Apache MINA: High-performance Network Applications Framework
Apache MINA is a robust framework for building high-performance network applications. With features like non-blocking I/O, event-driven architecture, and enhanced scalability, MINA provides a reliable platform for developing multipurpose infrastructure and networked applications. Its strengths lie i
3 views • 13 slides
Modeling and Generation of Realistic Network Activity Using Non-Negative Matrix Factorization
The GHOST project focuses on the challenges of modeling, analyzing, and generating patterns of network activity. By utilizing Non-Negative Matrix Factorization (NMF), realistic network activity patterns can be created and injected into live wireless networks. Understanding and predicting user behavi
4 views • 28 slides
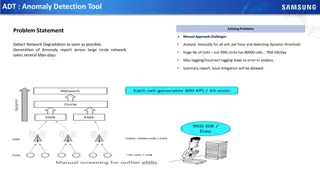
Automated Anomaly Detection Tool for Network Performance Optimization
Anomaly Detection Tool (ADT) aims to automate the detection of network degradation in a mobile communications network, reducing the time and effort required significantly. By utilizing statistical and machine learning models, ADT can generate anomaly reports efficiently across a large circle network
8 views • 7 slides
Revolutionizing Network Management with Intent-Based Networking
Explore the concept and benefits of Intent-Based Networking (IBN) in simplifying network configuration and enhancing efficiency. Learn how IBN automates network operations, aligns with business objectives, improves security, and ensures scalability and reliability. Discover the potential of IBN tool
0 views • 14 slides
Strategies for Personal Income Tax Enumeration Processes in Lagos State
Explore the detailed processes and strategies for Personal Income Tax (PIT) enumeration presented by Ayodele Adebayo, Director of Personal Income Tax at Lagos State Internal Revenue Service. Learn about the importance of enumeration in taxation, background information, channels of enumeration, and t
0 views • 18 slides
Network Compression Techniques: Overview and Practical Issues
Various network compression techniques such as network pruning, knowledge distillation, and parameter quantization are discussed in this content. The importance of pruning redundant weights and neurons in over-parameterized networks is highlighted. Practical issues like weight pruning and neuron pru
0 views • 37 slides
Network Slicing with OAI 5G CN Workshop Overview
Overview of Network Slicing with OAI 5G CN workshop focusing on the crucial role of network slicing in realizing the service-oriented 5G vision. This workshop covers topics like multiple logical networks creation on shared infrastructure, different types of network slices, preparation and instantiat
1 views • 6 slides
Understanding Blood Cell Enumeration Using Haemocytometer
Enumeration of red blood cells using a haemocytometer is crucial to assess blood profiles for conditions like anemia or polycythemia. This process involves manual counting with a specialized apparatus called a Neubauer chamber. The chamber's design includes specific grids and squares for accurate ce
0 views • 15 slides
Network Design Challenges and Solutions in Business Data Communications
Issues in designing a Local Area Network (LAN) include needs analysis, technological design, and cost assessment. The traditional approach involves structured systems analysis, but faces challenges due to rapidly changing technology and increasing network traffic. The Building Blocks Approach recomm
1 views • 20 slides
Understanding 5G RAN Network Slicing and Architecture
Explore the intricate world of 5G Radio Access Network (RAN) and Network Slicing, delving into concepts such as SO Service Orchestrator, SDN-C Service Design, and Core Network Elements. Discover the significance of managing and designing mobile slice services, including eMBB, Massive IoT, and Missio
0 views • 26 slides
Understanding Snort: An Open-Source Network Intrusion Detection System
Snort is an open-source Network Intrusion Detection System (NIDS) developed by Cisco, capable of analyzing network packets to identify suspicious activities. It can function as a packet sniffer, packet logger, or a full-fledged intrusion prevention system. By monitoring and matching network activity
0 views • 23 slides
Effective Management Systems for Field Enumeration in Population and Housing Censuses
Management Information Systems and tools play a crucial role in monitoring and managing field enumeration activities during population and housing censuses. Real-time monitoring of enumeration status, quality control measures, and data transmission to headquarters are essential for a successful enum
0 views • 13 slides
Data Flows and Network Challenges in Particle Physics Infrastructure
This overview delves into the data flows and network challenges faced in particle physics infrastructure, focusing on the JUNO project. It discusses the process of data reception, storage, and replication across various data centers, highlighting the bidirectional nature of data flows. Additionally,
0 views • 24 slides
Progress of Network Architecture Work in FG IMT-2020
In the Network Architecture Group led by Namseok Ko, significant progress has been made in defining the IMT-2020 architecture. The work has involved gap analysis, draft recommendations, and setting framework and requirements. Phase 1 focused on identifying 19 architectural gaps, such as demands for
1 views • 11 slides
Understanding Interconnection Networks Topology
Exploring the topology of interconnection networks helps determine the arrangement of channels and nodes, impacting network cost, performance, latency, energy consumption, and complexity of implementation. Abstract metrics such as degree, hop count, and network diameter play crucial roles in evaluat
1 views • 56 slides
Transportation Network Modeling and Analysis with C.Coupled SE Platform
This content outlines the features and functionalities of the C.Coupled SE Platform (CSET Platform) developed by the Connetics Transportation Group. It covers aspects such as interface design, inputs merging, purposes, platform development using Cube, TAZs merging, and network attributes. The platfo
0 views • 11 slides
Importance of Census 2020 for Fair Representation and Federal Funding
The Census 2020 regional coordination by Mid-America Regional Council and NARC highlights the significance of achieving a complete count for fair allocation of over $675 billion in federal funding across 132 programs. Challenges include distrust of government, mobility of population, and reaching ha
0 views • 15 slides
Human Disease Symptom Network: Understanding Disease Relationships Through Symptoms and Genes
The Human Disease Symptom Network (HSDN) is constructed using a large-scale medical bibliographic records database to form a network of human diseases based on symptom similarities. By integrating disease-gene associations and protein-protein interaction data, correlations between symptom similarity
0 views • 37 slides
Introduction to Network Analysis Using .NET
This presentation introduces the concept of network analysis using .NET in the humanities classroom. It provides a template for teaching and adapting network analysis tools for educational purposes. The guide explains the relevance of networks in processing and visualizing data, emphasizing the coll
0 views • 20 slides
Optimizing Join Enumeration in Transformation-based Query Optimizers
Query optimization plays a crucial role in improving database performance. This paper discusses techniques for optimizing join enumeration in transformation-based query optimizers, focusing on avoiding cross-products in join orders. It explores efficient algorithms for generating cross-product-free
0 views • 18 slides
Meridian: An SDN Platform for Cloud Network Services
Meridian is an SDN platform developed by Mohammad Banikazemi, David Olshefski, Anees Shaikh, John Tracey, and GuohuiWang at IBM T. J. Watson Research Center. The platform focuses on providing cloud network services efficiently. It encompasses an architecture that enables faster and more convenient n
0 views • 21 slides
Enhancing Network Security with Software-Defined Snort and OpenFlow
Explore the implementation of Snort, Barnyard, and PulledPork within a Software-Defined Network framework using OpenFlow technology. Learn how these tools enhance network security through intrusion detection engines, rule management, and network traffic control mechanisms. Dive into the architecture
0 views • 15 slides
Data-Parallel Finite-State Machines: A Breakthrough Approach
This research discusses a new method for breaking data dependencies in data-parallel finite-state machines. It highlights the importance of FSMs in various algorithms and the need for parallel versions in processing large data sets. The study explores breaking data dependences with enumeration and t
0 views • 19 slides
Challenges and Methodology of the Indian Census Program
The Indian Census is the world's largest administrative exercise, capturing the economic, social, and cultural snapshot of a multiethnic society. Managing vast and diverse provinces with millions of households and enumerators poses significant challenges. The methodology involves freezing administra
0 views • 13 slides
Cybersecurity Footprinting and Scanning Techniques
Learn about the techniques involved in cybersecurity footprinting and scanning to protect against information gathering, target acquisition, and unauthorized access. Explore topics such as network enumeration, DNS interrogation, and scanning methods to identify vulnerabilities and enhance security m
0 views • 8 slides
Evolution of Census Mapping in Belize
Integration of geospatial information and statistics in the Belize Census of 2020 marked a significant advancement from the methodology used in the 2010 census. The Statistical Institute of Belize (SIB) plays a crucial role in collecting, compiling, analyzing, and disseminating census data. Census m
0 views • 18 slides
Understanding Network Analysis: Whole Networks vs. Ego Networks
Explore the differences between Whole Networks and Ego Networks in social network analysis. Whole Networks provide comprehensive information about all nodes and links, enabling the computation of network-level statistics. On the other hand, Ego Networks focus on a sample of nodes, limiting the abili
0 views • 31 slides
Understanding Enumeration in Windows Networks
Enumeration in Windows networks involves obtaining information about accounts, network resources, shares, users, groups, applications, and banners. Techniques such as Telnet, netcat, Registry enumeration, Windows sources of information like protocols CIFS/SMB and NetBIOS, NetBIOS enumeration, SNMP e
1 views • 7 slides
Understanding Common Weakness Enumeration (CWE) in Software Security
Common Weakness Enumeration (CWE) provides a formal list of software weakness types, serving as a standard for measuring vulnerabilities and guiding their identification, mitigation, and prevention. This article covers the significance of CWE, the difference between prevention and mitigation strateg
0 views • 19 slides
Quality Assurance in Maldives Population and Housing Census 2014
The Quality Assurance process in the Maldives Population and Housing Census 2014 involved various stages including Cartography, Questionnaire Design, and Enumeration. Cartography played a crucial role in updating block maps used in different areas, ensuring all houses were visited during the listing
0 views • 13 slides
Discrete Optimization Methods Overview
Discrete optimization methods, such as total enumeration and constraint relaxations, are valuable techniques for solving problems with discrete decision variables. Total enumeration involves exhaustively trying all possibilities to find optimal solutions, while constraint relaxations offer a more tr
0 views • 80 slides
Network Function Virtualization (NFV) Overview
Network Function Virtualization (NFV) focuses on virtualizing network functions to improve efficiency and reduce costs in network infrastructure. The lecture discusses key readings, devices that compose a network, specialization of devices, benefits of one-device-does-anything approach, and the goal
0 views • 21 slides
Enhancing Network Stability with Network Monitoring Systems
Network monitoring is crucial for efficient management and proactive issue detection in a network environment. Factors influencing an effective network system include choosing the best OEM, SLA agreements, and selecting a reliable System Integrator. Reactive monitoring can lead to financial losses a
0 views • 12 slides
Operational Guidelines for WCA 2020 Census Enumeration Webinar
This webinar focuses on the operational guidelines for the WCA 2020 Census Enumeration, covering key steps such as pre-test surveys, pilot census, listing operation, and organization of census enumeration. It emphasizes the importance of careful planning to enhance the effectiveness of the census pr
0 views • 21 slides
Insights into the 2021 Australian Census
The 2021 Australian Census showcased significant changes and challenges, including a digital-first approach with a high online response rate, strategies to reach remote areas, and efforts to ensure accurate enumeration despite lockdown restrictions. With strong early responses and innovative methods
0 views • 13 slides
Post Enumeration Survey (PES) in Viet Nam 1999: Evaluation of Census Coverage
The Post Enumeration Survey (PES) conducted in Viet Nam in 1999 aimed to evaluate census coverage by matching individual census records with PES records. The survey focused on assessing the completeness of census data to inform accuracy and aid in improving future censuses. PES teams were assembled
0 views • 12 slides
Maximizing Efficiency Through GIS in the 2013 Population and Housing Census
The 2013 Population and Housing Census in The Gambia marked the first implementation of Geographic Information Systems (GIS) technology, streamlining data collection processes and ensuring comprehensive coverage of populated areas. GIS tools facilitated easy access to enumeration areas, data process
0 views • 5 slides
Efficient Enumeration and Minimal Area of Totally Concave Polyominoes
Researchers present findings on total concavity in polyominoes, exploring the minimal area, efficient enumeration methods, and asymptotic behaviors. Various bounds and algorithms are discussed, including a backtracking prototype and Jensen's algorithm for counting polyominoes without generating all
0 views • 22 slides
Accelerating Systemic Change Network Inaugural Workshop Summary
The Accelerating Systemic Change Network held its inaugural workshop at Howard Hughes Medical Institute in July 2016 to address the lack of coordination in improving higher education. With a vision to become a professional hub for change researchers in STEM education, the network aims to enhance ind
0 views • 5 slides
University Network Section Overview July 2015 - March 2016
The presentation covers the network team structure, team members, objectives, goals, report outline, network statistics, accomplishments, and future plans of the university network section from July 2015 to March 2016. It highlights efforts to provide stable internet and intranet services, restructu
0 views • 16 slides