HEAR: Higher Education Access Route
Learn about HEAR, the Higher Education Access Route, which provides a fair and equal opportunity for underrepresented school leavers to access third level education. Discover participating colleges, application process, and post-entry supports. Apply early for reduced points offers.
9 views • 41 slides
SACE Teachers Conference: Enhancing Professional Development in Education
The SACE Teachers Conference focuses on improving teacher education through developing a National Framework for Teacher Education in SA. The Ministerial Committee on Teacher Education aims to create a coordinated system for both initial and continuing professional education. Recommendations include
1 views • 34 slides
Enhancing Access to Medicines and Health Products through Innovative Approaches
Global Health Centre experts discuss how building access into innovation can ensure better access to medicines, vaccines, and health products. Key ideas include planting seeds for access early in innovation, exploring alternative innovation models, and rethinking the relationship between innovation
4 views • 20 slides
2022 Thales Access Management Index
Thales Access Management Index highlights the current landscape of access security, revealing insights on multi-factor authentication adoption, remote and privileged user access management, VPN usage trends, challenges faced, and preferences towards third-party access management. The report emphasiz
2 views • 9 slides
Guidelines for Expanded Access to Investigational Drugs and Devices
Providing guidance on types of Expanded Access for drugs, biologics, and devices, this content explains the concept of Expanded Access and the criteria that must be met. It covers different types of Expanded Access for drugs and devices, emphasizing the importance of patient safety and benefit. The
0 views • 10 slides
Tertiary Education Reform in Wales: The Future of Learning
The Tertiary Education and Research (Wales) Act aims to establish the Commission for Tertiary Education and Research (CTER) to oversee strategy, funding, and supervision of post-compulsory education in Wales. This legislation dissolves the Higher Education Funding Council for Wales (HEFCW) and focus
3 views • 20 slides
Personnel Safety Systems and Access Control at CERN Facilities
Personnel Safety Systems at CERN include ODH detection, fire safety measures, and access control to protect personnel from hazards. Various access control layers are implemented to regulate entry to different parts of the facility, ensuring only trained personnel access underground areas. Biometric
0 views • 19 slides
Education Policy and Development in South Sudan
South Sudan's education landscape is shaped by policies like the National Teacher Education Policy, Transitional Constitution, Right to Education, General Education Act, and Strategic Goals for building a prosperous, informed, and tolerant nation by 2040. The focus is on providing equal access to ed
0 views • 27 slides
Port of Stockton Restricted Area Access Control and ID Card Policy
Access to restricted areas at the Port of Stockton facilities requires possession of a TWIC (Transportation Worker Identification Credential). Only authorized personnel, such as employees, contractors, and those with regular access, may receive a Port Access Card after approval by the Facility Secur
0 views • 6 slides
Enhancing Capacity of Church Education Facilities for Education Transformation
The National Council for Technical and Vocational Education and Training (NACTVET) in Tanzania is focused on enhancing the capacity of church education facilities to implement ongoing education transformation. The presentation outlines the structure of Vocational Education and Training (VET) in Tanz
0 views • 21 slides
Importance of the Right to Education in Social Welfare Policies
The right to education is a fundamental human right recognized in various international conventions and laws. It includes provisions for free, compulsory primary education, accessible secondary education, and equitable higher education. Upholding this right is crucial for promoting equality, fosteri
0 views • 19 slides
Introduction to Database Security and Countermeasures
Database security is essential to protect data integrity, availability, and confidentiality. Countermeasures such as access control, inference control, flow control, and encryption can safeguard databases against threats. Access control restricts user access, inference control manages statistical da
0 views • 26 slides
O3 Access Control Solution Overview
O3 Access Control Solution offers unique selling points like single-seat management software, role-based permissions, customizable user information, and more. The system includes a compact controller with multi-format reader support and BACnet Access objects. It integrates with other O3 modules for
0 views • 10 slides
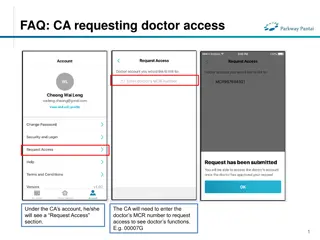
FAQs for Doctor and Clinical Assistant (CA) Account Access Management
Learn how CAs can request access to doctors' functions by entering the MCR number, how doctors can grant or remove CA access, and how CAs can manage access to multiple doctors. The process includes requesting, approving, and unlinking accounts, ensuring efficient and secure access management in a cl
0 views • 4 slides
Effective Implementation of Special & Inclusive Education Policy Overview
Providing an overview of the effective implementation of special and inclusive education policy, this content discusses inclusive education, special education, traditional education systems, historical dissatisfaction with dual systems, and the importance of the policy for children with special need
0 views • 29 slides
EventsHQ Virtual Event Registration: User Access and Setup Guide
This comprehensive guide provides step-by-step instructions on setting up virtual event registration using EventsHQ. It covers how users can access event details, join the event, and includes best practices for sharing access links. Learn how to utilize the Virtual Event Details feature, send remind
1 views • 19 slides
Accessible Voting System for Californians with Disabilities
Learn about the Remote Accessible Vote-by-Mail System in California, designed to empower voters with disabilities to securely access, mark, and return their ballots from any computer with internet access. Find out who is eligible to use the system, how to access and return the ballot, and the steps
0 views • 23 slides
Dell Networking Solutions for BYOD and Guest Access Projects
Dell offers end-to-end solutions for Bring-Your-Own-Device (BYOD) and guest access projects, enabling secure employee access and controlled connectivity for visitors. The framework includes mobility business models, device security, network protection, and scalability. Dell supports customers in imp
0 views • 11 slides
Importance of Mothers in Early Childhood Education
Mothers play a crucial role in early childhood education, especially in developing countries where many children lack access to formal education. Studies show a strong link between a mother's education level and the time she invests in her child's learning. By examining a 1997 education reform, rese
0 views • 8 slides
Access Higher Education Route for School Leavers - Overview 2023
The Higher Education Access Route (HEAR) aims to provide opportunities for under-represented school leavers to access third-level education in Ireland. HEAR ensures a fair chance for all Leaving Certificate students, with various participating colleges offering accessible pathways. Additionally, the
0 views • 39 slides
Lebanon RACE II Program for Education Improvement
The Lebanon RACE II program aims to enhance access, quality, and overall effectiveness of education systems for children and youth. Through pillars focusing on access, quality, and system strengthening, the program addresses various aspects such as improving educational services, learning environmen
0 views • 39 slides
Role-based Access Control Policies and Security Properties Overview
This content provides an overview of Role-based Access Control (RBAC) policies, Administrative RBAC (ARBAC) systems, and security properties in the context of access control in large organizations. It discusses the implementation of RBAC in various software systems, the assignment and revocation of
0 views • 18 slides
Open Access at Charles University: Opportunities and Challenges
Charles University is navigating the landscape of open access following the implementation of the Czech National Open Access Strategy. The university is working towards making all research articles and proceeding papers open access, monitoring article processing charges, and promoting open access as
0 views • 24 slides
Understanding Filesystem Security Principles and Access Control
Learn about filesystem security, general principles, discretionary access control (DAC), closed vs. open policy, closed policy with negative authorizations, and access control entries and lists. Discover how files and folders are managed, the role of access control lists (ACLs), and the different le
1 views • 56 slides
Understanding Ethernet and Multiple Access Protocols in Computer Networks
Exploring the fundamentals of Ethernet and multiple access protocols in computer networks, this content discusses the two primary categories of multiple access protocols - contention access and controlled access. It delves into topics such as CSMA/CD, LANs, performance of multiple access schemes, ad
0 views • 7 slides
Fostering Access to Higher Education for Refugees in Malaysia
The global trends show that access to higher education for refugees is limited, with only 3% having such access worldwide. In Asia Pacific, 7.7 million people of concern are hosted, including 3.5 million refugees. In Malaysia, as of early 2020, only 60 refugee youth were enrolled in tertiary educati
0 views • 7 slides
Understanding Shared Memory, Distributed Memory, and Hybrid Distributed-Shared Memory
Shared memory systems allow multiple processors to access the same memory resources, with changes made by one processor visible to all others. This concept is categorized into Uniform Memory Access (UMA) and Non-Uniform Memory Access (NUMA) architectures. UMA provides equal access times to memory, w
0 views • 22 slides
Understanding Access Changes and Community Relations at Fermilab
Access to Fermilab has become more complicated due to changing DOE guidance and security posture. Efforts are being made to streamline access while addressing security gaps. Public access to outdoor areas of the Fermilab campus is still encouraged, but communication regarding access changes needs im
0 views • 12 slides
Understanding Computer System Protection and Security
Mechanisms like protection and security ensure controlled access to a computer system's resources and prevent malicious activities. Protection involves defining access control levels through models, policies, and mechanisms. Security focuses on user authentication to safeguard stored information. Di
0 views • 25 slides
Understanding Access to ITU Information and Documents
Exploring the concept of access in the work of a dedicated group, this content delves into the types of information that could or should be made available to the public, along with considerations on when access should be provided. It highlights the varying stages of information dissemination, discus
0 views • 8 slides
Harvard Chan School 2021 Yearly Access Review Process
The Harvard Chan School conducts its annual Yearly Access Review (YAR) process to review user access to various financial systems. The process involves assessing permissions, levels of access, and organizational details for each team member. Instructions are provided on reviewing worksheets, adding
0 views • 19 slides
Understanding Security Access in PeopleSoft Finance
Explore the various levels of security access in PeopleSoft Finance, from basic entry access to transaction entry, approvals, and procurement processes. Learn how to request individual and department security access and find relevant forms on the financial services website. Discover the different ty
0 views • 11 slides
Proxy Access to Medications Implementation Stages
This document outlines the implementation stages for proxy access to medications. It covers agreements with healthcare providers, prerequisites including compliance and data sharing agreements, and systems configuration for access to medical records. The stages include setting up access for care pro
0 views • 7 slides
CSUEB Academic Access Enhancement and Excellence Fee Proposal
The CSUEB Academic Access Enhancement and Excellence Fee Proposal aims to enhance the academic environment, reduce student costs, and provide equal access to educational materials. Components include an Academic Access Enhancement fund, e-textbooks program, and provision of tablets/netbooks to all i
0 views • 23 slides
Evolution of Inclusive Education Policy in India
The evolution of inclusive education policy in India can be traced back to the initiatives of the Indian Education Commission and the Kothari Commission in the 1960s. These commissions highlighted the importance of providing education to children with disabilities within the general education system
0 views • 14 slides
Publishing Requirements and Challenges in Horizon Europe
The publication landscape under Horizon Europe presents challenges regarding compliance with publishing fee eligibility for hybrid journals and embargoes for open access. Hybrid journals feature subscription-based and open access parts, while open access journals require authors to pay open access f
0 views • 6 slides
Enhancing Access and Participation in Agricultural Education for Learners with Diverse Abilities
This research study, conducted from 2016 to 2018, focuses on determining the needs to enhance access and participation for learners with diverse ability levels in agricultural education programs. The study explores student and staff attitudes, identifies training needs, and provides recommendations
0 views • 11 slides
Special Education Process and Intervention Strategies in Alabama State Department of Education
Special Education Process and Intervention Strategies in Alabama's State Department of Education involve implementing intervention strategies in the general education program before referring a child for special education evaluation. The process includes referral meetings, consent for evaluation, in
0 views • 17 slides
Best Practices for Transradial Angiography and Intervention
This update highlights best practices for transradial angiography and intervention, including topics such as ultrasound guidance for transradial access, ulnar artery access recommendations, and future study opportunities. The importance of developing proficiency with ultrasound guidance, utilizing r
0 views • 15 slides
Evolution of Access Management in the 21st Century: RA21 Initiative
RA21, a joint initiative of STM Publishers and NISO, addresses the challenges of IP-based access management in the digital age. It aims to enhance user experience by optimizing access protocols across different stakeholder groups. The evolution from print to digital formats has led to the need for n
0 views • 12 slides