Apache MINA: High-performance Network Applications Framework
Apache MINA is a robust framework for building high-performance network applications. With features like non-blocking I/O, event-driven architecture, and enhanced scalability, MINA provides a reliable platform for developing multipurpose infrastructure and networked applications. Its strengths lie i
3 views • 13 slides
Modeling and Generation of Realistic Network Activity Using Non-Negative Matrix Factorization
The GHOST project focuses on the challenges of modeling, analyzing, and generating patterns of network activity. By utilizing Non-Negative Matrix Factorization (NMF), realistic network activity patterns can be created and injected into live wireless networks. Understanding and predicting user behavi
4 views • 28 slides
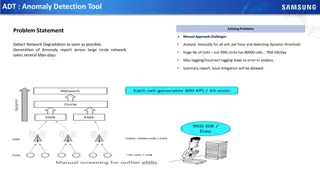
Automated Anomaly Detection Tool for Network Performance Optimization
Anomaly Detection Tool (ADT) aims to automate the detection of network degradation in a mobile communications network, reducing the time and effort required significantly. By utilizing statistical and machine learning models, ADT can generate anomaly reports efficiently across a large circle network
8 views • 7 slides
Revolutionizing Network Management with Intent-Based Networking
Explore the concept and benefits of Intent-Based Networking (IBN) in simplifying network configuration and enhancing efficiency. Learn how IBN automates network operations, aligns with business objectives, improves security, and ensures scalability and reliability. Discover the potential of IBN tool
0 views • 14 slides
Understanding the Contrast: Fear of God vs. Indifference in Today's Culture
Exploring the concept of fearing God and the consequences of indifference in contemporary society. The importance of revering God, as described in biblical texts, is contrasted with the prevailing indifference towards Him. The distinction between genuine fear of God and the absence of such reverence
0 views • 20 slides
Challenges of Fear and Rejection in Human Relationships
The fear of rejection can control us, leading to feelings of worthlessness when we seek acceptance from others. Various scenarios, from social events to professional roles, illustrate how fear of rejection impacts individuals differently. The discussion questions prompt self-reflection on past exper
0 views • 22 slides
Overview of Anxiety and Related Disorders
Anxiety disorders, such as PTSD, panic disorders, phobias, agoraphobia, and OCD, are characterized by varying degrees of fear and distress. Anxiety is a normal response to danger, but when it becomes chronic, it can lead to debilitating conditions. PTSD occurs post-trauma, panic disorders involve in
1 views • 42 slides
Overcoming Fear of Water: The Story of William Orville Douglas
William Orville Douglas, a renowned American jurist and politician, shares his childhood experience of nearly drowning and overcoming his fear of water in this excerpt from his autobiography. Despite his initial apprehension, with determination and some help, he conquered his fear and learned to swi
0 views • 16 slides
Unveiling the Superstitions and Origins of Friday the 13th Fear
Explore the life and works of Samuel Taylor Coleridge, a renowned English poet, and delve into the concept of superstitions, including the fear of Friday the 13th known as paraskevidekatriaphobia. Discover common superstitions, the Christian origins behind the fear of this day, and how it influences
0 views • 13 slides
Network Compression Techniques: Overview and Practical Issues
Various network compression techniques such as network pruning, knowledge distillation, and parameter quantization are discussed in this content. The importance of pruning redundant weights and neurons in over-parameterized networks is highlighted. Practical issues like weight pruning and neuron pru
0 views • 37 slides
Network Slicing with OAI 5G CN Workshop Overview
Overview of Network Slicing with OAI 5G CN workshop focusing on the crucial role of network slicing in realizing the service-oriented 5G vision. This workshop covers topics like multiple logical networks creation on shared infrastructure, different types of network slices, preparation and instantiat
1 views • 6 slides
Network Design Challenges and Solutions in Business Data Communications
Issues in designing a Local Area Network (LAN) include needs analysis, technological design, and cost assessment. The traditional approach involves structured systems analysis, but faces challenges due to rapidly changing technology and increasing network traffic. The Building Blocks Approach recomm
1 views • 20 slides
Understanding 5G RAN Network Slicing and Architecture
Explore the intricate world of 5G Radio Access Network (RAN) and Network Slicing, delving into concepts such as SO Service Orchestrator, SDN-C Service Design, and Core Network Elements. Discover the significance of managing and designing mobile slice services, including eMBB, Massive IoT, and Missio
0 views • 26 slides
Understanding Snort: An Open-Source Network Intrusion Detection System
Snort is an open-source Network Intrusion Detection System (NIDS) developed by Cisco, capable of analyzing network packets to identify suspicious activities. It can function as a packet sniffer, packet logger, or a full-fledged intrusion prevention system. By monitoring and matching network activity
0 views • 23 slides
Emotional and Logical Appeal in 'Sinners in the Hands of an Angry God'
Exploring Jonathan Edwards' persuasive techniques through appeals to fear, hope, and logic in 'Sinners in the Hands of an Angry God'. This analysis delves into the emotional impact of imminent damnation, the comforting notion of salvation, and the rational arguments presented to sway the congregatio
0 views • 7 slides
Data Flows and Network Challenges in Particle Physics Infrastructure
This overview delves into the data flows and network challenges faced in particle physics infrastructure, focusing on the JUNO project. It discusses the process of data reception, storage, and replication across various data centers, highlighting the bidirectional nature of data flows. Additionally,
0 views • 24 slides
Progress of Network Architecture Work in FG IMT-2020
In the Network Architecture Group led by Namseok Ko, significant progress has been made in defining the IMT-2020 architecture. The work has involved gap analysis, draft recommendations, and setting framework and requirements. Phase 1 focused on identifying 19 architectural gaps, such as demands for
1 views • 11 slides
Overview of Expedited Removal, Asylum, and Credible Fear Interviews
Expedited Removal is a process where individuals arriving at U.S. ports of entry may be subject to deportation if found inadmissible under specific grounds. This includes misrepresentations or lack of valid entry documents. The process can be applied by the Department of Homeland Security within 100
1 views • 14 slides
Understanding Fear of Falling: Causes, Consequences, and Assessment
Fear of falling is a prevalent concern among older adults and individuals with certain health conditions. It can lead to negative outcomes such as increased risk of falls, activity avoidance, and decreased mental well-being. Factors contributing to fear of falling include perceived threat to balance
1 views • 39 slides
Overcoming Fear and Embracing God: A Path to Spiritual Growth
Explore the detrimental effects of fear on our lives and the empowering journey of embracing God as your Father and enthroning Christ as your Lord. Learn to eradicate sin, deepen your faith, and empower yourself with love while overcoming fear. Discover the strict prohibitions of God against fear an
0 views • 10 slides
Overcoming Fear Through Faith in Christ
Believing in Jesus as the Christ, being born of God, and having faith empowers us to overcome fear and challenges in this world. Jesus within us is greater than any fear we face. Understanding how fear affects us helps us combat its negative impact and trust in the Lord for safety and destiny fulfil
0 views • 24 slides
Understanding and Overcoming the Fear of Reprisal in Addressing Fraud, Waste, and Abuse
This presentation delves into the fear of reprisal when exposing fraud, waste, and abuse, discussing reasons behind this fear and how it impacts decision-making. It explores survey results on staff fears, management trust issues, and communication challenges, aiming to provide insights on addressing
0 views • 24 slides
Understanding Healthy and Unhealthy Fears in Light of Scripture
Exploring the concept of fear as depicted in biblical verses, this content highlights the importance of a healthy fear of God for wisdom and understanding. It contrasts healthy fears that lead to blessings with unhealthy fears driven by human standards and reactions. Encouragement is given to overco
0 views • 13 slides
Understanding Interconnection Networks Topology
Exploring the topology of interconnection networks helps determine the arrangement of channels and nodes, impacting network cost, performance, latency, energy consumption, and complexity of implementation. Abstract metrics such as degree, hop count, and network diameter play crucial roles in evaluat
1 views • 56 slides
Overcoming the Fear of Public Speaking: Tips for Success
Surveys show that public speaking is a top fear for many, even ranking above death. The fear usually stems from a fear of embarrassment, whether physical or mental. To reduce the odds of feeling embarrassed, proper preparation is key. This includes physical preparations like having a checklist and m
0 views • 10 slides
Transportation Network Modeling and Analysis with C.Coupled SE Platform
This content outlines the features and functionalities of the C.Coupled SE Platform (CSET Platform) developed by the Connetics Transportation Group. It covers aspects such as interface design, inputs merging, purposes, platform development using Cube, TAZs merging, and network attributes. The platfo
0 views • 11 slides
Human Disease Symptom Network: Understanding Disease Relationships Through Symptoms and Genes
The Human Disease Symptom Network (HSDN) is constructed using a large-scale medical bibliographic records database to form a network of human diseases based on symptom similarities. By integrating disease-gene associations and protein-protein interaction data, correlations between symptom similarity
0 views • 37 slides
Introduction to Network Analysis Using .NET
This presentation introduces the concept of network analysis using .NET in the humanities classroom. It provides a template for teaching and adapting network analysis tools for educational purposes. The guide explains the relevance of networks in processing and visualizing data, emphasizing the coll
0 views • 20 slides
Rekindling the Gift of God: Overcoming Fear and Apathy
Encouragement and guidance are provided in this content to help individuals reignite the divine gift within them, equipping them with power, love, and self-discipline while combatting fear and lukewarm attitudes. Practical steps are outlined, emphasizing self-examination, determination, and proactiv
0 views • 17 slides
Meridian: An SDN Platform for Cloud Network Services
Meridian is an SDN platform developed by Mohammad Banikazemi, David Olshefski, Anees Shaikh, John Tracey, and GuohuiWang at IBM T. J. Watson Research Center. The platform focuses on providing cloud network services efficiently. It encompasses an architecture that enables faster and more convenient n
0 views • 21 slides
Enhancing Network Security with Software-Defined Snort and OpenFlow
Explore the implementation of Snort, Barnyard, and PulledPork within a Software-Defined Network framework using OpenFlow technology. Learn how these tools enhance network security through intrusion detection engines, rule management, and network traffic control mechanisms. Dive into the architecture
0 views • 15 slides
Understanding Network Metrics Through Centrality Analysis
This presentation introduces network metrics as tools to describe network characteristics and answer important questions. Using centrality metrics as an example, participants learn how to identify the most important nodes in a network based on different criteria such as degree centrality and closene
0 views • 15 slides
Understanding Network Analysis: Whole Networks vs. Ego Networks
Explore the differences between Whole Networks and Ego Networks in social network analysis. Whole Networks provide comprehensive information about all nodes and links, enabling the computation of network-level statistics. On the other hand, Ego Networks focus on a sample of nodes, limiting the abili
0 views • 31 slides
Understanding Network Interference in CS590B/690B Lecture
Delve into the realm of network interference through the CS590B/690B lecture with Phillipa Gill at UMass Amherst. Explore topics such as Internet routing, timing attacks, BGP hijacks, Tor network functionality, relay selection, collusion scenarios, use of guards, web site fingerprinting attacks, tra
0 views • 11 slides
Theses Reflecting Our Time: Human Relationship Structures and the Dynamics of Fear and Equilibrium
The thesis explores the central role of human beings in relationship structures, the processing of fear, and the concept of equilibrium in societal and personal life. It delves into the existential aspects of borders, the significance of crossing boundaries, and the impact of exponential effects whe
0 views • 26 slides
Contribution of HALA Network to ATM Community and SESAR 2020: Achievements and Future Directions
HALA network has been instrumental in fostering research and innovation in the field of automation for ATM systems, providing a platform for knowledge dissemination, collaboration, and advancement. The network has facilitated exploratory research, encouraged young scientists' participation, and crea
0 views • 12 slides
Network Function Virtualization (NFV) Overview
Network Function Virtualization (NFV) focuses on virtualizing network functions to improve efficiency and reduce costs in network infrastructure. The lecture discusses key readings, devices that compose a network, specialization of devices, benefits of one-device-does-anything approach, and the goal
0 views • 21 slides
Enhancing Network Stability with Network Monitoring Systems
Network monitoring is crucial for efficient management and proactive issue detection in a network environment. Factors influencing an effective network system include choosing the best OEM, SLA agreements, and selecting a reliable System Integrator. Reactive monitoring can lead to financial losses a
0 views • 12 slides
Accelerating Systemic Change Network Inaugural Workshop Summary
The Accelerating Systemic Change Network held its inaugural workshop at Howard Hughes Medical Institute in July 2016 to address the lack of coordination in improving higher education. With a vision to become a professional hub for change researchers in STEM education, the network aims to enhance ind
0 views • 5 slides
University Network Section Overview July 2015 - March 2016
The presentation covers the network team structure, team members, objectives, goals, report outline, network statistics, accomplishments, and future plans of the university network section from July 2015 to March 2016. It highlights efforts to provide stable internet and intranet services, restructu
0 views • 16 slides