Understanding Computer Organization and Architecture
A computer system is a programmable digital electronics device that processes data as per program instructions to provide meaningful output. It comprises hardware and software components, with hardware being the physical parts and software essential for driving the hardware. Computer organization fo
14 views • 71 slides
Expert Cybersecurity and Digital Forensics Consultants
Protect your digital assets with expert cybersecurity and digital forensics consulting from AliasCybersecurity.com. Our team of specialists will keep your data secure..\n\n\/\/aliascybersecurity.com\/
2 views • 1 slides
Malware Forensic in Malaysia
OGIT Forensics, a leading Cyber Crime Forensic service in Malaysia, specializes in social networking analysis, security intelligence, mobile phone forensic, computer forensic, and audio-video forensic services. Our adept team conducts in-depth digital investigations, delivering accurate and efficien
1 views • 1 slides
Overview of Computer Hardware Components and Software Functions
Computer hardware components such as monitor, CPU, mouse, and projector are essential physical parts of a computer system, while software includes intangible programs like operating systems and utility software. Hardware components perform tasks like displaying data, processing information, and prin
8 views • 9 slides
Modernizing Forensics: Transforming Strategies for Better Justice
The field of forensics is evolving to meet new challenges and demands. Key drivers for change include systemic issues and the need for shared priorities in the forensic services marketplace. The response involves a national approach to deliver improved criminal justice outcomes, reduced harm, and in
1 views • 9 slides
Understanding Computer Architecture and Organization
Computer architecture and organization are fundamental aspects of computing systems. Computer architecture focuses on the functional design and implementation of various computer parts, while computer organization deals with how operational attributes come together to realize the architectural speci
3 views • 40 slides
Understanding Computer System and Organization
Computer Organization involves the logical structure of a computer, defining the interconnections of components for optimal performance. Computers process data through an Input-Process-Output cycle, with input, processing, and output units working together. The characteristics of a computer include
1 views • 20 slides
Understanding DNA Sequencing: Principles, Applications, and Techniques
DNA sequencing plays a vital role in various fields such as research, diagnostics, biotechnology, forensics, and biological systematics. By determining the order of nucleotide bases in a DNA molecule, it helps in understanding genetic sequences, identifying mutations, and completing projects like th
0 views • 17 slides
Computer Science Department Information and Courses Offered
The Computer Science Department provides information on courses offered for GCSE or BTEC qualifications, specifically focusing on the AQA GCSE in Computer Science. The course equips students with valuable thinking and programming skills essential in the modern workplace, covering key concepts and pr
3 views • 7 slides
Expert Cybersecurity and Digital Forensics Consultants
Protect your digital assets with expert cybersecurity and digital forensics consulting from AliasCybersecurity.com. Our team of specialists will keep your data secure.\n\n\/\/aliascybersecurity.com\/
3 views • 1 slides
OGIT Forensics has the most up-to-date high-speed disperser solutions in Malaysi
OGIT Forensics has the most up-to-date high-speed disperser solutions in Malaysia. They are experts in live forensic analysis, picture forensic examination, mobile phone forensic investigations, malware forensic detection, and digital forensic knowle
0 views • 1 slides
Anatomy of a Computer System: Hardware Components and Functions
A typical computer system consists of hardware and software working together to perform various computational tasks. The hardware components include the central processing unit (CPU), input/output devices, storage units, and the motherboard. The CPU acts as the main brain of the computer, performing
6 views • 6 slides
Understanding Computer Processing Systems
Computer processing systems consist of various components such as the control unit, ALU, input unit, CPU, output unit, memory, and more. Input devices feed raw data to the computer, while output devices provide processed information. The CPU plays a crucial role in executing instructions and data pr
0 views • 13 slides
EnCase Forensics: Official Study Guide Overview
Explore the key features of EnCase Forensics including the EnCase Environment, home screen navigation, browsing evidence, layout details, and case creation processes. Gain insights into working with evidence, templates, and custom options in a detailed manner to enhance your knowledge in computer fo
1 views • 32 slides
**Exploring Inquiry-Based Learning in Computer Science Education**
Inquiry-based learning (IBL) in computer science classrooms focuses on fostering communication, collaboration, decision-making, and problem-solving skills among students. The approach involves students constructing knowledge through independent, active activities based on real-world experiences. How
0 views • 18 slides
Computer Forensic Fundamentals in Modern Computing Environment
The field of computer forensics has become increasingly significant due to rising cybercrimes. Dr. SNS Rajalakshmi College of Arts & Science offers insights into computer forensic services, including data collection, analysis, and investigations. Digital evidence plays a crucial role in both legal p
0 views • 27 slides
Evolution of Algorithms and Computer Science Through History
The history of algorithms and algorithmic thinking dates back to ancient times, with the development of general-purpose computational machines by Charles Babbage in the 19th century marking a significant advancement. The term "computer science" emerged in 1959, encompassing theoretical computer scie
1 views • 39 slides
Strategies for Developing a National Nuclear Forensics Library
Nuclear forensics involves comparing data from unknown sources with known material characteristics to determine their origin. Establishing a national nuclear forensics library is crucial for identifying nuclear materials and promoting international cooperation in investigations. Key elements include
0 views • 18 slides
Guide to Setting Up a Computer Forensics Lab
Explore the essential aspects of creating a computer forensics lab, including where to establish it, tools needed, forensic software, storing evidence, access controls, chain of custody, and recording details about forensic images. Learn about the differences between criminal and civil investigation
0 views • 36 slides
EnCE EnCase Forensic Boot Disks and Acquiring Digital Evidence
Learn about creating EnCase forensic boot disks, utilizing them to acquire digital evidence, and understanding invisible HPA and DCO data. Discover the steps involved in DOS booting and drive-to-drive DOS acquisition in computer forensics.
0 views • 30 slides
Digital Forensics Investigation Process Overview
Explore the essential steps and considerations involved in approaching a computer forensics investigation, from testing hypotheses to assessing available data sources and seeking appropriate authorization. Learn about data carving, handling sensitive issues like child pornography, and the importance
0 views • 49 slides
Overview of Computer Input and Output Devices
Input devices of a computer system consist of external components like keyboard, mouse, light pen, joystick, scanner, microphone, and more, that provide information and instructions to the computer. On the other hand, output devices transfer information from the computer's CPU to the user through de
0 views • 11 slides
Biomedical Forensics: Solving Mysteries Through DNA Analysis
Explore the world of biomedical forensics with a focus on DNA extraction, blood typing, and fingerprinting techniques. Unravel murder mysteries using basic forensic skills and investigative procedures. Learn about the properties of DNA, forensic techniques like blood typing and fingerprinting, and t
0 views • 14 slides
Introduction to Computer Forensics: Uncovering Digital Evidence
Delve into the world of computer forensics with this comprehensive guide featuring key concepts, techniques, and tools used in investigating digital evidence for criminal and civil cases. Learn about the process of discovering, collecting, and analyzing data from computers and networks, as well as t
0 views • 17 slides
Exploring the Integration of Digital Forensics in Digital Curation Workflows
This content delves into the role of digital forensics within the digital curation workflow, examining how institutions can combine tools to meet local needs and implement handoffs between different systems. It also discusses the socio-technical factors and institutional drivers influencing decision
0 views • 27 slides
Understanding Computer Graphics: An Overview
Computer graphics involves creating images and animations using a computer through hardware and software systems. It has evolved significantly over the years, with advancements in generating various types of computer graphics. Learn about the basics of computer graphics, including digital image repr
0 views • 15 slides
Understanding Computer Crimes and Prevention Strategies
Computer crimes involve illegal acts utilizing computer systems, leading to various consequences. This lecture covers the types of computer system attacks, motives behind computer crimes, costs, prevention strategies, and reflection on the discussed topics. It emphasizes the increasing scope of comp
1 views • 20 slides
Understanding File Systems and Disk Basics in Computer Forensics
Explore the fundamentals of file systems and disk basics in computer forensics, covering topics such as disk preparation, partitioning, volume creation, file system formatting, FAT basics, and file allocation tables. Learn about disk structures, cluster allocation, and the functioning of FAT version
0 views • 24 slides
Computer Forensics: Capturing and Verifying Evidence
This guide focuses on the process of capturing and verifying digital evidence in computer forensics. Topics include creating forensic images of hard drives, using forensically sound methods, imaging internal hard drives, utilizing hardware write blockers, different types of forensic images, hashing
0 views • 28 slides
DNS Forensics & Protection: Analyzing and Securing Network Traffic
DNS Forensics involves using DNS traffic to analyze network health, detect anomalous behavior, and combat malicious activities. By understanding DNS activity on systems and implementing defense strategies, users and network providers can enhance security and privacy.
0 views • 16 slides
Network Forensics and Incident Response Overview
Explore the role of network forensics in incident response, focusing on the analysis tools that reveal insecurities in networks. Understand the importance of chain of custody in maintaining electronic evidence integrity and learn about monitoring network data for effective security measures.
0 views • 27 slides
VAST: A Unified Platform for Interactive Network Forensics
VAST is a comprehensive platform designed for interactive network forensics, addressing the increasing frequency of security incidents and large-scale data breaches. It aims to provide solutions for detecting, analyzing, and preventing breaches efficiently, with features like data exploration, query
0 views • 17 slides
Overview of Computer Science at Al Mustaqbal University College of Dentistry
Al Mustaqbal University College of Dentistry offers courses in computer science, covering topics like data reception, processing, storage, and output. The curriculum includes the study of computers as electronic devices, data and information, computer features, operating systems like Windows, and ta
0 views • 10 slides
Digital Evidence Processing and Computer Forensics Overview
Discover the importance of electronic evidence in high-tech investigations, the principles guiding its handling, and the step-by-step process involved in processing digital evidence. Learn about the critical role of trained personnel and the need for ongoing training in the dynamic field of computer
0 views • 20 slides
Understanding the Essence of Computer Science and Computational Thinking
Delve into the fundamentals of Computer Science and Computational Thinking through chapters discussing the nature of science, predictions in physics, and the distinction between Computer Science and Computer Information Systems. Explore the relationships between Math, Physics, and Computer Science i
0 views • 29 slides
Digital Forensics: Date and Time Analysis in Computer Systems
Conducting date and time analysis in computer forensics is essential to verify evidence accuracy. Tasks include adjusting time zone offsets, accessing registry keys, and adjusting zone settings for data integrity. Understanding timestamps aids in investigations for legal purposes.
0 views • 35 slides
Insights into Information Terrorism from IT Forensics Perspective
Delve into the world of terrorism and information technology through the lens of IT forensics. Explore topics such as the uncertainties surrounding cybersecurity and digital crimes, the role of security players, Locard's Exchange Principle, computer investigations, evidence analysis, investigator qu
0 views • 15 slides
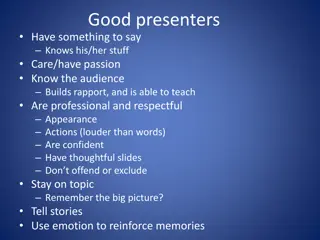
Effective Presentation Skills and Hair Analysis in Forensics
Good presenters engage their audience by knowing their subject well, showing passion, and utilizing effective communication strategies such as storytelling and emotion. Examples of successful presenters like Julian Treasure and Ken Robinson demonstrate these skills. On the other hand, poor presentat
0 views • 8 slides
National Nuclear Forensics Library Development Overview
The presentation highlights the establishment of the National Nuclear Forensics Library (NNFL) aimed at enhancing nuclear material identification and tracking to counter potential threats. It discusses the approach, goals, and challenges of developing a comprehensive inventory of nuclear materials,
0 views • 20 slides
Comprehensive Network Forensics Course Overview
Explore the essentials of network monitoring, forensics, and analysis in this detailed course by Jim Irving. Learn about network events capture, forensic data interpretation, working with PCAP and flow data, host forensics, logs, alerts, SIEMs, and more. Gain a broad understanding of network forensi
0 views • 102 slides