BCA 601(N): Computer Network Security
Explore various aspects of computer network security including cryptography, IP security, web security, and system security. Learn about authentication, encryption, key management, and network management security. Real-world examples and best practices covered.
0 views • 23 slides
Airport Security Market to be Worth $25.27 Billion by 2031
\u00ae, the airport security market is projected to reach $25.27 billion by 2031, at a CAGR of 8.6% from 2024 to 2031. Some of the major factors driving the growth of this market are stringent government regulations for airport security and the growing number of air passengers. In addition, increasi
7 views • 5 slides
KEERTHI SECURITY - Best Security Agencies In Bangalore
Keerthi Security is a security and facility management services provider in Bangalore. We are committed to offering top-notch security services for commercial and residential places. We aim to offer very secure and reliable security services to everyone. Our best-trained security guards are very sha
10 views • 11 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
0 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Understanding the Role of Security Champions in Organizations
Security Champions play a vital role in decision-making concerning security engagement, acting as a core element in security assurance processes within a team. They foster a security culture, reduce dependency on the CISO, and promote responsible autonomy and continuous security education in the org
3 views • 13 slides
Enhancing Security Definitions for Functional Encryption
This study delves into the realm of functional encryption (FE) against probabilistic queries, highlighting the necessity for improved security definitions to address existing limitations such as counter-intuitive examples and impossibility results. The exploration leads to proposing a new security n
4 views • 20 slides
ADAS DRIVER TRAINING
In-cab devices in trucks include an ADAS camera and Driver Feedback Device (DFD) to alert drivers of unsafe conditions like short following, collisions, and lane departures. The DFD enables visual and audible alerts, with options to manually trigger events and adjust volume. Visual and audible alert
2 views • 8 slides
National Child Protection Alerts: Guidance on Practice and Issuance
National Child Protection Alerts are crucial for children subject to protection plans who go missing. This guide outlines the principles, process, and actions required to issue and manage alerts effectively. It emphasizes the importance of collaboration between relevant authorities and agencies to e
3 views • 9 slides
Shielding Your Organization: Chief Security Officer Recruitment Insights
\"Shielding Your Organization: Chief Security Officer Recruitment Insights\" offers invaluable guidance for businesses seeking to fortify their security posture by recruiting the right Chief Security Officer (CSO). This comprehensive resource delves into the intricacies of chief security officer rec
1 views • 7 slides
security service solutions
With skilled workers and cutting-edge technology, Ingenuity Security Solutions offers full tower security services in Maryland to keep your property safe. Our personalized security options for businesses include video, limiting who can enter, and assessing the risk. Keeping the highest standards of
0 views • 1 slides
Virginia Perspective 2020 State Supervised Eligibility Dashboard
The implementation of Virginia Perspective 2020, a state-supervised and locally-administered program, involves notifying staff through agency broadcasts and email alerts to detect fraud. Eligibility workers receive alerts through VaCMS Dashboard for PARIS matches, ensuring timely actions on case eli
0 views • 10 slides
Understanding the Roles of a Security Partner
Learn about the roles and responsibilities of a Security Partner, including requesting changes to security roles, approving security requests, and initiating access requests. Explore the overview of Workday Security, the security access request process, and the pre-request process flow. Discover how
2 views • 17 slides
Enhancing California's Election Cybersecurity Readiness
California has taken significant steps to bolster its election cybersecurity readiness, including rigorous source code reviews, red team testing, and open-ended penetration testing. The state has visited fusion centers, engaged local election officials, upgraded technology infrastructure, and establ
0 views • 6 slides
Enhancing Travel Planning with Fiji's National Journey Planner (NJP)
Fiji is introducing the National Journey Planner (NJP) to help travelers efficiently plan their bus journeys for various purposes. The NJP will not only benefit tourists and locals but also support Fiji's Bus Operators Association by promoting bus usage. This innovative tool will integrate with the
0 views • 18 slides
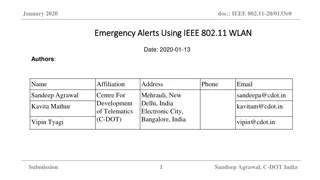
Emergency Alerts Using IEEE 802.11 WLAN in India
Proposal for utilizing public Wi-Fi infrastructure in India for emergency communication, focusing on early alerts for natural and man-made disasters. Discusses the limitations of cellular communication and suggests using IEEE 802.11 WLAN technology to enhance communication in critical situations.
0 views • 14 slides
ACAS Improvements for Enhanced Airborne Safety
Module N.B0-101 focuses on improving existing Airborne Collision Avoidance Systems (ACAS) to reduce nuisance alerts without compromising safety levels. It introduces several optional enhancements to minimize unnecessary alerts and improve overall safety during airborne operations. The module aims to
0 views • 12 slides
Simplifying IT Security with ADAudit Plus - Overview and Features
ADAudit Plus is an integrated auditing tool that offers real-time alerts and over 200 event-specific reports for Active Directory, Azure AD, Windows servers, file servers, and workstations. It helps in tracking changes made to configurations, monitoring access, and providing 24/7 surveillance. With
0 views • 14 slides
Event Vetting Process and Rapid Response Teams at LIGO-Virgo Collaboration
The LIGO-Virgo Collaboration utilizes a comprehensive event vetting process involving Rapid Response Teams to assess the quality of alerts and potential events. The teams, consisting of site advocates, experts, and operators, convene online to either retract or promote alerts based on their quality.
0 views • 8 slides
Student Success Management System at University of Louisiana at Lafayette
The Student Success Management System at the University of Louisiana at Lafayette includes features like Faculty Alerts, CRM Advising, and Academic Counseling to support student success. The system allows faculty to submit alerts for various categories like Excessive Absences and At Risk in Class to
0 views • 14 slides
Achievements and Challenges in Improving AKI Management at NHS Fife
The collaborative effort at NHS Fife has successfully implemented AKI alerts in hospitals and increased awareness in the community, leading to improved patient outcomes. Key success factors included enthusiastic engagement, hard work, and effective communication strategies. Overcoming challenges suc
0 views • 5 slides
Understanding Security in World Politics
Security studies delve into the intricate processes of defining and addressing security threats in global politics. It explores the contested nature of security definitions, emphasizes the political significance of security, and challenges the conventional boundaries of International Relations. The
0 views • 8 slides
Innovative August Doorbell Cam for Smart Home Security
August Doorbell Cam provides real-time alerts and video communication with visitors via a smartphone app, enhancing home security and convenience. It intelligently detects motion, records interactions, and works seamlessly with existing doorbells. The system is easy to install and compatible with st
0 views • 6 slides
Understanding Intrusion Detection Systems (IDS) and Snort in Network Security
Intrusion Detection Systems (IDS) play a crucial role in network security by analyzing traffic patterns and detecting anomalous behavior to send alerts. This summary covers the basics of IDS, differences between IDS and IPS, types of IDS (host-based and network-based), and the capabilities of Snort,
0 views • 34 slides
Comprehensive Course Review: Security Research Cornerstones at Carnegie Mellon University
Dive into the essential topics of software security, network security, OS security, and cryptography in the course offered by Vyas Sekar at Carnegie Mellon University. Explore control flow hijacks, cryptography terminology, and the importance of network security in protecting data transmissions. Lea
1 views • 41 slides
Innovative Application Integrating Current Weather & Events for Optimal Route Planning
Weatherways Mapping Application combines real-time weather and event data to predictively model optimal routes, accounting for anticipated weather, traffic, road conditions, events, and more. Integrating Google Maps API and Weather API, the application provides picture views for trouble areas, proje
0 views • 7 slides
UIC Security Division Overview and International Activities
The UIC Security Division plays a crucial role in supporting the security platform of the International Union of Railways (UIC). Headed by Jacques Colliard, the division is based in Paris and consists of key personnel like Marie-Hélène Bonneau, Jos Pires, and Laetitia Granger. The division's activ
0 views • 12 slides
Mass Notification Alerts and Emergency Preparedness Information
Stay informed and prepared with a range of alerts including emergency notifications, weather warnings, traffic alerts, and more in Troy, Goshen, and Pike County. Discover the limitations of sirens and the benefits of alternative notification methods like Smart911. Explore text and voice alert option
0 views • 4 slides
Wireless Public Alerting System in Canada: Update and Challenges
The National Public Alerting System in Canada, operating successfully since 2015, delivers emergency level alerts via various broadcasting methods. Despite its effectiveness, the system faces complaints and challenges, particularly regarding wireless alerts. Issues range from alert timing to the ann
0 views • 20 slides
Automating Security Operations Using Phantom
Isabella Minca, an intern for 4 months in the Security Team at Adobe, presents an overview of automating security operations using Phantom. The presentation covers goals, security alerts, Phantom playbooks, handling security data, and the capabilities of Phantom in orchestrating security responses.
0 views • 28 slides
Efficient Ways to Stay Updated: Alerts & Journal TOCs
Learn how to set up search alerts for evidence/literature searches, subscribe to journal table of contents alerts, and utilize internet alert feeds to receive new published material relevant to your research or expertise. Explore various resources such as Cochrane Library, NHS Evidence, Dynamed, Goo
0 views • 25 slides
Power Saver Rewards and Flex Alert Program Details
Power Saver Rewards is a program that offers bill credits to users who reduce energy consumption during Flex Alerts. Flex Alerts are issued to Californians to voluntarily decrease energy use during peak demand hours to prevent power outages. By following simple energy-saving actions, individuals can
0 views • 5 slides
Understanding HTTP Security Headers for Web Apps
Explore the importance of HTTP security headers on web applications through a detailed breakdown of headers like HSTS, XFO, XSS, CSP, CTO, RH, and FP. Learn how these headers enhance security by instructing browsers on handling website content, preventing various attacks. Gain insights on configurin
1 views • 68 slides
Understanding the Clery Act: Campus Security Authority Responsibilities at Texas A&M University - Kingsville
The Clery Act, named after Jeanne Clery, requires universities to disclose and report campus crime statistics, issue crime alerts, maintain fire safety information, and more. As a Campus Security Authority (CSA) at Texas A&M University - Kingsville, it is crucial to understand your responsibilities
0 views • 25 slides
Modular Security Analysis for Key Exchange and Authentication Protocols
Explore the modular security analysis approach used to examine the security of key exchange and authentication protocols, focusing on the universally composable authentication with a global Public Key Infrastructure. The analysis involves splitting the system into smaller components, separately anal
1 views • 15 slides
Revolutionizing Security Testing with BDD-Security
Explore the innovative approach of Continuous and Visible Security Testing with BDD-Security by Stephen de Vries. Gain insights into how security testing can be integrated seamlessly into modern development practices, shifting the focus from reactive to proactive measures. Learn about the importance
0 views • 33 slides
Comprehensive DevOps Security Training Overview
This Certified DevOps Security Practitioner course provides a deep dive into implementing DevSecOps, integrating security into the DevOps processes. Covering topics like security testing, Docker security, automation, and more, the training aims to equip participants with the necessary skills to embe
0 views • 5 slides
Secure Your Data with an Air Gapped Environment
Take use of SendQuick.com air gapped environment to safeguard your critical data. Ensure the security of your data and shield it from cybercriminals. Check it out right now!\n\n\/\/ \/navigating-it-and-security-alerts-in-an-air-gapped-environment\/
4 views • 1 slides
Understanding Security Testing and Architecture
Explore the fundamentals of security testing, computer security goals, software security approach, and security architecture. Learn about securing computer assets, verifying trustworthiness of security mechanisms, and validating security architecture through threat modeling. Enhance your knowledge o
0 views • 57 slides