An Easy Method To Resolve QuickBooks Backup Failed Issue
Businesses that depend on QuickBooks accounting software may find it alarming when they receive a \"QuickBooks Backup Failed\" warning. Network problems, corrupted data files, and inadequate storage are examples of potential causes. Take immediate action to resolve these problems by making sure ther
5 views • 7 slides
Maximizing Impact: The Role of Rich Snippets in SERPs"User Intent
User intent, also known as search intent, refers to the underlying goal or purpose a user has when performing an online search. It goes beyond the literal interpretation of keywords and focuses on understanding why a person is searching. Recognizing and catering to user intent is crucial for creatin
3 views • 10 slides
Data Backup Best Practices
Data backup is crucial for protecting your information in case of disasters or accidents. Learn about the importance of data backup, different backup options like removable media, external hard drives, hardware appliances, and cloud services, as well as the 3-2-1 backup strategy. Make sure to verify
0 views • 8 slides
NOAA HRD User Group
Kelvin Brentzel provides updates on NOAA HRD User Group activities, including post-launch updates for NOAA-21 HRD and pre-launch updates for J3 HRD. The DRL team collaborates closely with JPSS teams and commercial partners to enhance HRD signal performance and data processing capabilities. Detailed
0 views • 4 slides
4 Common Backup Mistakes Every Organization Must Avoid
Avoid data loss! Discover the 6 common backup mistakes every organization must avoid with Backup Installation Dubai from VRS Technologies LLC. For More info Contact us: 056-7029840.
2 views • 7 slides
Database Backup and Recovery Models Explained
Explore different database recovery models - Full Recovery, Bulk-Logged Recovery, and Simple Recovery. Learn about backup types like Full Backup, Differential Backup, and File/Filegroup Backup. Understand the importance of transaction logs in data recovery processes.
1 views • 17 slides
Implementing Alert Messages and User Input Handling in Java
This tutorial guides you through creating alert messages, handling user input, defining functions, calling functions from the `onCreate` method, and creating an XML file for user data entry validation in Java. Learn how to display alerts for empty user credentials and process user actions accordingl
1 views • 6 slides
Proposal NPRR.1144: Station Backup Power Requirements Exception
NPRR.1144 proposes an exception allowing up to 500kW of auxiliary load to connect to a Transmission/Distribution Service Provider's facilities through a separately metered point using an emergency load transfer switch. This exception aims to provide flexibility in redundant power supply options for
0 views • 4 slides
The Importance of Backup Systems in Proximity Card Access Control
Discover why backup systems are crucial for ensuring security and reliability in proximity card access control.
1 views • 7 slides
Unsupervised Clickstream Clustering for User Behavior Analysis
Understanding user behavior in online services is crucial for businesses. This research focuses on utilizing clickstream data to identify natural clusters of user behavior and extract meaningful insights at scale. By analyzing detailed user logs, the study aims to reveal hidden patterns in user inte
0 views • 19 slides
Introduction to Archiving and Backup Tools in Linux
Learn about essential archiving and backup commands in Linux, including gzip for compression, gunzip for decompression, tar for archiving files, zip for compression and archiving, and unzip for decompressing zip files. Understand the purpose and usage of each command with examples provided.
0 views • 6 slides
Introduction to Backup and Recovery Procedures in Databases
Backup and recovery procedures are essential for protecting databases against data loss. This chapter covers fundamental concepts and strategies for designing a backup plan, including physical and logical backups, consistent and inconsistent backups, and the importance of whole database backups.
0 views • 17 slides
Data Storage, Backup, and Security Essentials
Understanding the importance of data storage, backup, and security in research projects is crucial. This guide covers best practices for creating a data management strategy, evaluating storage media, implementing backup protocols, and ensuring data security. Learn about storage options, backup proce
0 views • 14 slides
Practical Lecture #1: Backup & Recover User Data
Learn how to back up and recover user data, including hidden files and folders using a PC or mobile device. The lecture covers steps for backing up data to an external disk in Windows, setting up backup schedules for specific folders, and exploring cloud-based backup services for remote disk backup.
2 views • 13 slides
Essential Guide to Data Storage and Backup
Explore the crucial aspects of data storage and backup, covering network drives, local devices, cloud storage, and the importance of regular backups for key data like programs, algorithms, and documentation. Learn best practices to keep your information secure and accessible.
0 views • 6 slides
Accelerator for VMware Backup Solutions
Today's challenges in backing up data from VMware environments include high data volume, small backup windows, slow traditional backups, network bandwidth utilization, and CPU overhead. NetBackup's Accelerator for VMware in version 7.6 addresses these challenges by using Changed Block Tracking (CBT)
0 views • 18 slides
Developing a Successful Backup Processing Strategy
This unit explores backup processing alternatives, contingency planning, and the importance of selecting and implementing alternate processing support in advance. It emphasizes the need for well-documented strategies to ensure rapid recovery from disruptions in data processing, along with identifyin
1 views • 128 slides
WhatsApp End-to-End Encrypted Backup Protocol Security Analysis
This security analysis delves into the WhatsApp end-to-end encrypted backup protocol, highlighting the potential risks associated with chat history backups. It discusses the dangers of password guessing, the vulnerabilities of cloud providers, and proposes solutions for a more secure backup system t
0 views • 20 slides
Comprehensive Guide to Archives and Backups
Explore the importance of backups, types of failures they protect against, and best practices for creating effective backup systems. Learn about common backup strategies, best practices for backup data management, and various backup media options available. This comprehensive guide covers everything
0 views • 31 slides
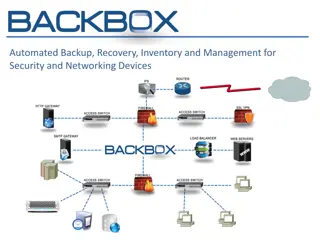
Automated Backup, Recovery, Inventory, and Management Solutions for Security and Networking Devices
BackBox offers industry-leading automated solutions for backup, restore, inventory, and management of security and networking devices. With a global presence and 24/7 support, BackBox aims to streamline operations, minimize downtime, and ensure business continuity through efficient disaster recovery
0 views • 17 slides
VMware Backup Best Practices with NetBackup Accelerator
Managing backups for VMware environments can be challenging due to high data volumes and small backup windows. Traditional full backups can be slow and resource-intensive. NetBackup Accelerator for VMware introduced in NetBackup 7.6 offers a more efficient solution by utilizing VMware Changed Block
0 views • 22 slides
Exciting Features in Vembu BDR Suite v3.5 - Latest Updates Revealed!
Discover the upcoming Vembu BDR Suite v3.5 features, including VMware failover & failback, IP & network remapping support, new releases like Vembu SaaSBackup and BDR360. Learn about Vembu's impressive background, founded in 2004, with a focus on serving over 60,000 businesses worldwide. Explore the
0 views • 31 slides
SQL Server Database Recovery Models and Backup Strategies
Explore the intricacies of SQL Server database recovery models including SIMPLE, BULK-LOGGED, and FULL, along with backup techniques such as full database backups, transaction log backups, and differential backups. Learn about database states, mirror states, and various system databases in SQL Serve
2 views • 24 slides
Backup Link Establishment for Low Latency Communication
Achieving low latency communication is crucial when link quality deteriorates. This presentation by Qi Wang et al. from Apple Inc. introduces the concept of establishing a Backup Link to swiftly switch LL communication to a better link, enhancing data transmission efficiency in scenarios where the p
3 views • 12 slides
Health IT Systems Maintenance: Fault-Tolerant Strategies and Backup Best Practices
Explore the essential practices for creating fault-tolerant IT systems in healthcare, including risk assessment, backup strategies, and decommissioning guidelines. Learn about the importance of backups, backup strategies, and the challenges of maintaining system availability 24/7.
0 views • 17 slides
Windows Azure Recovery Services Overview
Windows Azure Recovery Services offer various solutions for automated server backups, orchestrated protection, and recovery of private clouds. With features like Hyper-V Recovery Manager and Backup Preview, you can protect important data offsite in the cloud and automate backup processes for easy da
0 views • 14 slides
Modernizing Backup and Archival for the Multi-Cloud World by FalconStor
FalconStor focuses on modernizing backup and archival solutions for the multi-cloud world, offering fast data backup and restore speeds, significant data reduction capabilities, cost savings, and cloud-ready operations. The company is recognized as a trusted data protection leader with a strong trac
4 views • 12 slides
Efficient User Management System for Health Facilities
Record and manage user details effectively with the new Version 2.0 User Management feature. RNTCP has now registered over 35,000 PHIs, 140,000 Private Health Facilities, 15,000 Private Labs, 31,000 Private Chemists, across 700 Districts and 8,000 TUs in Nikshay. Enhance operations by editing TU pro
0 views • 26 slides
Effective Data Management Planning for Research Projects
Data management planning is essential for research projects to ensure data integrity, accessibility, and longevity. This involves creating a plan outlining data creation, documentation, storage, access, backup, sharing, and preservation strategies. Developing a DMP helps avoid problems, comply with
1 views • 15 slides
Enhancing User Experience Through Data Trails and Metrics
Andrea Thompson, a Sr. User Experience Manager at The Home Depot, highlights the importance of measuring and analyzing user experience metrics to understand and improve customer interactions. By investigating data trails from various touchpoints, such as customer sign-ups, interactions with associat
0 views • 17 slides
IT Solutions for Small to Medium Businesses
Flamingo Computer Services and Networking offers comprehensive IT support and solutions for small to medium business networks. Challenges in backup solutions are addressed with the Symantec Backup Exec System Recovery, ensuring reliable and fast recovery from various threats. The impact of longer re
0 views • 13 slides
Overview of Rule 21 Non-Exporting and Backup Options
This content provides an overview of Rule 21 Non-Exporting and Backup options. It covers non-exporting projects, backup systems, inadvertent exports, NEM solar with paired storage, and non-export options for storage under the Rule 21 tariff/option. Detailed information is presented regarding project
0 views • 8 slides
High-Tech Equipment for Reaction and Impregnation Processes
Cutting-edge technology described in detail for reaction and impregnation processes, including fixture setups, temperature monitoring, data logging, and backup systems. The equipment is designed for precision and control, with capabilities for remote monitoring via web or smartphone and backup power
0 views • 5 slides
ARM Microcontroller Power Supply, Reset, and Clock Control Overview
This overview covers the power supply, reset control, and clock sources for ARM microcontrollers, focusing on aspects such as power supplies, battery backup, voltage regulator operation modes, and power supply supervisor functions. It discusses essential details like operating voltages, backup domai
0 views • 27 slides
User Interface Design Principles in Human-Computer Interaction
User interface design principles are crucial in Human-Computer Interaction. This content highlights key principles such as aesthetics, anticipation, autonomy, and color consideration for users with color blindness. It emphasizes the importance of user testing, user autonomy, and providing essential
0 views • 24 slides
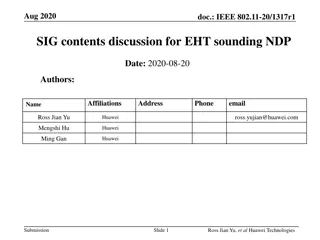
IEEE 802.11-20/1317r1 EHT-SIG Proposal Discussion
The document discusses EHT-SIG for single-user and sounding NDP in IEEE 802.11-20/1317r1, focusing on overflow bits, user fields, CRC, and tail formats. It covers the format details, subfields, and overhead compared to HE sounding, proposing specific bit allocations for different elements. The EHT-S
0 views • 16 slides
Administrator Deletes User - User Management System Storyboard
An administrator navigates through a user list, selects a user for deletion, confirms the action, and successfully removes the user from the system. The process involves interacting with user details, confirming the deletion, and updating the user list accordingly in a structured manner.
1 views • 4 slides
Reliable Data Backup Support in NJ Secure Your Business’s Information
Data Backup Support in New Jersey from Aaryasys.com is dependable, so you can rest easy. Put your trust in our skilled team and never worry about losing vital files again.\n\n\/\/aaryasys.com\/index.php\/backup\/
4 views • 1 slides
Disaster Recovery and Data Backup in Managed IT
Secure your business with reliable disaster recovery and data backup solutions tailored for managed IT services. Stay prepared!\n
1 views • 5 slides
Context Switching and User-Kernel Interaction in Operating Systems
Context switching in operating systems involves a seamless transition between user-level threads without the kernel's awareness. User-level code manages register state and stack pointers, while user-kernel mode switching requires changing processor privilege levels and agreement on information excha
1 views • 25 slides