Enhancing Security with Two-Factor Authentication in Funding & Tenders Portal
Increase in cybersecurity threats necessitates the use of two-factor authentication in the Funding & Tenders Portal to safeguard valuable information. Users are encouraged to adopt this secure login method, which will soon become mandatory. Methods such as mobile devices, SMS, and security keys are
2 views • 31 slides
Guide to Setting Up EU Login and Two-Factor Authentication
Learn how to create your EU Login account and add two-factor authentication for accessing Europass and other EU services. Follow step-by-step instructions to register, verify your email, and set up a secure password. Ensure a seamless process by understanding the difference between Europass and EU L
4 views • 18 slides
Two-Step Authentication Implementation for Enhanced Security
Learn about the implementation of two-step authentication at a university to combat phishing attacks and enhance security. Discover how Duo Security was used to provide a seamless two-step authentication solution, the challenges faced during the enrollment tool setup, and the successful implementati
1 views • 10 slides
Leadership, Trust, and Crisis: Lessons from Central Europe Project
The project funded by multiple governments in Central Europe aims to advance sustainable regional cooperation. The initiative focuses on understanding leadership as a process involving trust, especially in crisis situations. The lesson structure includes case studies, discussions on resources, and e
4 views • 19 slides
Implementing 2FA for UW Azure AD: Best Practices and Options
Explore the implementation of two-factor authentication (2FA) for UW Azure Active Directory (AD) based on key decisions and options outlined in the provided slides. Understand the strategies for enforcing MFA, handling legacy authentication, and transitioning to cloud-based authentication. Discover
3 views • 19 slides
Digital Twin for Green Shipping Project Overview
The Digital Twin for Green Shipping (DT4GS) project, funded by the Horizon Europe framework programme, aims to make Digital Twin technology accessible to the shipping industry to facilitate a faster transition to zero emissions. The project focuses on open ship operational optimization, a multi-stak
1 views • 11 slides
Security and Authentication in Electronic Filing Systems: Arkansas Subcommittee Report
Explore the subcommittee report on security and authentication in electronic filing systems for campaign and finance reports in Arkansas. Learn about user authentication, risks, mitigation strategies, and approaches used in other states. Discover the filing processes in both paper and electronic for
2 views • 24 slides
DAVA Drugs Authentication & Verification Application by National Informatics Centre
The DAVA Drugs Authentication & Verification Application, developed by the National Informatics Centre of the Government of India, enables authentication, tracking, and tracing of Indian drugs at different packaging levels. Manufacturers maintain Unique Serial Numbers for primary and secondary packa
2 views • 42 slides
Setting Up Two-Factor Authentication for HRMS Access
Learn how to enhance HR system security by setting up two-factor authentication for off-campus access. This tutorial covers the importance of two-factor authentication, using your phone as a second layer of security, initial setup procedures through Wyoweb, requesting permission for HR self-service
1 views • 9 slides
Trust and Equitable Charges in Property Law
Trust and equitable charges in property law involve a legal obligation where the property holder manages the property for the benefit of another person. This trust relationship consists of elements like legal title, trust property, and beneficiaries. The creators of a trust can be referred to as set
0 views • 25 slides
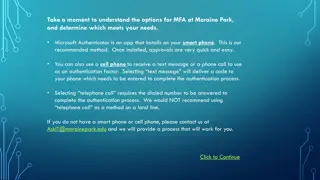
Setting Up Multi-Factor Authentication at Moraine Park
Explore the options for setting up Multi-Factor Authentication (MFA) at Moraine Park, with Microsoft Authenticator as the recommended method. You can choose between using the Microsoft Authenticator app on a smartphone, receiving a text message, or a phone call for authentication. Detailed steps for
1 views • 16 slides
Authentication Mechanisms and Security Vulnerabilities
Authentication lies at the core of application security, serving as the primary defense against malicious attacks. This article explores various authentication technologies, including HTML forms-based authentication, multi-factor mechanisms, client SSL certificates, and more. It delves into common d
0 views • 70 slides
An Open-Source SPDM Implementation for Secure Device Communication
This article introduces an open-source SPDM (Secure Protocol and Data Model) implementation for secure device communication, developed by Jiewen Yao and Xiaoyu Ruan, Principal Engineers at Intel. SPDM aims to enhance device security through protocols for device authentication, session key establishm
1 views • 29 slides
Authentication and Authorization in Astronomy: A Deep Dive into ASTERICS
Explore the world of authentication and authorization in the field of astronomy through the lens of the ASTERICS project. Learn about the importance of verifying identities and granting access rights, the Virtual Observatory Approach, Single Sign-On standards, and Credential Delegation protocols. Di
0 views • 9 slides
Evolution of User Authentication Practices: Moving Beyond IP Filtering
The article explores the obsolescence of IP filtering in user authentication, highlighting the challenges posed by evolving technology and the limitations of IP-based authentication methods. It discusses the shift towards improving user experience and addressing security concerns by focusing on user
1 views • 22 slides
Kerberos Authentication in Network Security
Kerberos is a trusted authentication service for establishing secure communication between clients and servers in a distributed environment. Developed at MIT, it addresses threats like user impersonation and eavesdropping by providing centralized authentication. Kerberos relies on symmetric encrypti
1 views • 13 slides
Secure Authentication Using ISO 15693 RFID Tags
The authentication process with ISO 15693 tags involves generating a signature using a hash of the tag UID and a private key. This signature, programmed during manufacturing, must match with the one generated by the reader for successful authentication. Advantages include enhanced security with priv
1 views • 7 slides
Uncovering Flaws in Authentication Solutions: A Privacy Concern
Delve into the potential privacy risks posed by design flaws in authentication solutions, as discussed by security consultant David Johansson. Explore scenarios where digital identities can be compromised, the implications of exposed electronic IDs, and the urgent need for software updates to safegu
0 views • 34 slides
Authentication and Authorization in Information Assurance
Explore the concepts of authentication and authorization in information assurance through a series of visuals and explanations provided by Adam Doup from Arizona State University. Learn about authentication terms, mechanisms, password systems, and UNIX standard hash functions. Gain insights into how
1 views • 26 slides
ASP.NET Web API Security and Authentication Overview
Explore the essential elements of ASP.NET Web API security, including HTTPS transport security, authentication filters, access to client identities, and OWIN middleware. Learn about securing your Web API with integrity protection, replay protection, and encryption for confidentiality. Dive into the
1 views • 29 slides
Modular Security Analysis for Key Exchange and Authentication Protocols
Explore the modular security analysis approach used to examine the security of key exchange and authentication protocols, focusing on the universally composable authentication with a global Public Key Infrastructure. The analysis involves splitting the system into smaller components, separately anal
1 views • 15 slides
Clinical Practice Guidelines for Twin-Twin Transfusion Syndrome by Society for Maternal Fetal Medicine
This clinical practice guideline by the Society for Maternal Fetal Medicine provides recommendations for the diagnosis and management of twin-twin transfusion syndrome (TTTS). Key points include criteria for TTTS diagnosis, the usefulness of the Quintero staging system, the importance of serial sono
0 views • 18 slides
Twin Soul Mates Love
Don\u2019t confuse Soul Mates with Twin Flame in your love life, these two are widely misunderstood as the same. Tonya Somers will help you attract your Twin Flame by breaking some unhealthy patterns of attracting wrong soul mates. If not the twin fl
1 views • 6 slides
Authentication and Message Authentication in Network Security
Authentication is crucial in establishing identity in the digital world to access rights, products, and services. It involves validating credentials to prove identity and ensure security. Message authentication confirms the integrity and origin of transmitted data, preventing alteration or unauthori
0 views • 24 slides
Authentication in Networking Environments
Authentication is a crucial process in computer networks where clients prove their identity to servers. This article covers the concept of authentication, its importance, and specific guidance on network authentication, particularly focusing on Windows and Linux VMs. Key topics include the use of pa
0 views • 30 slides
Web Synergies Digital Twin Solutions
Explore how Web Synergies' Digital Twin Solutions, including Asset Twin, asset management with 3D modeling, data integration, and monitoring across industries.
4 views • 7 slides
Flame Soul Mates
Don\u2019t confuse Soul Mates with Twin Flame in your love life, these two are widely misunderstood as the same. Tonya Somers will help you attract your Twin Flame by breaking some unhealthy patterns of attracting wrong soul mates. If not the twin fl
2 views • 2 slides
Electronic Mail Security: PGP and S/MIME
Explore the world of Electronic Mail Security through the lenses of two prominent systems - PGP and S/MIME. Learn about the origins of PGP encryption, the authentication and confidentiality problems it addresses, and the utilization of S/MIME in business and personal electronic mail. Discover the ke
0 views • 10 slides
Digital Twin Market Revenue Share, Key Players, & Regional Analysis
The global digital twin market is projected to reach $1,036.4 billion by 2033 from $10.3 billion in 2023, growing at a CAGR of 58.52% during the forecast period 2023-2033.\n\nRead Report Overview: \/\/bisresearch.com\/industry-report\/digital-twin-ma
1 views • 4 slides
Trust Metric Estimator: Computational Model for Trustworthiness Assessment
The Trust Metric Estimator project aims to create a computational model to estimate user trust levels towards system performance over time. It considers social and technical factors, integrating trust, trustworthiness, and economic aspects to aid decision-making. Research includes surveys to identif
2 views • 8 slides
Trust Evaluation Process in Tribal Compacts and Trust Funds Administration
Trust Evaluations are mandated under the Tribal Self Governance Act for Tribes engaging in trust programs. The Bureau of Trust Funds Administration conducts these evaluations, focusing on compliance with federal laws and safeguarding trust assets. The process includes questionnaires, reviews, and re
0 views • 13 slides
Trust Dynamics in Political Relationships: Evidence and Implications
Exploring the intricate dynamics of trust between Principals and Agents in political relationships, this study delves into the implications of mistrust and the shift in trust levels over time. Utilizing surveys on political trust and data on trust in governmental branches, the analysis sheds light o
0 views • 22 slides
Scalable Cryptographic Authentication for High Performance Computing
This work discusses the scalable cryptographic authentication approach developed by Andrew Prout and team for high-performance computing. The LLGrid system architecture, challenges with interactive supercomputing, and utilization of LLGrid for various computing tasks are explored, highlighting the i
0 views • 34 slides
Twin Flame Soul Mates Love
Tonya Somers will help you attract your Twin Flame by breaking some unhealthy patterns of attracting wrong soul mates. If not the twin flame, at least attract someone to go in relationship with a very clean slate. \/\/ \/soul-mate-or-twin-flame\/
1 views • 2 slides
Anti-Shoulder Surfing based Authentication Mechanism using Graphical Passwords
Authentication plays a crucial role in system accessibility, with strong passwords being a major concern. This research focuses on proposing an anti-shoulder surfing mechanism using graphical passwords to enhance security. Existing techniques like Triangle Scheme, Convex Hull, Intersection Scheme, a
0 views • 10 slides
Authentication Overview: Definition and Means
The essential concepts of authentication, including its definition, means, steps, and types like password-based and token-based authentication. Learn about the importance of identification and verification in securing access to systems and the various factors involved in authentication methods.
0 views • 19 slides
Assumptions in Genetic Twin Modeling: Technical and Interpretational Aspects
Genetic twin modeling involves making specific assumptions, some technical and others related to result interpretation. These assumptions, such as similar variances in MZ and DZ twins, play a crucial role in model estimation. Violations of these assumptions can lead to erroneous conclusions. Underst
0 views • 21 slides
Twin Pair Analysis in Simplex Model Research
Conducting a twin pair analysis using data gathered from 562 pairs, including 261 monozygotic and 301 dizygotic twins at various time points. Models such as Saturated Model, ACE Cholesky Model, and Simplex Model were utilized to analyze the observed FSIQ data. The study focused on within-twin cross-
0 views • 26 slides
Introduction to Entity Authentication and Key Establishment Protocols
Learn about entity authentication, key establishment, integrity, message authentication, and confidentiality in network security protocols. Explore the importance of user authentication and different security schemes to ensure data confidentiality and integrity.
0 views • 59 slides
Twin Cities: Gaziantep and Aleppo - A Historical Connection
The cities of Gaziantep and Aleppo, located just about 100 kilometers apart, share a deep historical and cultural connection. Despite the once flourishing relationship, the onset of the civil war in Syria drastically altered the dynamic between the twin cities. Gaziantep has now become a crucial hub
0 views • 29 slides