Efficient Key Recovery Attack on SIDH
Efficient key recovery attack on Supersingular Isogeny Diffie-Hellman (SIDH) protocol. It explores the vulnerability of the protocol and proposes a concrete solution. The attack leverages auxiliary points to solve the isogeny problem and reveals instances of the common secret key.
5 views • 22 slides
Myocardial infarction
Myocardial infarction (heart attack), including its types, causes, symptoms, and first aid techniques. Discover how to recognize the signs of a heart attack and provide immediate care at home or in a hospital setting.
2 views • 14 slides
Fernandes Thriving in United's Resurgent Attack^J Euro 2024 Success
Fernandes Thriving in United's Resurgent Attack, Euro 2024 Success\n\nhttps:\/\/blog.worldwideticketsandhospitality.com\/2024\/02\/15\/fernandes-thriving-in-uniteds-resurgent-attack-euro-2024-success\/\n\nUEFA Euro 2024 fans from all over the world can book European Championship 2024 Tickets on our
2 views • 5 slides
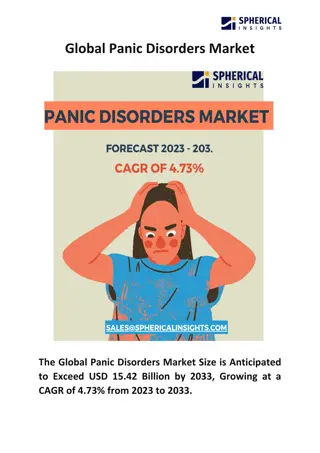
Global Panic Disorders Market
The Global Panic Disorders Market Size is Anticipated to Exceed USD 15.42 Billion by 2033, Growing at a CAGR of 4.73% from 2023 to 2033.\n\n
0 views • 5 slides
Dr. Arnab Pathak
Don't Let Fear Control You! Help for Panic Attacks & Phobias: Dr. Arnab. Dr. Arnab: Helping You Manage Anxiety & Fear. Panic Attacks & Phobias? See Dr. Arnab. Welcome to \"Panic Attack and Phobia - Dr. Arnab,\" a comprehensive resource dedicated to u
0 views • 3 slides
Understanding Panic Disorder: Symptoms, Diagnosis, and Management
Panic disorder is characterized by sudden, intense surges of fear or discomfort known as panic attacks. Individuals with this disorder may experience symptoms like chest pain, shortness of breath, dizziness, and a fear of having a heart attack. Differential diagnosis includes conditions like coronar
0 views • 8 slides
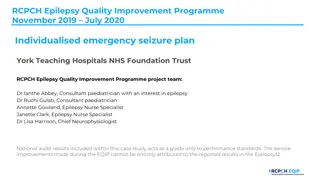
Enhancing Care for Children with Epilepsy: A Quality Improvement Initiative at York Teaching Hospitals NHS Foundation Trust
Development of a digital epilepsy passport aiming to improve care and reduce risks for children with complex epilepsy at York Teaching Hospitals NHS Foundation Trust. The initiative addressed issues such as misplacement of paper emergency seizure plans, leading to delays in treatment. By incorporati
0 views • 16 slides
Overview of Anxiety and Related Disorders
Anxiety disorders, such as PTSD, panic disorders, phobias, agoraphobia, and OCD, are characterized by varying degrees of fear and distress. Anxiety is a normal response to danger, but when it becomes chronic, it can lead to debilitating conditions. PTSD occurs post-trauma, panic disorders involve in
1 views • 42 slides
Understanding ICD-10-CM Coding for Seizure Disorders: A Comprehensive Guide
ICD-10-CM codes play a crucial role in diagnosing and managing seizure disorders, including epilepsy and non-epileptic seizures. This detailed guide covers the coding guidelines for various types of seizures, such as intractable epilepsy and conversion disorder with seizures. It also explains how th
0 views • 6 slides
First Nations Attack on Fort Michilimackinac 1763: Causes, Tribes, and Aftermath
The First Nations' attack on Fort Michilimackinac in 1763 was triggered by British actions that disrupted their way of life. The Ojibwe, Odawa, Potawatomi, Ottawas, and Hurons were involved in the attack, led by Chief Pontiac. Following the attack, the British did not rebuild the fort but establishe
1 views • 7 slides
Understanding Epilepsy and Driving: What Parents Need to Know
People living with epilepsy face challenges regarding driving, as seizures can pose a serious risk. Laws and regulations vary by state, requiring individuals to be seizure-free for a specific period. Teenagers with epilepsy may desire independence through driving, prompting discussions on seizure ma
1 views • 20 slides
Information Security Tabletop Exercise: Malware & DDOS Attack
Conduct a tabletop exercise focused on a malware and DDOS attack scenario at your company. Explore incident response, decision-making, communication, and coordination among your crisis team. Enhance preparedness and identify gaps in your cybersecurity strategy to effectively mitigate threats. The ex
0 views • 21 slides
Enhancing Cybersecurity for Windows Infrastructure: A Practical Guide
In this informative session, Vladimir Stefanovi, a seasoned System Engineer and Technical Trainer, sheds light on the vulnerabilities of Windows servers and provides valuable insights on how to protect and fortify your infrastructure against cyber threats. From traditional to modern attack vectors,
0 views • 21 slides
Panic Attack and Phobia Expert Care with Dr Arnab
Dr. Arnab Pathak, a neuropsychiatrist based in Kolkata, is known for his expertise in managing a variety of mental health conditions, including panic attacks and phobic anxiety disorders.\nContact us today and step into the serene embrace of Dr. Arna
0 views • 3 slides
Exploring Cinematography and Lighting in "Attack the Block
Discover how cinematography and lighting play a crucial role in shaping the visual aesthetics of the film "Attack the Block." Dive into key sequences and technical terminology to understand how these elements contribute to the overall look and feel of the movie. Explore the use of various camera sho
1 views • 10 slides
Understanding Network Denial of Service (DoS) Attacks
Network Denial of Service (DoS) attacks aim to disrupt services by overwhelming them with traffic. These attacks can occur at various layers of the network stack and exploit weaknesses to achieve their goal. Amplification attacks, such as the Smurf attack and DNS Amplification attack, can significan
2 views • 52 slides
Duane Wolf Attack Simulation Study: Insights for Law Enforcement Officers
Duane Wolf conducted an attack simulation study to test the speed at which an un-handcuffed suspect sitting on a curb can launch an attack on officers. The study involved volunteers in different leg positions to mimic real-life scenarios. Findings emphasized the importance of officers staying alert
0 views • 9 slides
Cross-Border Search and Seizure of Digital Evidence in Global Criminal Investigations
The globalization of criminal information has brought challenges to the search and seizure of digital evidence across borders. Issues like remote data storage, mutual legal assistance procedures, and technical difficulties in prosecution systems require a new approach. Initiatives such as the CLOUD
0 views • 13 slides
World War II in the Pacific: Unfolding of Events Post Pearl Harbor Attack
The war in the Pacific escalated post the Pearl Harbor attack with Japan's domination over various territories, including the Philippines leading to significant battles like the Japanese Invasion of the Philippines and Doolittle's Raid. American strategy, led by figures like Gen. MacArthur, played a
0 views • 12 slides
Adversarial Risk Analysis for Urban Security
Adversarial Risk Analysis for Urban Security is a framework aimed at managing risks from the actions of intelligent adversaries in urban security scenarios. The framework employs a Defend-Attack-Defend model where two intelligent players, a Defender and an Attacker, engage in sequential moves, with
1 views • 26 slides
Understanding Inspection, Search, Seizure & Arrest in Taxation Laws
Detailed exploration of the provisions related to inspection, search, seizure, and arrest under tax laws, including who may conduct inspections, the reasons for conducting them, the meaning of "reason to believe," and the role of the proper officer. Learn about the powers, procedures, and significan
2 views • 49 slides
Understanding the Fourth Amendment: Search and Seizure Laws in the United States
The Fourth Amendment of the United States Constitution protects individuals from unreasonable searches and seizures by the government. It outlines the requirements for obtaining a search warrant, defines a reasonable expectation of privacy, and details the types of searches allowed without a warrant
0 views • 18 slides
Understanding Blending Attacks on Mixes by Meng Tang
Explore the effectiveness of blending attacks on mixes, including steps of a blending attack, attack models, factors affecting the attack, defense strategies, and insights from the attacker's viewpoint.
0 views • 25 slides
Understanding Seizure Disorders and First Aid
Seizure disorders can have varying symptoms and may occur at any time in life. Immediate medical treatment is crucial for the first seizure. Factors like stress, illness, temperature changes, and photosensitivity can impact seizure thresholds. Different types of seizures, including focal aware tonic
0 views • 17 slides
Multi-phase System Call Filtering for Container Security Enhancement
This tutorial discusses the importance of multi-phase system call filtering for reducing the attack surface of containers. It covers the benefits of containerization, OS virtualization, and the differences between OS and hardware virtualization. The tutorial emphasizes the need to reduce the kernel
0 views • 32 slides
Understanding Vulnerabilities and Attack Surfaces in Cybersecurity
Exploring the complexities of system security metrics, this study delves into the challenges of measuring and improving security techniques. It highlights the limitations of current metrics, emphasizing the importance of evaluating the impact in deployment environments. By examining various vulnerab
0 views • 32 slides
Signature-Based IDS Schemes for Heavy Vehicles
This research focuses on developing signature-based Intrusion Detection System (IDS) schemes for heavy vehicles, particularly targeting the Controller Area Network (CAN) bus. The study delves into various attack vectors and payloads that have targeted commercial vehicles over the years, proposing th
0 views • 18 slides
Volleyball Referee Hand Signals for Common Violations
Learn the essential hand signals used by volleyball referees to indicate common violations during a game. Signals include illegal alignment, line violation, illegal hit, delay of service, over the net, net foul, legal back row attack, illegal attack of serve back row attack, and illegal block/screen
0 views • 26 slides
Understanding Key Events in "Of Mice and Men": Curley's Attack on Lennie
In Chapter Three of "Of Mice and Men," Curley's attack on Lennie is a key incident that reveals the brutal nature of Curley and the immense strength and vulnerability of Lennie. The event not only showcases effective characterisation but also evokes sympathy for Lennie while foreshadowing the conseq
0 views • 24 slides
Understanding Seizures and Epilepsy: A Practical Guide for Primary Care Providers
This practical guide provides valuable insights into seizures and epilepsy for primary care providers, covering topics such as different seizure types, epilepsy definition and treatment initiation, antiseizure medications, and status epilepticus management. Terminology and a clinical scenario are di
0 views • 53 slides
Defending Against Cache-Based Side-Channel Attacks
The content discusses strategies to mitigate cache-based side-channel attacks, focusing on the importance of constant-time programming to avoid timing vulnerabilities. It covers topics such as microarchitectural attacks, cache structure, Prime+Probe attack, and the Bernstein attack on AES. Through d
0 views • 25 slides
The Panic of 1819 and its Relevance Today - A Historical Analysis
The presentation delves into the significant yet overlooked Panic of 1819, caused by the Second Bank of the United States' credit expansion and intense cronyism. It explores the impact on free market thinking, the revival of Antifederalism, and the formation of the Jacksonian coalition. Drawing para
0 views • 19 slides
Peer-Led Wellness Course: Managing Panic and Anxiety
Educational opportunities at the Recovery College support positive mental well-being through peer-led courses tackling worry, providing a safe and supportive environment to share experiences, learn coping mechanisms for anxiety and panic, and build resiliency. Participants engage in activities like
0 views • 6 slides
Mechanism of Br2 Attack on Trans-Cinnamic Acid
The detailed anti-attack and syn-attack mechanisms of Br2 on trans-cinnamic acid are presented, illustrating the intricate steps involved in preventing or facilitating the attack of bromine on the compound. The process involves initial attack, bridgehead formation, bond rupture, bond stabilization,
0 views • 11 slides
Understanding the Use of Duress, Hold-up, and Panic Alarms
Learn about the appropriate use of duress alarms which signal forced deactivation, hold-up alarms for robberies, and panic alarms for emergencies. Discover when to use these alarms in life-threatening situations and when not to use them. Contact the False Alarm Reduction Association for more informa
0 views • 7 slides
Optimizing Channel Selection for Seizure Detection with Deep Learning Algorithm
Investigating the impact of different channel configurations in detecting artifacts in scalp EEG records for seizure detection. A deep learning algorithm, CNN/LSTM, was employed on various channel setups to minimize loss of spatial information. Results show sensitivities between 33%-37% with false a
0 views • 12 slides
The Financial Panic of 1932-33: A Historical Account
The Financial Panic of 1932-33 was marked by a stock market bubble, bank runs, and an international crisis. The Great Bubble of the 1920s led to severe economic repercussions, with banks facing liquidity problems and a lack of support from the Federal Reserve. Bankers' responses and the economic ind
0 views • 23 slides
Understanding Seizure Disorders in Children: Causes, Types, and Response
Seizure disorders in children can be caused by various factors such as brain development issues, brain injuries, infections, and more. Triggers like stress, lack of sleep, and certain lifestyle habits can lead to seizures. There are different types of seizures, including tonic-clonic, absence, myocl
0 views • 20 slides
Understanding Social Anxiety Disorder and Panic Disorder
Social anxiety disorder and panic disorder are common mental health conditions characterized by intense feelings of fear and anxiety in social situations. Individuals with these disorders may experience physical symptoms such as trembling, racing heart, and upset stomach, along with emotional signs
0 views • 18 slides
Social Engineering Attack Framework (SEAF) - Understanding the Process
Social Engineering Attack Framework (SEAF) provides a structured approach to executing social engineering attacks. It defines the attack framework, assists in planning and execution, and helps in verifying the success of the attack. The process involves identifying the attack goal, assessing potenti
0 views • 16 slides