Maximizing Impact: The Role of Rich Snippets in SERPs"User Intent
User intent, also known as search intent, refers to the underlying goal or purpose a user has when performing an online search. It goes beyond the literal interpretation of keywords and focuses on understanding why a person is searching. Recognizing and catering to user intent is crucial for creatin
3 views • 10 slides
Pest control in Kolkata
Are you looking for professional pest control services in Kolkata? Socspl.com is here to provide the most reliable and efficient pest control services in Kolkata. We have extensive knowledge and experience in handling all kinds of pest infestations such as termite control, cockroach control, ant con
4 views • 8 slides
2022 Thales Access Management Index
Thales Access Management Index highlights the current landscape of access security, revealing insights on multi-factor authentication adoption, remote and privileged user access management, VPN usage trends, challenges faced, and preferences towards third-party access management. The report emphasiz
2 views • 9 slides
Personnel Safety Systems and Access Control at CERN Facilities
Personnel Safety Systems at CERN include ODH detection, fire safety measures, and access control to protect personnel from hazards. Various access control layers are implemented to regulate entry to different parts of the facility, ensuring only trained personnel access underground areas. Biometric
0 views • 19 slides
Linux User Capabilities and Namespace Management
Linux user namespaces and capabilities play a critical role in managing system security and permissions. Users and groups are assigned unique IDs, and processes are associated with the user's ID. The kernel enforces permission checks based on user IDs and group IDs, allowing root access to bypass ce
1 views • 14 slides
Processor Control Unit and ALU Implementation Overview
In Chapter 4, the processor's control unit and ALU are detailed in a simple implementation scheme. The ALU performs operations based on opcode values, while the control unit provides signals for various functions such as load/store, compare, and branch. Decoding techniques and control signal generat
2 views • 21 slides
Asian Pest Control - Professional Pest Management Services in Dhaka
Asian Pest Control offers top-quality pest control services in Dhaka, with a mission to be recognized as the best in the industry. Their highly trained professionals prioritize safety and environmental care while providing services like cockroach control, rodent control, snake repellent, lizard cont
1 views • 16 slides
Basic Computer Organization and Design - Timing and Control
The timing of all registers in a basic computer is governed by a master clock generator, with clock pulses controlling the flip-flops and registers in the system. Two main types of control organization are Hardwired Control and Micro-programmed Control. The former uses digital circuitry like gates a
3 views • 4 slides
Introduction to Database Security and Countermeasures
Database security is essential to protect data integrity, availability, and confidentiality. Countermeasures such as access control, inference control, flow control, and encryption can safeguard databases against threats. Access control restricts user access, inference control manages statistical da
2 views • 26 slides
Database Security Measures and Controls
Database security is crucial to protect against threats like loss of integrity, availability, and confidentiality. Countermeasures such as access control, inference control, flow control, and encryption are important for safeguarding databases. Access control involves creating user accounts and pass
1 views • 35 slides
National Labor Mapping Application User Roles and Access Overview
This detailed overview outlines the implementation plan, user roles, and access benefits of the National Labor Mapping Application. Users are assigned specific roles with established access through domain usernames, enhancing security measures. Different user roles such as VISN Coordinators, Site Te
1 views • 14 slides
O3 Access Control Solution Overview
O3 Access Control Solution offers unique selling points like single-seat management software, role-based permissions, customizable user information, and more. The system includes a compact controller with multi-format reader support and BACnet Access objects. It integrates with other O3 modules for
0 views • 10 slides
Marketing Control and Its Importance in Business
Marketing control is a crucial process for firms to evaluate the impact of their marketing strategies and initiatives, making necessary adjustments for better outcomes. It involves various aspects such as annual plan control, profitability control, efficiency control, and strategic control. The proc
1 views • 20 slides
Implementing Alert Messages and User Input Handling in Java
This tutorial guides you through creating alert messages, handling user input, defining functions, calling functions from the `onCreate` method, and creating an XML file for user data entry validation in Java. Learn how to display alerts for empty user credentials and process user actions accordingl
1 views • 6 slides
Control Plans in Process Management
A Control Plan is vital in controlling risks identified in the FMEA process, focusing on process and product characteristics, customer requirements, and establishing reaction plans for out-of-control conditions. It serves as a central document for communicating control methods and includes key infor
2 views • 20 slides
Collaborative Access Control in Webdamlog System Analysis
In the WebdamLog system, Serge Abiteboul delves into collaborative access control, loss of user control over data, and the need for a Distributed Knowledge Base. Discussing rule-based language, contradictions in data, and Webdamlog+Proba for access control and data management, this exploration sheds
1 views • 28 slides
Unsupervised Clickstream Clustering for User Behavior Analysis
Understanding user behavior in online services is crucial for businesses. This research focuses on utilizing clickstream data to identify natural clusters of user behavior and extract meaningful insights at scale. By analyzing detailed user logs, the study aims to reveal hidden patterns in user inte
0 views • 19 slides
Efficient User Management System for Health Facilities
Record and manage user details effectively with the new Version 2.0 User Management feature. RNTCP has now registered over 35,000 PHIs, 140,000 Private Health Facilities, 15,000 Private Labs, 31,000 Private Chemists, across 700 Districts and 8,000 TUs in Nikshay. Enhance operations by editing TU pro
0 views • 26 slides
User Roles and Responsibilities Overview
The user roles within the application are categorized into Account Manager, Data Steward, and Common Functionality roles. Each role comes with specific responsibilities such as managing user accounts, database management, data stewardship, incident management, and more. Non-privileged roles provide
1 views • 11 slides
EventsHQ Virtual Event Registration: User Access and Setup Guide
This comprehensive guide provides step-by-step instructions on setting up virtual event registration using EventsHQ. It covers how users can access event details, join the event, and includes best practices for sharing access links. Learn how to utilize the Virtual Event Details feature, send remind
2 views • 19 slides
Agile User Stories in Software Development
Agile user stories play a crucial role in software development by providing short descriptions of features desired by customers in a language they understand. This method allows for agile planning, efficient documentation, and effective communication between development teams and clients. Extracting
0 views • 30 slides
Enhancing User Experience Through Data Trails and Metrics
Andrea Thompson, a Sr. User Experience Manager at The Home Depot, highlights the importance of measuring and analyzing user experience metrics to understand and improve customer interactions. By investigating data trails from various touchpoints, such as customer sign-ups, interactions with associat
0 views • 17 slides
UNIX System Permissions and User Terminology
Explore the concept of UNIX system permissions, including discretionary access control (DAC) model, user terminology, file/directory access, access permission modes, categories of users, and checking permissions using examples. Learn about user IDs, groups, superuser privileges, ownership, access mo
1 views • 24 slides
User Identity and Access Tokens in Windows Security
Delve into the intricate world of user identity and access tokens in Windows security. Explore how user identities are represented, the structure of access tokens, and the significance of processes running under different user contexts. Gain insights into advanced Windows security principles and lea
2 views • 13 slides
User and Group Permissions in Linux Systems
Linux uses user and group permissions to control access to files, directories, and peripherals. Users are managed for security purposes by limiting access, with the root user having full system access. Grouping users into groups with specific access grants can enhance security. Each file is owned by
1 views • 23 slides
Role-based Access Control Policies and Security Properties Overview
This content provides an overview of Role-based Access Control (RBAC) policies, Administrative RBAC (ARBAC) systems, and security properties in the context of access control in large organizations. It discusses the implementation of RBAC in various software systems, the assignment and revocation of
0 views • 18 slides
User Interface Design Principles in Human-Computer Interaction
User interface design principles are crucial in Human-Computer Interaction. This content highlights key principles such as aesthetics, anticipation, autonomy, and color consideration for users with color blindness. It emphasizes the importance of user testing, user autonomy, and providing essential
0 views • 24 slides
Filesystem Security Principles and Access Control
Learn about filesystem security, general principles, discretionary access control (DAC), closed vs. open policy, closed policy with negative authorizations, and access control entries and lists. Discover how files and folders are managed, the role of access control lists (ACLs), and the different le
2 views • 56 slides
Interaction Design in Human-Computer Interaction
Interaction design focuses on creating interactive products that are easy, effective, and enjoyable to use. It aims to reduce negative user experiences while enhancing positive ones. Designing interactive products requires understanding user activities, interfaces, and device arrangements to support
0 views • 11 slides
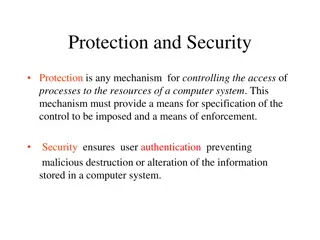
Computer System Protection and Security
Mechanisms like protection and security ensure controlled access to a computer system's resources and prevent malicious activities. Protection involves defining access control levels through models, policies, and mechanisms. Security focuses on user authentication to safeguard stored information. Di
0 views • 25 slides
Harvard Chan School 2021 Yearly Access Review Process
The Harvard Chan School conducts its annual Yearly Access Review (YAR) process to review user access to various financial systems. The process involves assessing permissions, levels of access, and organizational details for each team member. Instructions are provided on reviewing worksheets, adding
0 views • 19 slides
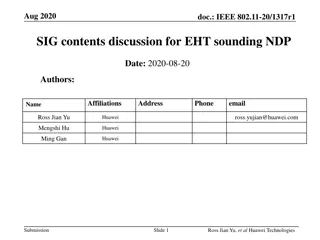
IEEE 802.11-20/1317r1 EHT-SIG Proposal Discussion
The document discusses EHT-SIG for single-user and sounding NDP in IEEE 802.11-20/1317r1, focusing on overflow bits, user fields, CRC, and tail formats. It covers the format details, subfields, and overhead compared to HE sounding, proposing specific bit allocations for different elements. The EHT-S
0 views • 16 slides
Administrator Deletes User - User Management System Storyboard
An administrator navigates through a user list, selects a user for deletion, confirms the action, and successfully removes the user from the system. The process involves interacting with user details, confirming the deletion, and updating the user list accordingly in a structured manner.
1 views • 4 slides
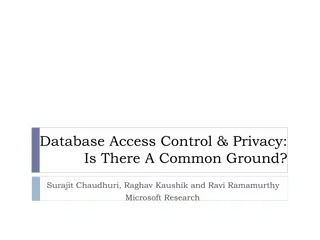
Database Access Control & Privacy: A Common Ground Explored
Exploring the intersection of database access control and data privacy, this paper delves into the implications of data privacy concerns on Database Management Systems (DBMS). It discusses the need for more than just access control mechanisms and highlights the evolving landscape of data publishing,
0 views • 29 slides
User Interface vs User Experience: Understanding the Essentials
Exploring the distinctions between User Interface (UI) and User Experience (UX) in human-computer interaction design. UI focuses on the space of interaction between humans and machines, while UX encompasses users' behavior, attitude, and emotions towards a product or service. The goal is to create i
0 views • 63 slides
Effective Regulation of Active Power in Renewable Energy Sources
The balance between generation and load is crucial in power systems operation. Various control levels ensure this balance, from frequency control to power station planning. DER units may lack control means, but specific configurations allow for frequency and voltage control. Performance indicators a
0 views • 51 slides
Evolution of Access Management in the 21st Century: RA21 Initiative
RA21, a joint initiative of STM Publishers and NISO, addresses the challenges of IP-based access management in the digital age. It aims to enhance user experience by optimizing access protocols across different stakeholder groups. The evolution from print to digital formats has led to the need for n
0 views • 12 slides
Context Switching and User-Kernel Interaction in Operating Systems
Context switching in operating systems involves a seamless transition between user-level threads without the kernel's awareness. User-level code manages register state and stack pointers, while user-kernel mode switching requires changing processor privilege levels and agreement on information excha
1 views • 25 slides
Control Plans in Process Management
Control plans are essential tools for managing process risks and ensuring quality control. They focus on controlling process and product characteristics, meeting customer requirements, and having reaction plans in place. A control plan contains key information such as control factors, specifications
1 views • 20 slides
A GUIDE TO COMPUTER USER SUPPORT
This material delves into the impact of technological changes on computer users, classification of end users, essential resources, common end-user software categories and problems. It also explores the job market demand, support service organization, skills required, and career paths for user suppor
0 views • 51 slides