2022 Reach Codes Initiative. Advancing safer, healthier and more affordable buildings and vehicles
The 2022 Reach Codes Initiative focuses on advancing the adoption of safer, healthier, and more affordable buildings and vehicles through local enhancements to state building codes. This initiative addresses building electrification, reduced methane gas usage, and increased electric vehicle charging
0 views • 52 slides
Understanding Binary Codes and Their Applications
Binary coding is crucial for digital systems as they understand only 0s and 1s. This process converts information into binary language for processing by digital circuits. Different types of binary codes like weighted codes and BCD codes are used for error correction, digital communication, and compu
7 views • 20 slides
Modeling and Generation of Realistic Network Activity Using Non-Negative Matrix Factorization
The GHOST project focuses on the challenges of modeling, analyzing, and generating patterns of network activity. By utilizing Non-Negative Matrix Factorization (NMF), realistic network activity patterns can be created and injected into live wireless networks. Understanding and predicting user behavi
4 views • 28 slides
Understanding Activity, Pay, and Special Codes in API Terminology
Dive into the terminology surrounding Activity Codes, Pay Codes, and Special Codes within the realm of APIs. Explore how these codes represent different aspects of scheduling, productivity, and payroll management. Gain insights into the distinctions between Activity Codes and Pay Codes, their implic
5 views • 8 slides
General Ledger Book Codes and Books Overview
Companies often need to report financial information in different ways for various purposes, such as management view, GAAP, and tax basis. Workday provides tools like Book Codes and Books to facilitate different types of reporting. Book Codes define transaction accounting locations, while Books grou
0 views • 5 slides
Network Compression Techniques: Overview and Practical Issues
Various network compression techniques such as network pruning, knowledge distillation, and parameter quantization are discussed in this content. The importance of pruning redundant weights and neurons in over-parameterized networks is highlighted. Practical issues like weight pruning and neuron pru
0 views • 37 slides
Network Slicing with OAI 5G CN Workshop Overview
Overview of Network Slicing with OAI 5G CN workshop focusing on the crucial role of network slicing in realizing the service-oriented 5G vision. This workshop covers topics like multiple logical networks creation on shared infrastructure, different types of network slices, preparation and instantiat
1 views • 6 slides
Understanding CB Codes in Curriculum Development
Delve into the world of CB codes, where CB stands for course basic, used by CCCCO for counting and funding various elements in curriculum development. Discover the purpose and significance of different CB codes ranging from course control numbers to special status indicators. Gain insights into the
0 views • 20 slides
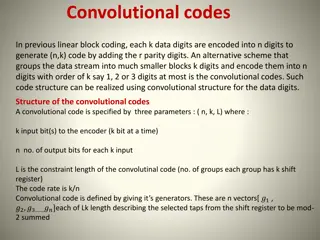
Understanding Convolutional Codes in Digital Communication
Convolutional codes provide an efficient alternative to linear block coding by grouping data into smaller blocks and encoding them into output bits. These codes are defined by parameters (n, k, L) and realized using a convolutional structure. Generators play a key role in determining the connections
0 views • 19 slides
Understanding Binary Codes and Self-Complementing Codes
The concept of binary codes, including Binary Coded Decimal (BCD) codes, and self-complementing codes is explored in this informative content. Learn about how decimal numbers are represented in binary form, the structure of BCD codes, and the properties of self-complementing codes like 2421 and Exce
2 views • 34 slides
Understanding Snort: An Open-Source Network Intrusion Detection System
Snort is an open-source Network Intrusion Detection System (NIDS) developed by Cisco, capable of analyzing network packets to identify suspicious activities. It can function as a packet sniffer, packet logger, or a full-fledged intrusion prevention system. By monitoring and matching network activity
0 views • 23 slides
Understanding C Codes in Institutional Student Information Records (ISIRs)
C codes are indicators generated by CPS requiring resolution from the Financial Aid Administrator. This article explores the process of resolving C codes and highlights the seven common areas where C codes are generated, including Selective Service, Social Security, and Veterans Affairs matches. It
0 views • 32 slides
Updates on Oil & Gas NAICS Codes and Classification Guidelines
The National Oil and Gas Emissions Committee discusses the recent changes in NAICS codes for the oil and gas industry, including the breakdown of Crude Petroleum and Natural Gas Extraction codes. The U.S. Census Bureau provides guidance on assigning NAICS codes based on the primary economic activity
0 views • 12 slides
Understanding ICD-11 and Morbidity Coding Principles
ICD-11 is a classification system that groups entities based on statistical relevance and specificity of codes. Entities without specific codes are assigned to residual codes (Y for specified, Z for unspecified) based on hierarchy. Examples illustrate the differentiation between specified and unspec
0 views • 15 slides
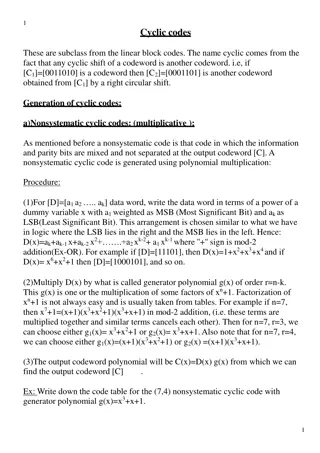
Understanding Cyclic Codes: Generation and Examples
Cyclic codes are a subclass of linear block codes where any cyclic shift of a codeword results in another valid codeword. This article explains the generation of nonsystematic cyclic codes through polynomial multiplication and provides examples and code tables for both nonsystematic and systematic c
0 views • 11 slides
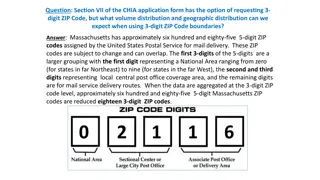
Understanding Geographic Distribution Using 3-Digit ZIP Codes
Massachusetts has approximately 685 5-digit ZIP codes assigned by the USPS, which can be aggregated into 18 3-digit ZIP codes for geographic analysis. The distribution of Emergency Department visit volumes varies across these 3-digit ZIP code boundaries, reflecting different regional characteristics
1 views • 4 slides
Introduction to Capacity Allocation & Congestion Management Network Code Stakeholder Meeting
This presentation discusses the importance of network codes, ENTSO-E's role, and the development process of the Capacity Allocation & Congestion Management Network Code. It highlights the legal framework, significance of network codes, and the process involved in drafting and implementing these code
1 views • 29 slides
Transportation Network Modeling and Analysis with C.Coupled SE Platform
This content outlines the features and functionalities of the C.Coupled SE Platform (CSET Platform) developed by the Connetics Transportation Group. It covers aspects such as interface design, inputs merging, purposes, platform development using Cube, TAZs merging, and network attributes. The platfo
0 views • 11 slides
Equidistant Codes in the Grassmannian: Mathematical Structures and Applications
Explore the concept of equidistant codes in the Grassmannian space, discussing their definitions, motivation, and applications in network coding. Learn about the construction of trivial and non-trivial equidistant codes, their properties, and how they play a crucial role in error correction and dist
0 views • 25 slides
Understanding Professional Codes of Ethics
Explore the foundations and evolution of professional codes of ethics, examining values, ideals, and principles that shape ethical behavior. Learn about the roles and responsibilities of codes of ethics, concerns surrounding them, and how they influence policies in organizational settings. Delve int
0 views • 11 slides
Enhancing Spectrum Efficiency with Low Complexity Erasure Codes in IEEE 802.11 Document
This document delves into the implementation of erasure codes for content channels in IEEE 802.11 systems. By utilizing erasure codes, spectrum efficiency can be boosted without significantly increasing the complexity of encoding and decoding processes. The discussion also covers the duplication of
0 views • 20 slides
Enhancing Data Integrity Protection in Cloud Storage Using Regenerating Codes
This paper explores the importance of data integrity protection in cloud storage and presents a solution using regenerating codes to detect corrupted data chunks, provide fault tolerance, and enable efficient recovery. It compares regenerating codes with Reed-Solomon codes and discusses their implic
0 views • 36 slides
Meridian: An SDN Platform for Cloud Network Services
Meridian is an SDN platform developed by Mohammad Banikazemi, David Olshefski, Anees Shaikh, John Tracey, and GuohuiWang at IBM T. J. Watson Research Center. The platform focuses on providing cloud network services efficiently. It encompasses an architecture that enables faster and more convenient n
0 views • 21 slides
Lower Bounds on Sampling Good Codes in Bounded-Depth Circuits
Bounded-depth circuits are proven unable to sample or approximate good codes effectively. This work delves into lower bounds, showcasing that bounded families of circuits face limitations in computing specific functions or sampling distributions. The example of Parity in AC0 circuits illustrates the
0 views • 21 slides
DukeShift User Group and Special Codes Overview
Explore the DukeShift user group details featuring Julia Bambach, Tiffany McNeill, Bernard Rice, John Dale, and updates for February 2023. Learn about new special codes for virtual nursing, quick special code review, VA and SC special codes, and reporting on special codes. Dive into essential topics
0 views • 11 slides
Comprehensive Overview of Multi-delimiter Data Compression Codes and Key Features
This content showcases the concept of multi-delimiter data compression codes, their application in various algorithms such as arithmetic, finite state entropy, Huffman, and Fibonacci. Key features including compression rate, synchronization, search in compressed files, encoding/decoding speed, and c
0 views • 27 slides
Understanding Binary Codes and Character Coding Techniques
Binary codes, such as ASCII and EBCDIC, are crucial in representing data in computers and digital systems. They play a key role in error detection and data encoding. This article discusses the basics of binary coding, various types of binary codes, character coding techniques like ASCII and EBCDIC,
0 views • 22 slides
Understanding Network Analysis: Whole Networks vs. Ego Networks
Explore the differences between Whole Networks and Ego Networks in social network analysis. Whole Networks provide comprehensive information about all nodes and links, enabling the computation of network-level statistics. On the other hand, Ego Networks focus on a sample of nodes, limiting the abili
0 views • 31 slides
Quantum Error-Correcting Codes and Subsystem Codes
Quantum error-correcting codes (QECC) play a crucial role in protecting quantum information from errors. Stabilizer codes with fault-tolerant error-detecting circuits can lead to the construction of resilient subsystem codes. These codes involve encoding logical qubits into physical qubits and error
0 views • 26 slides
Overview of V*LIDORT and Other Radiative Transfer Models by Robert Spurr
The presentation provides an update on the status of V*LIDORT and other radiative transfer models as discussed at the Third TEMPO Science Team Meeting. It covers the LIDORT family overview, upgrades to the codes, new releases for RT models, and accelerated RT developments using PCA. The V*LIDORT cod
0 views • 12 slides
Understanding Tilde Codes for Custom Result Pictures
Tilde codes are utilized in the creation of custom result pictures from a mentometer system, offering flexibility in formats and colors. These codes are embedded within result pictures and replaced with numerical values by the mentometer system. Learn how to hide/unhide tilde codes, commonly used ti
0 views • 21 slides
Evolution of Communication Systems: From Bandwidth Division to Spread Spectrum
Third-generation communication systems utilize Pseudo-Noise (PN) codes to share bandwidth without interference, while first and second-generation systems divide bandwidth into smaller channels. PN codes are vectors with 1s and -1s, orthogonal to each other. Users transmit data using PN coding, combi
0 views • 14 slides
Managing Student Moves and Transfers in DLM 2022-2023
This content provides detailed guidance on managing student moves and transfers within the Dynamic Learning Maps (DLM) system for the 2022-2023 academic year. It covers the use of exit codes, special circumstance codes, key dates for assessments, required training materials, New Jersey specific guid
0 views • 22 slides
Current Policy Issues Regarding Three-Character Country Codes as Top-Level Domains
The GAC Agenda Item 10 discusses the possibility of using three-character country codes as top-level domains in the future rounds, addressing concerns of potential confusion with existing ccTLDs. The joint ccNSO and GNSO working group is exploring lifting restrictions on three-letter codes, with the
0 views • 6 slides
Benchmarking Study of Probabilistic Fracture Mechanics Codes for Piping
This study presents the preliminary results of a benchmarking study on probabilistic fracture mechanics (PFM) codes for piping systems conducted by KINS and CRIEPI. The study aims to improve understanding, recommend best practices, and identify unexpected code behaviors for future enhancements. The
0 views • 37 slides
Network Function Virtualization (NFV) Overview
Network Function Virtualization (NFV) focuses on virtualizing network functions to improve efficiency and reduce costs in network infrastructure. The lecture discusses key readings, devices that compose a network, specialization of devices, benefits of one-device-does-anything approach, and the goal
0 views • 21 slides
Enhancing Network Stability with Network Monitoring Systems
Network monitoring is crucial for efficient management and proactive issue detection in a network environment. Factors influencing an effective network system include choosing the best OEM, SLA agreements, and selecting a reliable System Integrator. Reactive monitoring can lead to financial losses a
0 views • 12 slides
Career Path Codes Update: 2016-17 Overview
Explore the proposed updates to Career Path Codes for the 2016-17 academic year, focusing on student achievement criteria, pathway assessments, and alternative exams in various subjects. Learn about the new codes and definitions in Arts, Career and Technical Education, Humanities, and more, as well
0 views • 29 slides
Quantum Error Correction and Fault Tolerance Overview
Quantum error correction and fault tolerance are essential for realizing quantum computers due to the challenge of decoherence. Various approaches, including concatenated quantum error correcting codes and topological codes like the surface code, are being studied for fault-tolerant quantum computin
0 views • 19 slides
Understanding Account Codes for Business Management Specialists
This content covers the basics of account codes, including types of expenses, selecting account codes for documents, allowable expenses, and more. It delves into operating ledger categories, computer account codes, and the selection process for different expenses, providing valuable insights for fin
0 views • 18 slides