Active Directory Delegation, cionsystems.com
The Active Directory Manager Pro features active directory delegation which can help organizations to reduce the number of high privilege accounts thereby reducing risk and enhancing security. https:\/\/shorturl.at\/uLNP7
2 views • 7 slides
Active Directory Auditing, cionsystems.com
A very simple and cost effective solution that makes active directory auditing easy proactively tracking and giving change alerts. https:\/\/rb.gy\/ttey9o
2 views • 7 slides
Active Directory Backup and Recovery, cionsystems
Sometimes human error, technology failures and malicious actions can easily corrupt the directory. \/\/rb.gy\/klwubf
1 views • 7 slides
Arkansas Community Mental Health Center Directory
The Arkansas Community Mental Health Center Directory provides contact information for various mental health providers in different areas of Arkansas, including services offered and emergency contact numbers. The directory includes details for Ouachita Behavioral Health and Wellness, Counseling Asso
0 views • 7 slides
Reflecting on Catholic School Prayer and Liturgy: A Journey of Faith and Education
Explore the intersection of faith and education in Catholic schools through the lens of prayer and liturgy, guided by the new Prayer and Liturgy Directory. Delve into the essence of worship, the importance of holding onto our beliefs, and the role of Jesus Christ in shaping the ethos of Catholic edu
2 views • 37 slides
Understanding Active Directory: Key Components and Security Considerations
Active Directory is a crucial component in Windows networks, providing centralized resource management, authentication, and authorization services. Key components include objects, domains, domain controllers, OUs, forests, and group policies. Understanding the data store, NTDS.dit file, partitions,
6 views • 68 slides
Active Directory Backup and Recovery, cionsystems
Sometimes human error, technology failures and malicious actions can easily corrupt the directory. \/\/tinyurl.com\/5xpuutyd
3 views • 7 slides
Understanding Secure Act 2.0 Key Provisions
In a detailed report by Dee Spivey and Angie Zouhar, key provisions of SECURE Act 2.0 are outlined, including changes in retirement plans like RMD age increase, employee certification of hardship withdrawals, and more. Secure 1.0 and Secure 2.0 differences, effective dates, and necessary actions for
5 views • 12 slides
School Staff Directory and Special Education Team at Terra Centre 2023-2024
Explore the comprehensive staff directory for Terra Centre 2023-2024, including teachers from Kindergarten to 6th grade, specialists, support staff, and the Special Education Team. Learn about key administrators, student monitors, and the PAC and ECCB teams. Dive into a dynamic educational environme
1 views • 123 slides
Understanding File and Directory Operations in Operating Systems
Explore the concepts of files and directories in operating systems, including persistent storage, file systems, directory structures, creating and accessing files, and reading/writing file data. Dive into the foundational elements essential for managing data effectively on computer systems.
0 views • 34 slides
Directory of Algerian Importers - Contact Information and Activities
Explore a comprehensive directory of Algerian importers showcasing a variety of products such as textiles, carpets, leather, rice, fruits, sports wear, spices, pharmaceuticals, and surgical equipment. Contact details and activities of various importers in Algeria provided.
1 views • 29 slides
Introduction to SFTP & PGP Encryption for Secure Data Transfer
Discover how to ensure reliable data transfer, make informed decisions, and gain a strategic advantage through the use of Secure File Transfer Protocol (SFTP) and Pretty Good Privacy (PGP) encryption. The session includes demonstrations on PGP encryption and SFTP access, along with insights on setti
1 views • 22 slides
Understanding Mandatory and Directory Statutes: A Legal Overview
Mandatory statutes compel specific actions with no discretion allowed, making non-compliance potentially void. Directory statutes outline procedures without affecting substantial rights, with compliance regarded as a matter of convenience. The interpretation of these statutes rests on legislative in
1 views • 18 slides
Ensuring Secure Testing Environments in Oregon Education System
Oregon's Statewide Assessment System (OSAS) emphasizes the critical need for secure testing environments to maintain the validity and accuracy of assessment data. This includes handling secure printed test materials, identifying and preventing improprieties, and reporting any irregularities. From ma
2 views • 20 slides
Oregon Teacher Loan Forgiveness Program Overview
The Oregon Teacher Loan Forgiveness Program is designed to incentivize individuals to pursue and remain in the teaching profession, particularly in high-poverty schools. The Oregon Department of Education plays a crucial role in determining school eligibility for the Teacher Cancellation Low Income
0 views • 19 slides
Approved Food Sources for Armed Forces Procurement
The Worldwide Directory of Sanitarily Approved Food Establishments provides a comprehensive list of approved food sources for Armed Forces procurement, audited for sanitation and quality. Suppliers seeking approval must follow specific requirements outlined in the directory to become eligible for bi
0 views • 14 slides
Secure Computation Techniques in RAM Models with Efficient Automation
Explore the automation of efficient RAM-model secure computation techniques, including examples such as secure binary search. Discover how traditional solutions using circuit abstractions can be improved for sub-linear time computation through methods like Oblivious RAM. Learn about techniques such
0 views • 37 slides
Understanding Directory Structures in Operating Systems
Directory structures play a crucial role in operating systems, organizing files, and supporting essential operations like file search, creation, deletion, listing, and traversal. This content explores single-level and two-level directory structures, addressing their benefits and limitations in manag
2 views • 23 slides
Tamper-Evident Pairing (TEP) Protocol for Secure Wireless Pairing Without Passwords
This article discusses the challenges of traditional secure wireless pairing methods that rely on password validation and proposes the Tamper-Evident Pairing (TEP) protocol as a secure in-band solution to protect against Man-in-the-Middle (MITM) attacks. TEP eliminates the need for out-of-band chann
1 views • 40 slides
Telisca Suite: Enhancing MS Teams Integration with Advanced Tools
Explore the Telisca suite of applications and tools designed to enhance MS Teams functionality. From call recording to global directory management, Azure authentication, and gateway configurations, Telisca offers a comprehensive solution for optimizing communication and collaboration within the Team
0 views • 92 slides
Actively Secure Arithmetic Computation and VOLE Study
Exploring actively secure arithmetic computation and VOLE with constant computational overhead at Tel Aviv University. Understanding how functions are represented in secure computation using arithmetic circuits over boolean circuits. Efficiently evaluating arithmetic circuits over large finite field
0 views • 36 slides
Accessing and Utilizing CPCSSN Secure Research Environment (SRE)
Learn how to access the CPCSSN Secure Research Environment (SRE) for secure data analysis. Follow steps such as setting up VPN, accessing SQL databases, and establishing ODBC connections for statistical analysis using tools like SAS, R, SPSS, or Stata. Enhance your research capabilities within a sec
0 views • 12 slides
Enhancing Animal Telemetry Data Systems for Secure Collaboration
Wide spectrum of animal telemetry data collection protocols and platforms require enhanced data stewardship options for secure sharing before public release. The need for a more granular understanding of available data and structured systems integration is crucial. Initial workflow involves providin
0 views • 4 slides
Mastering Active Directory Management with PowerShell
Learn essential tips and techniques for managing Active Directory using PowerShell, including starting tips, staying up-to-date with PowerShell versions, methods of management, exploring Active Directory commands, getting information from AD, and selecting, sorting, and exporting data efficiently.
0 views • 15 slides
STM32WB BLE Secure Connections Overview
This detailed content provides insights into the secure connections in STM32WB BLE devices, covering aspects such as BLE security methods, encryption techniques, pairing processes, key distribution, and security modes and levels. It emphasizes the use of Long Term Keys (LTK), Diffie-Hellman key exch
0 views • 12 slides
Understanding Secure Electronic Transactions (SET)
Secure Electronic Transactions (SET) is an encryption and security specification designed to protect credit card transactions on the Internet. SET provides a secure way to utilize existing credit card payment infrastructure on open networks, such as the Internet, involving participants like clients,
1 views • 6 slides
An Open-Source SPDM Implementation for Secure Device Communication
This article introduces an open-source SPDM (Secure Protocol and Data Model) implementation for secure device communication, developed by Jiewen Yao and Xiaoyu Ruan, Principal Engineers at Intel. SPDM aims to enhance device security through protocols for device authentication, session key establishm
0 views • 29 slides
Exploring Secure Care Services in Scotland
Delve into the world of secure care services in Scotland, focusing on achievements, challenges, and opportunities in providing youth justice. Learn about trends in secure care, reduction in costs, reasons for referrals, and evidence-based programs like DBT in Glasgow. Gain insights from industry lea
0 views • 77 slides
Understanding Secure PRFs and PRPs in Cryptography
Dive into the world of secure Pseudo-Random Functions (PRFs) and Pseudo-Random Permutations (PRPs) in cryptography. Learn about the definitions, security criteria, and examples of secure PRFs and PRPs such as 3DES and AES. Explore the concepts of secure block ciphers and key principles behind these
0 views • 54 slides
Understanding User Accounts and Directory Services in Network Computing
Explore the role of user accounts and directory services in network-centric computing infrastructure. Learn about Directory Servers, User Administration in Unix, and the concept of Group Accounts in Unix. Discover how Directory Services provide centralized repositories for managing information, enab
0 views • 9 slides
NAU WordPress Unit Updates and Training Highlights - July 2019
NAU's WordPress Unit web coordinators conducted their monthly summit in July 2019, covering status updates, site level moves, directory updates, training, enterprise workshops, accessibility improvements, and more. Key highlights include the transfer of sites between platforms, launch of new sites,
0 views • 16 slides
Provider Directory Advisory Group Meeting Summary
The Provider Directory Advisory Group Meeting held on November 18, 2015, covered various topics including Clinical Quality Metrics, Registry Presentation, Procurement updates, and Common Credentialing. The meeting involved breakout sessions, group discussions, and group presentations focusing on ref
0 views • 48 slides
Understanding Fine-Grained Password Policies in Active Directory
Explore the intricacies of Fine-Grained Password Policies (FGPP) in Active Directory, covering topics such as domain account policies, policy recovery methods, interpreting pwdProperties attribute, and implementing PSOs for granular password settings. Delve into the nuances of password complexity, h
0 views • 11 slides
SecDir: A Secure Directory to Defeat Directory Side-Channel Attacks
SecDir introduces a secure directory design to mitigate directory side-channel attacks, a critical security threat. By reassigning part of the conventional directory storage to per-core private directories, SecDir aims to block directory interference between processes and enhance security in cache h
0 views • 49 slides
Essential Windows Enterprise Services Overview
Exploring Windows Enterprise Services, the Introductions to UNM Directory Services, the LAMB Authoritative Source of Information for AD processes, and the benefits of RSAT (Remote Server Administration Tools). Discover the delegation of responsibilities in OU structures and the nuances of Group Type
0 views • 16 slides
Civic Directory and Citizen Inputs from Ward Sabha Meeting
The content provides information about the Ward Sabha meeting held in Madiwala Ward #172 on September 23, 2017. It includes details about Covered RWAs, Civic Directory listing agency contacts, and guidelines for referring to the minutes of the meeting. The slides showcase citizen inputs and agency r
0 views • 23 slides
Managing and Updating R2 Source Codes and Data Documentation
Set the home directory to prevent future directory changes before running real-time processes. Two versions of run_gdas scripts are provided along with instructions for setting up directories, updating scripts, and accessing necessary data files. Various resources and tools are mentioned, including
0 views • 62 slides
Envirolink Tools Project - Decision Support Systems Directory
Envirolink Tools Project offers a web-based searchable directory of Decision Support Systems (DSS) with key metadata and case studies, aiding Councils in evaluating DSS opportunities. Created due to demand identified in workshops, the project aims to assist in meeting management needs effectively. V
0 views • 8 slides
Guide for Adding an EAST Entry in OCLC Policies Directory
Learn how to add a new policy entry in the OCLC Policies Directory specifically for EAST (Eastern Academic Scholars Trust) including selecting policies for copies and loans, setting copy fees, choosing borrower groups like EAST and library categories, indicating collections and formats, and more.
0 views • 30 slides
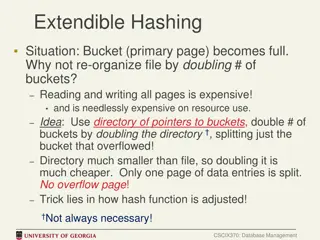
Efficient Bucket Management in Extendible Hashing
In cases where a bucket (primary page) becomes full in extendible hashing, re-organizing the file by doubling the number of buckets can be costly in terms of resource utilization. An alternative approach involves using a directory of pointers to buckets and doubling the directory instead of all buck
0 views • 9 slides