Understanding Secure Act 2.0 Key Provisions
In a detailed report by Dee Spivey and Angie Zouhar, key provisions of SECURE Act 2.0 are outlined, including changes in retirement plans like RMD age increase, employee certification of hardship withdrawals, and more. Secure 1.0 and Secure 2.0 differences, effective dates, and necessary actions for
5 views • 12 slides
Introduction to SFTP & PGP Encryption for Secure Data Transfer
Discover how to ensure reliable data transfer, make informed decisions, and gain a strategic advantage through the use of Secure File Transfer Protocol (SFTP) and Pretty Good Privacy (PGP) encryption. The session includes demonstrations on PGP encryption and SFTP access, along with insights on setti
1 views • 22 slides
Amity School of Engineering & Technology - Java Program Compilation and Execution
Explore the steps for compiling and running a Java program at Amity School of Engineering & Technology. Learn about the compilation and execution process, converting source code into byte code, creating directories, renaming files, and launching command prompts. Dive into the world of Java programmi
1 views • 19 slides
Understanding the Compilation Toolchain in Software Development
Delve into the world of the Compilation Toolchain, from pre-processing to dynamic linking and loading. Explore the functionalities of the preprocessor, compiler, and include guards in C programming. Discover the significance of header files, #define directives, and preprocessor macros in converting
0 views • 40 slides
Ensuring Secure Testing Environments in Oregon Education System
Oregon's Statewide Assessment System (OSAS) emphasizes the critical need for secure testing environments to maintain the validity and accuracy of assessment data. This includes handling secure printed test materials, identifying and preventing improprieties, and reporting any irregularities. From ma
2 views • 20 slides
Secure Computation Techniques in RAM Models with Efficient Automation
Explore the automation of efficient RAM-model secure computation techniques, including examples such as secure binary search. Discover how traditional solutions using circuit abstractions can be improved for sub-linear time computation through methods like Oblivious RAM. Learn about techniques such
0 views • 37 slides
Tamper-Evident Pairing (TEP) Protocol for Secure Wireless Pairing Without Passwords
This article discusses the challenges of traditional secure wireless pairing methods that rely on password validation and proposes the Tamper-Evident Pairing (TEP) protocol as a secure in-band solution to protect against Man-in-the-Middle (MITM) attacks. TEP eliminates the need for out-of-band chann
1 views • 40 slides
Federal Green Procurement Compilation (GPC) Overview and Resources
Federal Green Procurement Compilation (GPC) provides an overview of sustainable acquisition policies, applicable federal programs, EPA recommendations, and guidance on identifying environmentally preferable products. It consolidates information on green purchasing requirements, mandatory programs, a
0 views • 10 slides
Compilation Guidance Development for National Accounts
Compilation guidance development for national accounts involves creating manuals, handbooks, and guidance notes to support the compilation of basic economic statistics. This process aims to enhance statistical capacity, address data quality issues, and ensure proper dissemination of information. Res
0 views • 10 slides
Actively Secure Arithmetic Computation and VOLE Study
Exploring actively secure arithmetic computation and VOLE with constant computational overhead at Tel Aviv University. Understanding how functions are represented in secure computation using arithmetic circuits over boolean circuits. Efficiently evaluating arithmetic circuits over large finite field
0 views • 36 slides
Maven - Automate Software Compilation and Deployment
Learn how Maven can simplify your software development process by automating compilation, testing, and deployment tasks. This tool helps manage dependencies, run test cases, and create executable JAR files efficiently. Follow step-by-step instructions to set up Maven, configure your project, and cre
0 views • 12 slides
Accessing and Utilizing CPCSSN Secure Research Environment (SRE)
Learn how to access the CPCSSN Secure Research Environment (SRE) for secure data analysis. Follow steps such as setting up VPN, accessing SQL databases, and establishing ODBC connections for statistical analysis using tools like SAS, R, SPSS, or Stata. Enhance your research capabilities within a sec
0 views • 12 slides
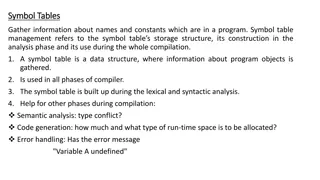
Understanding Symbol Table Management in Program Compilation
Symbol table management is crucial in program compilation as it involves gathering information about names and constants, constructing storage structures, and aiding different phases like lexical and syntactic analysis, semantic analysis, code generation, and error handling. The symbol table serves
0 views • 22 slides
Understanding Computer System Organization and Compilation Process
Explore the intricate details of computer system organization, the compilation process, and the role of components like the preprocessor, compiler, assembler, and linker. Learn how programs are processed and executed, from source code to executable code.
1 views • 47 slides
Enhancing Animal Telemetry Data Systems for Secure Collaboration
Wide spectrum of animal telemetry data collection protocols and platforms require enhanced data stewardship options for secure sharing before public release. The need for a more granular understanding of available data and structured systems integration is crucial. Initial workflow involves providin
0 views • 4 slides
Compilation of Accommodation Statistics for Tourism Development
Compilation of accommodation statistics is crucial for understanding tourism supply, analyzing demand segments, and enhancing tourism development. This process involves identifying different types of accommodations, data collection, and classification of establishments to meet the diverse needs of t
0 views • 23 slides
Energy Data Management and Compilation Overview
This document provides insights into the data management processes related to energy balances compilation, covering aspects such as electricity generation, petroleum products, coal production, gas, and renewable energy data. It details data collection methods, quality control procedures, and prepara
0 views • 8 slides
Evolution of Separate Compilation and Linking in Computing
Separating compilation and linking processes has been crucial for code reusability and program efficiency in computing history. From the early days of manually recalculating addresses to modern linkers and library routines, the evolution has revolutionized how programs are developed and executed on
0 views • 17 slides
STM32WB BLE Secure Connections Overview
This detailed content provides insights into the secure connections in STM32WB BLE devices, covering aspects such as BLE security methods, encryption techniques, pairing processes, key distribution, and security modes and levels. It emphasizes the use of Long Term Keys (LTK), Diffie-Hellman key exch
0 views • 12 slides
Understanding Secure Electronic Transactions (SET)
Secure Electronic Transactions (SET) is an encryption and security specification designed to protect credit card transactions on the Internet. SET provides a secure way to utilize existing credit card payment infrastructure on open networks, such as the Internet, involving participants like clients,
1 views • 6 slides
An Open-Source SPDM Implementation for Secure Device Communication
This article introduces an open-source SPDM (Secure Protocol and Data Model) implementation for secure device communication, developed by Jiewen Yao and Xiaoyu Ruan, Principal Engineers at Intel. SPDM aims to enhance device security through protocols for device authentication, session key establishm
0 views • 29 slides
Exploring Robust Property Preservation for Secure Compilation
This exploration delves into the importance of preserving security properties throughout the compilation process to maintain the integrity and security of software programs. It discusses the challenges posed by adversarial low-level code and the need for secure compilation chains. The focus is on en
0 views • 15 slides
Exploring Secure Care Services in Scotland
Delve into the world of secure care services in Scotland, focusing on achievements, challenges, and opportunities in providing youth justice. Learn about trends in secure care, reduction in costs, reasons for referrals, and evidence-based programs like DBT in Glasgow. Gain insights from industry lea
0 views • 77 slides
Understanding Secure PRFs and PRPs in Cryptography
Dive into the world of secure Pseudo-Random Functions (PRFs) and Pseudo-Random Permutations (PRPs) in cryptography. Learn about the definitions, security criteria, and examples of secure PRFs and PRPs such as 3DES and AES. Explore the concepts of secure block ciphers and key principles behind these
0 views • 54 slides
Irish Mythological Cycle: Lebor Gabála Érenn Compilation
The Lebor Gabála Érenn, a 12th-century compilation, aims to preserve traditional Irish foundation myths, synchronize Irish and Christian myths, and provide Irish myths with Biblical authority. It outlines the arrival of different groups in Ireland, battles against the Fomoire, establishment of kin
0 views • 6 slides
Compilation and Evaluation of Experimental Data for Nuclei in Z=2-28 Region
Completed compilation and evaluation of experimental Pn and half-lives for nuclei in the Z=2-28 region, led by Balraj Singh at McMaster University. The work involved preparing lists of neutron-rich nuclides, identifying potential emitters, analyzing available experimental data for 1n, 2n, 3n, and 4n
0 views • 20 slides
Understanding Scopes and Symbol Tables in Compiler Construction
Scopes and symbol tables play a crucial role in programming languages by regulating the visibility of identifiers and establishing the relationship between binding and applied occurrences. Language issues such as single vs. multiple-pass compilation further impact the implementation of compilers, as
0 views • 26 slides
Typed Assembly Language and Type Inference in Program Compilation
The provided content discusses the significance of typed assembly languages, certifying compilers, and the role of type inference in program compilation. It emphasizes the importance of preserving type information for memory safety and vulnerability prevention. The effectiveness of type inference me
0 views • 17 slides
Municipal Revenue Budget Compilation Details
The document outlines the administrative arrangements for the budget process as per the Municipal Finance Management Act (MFMA) of 2003. It provides guidelines, assumptions, and revenue projections for electricity, water, and sanitation services. Details include consumer breakdowns, tariff adjustmen
0 views • 16 slides
Compilation and Significance of the Holy Quran: A Comprehensive Insight
Delve into the profound exploration of the holy Quran, uncovering its divine revelations, stages of compilation, and the linguistic intricacies behind its root words. Discover the historical and spiritual dimensions that make this sacred text a beacon of guidance and wisdom.
0 views • 31 slides
Understanding the Non-Observed Economy in GDP Compilation
The non-observed economy, including informal and illegal activities, poses challenges in GDP compilation, affecting growth rates and international comparability. Comprehensive coverage and terminology are vital to address these issues. The size of the informal economy in the Pacific region and globa
0 views • 21 slides
Instant Radiosity: Compilation and Screenshots
Learn how to compile and run skeleton code for Instant Radiosity. Follow a step-by-step guide for setting up the building environment using CMake-GUI and compile the code successfully. Capture and share screenshots displaying different Virtual Point Lights (VPLs) post-compilation.
0 views • 21 slides
Programming Fundamentals Midterm Review
The review covers various topics including C parameters passing, compilation, program organization, C++ I/O, the use of stringstream, pointers, structures, classes, access control, constructors/destructor, and operator overloading. It includes code snippets and explanations on parameter passing, pro
0 views • 9 slides
Understanding Dataflow Analysis Frameworks in Compilation
Dataflow analysis plays a crucial role in compilation by computing dataflow facts within basic blocks, using transfer functions and merge operators for inter-block analysis. This process helps in achieving convergence iteratively to a fixpoint, ensuring soundness, precision, and efficiency in runtim
0 views • 53 slides
Nuclear Data Needs for Future Space Exploration
The future of space exploration requires extensive nuclear data for shielding against Galactic Cosmic Rays (GCR) that pose challenges due to their high energy. Transport codes like FLUKA, PHITS, and GEANT4 play crucial roles in simulating shielding applications. There is a need for comprehensive dat
0 views • 7 slides
Understanding Programming Language Features
Exploring syntax and semantics in programming languages, differences between interpretation and compilation, advantages and disadvantages of interpreters and compilers, and the concepts of static and dynamic behaviors in programming. Discover how different languages handle syntax and semantics, and
0 views • 7 slides
Programming Fundamentals: Organizing C++ Code and Compilation Steps
Lecture notes covering program organization in C++, including using header and .cc files, the importance of multiple files for code organization, example linked list implementation, file structure for a linked list program, compilation process with g++, and the purpose of #include directives.
0 views • 12 slides
Understanding Makefiles and Automated Compilation in C++ Projects
Makefiles are essential tools that automate the compilation process in C++ projects, saving time and ensuring only necessary files are recompiled. They help manage dependencies efficiently, making development more streamlined and organized. This article discusses the importance of Makefiles, their s
0 views • 20 slides
Understanding Constant Expressions in C++: Essential Concepts and Best Practices
Explore the crucial concepts of const and by reference in C++, along with their importance and best practices. Dive into the compilation process of C and C++ programs, understand how programs become executables, and discover the significance of compile-time expression evaluation as a powerful concep
0 views • 61 slides
German Discourse Blog Corpus Compilation & Annotation
Compilation and annotation of a discourse-structured blog corpus for German, involving data collection, annotation, addressing specific problems, and planning next steps. The project focuses on fostering interoperability, meeting requirements, and developing models for annotating blogs' structural a
1 views • 39 slides