Enhancing Access to Medicines and Health Products through Innovative Approaches
Global Health Centre experts discuss how building access into innovation can ensure better access to medicines, vaccines, and health products. Key ideas include planting seeds for access early in innovation, exploring alternative innovation models, and rethinking the relationship between innovation
4 views • 20 slides
Enhancing Healthcare Efficiency, The Vital Role of Patient Access Services at MedKarma
In today's fast-paced healthcare landscape, patient access services stand as the cornerstone of efficient healthcare delivery. At MedKarma, we understand the pivotal role these services play in ensuring seamless patient experiences, optimizing operational efficiency, and ultimately improving healthc
2 views • 7 slides
Streamlining Care, Navigating Patient Access Services in Healthcare
In today's healthcare landscape, patient access services play a pivotal role in ensuring seamless care delivery. From scheduling appointments to navigating insurance processes, these services streamline the patient journey and enhance overall satisfaction. Let's delve into the key points of how pati
6 views • 6 slides
2022 Thales Access Management Index
Thales Access Management Index highlights the current landscape of access security, revealing insights on multi-factor authentication adoption, remote and privileged user access management, VPN usage trends, challenges faced, and preferences towards third-party access management. The report emphasiz
2 views • 9 slides
Enhancing Healthcare Accessibility, The Role of Patient Access Services by MedKarma
In the dynamic landscape of healthcare, accessibility stands as a cornerstone of quality patient care. Amidst the intricate network of medical services, patient access services emerge as a vital component, ensuring seamless and efficient navigation for individuals seeking healthcare solutions. At th
5 views • 7 slides
Guidelines for Expanded Access to Investigational Drugs and Devices
Providing guidance on types of Expanded Access for drugs, biologics, and devices, this content explains the concept of Expanded Access and the criteria that must be met. It covers different types of Expanded Access for drugs and devices, emphasizing the importance of patient safety and benefit. The
0 views • 10 slides
Personnel Safety Systems and Access Control at CERN Facilities
Personnel Safety Systems at CERN include ODH detection, fire safety measures, and access control to protect personnel from hazards. Various access control layers are implemented to regulate entry to different parts of the facility, ensuring only trained personnel access underground areas. Biometric
0 views • 19 slides
Port of Stockton Restricted Area Access Control and ID Card Policy
Access to restricted areas at the Port of Stockton facilities requires possession of a TWIC (Transportation Worker Identification Credential). Only authorized personnel, such as employees, contractors, and those with regular access, may receive a Port Access Card after approval by the Facility Secur
0 views • 6 slides
Proposal to Add National Security and Emergency Preparedness Priority Access Feature in IEEE 802.11be Amendment
The document proposes integrating the National Security and Emergency Preparedness (NSEP) priority access feature into the IEEE 802.11be standard to ensure seamless NSEP service experience, particularly in Wi-Fi networks used as last-mile access. The NSEP priority feature at the MAC layer is indepen
0 views • 12 slides
Medicaid Waivers and Services in Kentucky
Seven Counties Developmental Services Division in Kentucky provides a range of services including alcohol and drug addictions, mental health, developmental services, and more. The Division offers case management, behavior analysis, therapy services, supported employment, crisis services, grant-based
1 views • 25 slides
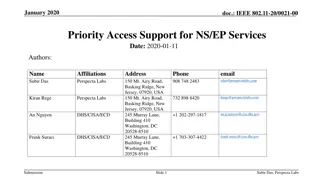
IEEE 802.11-20/0021-00 Priority Access Support for NS/EP Services Overview
This document discusses the importance of priority access support in IEEE 802.11be for National Security and Emergency Preparedness (NS/EP) services. It outlines the need for standardized mechanisms to ensure priority services in WLAN networks during NS/EP events when cellular coverage is unavailabl
1 views • 15 slides
Facilitating Access to GBV Services in Tigray: Service Mapping and Findings
This project in Tigray aims to enhance access to Gender-Based Violence (GBV) response services by mapping existing services, identifying gaps, and recommending improvements. With a focus on health, psychosocial, legal, and safety services, the initiative targets specific zones within the region. The
0 views • 10 slides
Introduction to Database Security and Countermeasures
Database security is essential to protect data integrity, availability, and confidentiality. Countermeasures such as access control, inference control, flow control, and encryption can safeguard databases against threats. Access control restricts user access, inference control manages statistical da
0 views • 26 slides
O3 Access Control Solution Overview
O3 Access Control Solution offers unique selling points like single-seat management software, role-based permissions, customizable user information, and more. The system includes a compact controller with multi-format reader support and BACnet Access objects. It integrates with other O3 modules for
0 views • 10 slides
The Long Term Plan in Mental Health Services: Key Ambitions and Achievements
Professor Tim Kendall, National Clinical Director for Mental Health, outlined key ambitions for mental health services in the NHS Long Term Plan by 2023/24. These include increased access to specialist perinatal mental health services, school-based support teams, and NICE-approved IAPT services. The
0 views • 9 slides
Empowering Individuals with Disabilities through Housing Access Services
Empowering individuals with disabilities, Housing Access Services (HAS) was initiated in 2009 as a partnership between Arc Minnesota and the Department of Human Services Housing Division. HAS assists with housing searches, financial burdens, and coordinates housing access for individuals eligible fo
1 views • 12 slides
Enhancing Voter Services through National Voters Services Portal (NVSP)
National Voters Services Portal (NVSP) was launched on National Voters Day in 2015 to provide citizens with user-friendly access to electoral registration services, aiming to increase transparency and ease of information access. The portal offers a range of services including electoral roll search,
0 views • 19 slides
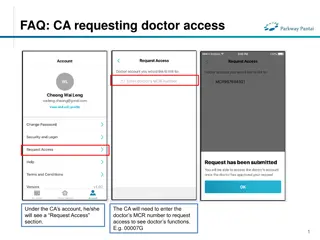
FAQs for Doctor and Clinical Assistant (CA) Account Access Management
Learn how CAs can request access to doctors' functions by entering the MCR number, how doctors can grant or remove CA access, and how CAs can manage access to multiple doctors. The process includes requesting, approving, and unlinking accounts, ensuring efficient and secure access management in a cl
0 views • 4 slides
Access Point: Individual Supports & Supportive Housing in Toronto
The Access Point provides centralized access to mental health support services and supportive housing in Toronto, partnering with over 45 service providers. Applicants can apply online for various services, including intensive case management and Assertive Community Treatment Teams. The application
0 views • 11 slides
EventsHQ Virtual Event Registration: User Access and Setup Guide
This comprehensive guide provides step-by-step instructions on setting up virtual event registration using EventsHQ. It covers how users can access event details, join the event, and includes best practices for sharing access links. Learn how to utilize the Virtual Event Details feature, send remind
1 views • 19 slides
Understanding Access to Healthcare in Northern Ireland
Access to healthcare services in Northern Ireland is crucial for the well-being of residents and eligible visitors. Family Practitioner Services play a significant role in providing advice, training, and verification for entitlement to publicly funded healthcare. The main legislation, including the
0 views • 19 slides
Key Access Services Audit Process Overview
This document provides a detailed guide on the Key Access Services Audit Process, including key steps for certifying signatories, assigning Key Auditors, and completing Key Audits. It covers processes for assigning auditors to departments, completing audits, and verifying audit results. Instructions
1 views • 14 slides
Accessible Voting System for Californians with Disabilities
Learn about the Remote Accessible Vote-by-Mail System in California, designed to empower voters with disabilities to securely access, mark, and return their ballots from any computer with internet access. Find out who is eligible to use the system, how to access and return the ballot, and the steps
0 views • 23 slides
Dell Networking Solutions for BYOD and Guest Access Projects
Dell offers end-to-end solutions for Bring-Your-Own-Device (BYOD) and guest access projects, enabling secure employee access and controlled connectivity for visitors. The framework includes mobility business models, device security, network protection, and scalability. Dell supports customers in imp
0 views • 11 slides
Role-based Access Control Policies and Security Properties Overview
This content provides an overview of Role-based Access Control (RBAC) policies, Administrative RBAC (ARBAC) systems, and security properties in the context of access control in large organizations. It discusses the implementation of RBAC in various software systems, the assignment and revocation of
0 views • 18 slides
Open Access at Charles University: Opportunities and Challenges
Charles University is navigating the landscape of open access following the implementation of the Czech National Open Access Strategy. The university is working towards making all research articles and proceeding papers open access, monitoring article processing charges, and promoting open access as
0 views • 24 slides
Understanding Filesystem Security Principles and Access Control
Learn about filesystem security, general principles, discretionary access control (DAC), closed vs. open policy, closed policy with negative authorizations, and access control entries and lists. Discover how files and folders are managed, the role of access control lists (ACLs), and the different le
1 views • 56 slides
Understanding Ethernet and Multiple Access Protocols in Computer Networks
Exploring the fundamentals of Ethernet and multiple access protocols in computer networks, this content discusses the two primary categories of multiple access protocols - contention access and controlled access. It delves into topics such as CSMA/CD, LANs, performance of multiple access schemes, ad
0 views • 7 slides
Understanding Shared Memory, Distributed Memory, and Hybrid Distributed-Shared Memory
Shared memory systems allow multiple processors to access the same memory resources, with changes made by one processor visible to all others. This concept is categorized into Uniform Memory Access (UMA) and Non-Uniform Memory Access (NUMA) architectures. UMA provides equal access times to memory, w
0 views • 22 slides
Understanding Pennsylvania's Medical Assistance Transportation Program (MATP)
The Medical Assistance Transportation Program (MATP) in Pennsylvania provides essential transportation services to access medical care. Governed by state plans and codes, MATP aims to offer access to medical, pharmacy services, chronic disease management, and preventative care. Transportation provid
0 views • 16 slides
Understanding Public Services in Modern Democracies
Public services play a crucial role in modern democracies, encompassing a wide range of essential services provided by the government to its citizens. These services, whether directly provided or publicly financed, are integral to ensuring equal access and upholding fundamental human rights. Public
0 views • 10 slides
Understanding Access Changes and Community Relations at Fermilab
Access to Fermilab has become more complicated due to changing DOE guidance and security posture. Efforts are being made to streamline access while addressing security gaps. Public access to outdoor areas of the Fermilab campus is still encouraged, but communication regarding access changes needs im
0 views • 12 slides
Understanding Computer System Protection and Security
Mechanisms like protection and security ensure controlled access to a computer system's resources and prevent malicious activities. Protection involves defining access control levels through models, policies, and mechanisms. Security focuses on user authentication to safeguard stored information. Di
0 views • 25 slides
Understanding Access to ITU Information and Documents
Exploring the concept of access in the work of a dedicated group, this content delves into the types of information that could or should be made available to the public, along with considerations on when access should be provided. It highlights the varying stages of information dissemination, discus
0 views • 8 slides
Harvard Chan School 2021 Yearly Access Review Process
The Harvard Chan School conducts its annual Yearly Access Review (YAR) process to review user access to various financial systems. The process involves assessing permissions, levels of access, and organizational details for each team member. Instructions are provided on reviewing worksheets, adding
0 views • 19 slides
Understanding Security Access in PeopleSoft Finance
Explore the various levels of security access in PeopleSoft Finance, from basic entry access to transaction entry, approvals, and procurement processes. Learn how to request individual and department security access and find relevant forms on the financial services website. Discover the different ty
0 views • 11 slides
Proxy Access to Medications Implementation Stages
This document outlines the implementation stages for proxy access to medications. It covers agreements with healthcare providers, prerequisites including compliance and data sharing agreements, and systems configuration for access to medical records. The stages include setting up access for care pro
0 views • 7 slides
CSUEB Academic Access Enhancement and Excellence Fee Proposal
The CSUEB Academic Access Enhancement and Excellence Fee Proposal aims to enhance the academic environment, reduce student costs, and provide equal access to educational materials. Components include an Academic Access Enhancement fund, e-textbooks program, and provision of tablets/netbooks to all i
0 views • 23 slides
Overview of Dentistry in England and Scotland
Dentistry in England and Scotland encompasses various services including NHS primary care dental services, hospital dental services, public dental services, dental public health services, and private dentistry. The NHS dentistry structure differs between England and Scotland, with data collection me
0 views • 9 slides
Publishing Requirements and Challenges in Horizon Europe
The publication landscape under Horizon Europe presents challenges regarding compliance with publishing fee eligibility for hybrid journals and embargoes for open access. Hybrid journals feature subscription-based and open access parts, while open access journals require authors to pay open access f
0 views • 6 slides