Stochastic Storm Transposition in HEC-HMS: Modern Techniques and Applications
Explore the innovative methods and practical applications of Stochastic Storm Transposition (SST) in the context of HEC-HMS. Delve into the history, fundamentals, simulation procedures, and benefits of using SST for watershed-averaged precipitation frequency analysis. Learn about the non-parametric
3 views • 41 slides
Accessibility Monitoring Project Overview at the Portuguese National Observatory
The project overview at the Portuguese National Observatory on September 22, 2020, in Lisbon involved the implementation of Horizon 2020 Project to enhance awareness and learning through accessible monitoring activities. Evaluation methods outlined in the Directive and the PT transposition focused o
1 views • 12 slides
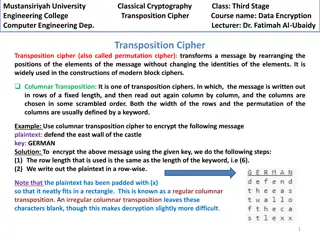
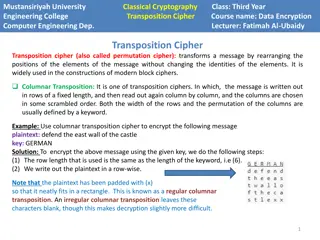
Columnar Transposition Cipher: Data Encryption Techniques at Mustansiriyah University Engineering College
Transposition ciphers, particularly the columnar transposition technique, are explored in the course "Data Encryption" at Mustansiriyah University Engineering College. The cipher involves rearranging message elements without changing their identities, making it crucial in modern block cipher designs
0 views • 4 slides
Challenges and Future of EU Environmental Law Enforcement
Challenges in enforcing EU environmental law include flawed transposition by Member States, insufficient application, and lack of resources. The implementation deficit hampers effective enforcement, requiring better legislative mechanisms. Transposition of directives is crucial but complex due to va
0 views • 22 slides
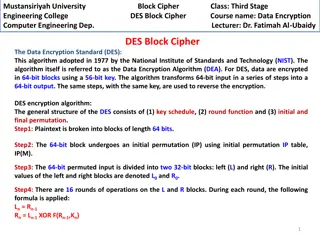
DES Block Cipher in Computer Engineering at Mustansiriyah University
Data Encryption Standard (DES) is a widely used algorithm for encrypting data in 64-bit blocks with a 56-bit key. This course at Mustansiriyah University covers the key components of DES, including the key schedule, round function, and initial/final permutation. Students learn about the encryption p
1 views • 8 slides
Enhancing Web Accessibility Monitoring and Learning in the Portuguese Observatory
The Portuguese Observatory WAI-Tools Final Open Meeting focused on raising awareness and improving learning in Member States regarding web accessibility. The Directive and PT Transposition Evaluation Methods highlight the need for monitoring and transparency. Evaluation methods include Automatic/Sem
1 views • 12 slides
Overview of Cryptography Techniques and Algorithms
Exploring the diverse realm of cryptography, this chapter delves into both nonmathematical and mathematical encryption methods. It covers substitution and transposition ciphers, steganography, hybrid systems, hashing, symmetric algorithms like DES and AES, as well as asymmetric algorithms utilizing
7 views • 21 slides
Evolution of Cryptography: From Ancient Techniques to Modern Security Mechanisms
Explore the evolution of cryptography from ancient techniques like the Caesar Cipher to modern security mechanisms like SSL, SSH, and IPSec. Learn how cryptography plays a crucial role in ensuring confidentiality, integrity, authentication, non-repudiation, and availability in network security. Disc
1 views • 62 slides
UNR WLTP: Regulations Update for Vehicle Type Approval
This document details the transposition of GTR15 (WLTP) and GTR19 (Evap) into UN Regulations, focusing on the scope, definitions, and application for approval of vehicle categories M1, M2, N1, and N2. It outlines requirements for emissions testing, carbon dioxide, fuel consumption, electric energy c
0 views • 38 slides
Transposition of GTR20 into UN Regulations: Draft Amendments Overview
Japan and the European Commission are aligning with the administrative provisions of the UN 98 Agreement by transposing GTR20 into UN Regulations. The proposed amendments focus on incorporating technical provisions of GTR20 into existing UNRs while maintaining clarity on scope and safety requirement
0 views • 10 slides
ADFGVX Cipher: Encryption and Decryption Techniques
Discover the ADFGVX cipher, a historical encryption method used to secure messages during World War I. Learn about Fritz Nebel and Gino Painvin, who played significant roles in its development. Explore the Polybius Square invented by Polybius in the 2nd century BC for converting letters to numbers.
0 views • 14 slides
Transposition Cipher Techniques in Modern Block Ciphers
Transposition ciphers, specifically columnar and double columnar transpositions, are explored in the context of data encryption and computer engineering at Mustansiriyah University Engineering College. These techniques involve rearranging message elements without changing their identities, providing
0 views • 4 slides
Montenegro EU Accession Negotiating Team for Chapter 27 Environment
The Montenegro EU Accession Negotiating Team for Chapter 27 Environment discussed regulations, legislative frameworks, and institutional frameworks related to environment and climate change. Topics included the EU Timber Regulation, national laws on forests and inspection supervision, as well as the
3 views • 13 slides
Optimizing MIH SA Establishment for Single Radio Handover
This presentation discusses the optimization of MIH (Media Independent Handover) Security Association (SA) establishment for single radio handover. It covers the key points and methods proposed for enhancing the communication between Mobile Node (MN) and Top Point of Service (TPoS) using cipher suit
3 views • 6 slides
Block Ciphers in Cryptography
Explore the principles of block ciphers in modern cryptography, focusing on the Data Encryption Standard (DES) and its design principles. Learn about block cipher encryption, Feistel block cipher structure, n-bit block ciphers, ideal block ciphers, key length considerations, and challenges with idea
0 views • 44 slides
Symmetric Key Block Ciphers - Overview and Implementation
Delve into the world of symmetric key block ciphers through a detailed exploration of classical ciphers like substitution and transposition, modern cryptography advancements, DES encryption, Simplified DES, key scheduling, expansion functions, S-Box usage, and more. Discover the intricacies of encry
0 views • 40 slides
Encryption Techniques: From Transposition Ciphers to Rail Fence Ciphers
Explore the world of encryption techniques, diving into transposition ciphers and rail fence ciphers. Learn about encryption, decryption, plaintext, ciphertext, keys, and the art of secret writing. Discover how transposition ciphers reorder letters without changing their values and how rail fence ci
0 views • 26 slides
Impact of Changes in Radiation Protection Legislation on Dentistry Practice
Changes in radiation protection legislation are affecting the practice of dentistry, particularly in areas such as graded authorization, updated dental codes of practice, and enforcement of patient protection requirements. The European Directive and transposition of regulations play key roles in ens
2 views • 14 slides
Training and Social Security Schemes for Fishers in the EU: State of Play and Perspectives
This presentation discusses the mutual recognition of certificates of competency for fishers across the EU and the social security schemes in place. The focus is on the international legal framework, challenges, and recommendations for improving training and certification standards to enhance safety
0 views • 17 slides
Trailblazing Maize Cytogeneticist: Barbara McClintock's Revolutionary Discoveries
Barbara McClintock, a pioneering geneticist, revolutionized the field of maize cytogenetics through her groundbreaking discoveries on genetic recombination, transposition, and gene expression. Her innovative techniques and concepts reshaped our understanding of chromosomes and gene regulation, leadi
0 views • 21 slides
Key Principles in Cryptography: Kerckhoff's and Key Space
Understanding fundamental principles in cryptography, including Kerckhoff's principle, key space requirements, and the importance of secure private-key encryption. Exploring the Shift Cipher's security, key space size considerations, and the need for heuristic constructions for proving scheme securi
0 views • 51 slides
Overview of Modern Cryptography and Data Encryption Standard (DES)
Exploring modern cryptography including symmetric key block ciphers, public key ciphers, stream ciphers, and post-quantum ciphers. Focus on Data Encryption Standard (DES), Simplified DES, Feistel cipher, key schedule, expansion function, S-Box, DES encryption, and decryption processes.
1 views • 37 slides
Perineal Hernias in Veterinary Surgery
Perineal hernias are a common condition in uncastrated males but can also occur in females and cats. Weakness in the pelvic diaphragm can lead to herniation due to factors like hormonal disorders, prostatic diseases, and rectal issues. The symptoms include swelling in the perineal region, and diagno
0 views • 25 slides
Matrix Operations and Properties
Dive into the world of matrices with this comprehensive guide covering unary operations, matrix transposition, symmetry, trace calculation, and determinant computation. Explore examples and definitions to grasp these fundamental concepts in linear algebra effectively.
0 views • 42 slides
Overview of Data Protection Law Transposition in Swaziland
Presentation on the transposition of data protection law in Swaziland, discussing the background, national assessment, purpose of the law, objectives of the SADC model law, and the approach to drafting the Data Protection Bill. This includes establishing a Data Protection Authority, harmonizing appr
0 views • 21 slides
Denotative Meaning and Translation Issues in Arabic Language
The article delves into denotative meaning, semantic repetition, synonym/near-synonym repetition, grammatical transposition, and semantic distancing techniques in Arabic language translation. It discusses how Arabic utilizes various forms of repetition and transposition that differ from English, sho
0 views • 15 slides
Crack the Code: A Journey into Transposition Ciphers
Mathematicians play a crucial role in industries like telecommunications and internet companies by condensing data and ensuring error detection. Transposition ciphers, like the Scytale used by Romans, offer a challenging way to encrypt messages. Test your skills with code-breaking challenges and exp
0 views • 4 slides
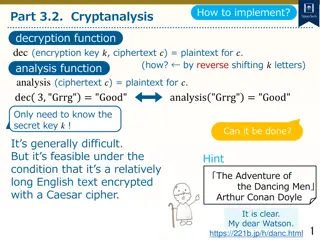
Cryptanalysis and Decryption Techniques for Caesar Cipher
Learn how to decrypt Caesar cipher text using cryptanalysis techniques by analyzing letter frequencies and determining the secret key through character analysis. Explore methods to count character frequencies and find the most common letter to decipher encrypted messages.
0 views • 11 slides
Implementation of Antitrust Damages Directive: Romanian Experience
In Romania, the transposition of the Antitrust Damages Directive involved key steps such as consultations, legal amendments, and drafting a new Act on Antitrust Damages Actions. The process also included decisions to adopt a new Act on Damages Claims for competition law breaches, addressing issues l
0 views • 9 slides
Overview of EU Environmental Law Harmonization and Implementation
This document delves into the basics of EU environmental law, highlighting the harmonization of environmental requirements, transposition and implementation of EU laws, the roles of national courts and the CJEU. It emphasizes the essential objective of protecting the environment within the EU framew
0 views • 65 slides
Analysis of Web Accessibility Directive Implementation by the European Disability Forum
The European Disability Forum conducted a survey on the transposition and implementation of the Web Accessibility Directive, focusing on awareness, feedback mechanisms, and examples. Results revealed challenges in transposition, dissatisfaction with outcomes, and barriers in website accessibility im
0 views • 15 slides
Fun Spy Challenges for Beavers - Crack the Codes!
Dive into exciting spy missions with a group of clever beavers! Decode secret messages using various encryption techniques such as switching codes, letter grouping, Pig Pen cipher, Morse code, and Caesar cipher. Test your spy skills as you unravel each challenge to reveal hidden messages. Unleash yo
0 views • 6 slides
EASA Update on Regulation 2020/469 and FIS/AFIS Requirements
EASA's update highlights the comprehensive set of requirements introduced by Regulation 2020/469 for Air Traffic Services (ATS) as of January 27, 2022. It emphasizes the alignment with ICAO provisions, transposition of SARPs and PANS for uniform application, and the certification of Flight Informati
0 views • 13 slides
Fundamentals of Cryptography and Network Security
Explore the basics of cryptography, including classical encryption techniques, terminology definitions, types of encryption operations, cryptanalysis objectives and attacks, and the concept of cipher strength. Uncover the principles and methods behind encryption and decryption, key distinctions betw
0 views • 52 slides
Unlock the Challenges in Cipher Cove: A STEM Adventure
Explore Cipher Cove and tackle five cryptographic challenges involving different ciphers such as Caesar Shift, Pigpen, Transposition, Substitution, and Periodic Table. Put your problem-solving skills to the test by deciphering hidden clues and codes to progress through each challenge and ultimately
0 views • 6 slides
Symmetric Encryption and Basic Terminology
This content covers symmetric encryption techniques, substitution and transposition methods, rotor machines, and basic cryptographic terminology such as plaintext, ciphertext, cipher, and key. It also discusses the requirements and assumptions for secure symmetric encryption, and the model of symmet
0 views • 49 slides
Montenegro's Progress in Environmental Legislation
Montenegro's journey towards EU accession focuses on Chapter 27: Environment and Climate Change. The presentation covers transposition directives, laws, and access to environmental information. Montenegro emphasizes the importance of the Aarhus Convention and its commitment to a healthy environment.
0 views • 31 slides
Power System Operation and Control
Learn about transmission line and transformer models in power systems, including topics like transposition, conductor bundling, inductance calculations, and more. Explore the concepts behind geometric mean distance, balancing systems, and bundled conductor configurations to understand the complexiti
0 views • 36 slides
Muddiest Point: Questions on RSA, DDoS Attacks, and Block Cipher Algorithms
In this collection of images, various concepts related to RSA encryption, DDoS attacks, block cipher algorithms like DES and AES, TCP protocols, and real-life applications of cryptography are explored. The images cover topics such as the Mirai-infected devices used in a DDoS attack on Dyn, differenc
0 views • 14 slides
Cryptography: Modern Symmetric Ciphers
Explore the world of modern symmetric ciphers used in network security, from encryption basics to advanced techniques like Block vs. Stream Cipher and Autokeyed Vigenere Cipher. Understand the importance of encryption in providing protection for confidentiality, authentication, integrity, and non-re
0 views • 60 slides