Understanding Modes of Communication and Verbal Messages
Communication occurs through verbal and nonverbal modes, with messages having denotative and connotative meanings. Verbal messages vary in directness, affecting the effectiveness of communication. Indirect messages offer advantages such as politeness and avoiding offense, but can also lead to misund
0 views • 64 slides
Heartwarming Messages of Thanks and Support from the Community
Heartfelt messages of gratitude and appreciation are shared by various organizations and community members for the efforts of frontline workers during challenging times. The messages highlight the unity, support, and resilience within the community as they come together to ensure the well-being and
0 views • 8 slides
Phishing Survival Guide: Educating Children and Parents
Empower children to identify and respond to phishing attacks with this comprehensive phishing survival guide. The guide includes learning outcomes, lesson notes, and instructions to create an engaging pocket guide for parents. Learn how to report suspicious emails, handle suspicious links, and prote
0 views • 4 slides
Understanding the Importance of Nonverbal Communication in Communication Skills
Nonverbal communication plays a crucial role in conveying messages and signals through platforms like eye contact, facial expressions, gestures, posture, and spatial distance. It includes appearance, body language, silence, time, and space. This form of communication can significantly impact the rec
0 views • 16 slides
Introduction to Public Key Cryptography
Public key cryptography, exemplified by algorithms like Diffie-Hellman and RSA, revolutionizes secure communication by allowing users to encrypt messages with public keys known to all and decrypt them with private keys known only to the intended recipient. This advanced encryption method ensures sec
1 views • 44 slides
Understanding Suspicious Activity Reports (SARs) and the Role of UKFIU in Tackling Illicit Finance
Explore the significance of Suspicious Activity Reports (SARs) in combating illicit finance, with a focus on reporting AML concerns, the role of the UKFIU, and the value of SARs in identifying money laundering activities. Learn about the quality of SARs, reporting breaches of standards and regulatio
0 views • 26 slides
Comprehensive Guide to Automated Export System (AES) Response Messages
Explore a detailed guide on Automated Export System (AES) response messages, covering topics such as common response messages, fatal errors, compliance alerts, and proper actions for different scenarios. Gain insights into ensuring compliance, resolving errors, and understanding the ITN issuance pro
1 views • 29 slides
Enhancing User Productivity with Outlook Actionable Messages
Explore how to develop and deploy Outlook Actionable Messages to optimize user productivity. Join Julie Turner, a seasoned professional developer, in learning about connectors, message creation, API endpoints, security, and more, to create targeted and interactive messages within Outlook. Get a hand
0 views • 18 slides
Phishing Survival Guide: How to Recognize and Respond to Suspicious Emails
Learn how to spot a phishing email and what steps to take if you receive one or fall victim to a phishing scam. Find out how to identify suspicious links, recognize phishing attempts, and protect yourself from giving out personal information or losing money. Stay informed and secure in the digital a
2 views • 5 slides
Understanding Suspicious Transactions and Activities in Financial Investigations
This guidance note by Senior Analyst Westmore Jeffers provides assistance and practical advice on reporting suspicious financial activities. It outlines the legislation, obligations, and definitions related to suspicious transactions and activities. The document emphasizes the importance of vigilanc
0 views • 20 slides
Suspicious Activity Reporting & Beneficial Ownership System Guidelines
Learn about the dos and don'ts of reporting suspicious activities and transactions, understanding beneficial ownership, and the importance of secure search systems. Discover insights on submitting reports, maintaining integrity, and transitioning from reactive to proactive reporting in various secto
0 views • 15 slides
Introduction to Cryptography, Cryptanalysis, and Cryptology
Cryptography involves protecting information by encrypting and decrypting data, while cryptanalysis focuses on breaking encryption methods to access hidden messages. Cryptology encompasses both cryptography and cryptanalysis. Encryption encodes messages to prevent unauthorized access, while decrypti
0 views • 12 slides
Types of Suspicious Messages by Cyber Sprinters and Urgent Call for Assistance
Cyber Sprinters are warning about three types of suspicious messages: Evil Emailers using phishing tactics, Malicious Messenger engaging in smishing, and Phoney Phone Caller utilizing vishing. The South West Constabulary urgently seeks the Cyber Crime Response Unit's help to investigate a group of c
1 views • 7 slides
Emergency Warning System: Important Messages Sent Directly to Mobile Telephones
The Emergency Warning System sends critical messages directly to mobile phones to ensure public safety. Users will receive alerts with vibrating, siren-like sounds and text messages informing them of any ongoing situation and necessary actions. A test is scheduled for Wednesday, 14th June at 12:00 t
0 views • 5 slides
Understanding Micro-Inequities in the Workplace
Exploring the concept of micro-inequities, this presentation delves into the subtle messages that devalue individuals, discussing their impact, forms, communication role, and conversion into positive affirmations. Highlighted are the reasons for learning about micro-inequities, emphasizing diversity
1 views • 17 slides
Understanding Micromessaging: Hidden Impact of Subtle Behaviors
Micromessaging refers to the subtle, semi-conscious messages we send through our behaviors, both verbal and physical, that influence our interactions with others. These messages, categorized as micro-affirmations and micro-inequities, can have a significant impact on individuals. The concept delves
1 views • 17 slides
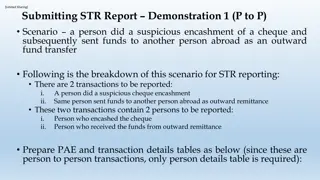
Demonstration: Reporting Suspicious Transactions and Persons for STR
Demonstrating the process of reporting suspicious cheque encashment and outward fund transfer transactions involving two individuals - one who encashed the cheque and the other who received funds abroad. Includes detailed person and transaction information for both instances, along with the preparat
0 views • 41 slides
Positive Messages for Encouragement and Growth
Empower yourself with inspirational messages about resilience, courage, kindness, and self-improvement. Encouraging individuals to bounce back from setbacks, be brave, make mistakes, and nurture a growth mindset. Remind yourself that smiling, apologizing, and facing challenges head-on are essential
0 views • 39 slides
Mastering Data-Driven Messages for Effective Communication
Unlock the power of data-driven messages to create impactful communication outcomes. Learn how to craft messages that inspire action and drive results through compelling storytelling. Explore the key elements of a message platform and harness the importance of data in shaping your message strategy f
0 views • 59 slides
Co-created Messages & Trusted Messengers for COVID-19 Vaccine Acceptance in Northern Nigeria
Dr. Chizoba Wonodi is evaluating the use of co-created messages and trusted messengers to improve COVID-19 vaccine acceptance in Northern Nigeria. Vaccine hesitancy due to conspiracy theories and safety concerns remains a challenge. TM-COVAC study aims to design targeted messages using human-centere
0 views • 8 slides
Understanding SMTP - Simple Mail Transfer Protocol
SMTP (Simple Mail Transfer Protocol) is a fundamental component of the application layer in computer networks. It is used for sending electronic mail messages between servers and user agents. The process involves user agents composing messages, connecting to mail servers, and transferring messages o
0 views • 29 slides
Inspirational Images and Messages from Harlem
Explore a collection of images and messages showcasing the beauty and community spirit of Harlem. From the historic Elmendorf Reformed Church to expressions of teamwork and hard work, these visuals reflect a culture of giving back and unity in the neighborhood. Feel inspired by the messages of hope,
0 views • 7 slides
Reported Conversations and Text Messages Example
This content highlights examples of reported speech in text messages, featuring various emotional expressions and conversations between two individuals. The provided text messages show dialogues involving feelings, requests, and decisions, which can serve as a practice exercise for reporting convers
0 views • 6 slides
Effective Strategies for Media Interactions: Tips, Key Messages, and More
Discover tips for interacting with print and television media, key messages about ACMS, and strategies for reinforcing mission and values. Learn how to handle interviews, turn questions towards key messages, and work effectively with reporters to create compelling news angles.
0 views • 28 slides
Cryptography in the Bounded Storage Model: Revisited - Eurocrypt 2023
Cryptography researchers revisit the Bounded Storage Model (BSM) to enhance security in transmitting messages while considering limited storage capacities. The BSM restricts adversaries to limited storage, enabling unconditional security. The model aims to address challenges in message transmission
0 views • 16 slides
Optimization Strategies for MPI-Interoperable Active Messages
The study delves into optimization strategies for MPI-interoperable active messages, focusing on data-intensive applications like graph algorithms and sequence assembly. It explores message passing models in MPI, past work on MPI-interoperable and generalized active messages, and how MPI-interoperab
0 views • 20 slides
Employee Vigilance Campaign: Strengthening Security Awareness in the Workplace
This employee vigilance campaign emphasizes that security is everyone's responsibility. It aims to raise awareness about hostile reconnaissance, educate staff on identifying suspicious behavior, and promote a culture of vigilance. Through various mediums like briefings, posters, and reminders, the c
0 views • 7 slides
Community Health & Wellness Messages from University of Hawai'i CHL Program
Community messages promoting healthy habits, such as encouraging kids to drink more water with fun flavors and keeping cool water readily available. Multiple messages shared by Dr. Rachel Novotny from the University of Hawai'i and the College of Tropical Agriculture and Human Resources. Contact info
0 views • 26 slides
Cybersecurity Awareness: Phishing Investigations Practitioner Notes and Game Instructions
This content focuses on teaching children to identify phishing tactics used by individuals and organizations through activities and lesson notes. It emphasizes recognizing scam attempts, understanding safe online practices, and evaluating suspicious messages. The interactive game instructions instru
0 views • 4 slides
COVID-19 Vaccination Programme for Childbearing Women - Educational Slides and Key Messages
This presentation focuses on the COVID-19 vaccination programme for childbearing women, providing information on learning objectives, key messages, and current vaccination programmes for pregnant and breastfeeding women. It discusses the understanding of COVID-19 symptoms, the importance of vaccinat
0 views • 24 slides
Deconstructing Media Messages: Key Concepts and Techniques
In media literacy, deconstructing media messages involves closely examining and dissecting TV shows, newspapers, movies, advertisements, etc., to understand their creators' intentions, biases, and hidden meanings. Key concepts include analyzing the source, text, subtext, audience, and persuasion tec
0 views • 19 slides
Messages of Hope and Faith Through Images
These images convey messages of hope, faith, and assurance of victory through challenging times. They depict themes of freedom, joy, safety, and the presence of Beloved Jesus. The visuals inspire courage, faith, and a sense of assurance that one is never alone, accompanied by powerful messages of lo
0 views • 10 slides
Working with SMS Messaging in Android Applications
Explore how to send and receive SMS messages programmatically within your Android application. Learn about utilizing the built-in Messaging application, sending SMS messages using Intents, and managing SMS messaging capabilities programmatically without user intervention. Discover techniques for sen
1 views • 29 slides
Understanding Semantic Aspects of Interpretation
Explore the semantic structure of oral messages, distinctions between meaning, sense, and semantics in linguistics, and the role of context in interpreting linguistic units. Discover how interpreters render sense in speech acts, the proposition as a picture of the world, and the components of verbal
0 views • 36 slides
Effective Communication with APRS via Emails and Text Messages
Discover how to utilize APRS for seamless communication through emails and text messages. Learn about sending and receiving messages, establishing accounts, confirming deliveries, and more using this innovative technology. Enhance your communication capabilities with APRS today!
0 views • 15 slides
Emergency Data Distribution Network (EDDN) Information and Updates
The Emergency Data Distribution Network (EDDN) is a system that receives data independently of Wallops Island and distributes it efficiently. Recent updates include receiving LRIT data feeds and becoming CS2 compliant. EDDN offers web services for accessing messages based on criteria and a public we
0 views • 9 slides
Understanding the Core Teachings of the Three Angels' Messages
Delve into the profound significance of the Three Angels' Messages as a foundational aspect of Seventh-day Adventist beliefs. Explore the theological and personal implications of these messages on individual spiritual growth and the broader Adventist community. Gain insights into the core doctrinal
0 views • 40 slides
The Art of Iconography: Conveying Messages Through Symbols
British typographer Margaret Vivienne Calvert revolutionized road sign design with simple yet meaningful pictograms. She created iconic symbols like 'men at work' and 'schoolchildren nearby.' This approach, known as iconography, allows for easy communication of complex messages internationally. Chal
0 views • 13 slides
Compliance Testing by ERA for IT Systems Developed and Deployed for TAF TSI
Compliance testing for IT systems developed and deployed for TAF TSI involves checking if messages comply with TAF XSD and basic parameters, assessing compliance of IT tools against TSI requirements, and issuing compliance assessment reports. The process includes testing messages for mandatory eleme
0 views • 4 slides
WhatsApp Scheduler How to schedule WhatsApp messages
Scheduling WhatsApp messages is an indispensable tool for business owners and professionals. This feature allows you to automatically send messages at a specific time, which is extremely useful for a variety of situations. Imagine you need to send pa
0 views • 10 slides