The Top 10 Signs Your Router May Have Been Hacked
Explore the 10 unmistakable signs indicating your router's security might have been compromised. Learn how to identify potential breaches and safeguard your network from cyber threats.\n
4 views • 1 slides
Step-by-Step TCP/IP Configuration on Windows 10 Client
Detailed guide on configuring TCP/IP settings on a Windows 10 client, including preparation steps, configuration steps, and verification of settings. The guide provides clear instructions with accompanying images for each step.
1 views • 12 slides
WHONET Training Course: Laboratory Configuration and Setup
Understanding the laboratory configuration process in WHONET is crucial for effective data entry and analysis. This module guides users on setting up a new laboratory, entering country and lab details, defining antibiotics, sample locations, and data fields, creating microbiological alerts, and savi
3 views • 57 slides
Proposal for Location Configuration Information (LCI) in IEEE 802.11 Beacons and Probe Responses
This document proposes the inclusion of Location Configuration Information (LCI) data in a standard information element broadcast in Beacons and Probe Responses within IEEE 802.11 networks. By enhancing the accessibility of infrastructure location to non-AP STAs, this proposal aims to simplify locat
1 views • 5 slides
Virtual Router Market Share, Opportunities, Trend, Revenue, Growth 2017-2027
At a compound annual growth rate of 22.3%, the size of the worldwide Virtual Router market is projected to reach US$ 614.6 Million in 2027.
0 views • 5 slides
IEEE 802.11-20/0668r1: EHT BSS Configuration Proposal
The document discusses the configuration of a 320 MHz BSS in the context of 6 GHz regulations, focusing on EHT operation elements such as channel width indication, CCFS principles, and BSS advertisement settings. It proposes design principles for managing legacy and EHT STA operations, emphasizing s
0 views • 14 slides
Enhancing EPS Authorization and Configuration Options in 5G Networks
The proposal focuses on enhancing authorization and configuration options in EPS using protocol configuration options. It discusses the attach procedure, ePCO checking, and the importance of ePCO support in the network architecture. The solution presented emphasizes the role of MME, SGW, and PGW-C+S
0 views • 8 slides
Discussion on 5G NR CADC Configuration Handling in RAN5
The discussion revolves around the existing Tdocs and WIs focusing on how to handle 5G NR CADC configuration within RAN5. It includes proposals to streamline guidelines and checklists to effectively manage new configurations. Various operators and entities like CMCC, Huawei, Ericsson, China Unicom,
0 views • 9 slides
Understanding Bipolar Transistor Configurations for Electronic Circuits
Explore the three common configurations - Common Base, Common Emitter, and Common Collector - for Bipolar Transistors in electronic circuits. Each configuration offers unique characteristics such as voltage gain, current gain, and impedance levels, impacting the signal processing and amplification c
0 views • 27 slides
Discussion on Multi-PUSCH Configuration for UTO-UCI Content Moderator at Ericsson
This discussion encompasses the configuration and implications of the Multi-PUSCH setup based on agreed parameters within the UTO-UCI content moderation context at Ericsson. It delves into varying configurations, potential impacts, and considerations for effective utilization. The slides provide ins
0 views • 17 slides
5G Use Case Proposal for Dublin Ericsson
This proposal outlines the use of NETCONF for configuration management in 5G networks, focusing on Dublin. It covers topics like Configuration with NETCONF, NETCONF Overview, NETCONF Security, YANG Overview, and Proposed Use Cases and Requirements for Dublin. The proposal emphasizes the importance o
7 views • 20 slides
Exploring the Impact of Wing Configuration on Paper Airplane Flight
Explore how changing the wing configuration of paper airplanes affects their flight distance. Learn about lift, drag, and aerodynamics, and conduct experiments to test hypotheses. The results provide insights into the role of wing design in flight performance.
0 views • 12 slides
Focal Point Responsibilities in Data Management System
Detailed instructions on key responsibilities of a focal point including user creation, configuration backups, data export, maintenance, and configuration import in a data management system. Tasks involve creating and editing users, exporting configurations and data, and maintaining system integrity
0 views • 12 slides
Techno-Economic Analysis of Calcium Looping Processes for Low CO2 Emission Cement Plants
This study explores the application of Calcium Looping (CaL) processes in cement plants to reduce CO2 emissions. The process involves using CaO as a sorbent to capture CO2 from flue gas, with the potential for integration at different points in the cement production process. The Tail-end CaL configu
3 views • 14 slides
Understanding Native VLAN 1 in Mesh Ethernet Bridging
Mesh Ethernet bridging utilizes native VLAN 1 for the initial configuration, ensuring the RAP connects to the native VLAN ID 1 on a switch. This setup affects the communication between the RAP and the Map devices, as well as their connection to the controller. Misconfigurations related to VLAN taggi
0 views • 9 slides
Managing Passive Host and Service Checks with Nagios Core
Learn how to enable passive host and service checks in Nagios Core via the configuration file, allowing for monitoring without actively polling the hosts and services. Understand the setup, configuration, and usage of passive checks in your monitoring system. Explore examples and best practices for
0 views • 30 slides
Understanding BIND DNS Security Vulnerabilities and Configuration
Dive into the world of BIND DNS with a focus on security vulnerabilities, zone transfer restrictions, rate limiting, and essential configuration options. Explore key topics such as ISC mailing lists, CVE announcements, and best practices for setting up BIND DNS servers.
0 views • 16 slides
Comprehensive Setup and Configuration Guide for Office Management Software
Detailed setup and configuration instructions for your office management software, including customizing company information, tax rates, localization settings, barcode types, stock management, receipts, and invoices. Ensure a seamless setup process by following the step-by-step guidance provided in
0 views • 31 slides
Configuration Examples for IP SLA with Object Tracking
Learn how to configure and troubleshoot IP SLA with Object Tracking using detailed examples for Static Routing, HSRP, and Policy Based Routing. Find out where Object Tracking can be implemented and when not to use it in various network scenarios. Understand the configuration components, including de
2 views • 17 slides
Understanding Router Routing Tables in Computer Networks
Router routing tables are crucial for directing packets to their destination networks. These tables contain information on directly connected and remote networks, as well as default routes. Routers use this information to determine the best path for packet forwarding based on network/next hop associ
0 views • 48 slides
Unleashing Router Processing Power: A Revolutionary Approach
Delve into the realm of router processing power optimization with Marat Radan and Isaac Keslassy as they propose tapping into unutilized resources. Explore the innovative concept of redirecting packets to alleviate congestion and maximize efficiency in network operations.
1 views • 29 slides
Evolution of Configuration Management in Software Engineering
Explore the evolution of configuration management in software engineering, highlighting key practices like cloud-based IDE, shared repositories, and unobtrusive configuration management. Understand the importance of modern best practices in software development, traditional vs. optimistic approaches
0 views • 20 slides
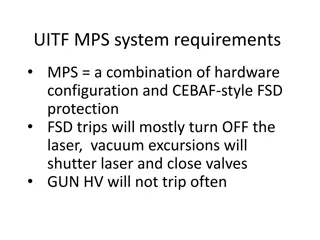
UITF MPS System Requirements and Protection Details
Combining hardware configuration and CEBAF-style FSD protection, the UITF MPS system ensures laser safety, vacuum control, and GUN HV stability. It protects against beam loss, maintains UHV, safeguards viewers, magnets, RF components, and more through a series of interlocks and comparator systems. T
0 views • 7 slides
BOR-60 Reactor Operating Experience and Design Configuration
The BOR-60 reactor, a key component of sustainable clean energy, has a rich history since its construction in the USSR. Its design configuration includes various components such as coolant inlet nozzles, control rod mechanisms, and fuel loading ducts. The core arrangement consists of control rods an
0 views • 12 slides
Overview of Computational Complexity Theory: Savitch's Theorem, PSPACE, and NL-Completeness
This lecture delves into Savitch's theorem, the complexity classes PSPACE and NL, and their completeness. It explores the relationship between time and space complexity, configuration graphs of Turing machines, and how non-deterministic space relates to deterministic time. The concept of configurati
0 views • 67 slides
3GPP TSG-RAN-WG4 Meeting #95e - CSI-RS Configuration and Measurement Definitions
This document outlines the discussions and decisions made at the 3GPP TSG-RAN-WG4 Meeting #95e held electronically from 25th May to 5th June 2020. The focus was on defining CSI-RS configuration and intra/inter-frequency measurements for CSI-RS based L3 measurements, with detailed requirements and sc
0 views • 5 slides
Understanding BGP Protocol and Configuration for Routing Policy Filtering
Explore the terminology, reasons, and methods behind routing policy filtering in the context of BGP protocol configuration. Learn how to control traffic routing preferences, filter routes based on AS or prefix, and use regular expressions for complex filtering rules. Discover the importance of AS-Pa
0 views • 29 slides
LArDPS to eFEX Test Configuration for FOX Demonstrator
Configuration details and diagrams for testing the direct path from the LArDPS to eFEX in the FOX Demonstrator, including optical insertion loss measurements, offset calibration using different setups, and diagrams without splitters. The setup matches the planned configuration for the test.
0 views • 34 slides
Updates on iKAGRA Installation and Configuration Changes
The report discusses changes in the iKAGRA configuration from Fabry-Perot Michelson Interferometer to Michelson Interferometer due to schedule constraints and budget limitations. The document outlines the revised schedule for installation tasks, shift applications, and the impact on the KAGRA projec
0 views • 16 slides
Understanding Network Layer Concepts in Router Design Lecture
This content delves into the fundamental concepts of network layer functions in router design, including data forwarding, control plane operations, and route processing. It explains the analogy of the postal system to address and locate network endpoints, and emphasizes the importance of route looku
0 views • 27 slides
Innovations in Software-Defined Network Computing
The presentation explores the evolution of routers in the early 2000s, the limitations of hardware routers, and the need for more flexible and extensible software routers. It discusses the concept of the Click modular router and its architecture, emphasizing the benefits of a modular design approach
0 views • 35 slides
Insights into Operating Experience and Configuration Management in Nuclear Power Plants
Explore the significance of Operating Experience (OE) in refining machine and human performance, reinforcing desired behaviors, solving problems timely, and sharing industry-wide knowledge in nuclear power. Learn from examples highlighting the importance of configuration management in mature nuclear
0 views • 11 slides
Simplified Router Implementation for CSC458/2209 Course
You will be designing a simplified router for CSC458/2209 course with specific functionalities such as handling Ethernet frames, ICMP messages, ARP requests, IP packets, and more. The router will operate in an emulated network environment using Mininet and will need to route traffic between a client
0 views • 16 slides
Web Development Lecture Highlights & Tips
Explore key topics covered in a web development lecture, including routing, forms, API fetching, and web project assignments. Learn about bug fixes, stable code updates, React 16 features, layout design considerations, React Router philosophy, and various routing mechanisms. Enhance your understandi
0 views • 25 slides
Non-Interactive Anonymous Router with Quasi-Linear Computation
Explore the concept of a Non-Interactive Anonymous Router with Quasi-Linear Computation, Receiver Insider Protection (RIP), Sender Insider Protection (SIP), and Multi-Client Functional Encryption. The comparison of anonymity notions in NIAR and the motivation behind the non-interactive anonymous shu
0 views • 29 slides
Advanced Neutronics Parameters for Fusion Chamber Configuration with Magnetic Intervention
Detailed analysis and design considerations for a fusion chamber configuration utilizing magnetic intervention to optimize neutronics parameters. The discussion includes blanket configuration, neutron wall loading distribution, blanket design options, nuclear design requirements, and dimensions meet
0 views • 12 slides
Innovative NoX Router: Transforming Low-Latency Router Techniques
Discover the groundbreaking NoX Router developed by Mitchell Hayenga and Mikko Lipasti from the Department of ECE. This router introduces a non-speculative control technique, enhancing efficiency by encoding and controlling traffic with XOR properties. By eliminating arbitration latency and dead cyc
0 views • 21 slides
Recap of eZeeKonfigurator Notice Configuration and Zeek Week Oct 2019
A summary of events involving a talk at Zeek Week, issues with notice configuration, experiences with Zeek/Bro, and the introduction of eZeeKonfigurator for configuring Zeek clusters. The content includes descriptions of individuals involved, challenges faced, support for cluster configurations, and
0 views • 20 slides
Efficient Skyline Batch Workflow Tool for Processing Multiple Files
Utilize Skyline Batch, a user-friendly tool developed by Ali Marsh, to run simple Skyline workflows on multiple files efficiently. This tool is ideal for overnight processing, reprocessing data easily, and sharing workflows across different computers. Quickly transform Skyline templates into report
0 views • 4 slides
Removal of FILS IP Address Configuration in IEEE 802.11-14/0093r2
This document details the rationale behind the proposal to remove FILS IP Address Configuration in IEEE 802.11-14/0093r2. The author, Hitoshi Morioka, explains that the need for this configuration is redundant due to the HLP encapsulation's ability to support all required functions. By eliminating c
0 views • 18 slides