Understanding Floods: Major Hazards and Disasters in Environmental Geography and Disaster Management
Floods, a common natural disaster, are often caused by factors like intense rainfall, river overflow, and human activities. Regions in India, such as Assam and Bihar, face significant loss due to recurrent floods. Factors like skewed rainfall patterns and transnational rivers contribute to the flood
0 views • 15 slides
Small Animal Restraints and Safe Handling Practices in Veterinary Technology
Importance of safe practice when working with small animals includes preventing harm, reducing injury, and minimizing stress. Proper animal handling methods and tools are crucial for the safety of both animals and handlers. Common methods of handling different species, demonstrating appropriate anim
1 views • 22 slides
Understanding Primary Clarifiers in Wastewater Treatment
Primary clarifiers are crucial components designed to remove particles with specific settling rates from wastewater. They come in rectangular and circular designs, each with typical dimensions and performance data for BOD and TSS removal. Understanding the design parameters like detention time, over
0 views • 15 slides
IEEE 802.11-20/1238r5 August 2020 Preamble Design Open Issues
In these slides, designs for U-SIG content & overflow and EHT-SIG design are proposed. The focus is on punctured channel indication design with the aim of conveying puncturing patterns efficiently while keeping signaling overhead low. The proposal includes a 6-bit field for puncturing information, a
1 views • 41 slides
Understanding the FLAGS Register in Assembly Language
An exploration of the FLAGS register in assembly language, highlighting the key status flags such as Carry Flag (CF), Parity Flag (PF), Auxiliary Carry Flag (AF), Zero Flag (ZF), Sign Flag (SF), and Overflow Flag (OF). These flags play a crucial role in reflecting the outcome of operations within th
1 views • 24 slides
Understanding Flag Registers in Microprocessor 8086
This content discusses the flag registers in the Microprocessor 8086, covering conditional flags such as Carry Flag (CF), Auxiliary Flag (AF), Parity Flag (PF), Zero Flag (ZF), Sign Flag (SF), and Overflow Flag (OF), as well as control flags including Trap Flag (TP), Interrupt Flag (IF), and Directi
1 views • 23 slides
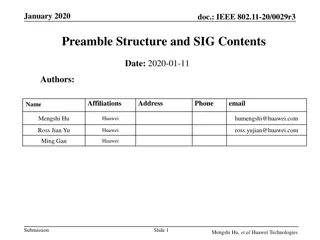
IEEE 802.11-20/0029r3 Preamble Structure and SIG Contents Overview
The document dated January 2020 discusses the preamble structure and SIG contents, focusing on EHT-SIG in IEEE 802.11-20/0029r3 amendment. It covers the introduction of U-SIG, EHT-SIG format, EHT.PPDU types, and EHT-SIG design for MU PPDU. The discussion includes the necessity of accommodating overf
3 views • 22 slides
Best Practices for Cash Handling and Receipt Management
Enhance your cash handling and receipt management practices with essential guidelines such as separation of duties, internal controls, and proper handling of funds and transactions. Discover key insights on authorized departments, standards for receipts and funds handling, and ways to share responsi
1 views • 43 slides
Understanding Buffer Overflow Attacks at Carnegie Mellon
Learn about the Carnegie Mellon 15-213 Recitation Attack Lab, where you can hijack programs using buffer overflow attacks. Gain insights into stack discipline, stack frames, and defeating secure programs through return-oriented programming. Dive into topics like stack smashing attacks, buffer overfl
8 views • 24 slides
Cash Handling Training Certification Overview
This overview provides information on cash handling training certification for satellite cashiers and occasional cash handlers at CSU. It covers the purpose of the training, responsibilities of cash handling locations, training requirements, and physical security protocols for handling university ca
3 views • 27 slides
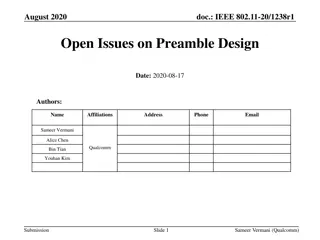
IEEE 802.11-20/1238r1 Preamble Design Open Issues
Proposed designs addressing preamble design issues in IEEE 802.11-20/1238r1 include U-SIG content and overflow for Unified SU/MU PPDU, EHT-SIG design, and punctured channel indication. The focus is on conveying puncturing patterns efficiently while minimizing signaling overhead. The design features
5 views • 32 slides
Overview of 8086 Assembly Language Arithmetic Operations
The 8086 assembly language provides instructions for arithmetic operations such as addition, subtraction, and comparison. These operations are essential for manipulating data in memory and registers. The instructions support various operand types, including registers, memory locations, and immediate
0 views • 24 slides
Manual Handling Toolbox Talk - Importance and Prevention of Injuries
Manual handling injuries are a prevalent issue in workplaces, leading to significant work-related musculoskeletal disorders. Employers must assess and mitigate risks associated with manual handling to ensure employee safety and well-being. Employees also have responsibilities to follow safety protoc
0 views • 16 slides
Understanding Arithmetic Operations for Computers
The chapter delves into the fundamentals of arithmetic for computers, covering operations on integers, dealing with overflow, handling floating-point real numbers, and more. It explores addition, subtraction, multiplication, and division in detail, showcasing examples and techniques for efficient co
4 views • 18 slides
Understanding Buffer Overflow Vulnerabilities in Programming
Buffer overflow vulnerabilities pose serious security threats by allowing attackers to execute arbitrary code on victim machines. This issue arises from overwriting memory in a way that manipulates the program's behavior. Learn about the dangers of buffer overflow bugs, how they can be exploited, an
2 views • 33 slides
Software Security Principles and Practices: Enhancing Program Code Security
Understanding and addressing critical web application security flaws like unvalidated input, cross-site scripting, buffer overflow, injection flaws, and improper error handling is crucial in enhancing the security of program code. The NIST report NISTIR 8151 provides valuable recommendations to redu
2 views • 44 slides
Buffer Overflow: Understanding, Defenses, and Detection
Dive into the world of buffer overflow attacks with insights on understanding the concept, implementing defenses, and detecting stack smashing using techniques like canary values. Discover how to protect against vulnerabilities and grasp the significance of elements such as EIP, ASLR, DEP, and NX bi
0 views • 10 slides
User-Centric Parameters for Call Handling in Cellular Mobile Voice Service
The ITU Regional Standardization Forum for Africa held in Kampala, Uganda in June 2014 introduced ITU-T Recommendation E.807, focusing on the definitions and measurement methods of user-centric parameters for call handling in cellular mobile voice service. The recommendation outlines five key parame
1 views • 15 slides
Understanding Heap Overflow Attacks
A heap is a collection of variable-size memory chunks managed by the program. Heap overflow attacks occur when malicious actors corrupt heap memory, potentially allowing them to overwrite data and execute arbitrary code. This poses a significant security risk. The process involves manipulating heap
2 views • 19 slides
Insights on Overflow through the Western Valley of the Iceland-Faroe Ridge
Research by Bogi Hansen, Karin M. H. Larsen, Steffen Olsen, Detlef Quadfasel, Kerstin Jochumsen, and Svein Østerhus delves into the negligible overflow through the Western Valley of the Iceland-Faroe Ridge. Various field experiments and data analyses demonstrate minimal flow through the Western Val
0 views • 12 slides
Role of Sugar Industry in Circular Economy - Case Study on Spray Pond Overflow Treatment
The two-day summit organized by Mahatma Phule Krushi Vidhyapeet Krushi Mahavidhyalaya, Pune, in collaboration with various organizations, focused on the significant role of sugar and allied industries in promoting circular economy and sustainability. The event highlighted the necessity of treating s
0 views • 15 slides
Understanding Interrupts in Computer Systems
Interrupts in computer systems play a crucial role in handling various events and managing the flow of instructions. This content discusses the types of interrupts, causes, handling procedures, and the role of supervisory modes in modern computers. It covers topics such as internal and external inte
0 views • 29 slides
Understanding Error Handling Techniques in VBA Programming
Error handling is crucial in VBA programming to catch and manage runtime errors effectively. This article explores various error handling techniques such as On Error GoTo statement to prevent program crashes and enhance the reliability of applications. By using structured error handling, developers
0 views • 17 slides
Understanding Buffer Overflow in Computer Programming
This content delves into the intricacies of buffer overflow vulnerabilities in computer programming, showcasing real-world examples such as the Internet Worm and IM War incidents. It covers topics like stack buffer overflow exploits, Unix function implementations prone to buffer overflow, and the re
1 views • 35 slides
Practical Approach to Year 2038 Problem for 32-bit Embedded Systems
A research study conducted at Osaka University addresses the Year 2038 problem in 32-bit embedded systems, discussing the potential time value issues and digit overflow that may occur. The study presents methods and outcomes to tackle this problem, highlighting the significance of handling time_t va
0 views • 39 slides
Understanding MIPS I/O and Interrupt Handling
Delve into the world of MIPS architecture, exploring how I/O operations and interrupts are managed. Learn about memory organization, system functions, I/O registers, and kernel data. Discover how SPIM facilitates input and output handling, including reading from the keyboard and managing output. Div
0 views • 18 slides
Effective Cash Handling Training Presentation
This training presentation focuses on the principles of good cash handling, types of deposits, and adherence to cash handling policies. It highlights the importance of accountability, outlines what is included in cash handling, and discusses the risks associated with cash handling. The presentation
0 views • 27 slides
Understanding Negative Bit Representation in Computer Science
Dive into the world of negative bit representation in computer science, exploring the need for representing negativity in integers, methods like Two's Complement, disadvantages of Sign-Value and One's Complement, range of Two's Complement values, overflow, underflow, and more. Discover the significa
0 views • 26 slides
Smart Bathtub Vulnerabilities and Remote Control Risks
Explore the risks associated with a remote-controlled bathtub controlled via a smartphone app, including vulnerabilities in controlling water flow, water level sensing, and potential overflow scenarios. Learn how attackers could manipulate signals wirelessly and the likelihood of causing the bathtub
0 views • 38 slides
Understanding Buffer Overflow in C and C++ Programs
Buffer overflow is a common vulnerability in C and C++ programs where the allocated memory buffer is overwritten, causing unpredictable behavior. This vulnerability allows attackers to exploit the program by injecting malicious code. The lack of automatic bounds checking in these languages makes it
0 views • 6 slides
Understanding Stack Buffer Overflow Vulnerabilities
Stack buffer overflow is a critical security issue caused by writing more data to a buffer than allocated, leading to bugs, crashes, and potential attacks. This vulnerability, exemplified by the Twilight Hack, allows executing arbitrary code. Learn about its causes, implications, and mitigation stra
0 views • 7 slides
Buffer Overflow Attack and Vulnerable Programs
Understanding buffer overflow attacks and vulnerable programs, the consequences of such attacks, how to run malicious code, and the setup required for exploiting vulnerabilities in program memory stack layouts. Learn about creating malicious inputs (bad files), finding offsets, and addressing shellc
0 views • 36 slides
Understanding Buffer Overflow in Stack: SEED Workshop Lab
This content provides a comprehensive overview of buffer overflow in stack focusing on SEED Workshop Lab scenarios. It covers principles, practice, high-level pictures, program memory layout, function stack layout, function call chains, vulnerable program examples, and more. Through detailed images
0 views • 34 slides
Understanding Stack Overflow Vulnerabilities and Exploitation Techniques
Explore the history of stack overflow vulnerabilities, learn how to control a PC using stack overflow, place shellcode in memory, calculate shellcode addresses, and execute shellcode. Understand different types of overflows including stack overflow, heap overflow, and integer overflow. Delve into th
0 views • 33 slides
Understanding Data Types and Operations in C Programming for Embedded Systems
Explore the importance of selecting appropriate data types and bitwise operations in C programming for embedded systems. Learn about the sizes of data types, performance considerations, ANSI C integer data types and their ranges, handling overflow issues, and coercion in programming. Enhance your kn
0 views • 17 slides
Exception Handling in Java: Basics, Examples, and Importance
Understanding the concept of exception handling in Java, including what exceptions are, the difference between errors and exceptions, reasons for exceptions, how to handle them, and the advantages of exception handling. This topic covers the basics of handling runtime errors in Java programming and
0 views • 27 slides
Understanding Exception Handling in Java
Exception handling in Java is a crucial mechanism to manage runtime errors effectively. This article explains the concept of exceptions, advantages of using exception handling, types of exceptions (checked, unchecked, and errors), common scenarios like ArithmeticException and NullPointerException, a
0 views • 23 slides
Understanding Exception Handling in Java Programming
Exception handling in Java is a crucial mechanism to manage runtime errors effectively. This process helps maintain the normal flow of an application, separates error-handling code from regular code, propagates errors up the call stack, and groups error types. By handling exceptions, developers can
0 views • 11 slides
Overview of Exception Handling in C++ Programming
This content provides insights into exception handling in C++ programming, specifically comparing it to Java. It covers the differences in exception handling between C++ and Java, such as the absence of null pointer exceptions and divide-by-zero exceptions in C++. It explains how C++ deals with exce
0 views • 13 slides
Understanding CSS Float, Positioning, and Clear Properties
CSS Float property allows elements to float to the left, right, or none (default), affecting the flow of text around them. Positioning elements using float can be tricky, especially when setting widths. The clear property prevents overlapping floated elements. Addressing common errors like container
0 views • 15 slides