Maximizing Impact: The Role of Rich Snippets in SERPs"User Intent
User intent, also known as search intent, refers to the underlying goal or purpose a user has when performing an online search. It goes beyond the literal interpretation of keywords and focuses on understanding why a person is searching. Recognizing and catering to user intent is crucial for creatin
3 views • 10 slides
Modeling and Generation of Realistic Network Activity Using Non-Negative Matrix Factorization
The GHOST project focuses on the challenges of modeling, analyzing, and generating patterns of network activity. By utilizing Non-Negative Matrix Factorization (NMF), realistic network activity patterns can be created and injected into live wireless networks. Understanding and predicting user behavi
4 views • 28 slides
Operating Systems
An operating system is a crucial program that manages all other programs on a computer. It handles tasks like input recognition, file management, and device control. There are different types of operating systems such as single-user, single-task systems, multi-user, multi-task systems, real-time ope
6 views • 11 slides
The Evolution of Graphical User Interfaces in Computing
Graphical User Interfaces (GUIs) have transformed computing into a more user-friendly and interactive experience, emphasizing the shift from technology-focused to human-centric living. This chapter delves into the various aspects of GUIs, including I/O alternatives, common GUI tasks, programming per
1 views • 32 slides
Understanding Activity, Pay, and Special Codes in API Terminology
Dive into the terminology surrounding Activity Codes, Pay Codes, and Special Codes within the realm of APIs. Explore how these codes represent different aspects of scheduling, productivity, and payroll management. Gain insights into the distinctions between Activity Codes and Pay Codes, their implic
5 views • 8 slides
Understanding Linux User Capabilities and Namespace Management
Linux user namespaces and capabilities play a critical role in managing system security and permissions. Users and groups are assigned unique IDs, and processes are associated with the user's ID. The kernel enforces permission checks based on user IDs and group IDs, allowing root access to bypass ce
0 views • 14 slides
Understanding Water Activity and Mass Transfer in Food Engineering
Water activity (aw) plays a crucial role in microbial activity, chemical and physical changes in foods, and the dehydration process. Maintaining water activity below specific levels can prevent microbiological spoilage and deterioration reactions, while also affecting texture, aroma, and overall qua
0 views • 11 slides
Understanding Heuristic Evaluation in User Interface Design
Heuristic evaluation is an analytical method where experts evaluate interfaces based on usability principles. This evaluation helps in identifying potential design issues that may impact user satisfaction. The process involves a small group of evaluators reviewing the interface against a set of reco
5 views • 12 slides
Understanding Different Types of Operating Systems
An operating system is the crucial program that manages a computer's resources and acts as an interface between the user and the machine. Various types of operating systems exist, including real-time, multi-user vs. single-user, multi-tasking vs. single-tasking, distributed, and embedded systems. Re
1 views • 11 slides
Implementing Alert Messages and User Input Handling in Java
This tutorial guides you through creating alert messages, handling user input, defining functions, calling functions from the `onCreate` method, and creating an XML file for user data entry validation in Java. Learn how to display alerts for empty user credentials and process user actions accordingl
1 views • 6 slides
Unsupervised Clickstream Clustering for User Behavior Analysis
Understanding user behavior in online services is crucial for businesses. This research focuses on utilizing clickstream data to identify natural clusters of user behavior and extract meaningful insights at scale. By analyzing detailed user logs, the study aims to reveal hidden patterns in user inte
0 views • 19 slides
Domain-Specific Visual Analytics Systems: Exploring Expert User Insights
This presentation delves into domain-specific visual analytics systems focusing on political simulation, wire fraud detection, bridge maintenance, and more. It emphasizes leveraging user expertise for effective system design and evaluation, highlighting the importance of user insights in data analys
0 views • 27 slides
Efficient User Management System for Health Facilities
Record and manage user details effectively with the new Version 2.0 User Management feature. RNTCP has now registered over 35,000 PHIs, 140,000 Private Health Facilities, 15,000 Private Labs, 31,000 Private Chemists, across 700 Districts and 8,000 TUs in Nikshay. Enhance operations by editing TU pro
0 views • 26 slides
User Roles and Responsibilities Overview
The user roles within the application are categorized into Account Manager, Data Steward, and Common Functionality roles. Each role comes with specific responsibilities such as managing user accounts, database management, data stewardship, incident management, and more. Non-privileged roles provide
0 views • 11 slides
Understanding Agile User Stories in Software Development
Agile user stories play a crucial role in software development by providing short descriptions of features desired by customers in a language they understand. This method allows for agile planning, efficient documentation, and effective communication between development teams and clients. Extracting
0 views • 30 slides
Exploring Usability Testing of New Interface in JMP Custom Design
In this study by Mark Bailey et al. from JMP Statistical Discovery in the USA, the focus lies on testing the usability of a new user interface using JMP Custom Design. The researchers highlight the significance of adding factors in the initial experiment design workflow to enhance user experience. U
0 views • 8 slides
Guide to Court Management System User Administration
Learn how to effectively manage user profiles, create sub-user accounts for legal assistants, update user information, and create associates' accounts in the Court Management System for the 17th Judicial Circuit Court of Florida. Detailed instructions provided for changing usernames, passwords, and
0 views • 15 slides
Enhancing User Experience Through Data Trails and Metrics
Andrea Thompson, a Sr. User Experience Manager at The Home Depot, highlights the importance of measuring and analyzing user experience metrics to understand and improve customer interactions. By investigating data trails from various touchpoints, such as customer sign-ups, interactions with associat
0 views • 17 slides
Guide to Using Edconnect 8.3 for Data Transmission and Security Management
Explore the key features of Edconnect 8.3 including security group management, data transmission processes, activity logging, and user access rights configuration. Learn how to effectively utilize Edconnect for secure data transmissions, manage user groups and access rights, and maintain activity lo
0 views • 14 slides
Adherence to 2008 Physical Activity Guidelines & Mortality Study
This study explores the association between adherence to the 2008 Physical Activity Guidelines for Americans and all-cause mortality. It analyzes data from the NHIS and NDI to assess the risks associated with aerobic and muscle-strengthening activities. The primary objective is to evaluate mortality
0 views • 29 slides
Understanding User Identity and Access Tokens in Windows Security
Delve into the intricate world of user identity and access tokens in Windows security. Explore how user identities are represented, the structure of access tokens, and the significance of processes running under different user contexts. Gain insights into advanced Windows security principles and lea
1 views • 13 slides
Understanding User and Group Permissions in Linux Systems
Linux uses user and group permissions to control access to files, directories, and peripherals. Users are managed for security purposes by limiting access, with the root user having full system access. Grouping users into groups with specific access grants can enhance security. Each file is owned by
0 views • 23 slides
Understanding Activity Diagrams and State Chart Diagrams
Activity diagrams describe the workflow behavior of a system by showing the sequence of activities performed, including conditional and parallel activities. Elements such as Initial Activity, Symbol Activity, Decisions, Signals, Concurrent Activities, and Final Activity are depicted in these diagram
0 views • 10 slides
Evolution of User Authentication Practices: Moving Beyond IP Filtering
The article explores the obsolescence of IP filtering in user authentication, highlighting the challenges posed by evolving technology and the limitations of IP-based authentication methods. It discusses the shift towards improving user experience and addressing security concerns by focusing on user
0 views • 22 slides
Introduction to Graphical User Interfaces (GUIs) in Python for Geographical Information Analysis
This content provides insights into creating Graphical User Interfaces (GUIs) in Python for Geographical Information Analysis. It covers the basics of GUI development using TkInter and event-based programming with a focus on user experience design and functionality. The lecture emphasizes the import
0 views • 45 slides
Importance of Human-Computer Interaction (HCI) in User Interface Design
Human-Computer Interaction (HCI) is a crucial discipline focusing on creating interactive computing systems that are user-friendly and efficient. This involves designing, evaluating, and implementing systems that cater to users' needs, ultimately improving user satisfaction and productivity. The fie
0 views • 39 slides
The Evolution of Cheerleading: From Yelling to Intense Physical Activity
Cheerleading ranges from yelling to intense physical activity, incorporating tumbling, dance, jumps, cheers, and stunting to motivate sports teams and entertain audiences. Originating in the United States, it has evolved from an all-male activity to a predominantly female sport with some co-ed teams
0 views • 9 slides
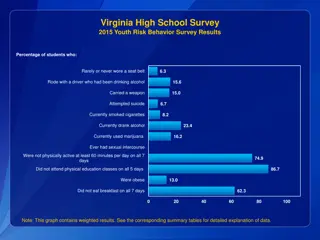
Virginia High School Survey 2015 Youth Risk Behavior Results
The Virginia High School Survey 2015 presented data on various risky behaviors among students, including seat belt usage, alcohol and drug consumption, weapon carrying, suicide attempts, physical activity, sexual activity, and more. The results are divided into percentages of students engaging in th
0 views • 4 slides
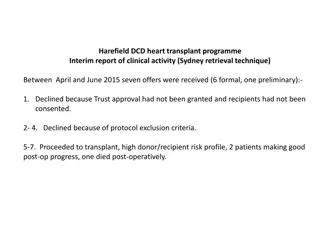
Interim Report of Harefield DCD Heart Transplant Programme Clinical Activity
The interim report highlights the clinical activity of the Harefield DCD Heart Transplant Programme, showcasing the feasibility of DCD heart transplantation using various methods. The report discusses donor/recipient risk profiles, feedback from medical teams, and the potential impact on national tr
0 views • 7 slides
User Interface Design Principles in Human-Computer Interaction
User interface design principles are crucial in Human-Computer Interaction. This content highlights key principles such as aesthetics, anticipation, autonomy, and color consideration for users with color blindness. It emphasizes the importance of user testing, user autonomy, and providing essential
0 views • 24 slides
Understanding Factors Affecting Enzyme Activity in Biochemistry
Enzyme assays measure substrate conversion to product under varying conditions like cofactors, pH, and temperature. Enzyme velocity represents the rate of a catalyzed reaction, typically reported as V0. Enzyme activity is expressed as mol of substrate transformed per minute, with enzyme unit and kat
0 views • 18 slides
Understanding Interaction Design in Human-Computer Interaction
Interaction design focuses on creating interactive products that are easy, effective, and enjoyable to use. It aims to reduce negative user experiences while enhancing positive ones. Designing interactive products requires understanding user activities, interfaces, and device arrangements to support
0 views • 11 slides
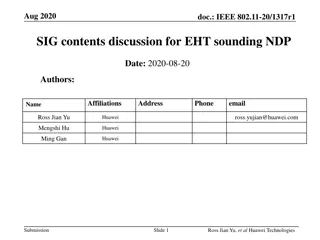
IEEE 802.11-20/1317r1 EHT-SIG Proposal Discussion
The document discusses EHT-SIG for single-user and sounding NDP in IEEE 802.11-20/1317r1, focusing on overflow bits, user fields, CRC, and tail formats. It covers the format details, subfields, and overhead compared to HE sounding, proposing specific bit allocations for different elements. The EHT-S
0 views • 16 slides
Understanding NUcore User and Account Management System
NUcore is a transaction processing system for core facilities at Northwestern University, comprising key components like Products, Payment Sources, and People roles. The system involves managing user accounts, payment sources, and different system roles such as Global Admins, Core Staff, and Purchas
0 views • 11 slides
Optimizing User Behavior in Viral Marketing Using Stochastic Control
Explore the world of viral marketing and user behavior optimization through stochastic optimal control in the realm of human-centered machine learning. Discover strategies to maximize user activity in social networks by steering behaviors and understanding endogenous and exogenous events. Dive into
0 views • 15 slides
Administrator Deletes User - User Management System Storyboard
An administrator navigates through a user list, selects a user for deletion, confirms the action, and successfully removes the user from the system. The process involves interacting with user details, confirming the deletion, and updating the user list accordingly in a structured manner.
0 views • 4 slides
User Interface vs User Experience: Understanding the Essentials
Exploring the distinctions between User Interface (UI) and User Experience (UX) in human-computer interaction design. UI focuses on the space of interaction between humans and machines, while UX encompasses users' behavior, attitude, and emotions towards a product or service. The goal is to create i
0 views • 63 slides
Activity Leader Guidelines for Volunteers
Welcome to the role of a leader, driver, or bus captain! As a leader, it is essential to familiarize yourself with the provided leader packets, understand the details of the activity, and prioritize safety. Taking pride in being a leader, owning the activity before the event, ensuring your packet is
0 views • 25 slides
Direct Experience Storyboards for User Engagement
Visual guide for simulating user experiences when direct user involvement is not feasible. Utilize photo-narrative storyboards to capture firsthand activity interactions. Ideal for understanding user perspectives and enhancing design solutions.
0 views • 9 slides
Understanding Context Switching and User-Kernel Interaction in Operating Systems
Context switching in operating systems involves a seamless transition between user-level threads without the kernel's awareness. User-level code manages register state and stack pointers, while user-kernel mode switching requires changing processor privilege levels and agreement on information excha
0 views • 25 slides