Adversarial Machine Learning in Cybersecurity: Challenges and Defenses
Adversarial Machine Learning (AML) plays a crucial role in cybersecurity as security analysts combat continually evolving attack strategies by malicious adversaries. ML models are increasingly utilized to address the complexity of cyber threats, yet they are susceptible to adversarial attacks. Inves
2 views • 46 slides
What is Email Marketing?
Email marketing is a cornerstone of digital marketing, leveraging targeted email communication to engage subscribers and drive desired outcomes. By crafting compelling content, personalized messages, and strategic segmentation, businesses can cultivate meaningful relationships with their audience. B
1 views • 7 slides
Enterprise Marketing Management (EMM) Capabilities for Effective Email Campaigns
Enterprise Marketing Management (EMM) offers a comprehensive suite of tools for tracking marketing expenditure, ROI, and lead performance. With capabilities ranging from Marketing Activity Codes (MAC) for tracking sources to customizable email templates and delivery reports, EMM streamlines the proc
0 views • 8 slides
Understanding Network Interference and Censorship in Social Media
Discover the insights into detecting network interference, censorship, and social media manipulation through a collection of case studies, research papers, and real-world examples discussed in a Spring 2018 lecture. Topics include the goals of PAM 2011 paper, the Green Dam and Blue Dam projects, the
1 views • 27 slides
Exploring Adversarial Machine Learning in Cybersecurity
Adversarial Machine Learning (AML) is a critical aspect of cybersecurity, addressing the complexity of evolving cyber threats. Security analysts and adversaries engage in a perpetual battle, with adversaries constantly innovating to evade defenses. Machine Learning models offer promise in combating
0 views • 43 slides
Staying Safe Online: Essential Tips for a Secure Online Experience
Stay safe online by protecting your personal information, avoiding strangers, and being cautious of viruses and spam emails. Learn how to use the internet wisely while respecting others and staying secure online.
0 views • 12 slides
Understanding Mail Server Basics from a Linux Operating System Perspective
Dive into the essentials of mail servers, exploring the key components of an email system, such as email clients and servers. Learn how email clients work, the functions they offer, and the role of email servers in managing and routing messages to ensure delivery over the Internet.
0 views • 25 slides
Mastering Email Management: Practical Tips for Efficiency
Learn how to conquer your email inbox with practical tips from Michael Lucido, MD, PhD, and David Thylur, MD. This seminar aims to improve your email culture, personalize management strategies, and enhance Outlook skills for increased efficiency. Discover how to shift to a compassionate email cultur
0 views • 18 slides
Introduction to Machine Learning Concepts
This text delves into various aspects of supervised learning in machine learning, covering topics such as building predictive models for email classification, spam detection, multi-class classification, regression, and more. It explains notation and conventions used in machine learning, emphasizing
1 views • 22 slides
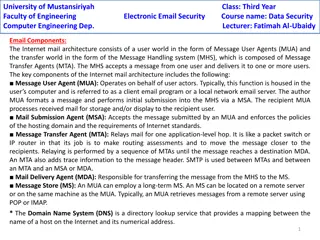
Understanding Internet Mail Architecture Components
The Internet mail architecture consists of key components including Message User Agents (MUA), Mail Submission Agent (MSA), Message Transfer Agent (MTA), Mail Delivery Agent (MDA), and Message Store (MS). These components work together to facilitate the sending, receiving, and storing of email messa
6 views • 4 slides
Mastering Email Communication: Layouts, Etiquette, and Best Practices
Dive into the world of email communication with this comprehensive guide covering email layouts, etiquette tips, common purposes, and general email format. Learn how to effectively structure your emails, address recipients, and maintain professionalism in your online correspondence.
0 views • 41 slides
Understanding ROC Curves and Operating Points in Model Evaluation
In this informative content, Geoff Hulten discusses the significance of ROC curves and operating points in model evaluation. It emphasizes the importance of choosing the right model based on the costs of mistakes like in disease screening and spam filtering. The content explains how logistical regre
7 views • 11 slides
Professionalism and Communication in the Digital Age
This presentation delves into the nuances of professionalism and effective communication in today's digital world, emphasizing the importance of email and social media etiquette. It explores topics such as managing perceptions, the myth of casual email, the value of business email, and the essential
0 views • 24 slides
Understanding Email Infrastructure: SPF, DKIM, DMARC, and SMTP
Email infrastructure involves protocols like SPF, DKIM, DMARC, and SMTP to ensure secure and reliable communication. SMTP is used to transport emails between servers, while MTA acts as the mail transport agent. Understanding these components is crucial for effective email communication and troublesh
5 views • 14 slides
Essential Email Writing Guidelines and Etiquette
Understanding the importance of email writing, this guide covers the functions, advantages, and pitfalls of using emails. It delves into the reasons for the popularity of emails, common mistakes to avoid, and key principles for composing effective emails. Additionally, it provides insights into emai
0 views • 8 slides
Enhancing Email Security with DMARC: A Comprehensive Approach
Explore the vital components of DMARC, a robust spam filtering and phishing protection methodology, as presented by Ben Serebin. Discover how DMARC integrates SPF and DKIM to safeguard email authenticity and ensure a secure communication environment. Uncover the challenges, prerequisites, and implem
0 views • 13 slides
Collective Spammer Detection in Evolving Social Networks
Exploring the growth of spam in social networks, this study highlights the challenges posed by spammers and the need for collective detection mechanisms. With insights on spam trends, interaction methods, and user profiles, it sheds light on the evolving landscape of social network spam.
0 views • 65 slides
Understanding Enterprise Email Spam Prevention Techniques
Learn about the key strategies used by enterprises to combat email spam, including spam filters, SPF records, DMARC, DKIM, whitelisting, and SCL ratings. Discover how these tools work together to protect against spam, spoofing, and phishing attempts.
0 views • 8 slides
Mastering Email Management: Tips, Statistics, and Best Practices
Explore key insights and strategies for effective email management in the digital age. Discover email statistics, protocol etiquette, inbox management techniques, and insights on popular email platforms like Gmail. From understanding email distributions to implementing rules and filters, enhance you
0 views • 7 slides
Analysis of Spam Activity on Popular Social Networks
This research paper presents an in-depth analysis of spam activity on major social networking platforms such as Facebook, MySpace, and Twitter. The study includes data collection, analysis of spam bots, identification of spam campaigns, and analysis of results. It reveals insights into user behavior
2 views • 38 slides
Mastering Email Communication for Effective Interactions
Enhance your email communication skills by understanding the nuances of emotional intelligence, proper email etiquette, and effective email format. Learn how to craft compelling subject lines, avoid common email pitfalls, and tailor your tone based on recipients. Discover strategies for improved ema
0 views • 16 slides
Personalized Spam Filtering for Gray Mail Analysis
This work delves into the concept of gray mail - messages that some users want while others don't. It explores the challenges posed by gray mail and presents a large-scale personalization algorithm to address these issues. The study leverages data from Hotmail Feedback Loop, focusing on user prefere
3 views • 22 slides
Efficient Email Management Strategies and Tips for Organizing Your Inbox
Learn essential email management techniques such as categorizing emails, setting up rules, minimizing unread messages, blocking spam, and handling important messages effectively. Discover how to manage your email efficiently to stay organized and ensure you don't miss critical information or lose im
0 views • 7 slides
Adversarial Learning in ML: Combatting Internet Abuse & Spam
Explore the realm of adversarial learning in ML through combating internet abuse and spam. Delve into the motivations of abusers, closed-loop approaches, risks of training on test data, and tactics used by spammers. Understand the challenges and strategies involved in filtering out malicious content
0 views • 13 slides
Understanding Email Campaigns in Internet Marketing
Email campaigns have transformed communication by allowing easy distribution of messages and documents worldwide within seconds. They can take various forms like direct emails, newsletters, and press releases. This chapter explores different types of email campaigns, including direct mail vs. direct
0 views • 25 slides
Mastering Email Communication in the Workplace
Dive into the intricacies of email communication in the workplace with insights on when to send emails, email etiquette, and valuable tips for composing effective professional emails. Understand the role of email in modern organizations, learn the do's and don'ts of email messaging, and enhance your
0 views • 32 slides
Understanding Classification in Data Mining
Classification in data mining involves assigning objects to predefined classes based on a training dataset with known class memberships. It is a supervised learning task where a model is learned to map attribute sets to class labels for accurate classification of unseen data. The process involves tr
0 views • 26 slides
Understanding Email Technologies and Infrastructure
Explore the intricacies of email technologies, infrastructure, and architecture, including the format of HTTP messages, the role of proxy servers, creating web servers, and key components of email systems like user agents, mail servers, and SMTP protocol. Delve into email protocols like SMTP, POP3,
0 views • 38 slides
Email Security and Encryption Technologies Overview
Email security is crucial in today's digital world. This content discusses various email security measures, including PGP and S/MIME systems, and their utilization in business and personal communications. It also explores the history of PGP encryption, the role of Philip R. Zimmermann, and the chara
0 views • 10 slides
Email Best Practices for Postfix and Dovecot Setup
In this guide, Kevin Chege discusses best practices for configuring email servers with Postfix and Dovecot. Topics covered include setting up SPF records, reverse records, using anti-spam and anti-virus software, implementing greylisting, and ensuring well-formatted messages to reduce spam. Learn ho
0 views • 38 slides
Mastering Email Etiquette for Business Success
Enhance your professional image by mastering email etiquette. Learn how to represent your company well, write effective emails, use proper subject lines, address recipients professionally, and avoid common mistakes. Understand the importance of email security and when not to use email for sensitive
1 views • 32 slides
Determining Email Spam using Statistical Analysis and Machine Learning
The discussion revolves around classifying spam from ham emails by analyzing word frequencies. Various techniques such as Logistic Regression, Linear Discriminant Analysis, and 10-fold Cross-Validation are employed to achieve this goal. Statistical analysis and machine learning models like LDA and L
0 views • 8 slides
Effective Email Strategies: Taming the Tiger
Strategies for managing email effectively are discussed in "Taming the Tiger: Strategies for Effective Use of Email," featuring insights from Elaine Shuck and Janine Lim. Tips include organizing emails into folders, using filters for newsletters and social media, and unsubscribing from listservs to
0 views • 25 slides
Passive DNS And The Halting Problem by Joe St. Sauver, Ph.D.
Exploring the interplay between Passive DNS and the Halting Problem, this document presents insights shared by Dr. Joe St. Sauver at B|Sides Vancouver, BC in March 2015. The detailed presentation covers various aspects such as the dynamic format of the session, unique slide style, author's backgroun
0 views • 84 slides
Understanding Deliverability and IP Warming in Email Marketing
Explore the concepts of deliverability and IP warming to improve your email marketing strategy. Learn about the importance of sender reputation, key factors affecting email delivery, and the methodology for warming up IP addresses. Discover how to establish a positive sender reputation and navigate
0 views • 15 slides
Four List Cleaning Methods Related to Reachability to Improve Email Reachability – Benchmark Email
Bulk Mail Masters specializes in efficient, high-impact bulk email marketing services. We help businesses grow by delivering personalized email campaigns at scale, boosting engagement, conversions, and brand visibility. Reach your audience with preci
0 views • 7 slides
Four List Cleaning Methods Related to Reachability to Improve Email Reachability – Benchmark Email
Bulk Mail Masters specializes in efficient, high-impact bulk email marketing services. We help businesses grow by delivering personalized email campaigns at scale, boosting engagement, conversions, and brand visibility. Reach your audience with preci
0 views • 7 slides
Four List Cleaning Methods Related to Reachability to Improve Email Reachability – Benchmark Email
Bulk Mail Masters specializes in efficient, high-impact bulk email marketing services. We help businesses grow by delivering personalized email campaigns at scale, boosting engagement, conversions, and brand visibility. Reach your audience with preci
0 views • 7 slides
Office 365 Email & Security Workshop Highlights
Office 365 Email & Security workshop was held with presenters Jason Hetterle, Steve Garcia, and Joseph Andreason covering topics like security awareness, self-service password reset, Office 365 webmail features, and more. The agenda included discussions on security measures, a case study on an anato
0 views • 9 slides
Updates on ABS and Anti-Spam Efforts in Japan
The content discusses the challenges faced by the ABS committee, the need for new members due to changing dynamics, and the apology for lack of communication. It also highlights significant changes in Japan regarding Anti-Spam regulations, forming an Anti-Spam council to combat abuse. The post empha
0 views • 5 slides