SINGLE DISCONNECTING LINK EARTH BAR
Nexus Metal & Alloys is one of the leading manufacturers, exporters, and suppliers of world-class Copper Single Disconnecting Link Earth Bar, Six Way Earth Bar with Single Disconnecting Link, Copper Single Disconnecting Earth Bar at very cheap rate from Mumbai, Maharashtra, India.
5 views • 4 slides
Maximizing Impact: The Role of Rich Snippets in SERPs"User Intent
User intent, also known as search intent, refers to the underlying goal or purpose a user has when performing an online search. It goes beyond the literal interpretation of keywords and focuses on understanding why a person is searching. Recognizing and catering to user intent is crucial for creatin
3 views • 10 slides
Operating Systems
An operating system is a crucial program that manages all other programs on a computer. It handles tasks like input recognition, file management, and device control. There are different types of operating systems such as single-user, single-task systems, multi-user, multi-task systems, real-time ope
6 views • 11 slides
Single-Family Rental, What You Need to Know
The world of single-family rentals (SFRs) is evolving rapidly, emerging as a highly popular choice for investors and tenants alike. From an investment perspective, the SFR market offers promising opportunities. As of 2023, the market accounts for 39% of all rentals in the United States, with over se
11 views • 8 slides
Single-Family Rental, What You Need to Know
The world of single-family rentals (SFRs) is evolving rapidly, emerging as a highly popular choice for investors and tenants alike. From an investment perspective, the SFR market offers promising opportunities. As of 2023, the market accounts for 39% of all rentals in the United States, with over se
8 views • 8 slides
Empowering Single Mothers: The Vigilant Mothers Association
Vigilant Mothers is an association dedicated to defending the rights of single mothers, providing support, and advocating for systemic changes. They address the challenges faced by single-parent families, particularly focusing on the gendered aspects affecting mothers. Through lobbying efforts and s
1 views • 15 slides
Navigating Divorce: A Guide for Newly Single Parents
Discover essential tips and advice for newly single parents navigating the challenges of divorce. Our guide is here to support you every step of the way. Get expert guidance on navigating divorce marriage site as a newly single parent. Our comprehensive guide offers practical tips and resources to h
2 views • 1 slides
The Evolution of Graphical User Interfaces in Computing
Graphical User Interfaces (GUIs) have transformed computing into a more user-friendly and interactive experience, emphasizing the shift from technology-focused to human-centric living. This chapter delves into the various aspects of GUIs, including I/O alternatives, common GUI tasks, programming per
1 views • 32 slides
Single Entry System in Financial Accounting
Single Entry System is a simplified method used by small businesses to track their financial transactions. It lacks the rigor of double-entry bookkeeping and focuses on recording cash transactions and personal accounts. This system presents challenges in accurately determining profits and financial
0 views • 14 slides
Single Audits for Federal Fund Compliance
Explore the process and requirements of single audits for federal fund compliance, including when they are required, the responsibilities involved, and the importance of OMB Compliance Supplement. Learn how single audits provide assurance to federal agencies about fund usage compliance and the stand
1 views • 33 slides
Tatmeen Users Training - User Registration Process Overview
This document provides an overview of the user registration process for Tatmeen users, focusing on the registration of Single Point of Contact (SPOC) and non-SPOC users. It includes details on how users receive registration invitations, the different user types, steps for SPOC registration, data flo
2 views • 20 slides
Different Types of Operating Systems
An operating system is the crucial program that manages a computer's resources and acts as an interface between the user and the machine. Various types of operating systems exist, including real-time, multi-user vs. single-user, multi-tasking vs. single-tasking, distributed, and embedded systems. Re
1 views • 11 slides
Implementing Alert Messages and User Input Handling in Java
This tutorial guides you through creating alert messages, handling user input, defining functions, calling functions from the `onCreate` method, and creating an XML file for user data entry validation in Java. Learn how to display alerts for empty user credentials and process user actions accordingl
1 views • 6 slides
Enhancing Supportive and Accessible User Experiences Through Single Sign-Ons and Peer Feedback
Empower your users with mobile-supportive single sign-ons, inclusive environments, and seamless peer-to-peer feedback. Ensure accessibility at all times, monitor skill development, and create positive user experiences. Utilize instant feedback mechanisms, track progress, and implement seamless seque
0 views • 9 slides
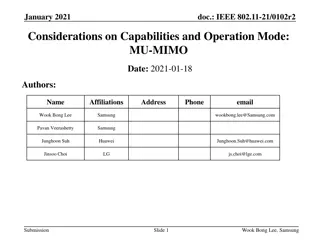
IEEE 802.11 MU-MIMO Considerations and Test Results
This document from January 2021 discusses considerations and test results related to IEEE 802.11 MU-MIMO (Multi-User Multiple Input Multiple Output) technology. It covers field test results, test setups, test scenarios, observations, and conclusions regarding supported NSS (Number of Spatial Streams
4 views • 22 slides
Advances in X-ray Phase Contrast Imaging with Single Crystal Scintillators
This presentation discusses the use of single-crystal scintillators in X-ray imaging systems to optimize spatial resolution and efficiency. By utilizing modified FO plates and single crystals, a new paradigm has been introduced to enhance the point-spread function while maintaining or improving effi
0 views • 43 slides
Unsupervised Clickstream Clustering for User Behavior Analysis
Understanding user behavior in online services is crucial for businesses. This research focuses on utilizing clickstream data to identify natural clusters of user behavior and extract meaningful insights at scale. By analyzing detailed user logs, the study aims to reveal hidden patterns in user inte
0 views • 19 slides
Domain-Specific Visual Analytics Systems: Exploring Expert User Insights
This presentation delves into domain-specific visual analytics systems focusing on political simulation, wire fraud detection, bridge maintenance, and more. It emphasizes leveraging user expertise for effective system design and evaluation, highlighting the importance of user insights in data analys
0 views • 27 slides
Efficient User Management System for Health Facilities
Record and manage user details effectively with the new Version 2.0 User Management feature. RNTCP has now registered over 35,000 PHIs, 140,000 Private Health Facilities, 15,000 Private Labs, 31,000 Private Chemists, across 700 Districts and 8,000 TUs in Nikshay. Enhance operations by editing TU pro
0 views • 26 slides
User Roles and Responsibilities Overview
The user roles within the application are categorized into Account Manager, Data Steward, and Common Functionality roles. Each role comes with specific responsibilities such as managing user accounts, database management, data stewardship, incident management, and more. Non-privileged roles provide
1 views • 11 slides
Agile User Stories in Software Development
Agile user stories play a crucial role in software development by providing short descriptions of features desired by customers in a language they understand. This method allows for agile planning, efficient documentation, and effective communication between development teams and clients. Extracting
0 views • 30 slides
Exploring Usability Testing of New Interface in JMP Custom Design
In this study by Mark Bailey et al. from JMP Statistical Discovery in the USA, the focus lies on testing the usability of a new user interface using JMP Custom Design. The researchers highlight the significance of adding factors in the initial experiment design workflow to enhance user experience. U
0 views • 8 slides
Guide to Court Management System User Administration
Learn how to effectively manage user profiles, create sub-user accounts for legal assistants, update user information, and create associates' accounts in the Court Management System for the 17th Judicial Circuit Court of Florida. Detailed instructions provided for changing usernames, passwords, and
0 views • 15 slides
Enhancing User Experience Through Data Trails and Metrics
Andrea Thompson, a Sr. User Experience Manager at The Home Depot, highlights the importance of measuring and analyzing user experience metrics to understand and improve customer interactions. By investigating data trails from various touchpoints, such as customer sign-ups, interactions with associat
0 views • 17 slides
Evolution of User Authentication Practices: Moving Beyond IP Filtering
The article explores the obsolescence of IP filtering in user authentication, highlighting the challenges posed by evolving technology and the limitations of IP-based authentication methods. It discusses the shift towards improving user experience and addressing security concerns by focusing on user
1 views • 22 slides
Introduction to Graphical User Interfaces (GUIs) in Python for Geographical Information Analysis
This content provides insights into creating Graphical User Interfaces (GUIs) in Python for Geographical Information Analysis. It covers the basics of GUI development using TkInter and event-based programming with a focus on user experience design and functionality. The lecture emphasizes the import
0 views • 45 slides
Importance of Human-Computer Interaction (HCI) in User Interface Design
Human-Computer Interaction (HCI) is a crucial discipline focusing on creating interactive computing systems that are user-friendly and efficient. This involves designing, evaluating, and implementing systems that cater to users' needs, ultimately improving user satisfaction and productivity. The fie
1 views • 39 slides
Importance of Single Crystals in Crystal Growth and Applications
Single crystals differ from polycrystalline samples due to their periodic atomic arrays in three dimensions, essential for applications in the electronic and optical industries. Growing single crystals is crucial for structure determination and intrinsic property measurements. Various methods of cry
0 views • 11 slides
User Interface Design Principles in Human-Computer Interaction
User interface design principles are crucial in Human-Computer Interaction. This content highlights key principles such as aesthetics, anticipation, autonomy, and color consideration for users with color blindness. It emphasizes the importance of user testing, user autonomy, and providing essential
0 views • 24 slides
Principles of User Interface Design in Human-Computer Interaction
User interface design principles play a crucial role in Human-Computer Interaction, emphasizing the importance of aesthetics, anticipation, autonomy, color usage, and consistency in creating effective interfaces. These principles guide designers in crafting interfaces that are visually appealing, us
0 views • 24 slides
Enhancing User Experience Through Dynamic Recommendations
In this presentation, the xStreams system is introduced for recommending items to users with changing preferences. The methodology involves learning user preferences, finding similar users, and providing item recommendations. The motivation behind the system includes dealing with vast amounts of dat
0 views • 27 slides
Interaction Design in Human-Computer Interaction
Interaction design focuses on creating interactive products that are easy, effective, and enjoyable to use. It aims to reduce negative user experiences while enhancing positive ones. Designing interactive products requires understanding user activities, interfaces, and device arrangements to support
0 views • 11 slides
Enhancing Recipe Recommendations with C-KGAT Model
Introducing the Contrastive Knowledge Graph Attention Network (C-KGAT) for personalized recipe recommendation, addressing user preferences and noise in interactions. The model leverages a collaborative knowledge graph, user-recipe interactions, and textual features to recommend top-K recipes to user
0 views • 21 slides
Semi-Supervised User Profiling with Heterogeneous Graph Attention Networks
Utilizing heterogeneous graph attention networks, this study addresses the limitations of existing user profiling methods by integrating multiple data types and capturing rich interactions in user data. The approach tackles critical problems in representation learning, information propagation, and m
0 views • 15 slides
IEEE 802.11-20/1317r1 EHT-SIG Proposal Discussion
The document discusses EHT-SIG for single-user and sounding NDP in IEEE 802.11-20/1317r1, focusing on overflow bits, user fields, CRC, and tail formats. It covers the format details, subfields, and overhead compared to HE sounding, proposing specific bit allocations for different elements. The EHT-S
0 views • 16 slides
Administrator Deletes User - User Management System Storyboard
An administrator navigates through a user list, selects a user for deletion, confirms the action, and successfully removes the user from the system. The process involves interacting with user details, confirming the deletion, and updating the user list accordingly in a structured manner.
1 views • 4 slides
Systematic Reduction of Proton-Removal Cross Section in Neutron-Rich Medium-Mass Nuclei
Single-nucleon knock-out reactions in neutron-rich medium-mass nuclei were studied to investigate the reduction of proton-removal cross section. Short-range correlated nucleon pairs, especially protons, were found to impact the probability of single-proton removal processes. Experimental measurement
0 views • 8 slides
User Interface vs User Experience: Understanding the Essentials
Exploring the distinctions between User Interface (UI) and User Experience (UX) in human-computer interaction design. UI focuses on the space of interaction between humans and machines, while UX encompasses users' behavior, attitude, and emotions towards a product or service. The goal is to create i
0 views • 63 slides
Context Switching and User-Kernel Interaction in Operating Systems
Context switching in operating systems involves a seamless transition between user-level threads without the kernel's awareness. User-level code manages register state and stack pointers, while user-kernel mode switching requires changing processor privilege levels and agreement on information excha
1 views • 25 slides
A GUIDE TO COMPUTER USER SUPPORT
This material delves into the impact of technological changes on computer users, classification of end users, essential resources, common end-user software categories and problems. It also explores the job market demand, support service organization, skills required, and career paths for user suppor
0 views • 51 slides