysis
This study conducted in Australia from 2007-2016 analyzed advanced HIV diagnoses among gay and bisexual men. The research identified factors like age (30-39, 40-49, 50-59, 60+), exposure type (bisexual, MSM + IDU), and region of birth (South East Asia and North East Asia) as significant contributors
0 views • 6 slides
Understanding Access Changes and Community Relations at Fermilab
Access to Fermilab has become more complicated due to changing DOE guidance and security posture. Efforts are being made to streamline access while addressing security gaps. Public access to outdoor areas of the Fermilab campus is still encouraged, but communication regarding access changes needs im
0 views • 12 slides
Understanding Computer System Protection and Security
Mechanisms like protection and security ensure controlled access to a computer system's resources and prevent malicious activities. Protection involves defining access control levels through models, policies, and mechanisms. Security focuses on user authentication to safeguard stored information. Di
0 views • 25 slides
Understanding Access to ITU Information and Documents
Exploring the concept of access in the work of a dedicated group, this content delves into the types of information that could or should be made available to the public, along with considerations on when access should be provided. It highlights the varying stages of information dissemination, discus
0 views • 8 slides
Harvard Chan School 2021 Yearly Access Review Process
The Harvard Chan School conducts its annual Yearly Access Review (YAR) process to review user access to various financial systems. The process involves assessing permissions, levels of access, and organizational details for each team member. Instructions are provided on reviewing worksheets, adding
0 views • 19 slides
Understanding Security Access in PeopleSoft Finance
Explore the various levels of security access in PeopleSoft Finance, from basic entry access to transaction entry, approvals, and procurement processes. Learn how to request individual and department security access and find relevant forms on the financial services website. Discover the different ty
0 views • 11 slides
Proxy Access to Medications Implementation Stages
This document outlines the implementation stages for proxy access to medications. It covers agreements with healthcare providers, prerequisites including compliance and data sharing agreements, and systems configuration for access to medical records. The stages include setting up access for care pro
0 views • 7 slides
CSUEB Academic Access Enhancement and Excellence Fee Proposal
The CSUEB Academic Access Enhancement and Excellence Fee Proposal aims to enhance the academic environment, reduce student costs, and provide equal access to educational materials. Components include an Academic Access Enhancement fund, e-textbooks program, and provision of tablets/netbooks to all i
0 views • 23 slides
Publishing Requirements and Challenges in Horizon Europe
The publication landscape under Horizon Europe presents challenges regarding compliance with publishing fee eligibility for hybrid journals and embargoes for open access. Hybrid journals feature subscription-based and open access parts, while open access journals require authors to pay open access f
0 views • 6 slides
Custom Groups and Advanced Filters in CERS
Explore the features of creating custom groups and using advanced filters in CERS for teachers. Learn how to generate ISRs, access resources, and find answers to questions specific to interim assessments. Discover the benefits of customizing groups and utilizing advanced filters to enhance monitorin
0 views • 27 slides
Best Practices for Transradial Angiography and Intervention
This update highlights best practices for transradial angiography and intervention, including topics such as ultrasound guidance for transradial access, ulnar artery access recommendations, and future study opportunities. The importance of developing proficiency with ultrasound guidance, utilizing r
0 views • 15 slides
Enhancing Primary Healthcare through Advanced Access Strategies
Explore how Health Quality Ontario (HQO) is promoting accessible and efficient care in primary healthcare with a focus on chronic disease management. Learn about the importance of advanced access, reducing delays, and improving patient-provider interactions for better healthcare outcomes. Discover i
0 views • 33 slides
Evolution of Access Management in the 21st Century: RA21 Initiative
RA21, a joint initiative of STM Publishers and NISO, addresses the challenges of IP-based access management in the digital age. It aims to enhance user experience by optimizing access protocols across different stakeholder groups. The evolution from print to digital formats has led to the need for n
0 views • 12 slides