Airport Security Market to be Worth $25.27 Billion by 2031
\u00ae, the airport security market is projected to reach $25.27 billion by 2031, at a CAGR of 8.6% from 2024 to 2031. Some of the major factors driving the growth of this market are stringent government regulations for airport security and the growing number of air passengers. In addition, increasi
6 views • 5 slides
KEERTHI SECURITY - Best Security Agencies In Bangalore
Keerthi Security is a security and facility management services provider in Bangalore. We are committed to offering top-notch security services for commercial and residential places. We aim to offer very secure and reliable security services to everyone. Our best-trained security guards are very sha
9 views • 11 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
0 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Understanding the Role of Security Champions in Organizations
Security Champions play a vital role in decision-making concerning security engagement, acting as a core element in security assurance processes within a team. They foster a security culture, reduce dependency on the CISO, and promote responsible autonomy and continuous security education in the org
3 views • 13 slides
Matrimonial Profiles - Seeking Companionship in Diverse Backgrounds
Explore a diverse range of matrimonial profiles featuring individuals of different Hindu backgrounds and citizenships, all seeking compatible partners. From medical professionals to teachers, these profiles showcase individuals with varied interests and aspirations for a happy union. Discover potent
1 views • 29 slides
Colorado State Epidemiological Profiles - Substance Abuse Trends & Response Task Force
The Colorado State Epidemiological Profiles provide a state-level overview of data from various surveillance sources for prevention, intervention planning, monitoring, and evaluation. The profiles cover demographics, alcohol, marijuana, opioids, sustainability, and next steps. Updated every 2 years,
0 views • 12 slides
Understanding Epidemiological Profiles in Public Health Practice
Epidemiological profiles play a crucial role in substance abuse and mental health planning, helping professionals prioritize issues and raise awareness. The profiles include quantitative and qualitative data to analyze behavioral risk factors, consumption patterns, and clinical outcomes, sourced fro
1 views • 13 slides
Efficient Staffing Strategies for Nursing Units
Implementing effective staffing templates, self-scheduling options, and allowable overstaffing on specialized profiles can enhance data reporting accuracy and ensure adequate nurse coverage. Additional tips for accurate staffing numbers include adjusting profiles, managing floaters, and handling sta
0 views • 5 slides
Understanding PeopleSoft Security: A Comprehensive Guide
Explore the intricacies of PeopleSoft security, including user profiles, roles, permission lists, and the importance of business process-based role design. Discover how security safeguards Personally Identifiable Information (PII) data, the significance of ZC/ZZ/ZD roles, and the role of SACR securi
4 views • 41 slides
Understanding the Roles of a Security Partner
Learn about the roles and responsibilities of a Security Partner, including requesting changes to security roles, approving security requests, and initiating access requests. Explore the overview of Workday Security, the security access request process, and the pre-request process flow. Discover how
1 views • 17 slides
Utilizing PARE Platform for Student Placements in Leeds
The PARE platform is a cloud-based system used in Leeds for managing student placements. Practice Supervisors, Assessors, and Educators play key roles in supporting students through PARE by maintaining profiles, accessing training, and ensuring accurate records. Practice Education Leads are responsi
0 views • 8 slides
Comprehensive Overview of EAL Profiles and Strategies for Language Skills Assessment
EAL Profiles offer a versatile tool for assessing pupils' language skills and setting targets. They can replace Form 1 documents, aid in transition planning, update progress profiles, and inform teaching strategies. These profiles include sections for pupil information, progress overview, review tab
0 views • 10 slides
Understanding Security Categorization of Information Systems
Explore the concept of security categorization for information and information systems, including its purpose, methodology, key references, and policy statements. Discover how organizations establish protection profiles and assign control settings based on data categories. Learn about the importance
5 views • 10 slides
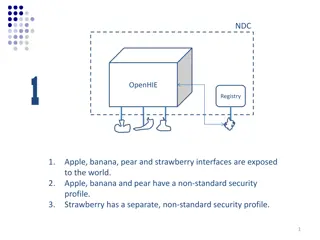
Comparison of Security Profiles in OpenHIE Registries
OpenHIE exposes interfaces with varying security profiles - non-standard in Scenario 1, standards-based in Scenarios 2 and 3. Scenario 1 requires managing multiple non-standard profiles, whereas Scenarios 2 and 3 facilitate plug-and-play with standard security protocols. Implications include ease of
4 views • 6 slides
Understanding Soil Profiles in Agricultural Science
Soil profiles are essential for classifying soils, with main profiles being Brown Earth, Podzol, and Gley. It's crucial to draw these profiles accurately for exams, considering horizons like O Horizon, A Horizon, B Horizon, and Bedrock. Brown Earth has a thick O horizon with uniform brown color, Pod
1 views • 8 slides
Efficient User Management System for Health Facilities
Record and manage user details effectively with the new Version 2.0 User Management feature. RNTCP has now registered over 35,000 PHIs, 140,000 Private Health Facilities, 15,000 Private Labs, 31,000 Private Chemists, across 700 Districts and 8,000 TUs in Nikshay. Enhance operations by editing TU pro
0 views • 26 slides
Learn about Rainforest Animals and Create Animal Profiles
In this activity, students will explore the characteristics of animals found in the rainforest such as the parrot, leopard, orangutan, toucan, and more. They will create animal profiles with their partner using German sentences. The profiles will include information on the animals' body parts, respi
0 views • 10 slides
EPA Oil and Gas VOC Speciation Improvement Efforts
EPA's VOC Speciation transforms inventory species into Air Quality model species to support chemistry, ozone, and aerosol chemistry. The Speciate4.5 update in 2016 added oil and gas profiles, including location-specific uncontrolled profiles and WRAP profiles for various basins. The Uinta TMSR profi
2 views • 10 slides
Understanding Security in World Politics
Security studies delve into the intricate processes of defining and addressing security threats in global politics. It explores the contested nature of security definitions, emphasizes the political significance of security, and challenges the conventional boundaries of International Relations. The
0 views • 8 slides
Comprehensive Course Review: Security Research Cornerstones at Carnegie Mellon University
Dive into the essential topics of software security, network security, OS security, and cryptography in the course offered by Vyas Sekar at Carnegie Mellon University. Explore control flow hijacks, cryptography terminology, and the importance of network security in protecting data transmissions. Lea
0 views • 41 slides
Inspection Profiles of Largest Children's Homes Providers - August 2018
Explore the inspection profiles of the largest private and voluntary providers of children's homes as of August 2018. Gain insights into ownership and inspection outcomes of over 500 homes, highlighting key organizations and national comparisons. Dive into the varying inspection profiles and outcome
0 views • 5 slides
Understanding Wind Profiles and Aerodynamic Roughness Length
Wind profiles are crucial in understanding how wind speed changes with height in the boundary layer. The logarithmic and power law profiles depict this relationship, influenced by surface characteristics and obstacles. The aerodynamic roughness length, defining where wind speed becomes zero, remains
0 views • 14 slides
UIC Security Division Overview and International Activities
The UIC Security Division plays a crucial role in supporting the security platform of the International Union of Railways (UIC). Headed by Jacques Colliard, the division is based in Paris and consists of key personnel like Marie-Hélène Bonneau, Jos Pires, and Laetitia Granger. The division's activ
0 views • 12 slides
Evolution of Collisionless Plasma Bounded by Absorbing Walls
Study on the evolution of collisionless plasma between absorbing walls, analyzing rarefaction waves, density profiles, and plasma potential decay. Kinetic simulations reveal gas dynamics-like behavior with flat density profiles and linear velocity profiles leading to asymptotic decay. The influence
0 views • 15 slides
Understanding Traffic Light Profiles for Special Educational Provision
Traffic Light Profiles are tools used to support children with special educational needs by setting termly targets and strategies to help them reach their potential. These profiles are created in consultation with the SENDCO and class teacher, with a focus on addressing the child's needs and trackin
0 views • 6 slides
Automating Security Operations Using Phantom
Isabella Minca, an intern for 4 months in the Security Team at Adobe, presents an overview of automating security operations using Phantom. The presentation covers goals, security alerts, Phantom playbooks, handling security data, and the capabilities of Phantom in orchestrating security responses.
0 views • 28 slides
Evolution of TLS Security Profiles and Best Practices
TLS security profiles have evolved with the introduction of new profiles, retirement of old ones, and emphasis on non-downgrading best practices. Motivated by changes in security threats and cryptographic methods, the IETF has issued recommendations to ensure secure connections using TLS 1.2. The ne
0 views • 5 slides
Understanding Lawson Security: Basics, Hierarchy, and Administration Tools
This comprehensive guide covers essential aspects of Lawson Security, including an overview of security components, user roles, secured objects, and implementation methodology. Learn about the hierarchy structure, what can be secured, rules, and the tools available for security administrators and RM
0 views • 28 slides
Understanding HTTP Security Headers for Web Apps
Explore the importance of HTTP security headers on web applications through a detailed breakdown of headers like HSTS, XFO, XSS, CSP, CTO, RH, and FP. Learn how these headers enhance security by instructing browsers on handling website content, preventing various attacks. Gain insights on configurin
0 views • 68 slides
REST Interface for HORUS.AI Platform - Tutorial Highlights
This tutorial delves into creating profiles and users using the ProfileManager service in the HORUS.AI platform. It covers steps like creating new profiles, adding users to profiles, and setting rules. The focus is on providing a REST interface for seamless interaction with the HORUS.AI system. The
0 views • 15 slides
Insights from Discussions with Admissions Officials on School Profiles, Grading Scales, and Admissions Criteria
Discussions with university officials shed light on the importance of school profiles, grading scale variations, and admissions criteria. Insights include the significance of school profiles, diversity in grading scales, and the role of NHS in the admissions process. Admissions offices consider fact
0 views • 25 slides
International Protection Needs Profiles in the Caribbean
Identified international protection needs profiles for asylum seekers in the Caribbean region, highlighting main countries of origin such as Cuba, Haiti, Jamaica, and Venezuela. Details include specific profiles and protection needs per country, along with recommended actions when encountering indiv
0 views • 10 slides
Colorado Epidemiological Profiles 2021 - Substance Use Data and Analysis
The 2021 Colorado Epidemiological Profiles provide in-depth data and analysis on substance use patterns, impacts, and demographics in Colorado. The profiles cover alcohol, marijuana, opioids, and tobacco, along with special considerations for populations like LGBTQ, veterans, tribal communities, unh
0 views • 19 slides
Modular Security Analysis for Key Exchange and Authentication Protocols
Explore the modular security analysis approach used to examine the security of key exchange and authentication protocols, focusing on the universally composable authentication with a global Public Key Infrastructure. The analysis involves splitting the system into smaller components, separately anal
0 views • 15 slides
Revolutionizing Security Testing with BDD-Security
Explore the innovative approach of Continuous and Visible Security Testing with BDD-Security by Stephen de Vries. Gain insights into how security testing can be integrated seamlessly into modern development practices, shifting the focus from reactive to proactive measures. Learn about the importance
0 views • 33 slides
Comprehensive DevOps Security Training Overview
This Certified DevOps Security Practitioner course provides a deep dive into implementing DevSecOps, integrating security into the DevOps processes. Covering topics like security testing, Docker security, automation, and more, the training aims to equip participants with the necessary skills to embe
0 views • 5 slides
Understanding Security Testing and Architecture
Explore the fundamentals of security testing, computer security goals, software security approach, and security architecture. Learn about securing computer assets, verifying trustworthiness of security mechanisms, and validating security architecture through threat modeling. Enhance your knowledge o
0 views • 57 slides
Creating User Profiles for Product or Service Development
Engage in an exercise outlined on page 130 to craft user profiles for a product or service using a partner, pen, paper, and internet resources. Follow the provided template to document your findings and focus on your design problem or the Designing Space Travel brief. Utilize existing data or genera
0 views • 10 slides