Understanding Cybersecurity Threats and Facebook Security
In today's digital landscape, cybersecurity threats are ever-present, ranging from phishing to ransomware. This presentation by Paul Haithcock sheds light on protecting networks and data. It also emphasizes the importance of securing Facebook accounts amidst the prevalence of cybercriminal activitie
1 views • 15 slides
Phriendly Phishing Training Solutions Overview
Phriendly Phishing offers security awareness and phishing simulation training solutions to organizations in Australia and New Zealand. Their training covers topics like phishing, spear-phishing, ransomware, malware, and scams, focusing on empowering employees to detect and prevent cyber threats effe
5 views • 42 slides
Healthcare Executive's Guide to Ransomware Threats
This comprehensive guide covers essential information on ransomware threats in healthcare, including the definition of ransomware, how it works, email and network threats, and statistics. Gain insights from Troy Ament, a seasoned CISO in the healthcare sector, to safeguard your organization against
0 views • 17 slides
Understanding Microsoft Sentinel Fusion for Advanced Threat Detection
Threat intelligence plays a crucial role in Microsoft Sentinel solutions, enabling the detection of multi-stage attacks, ransomware activities, and emerging threats. Fusion technology combines Graph-powered Machine Learning and probabilistic kill chain analysis to detect anomalies and high-fidelity
2 views • 5 slides
Healthcare Under Attack
\nFind out why ransomware attacks are targeting healthcare organizations and the alarming statistics behind this growing threat.\n
1 views • 7 slides
DataSecurity Plus - Unified Data Visibility and Security Platform
DataSecurity Plus by ManageEngine offers a unified data visibility and security platform with capabilities such as file server auditing, ransomware detection, data leak prevention, cloud protection, and more. It provides solutions for file audit, file analysis, data risk assessment, data leak preven
0 views • 24 slides
AEP Enterprise Security Program Overview - June 2021 Update
In the June 2021 update for the Kentucky Interim Committee on Natural Resources and Energy, American Electric Power (AEP) addresses recent ransomware events, their security program updates, and details about their enterprise security measures. AEP, one of the largest electric utilities in the U.S.,
0 views • 12 slides
Understanding Malware: Types, Risks, and Prevention
Dive into the world of malware to explore major types such as viruses, worms, ransomware, and more. Learn about social engineering tactics, insider threats, and best practices to safeguard against malware attacks. Discover the malicious intent behind grayware and how to prevent malware infections ef
0 views • 23 slides
Ransomware and Data Breaches in Public Libraries Analysis
Delve into the world of ransomware and data breaches in public libraries, exploring the definitions of ransomware and data breaches, the potential impacts on libraries, the financial losses incurred, and the value of library records. Understand the risks, implications, and consequences associated wi
0 views • 21 slides
Cybersecurity Challenges: Attacks on Web Applications and Cost of Security Breaches
In the realm of cybersecurity, attacks on web applications pose a significant threat with 78% of attacks targeting applications. The consequences of these attacks are immense, with projected costs reaching $6 trillion annually by 2021. Notable breaches in recent years highlight the urgency for robus
8 views • 23 slides
State Cyber Incident IT Q&A Call - July 30, 2019
A State Cyber Incident IT Q&A Call was held on July 30, 2019, to address cyber incidents affecting school systems in Louisiana. The call covered reporting procedures, current cyber threat status, actions steps, and a Q&A session. Several school systems were impacted by the RYUK ransomware strain, em
0 views • 18 slides
Cybersecurity Solutions to Protect Against Ransomware Attacks
Discover effective strategies and tools to protect your business from ransomware attacks. Stay secure and informed.\n
3 views • 6 slides
Understanding Malware: Types, Usage, and Protection
Malware, short for malicious software, encompasses various forms of hostile software designed to disrupt computer operation, steal sensitive information, or gain unauthorized access. It includes viruses, trojan horses, worms, spyware, phishing, ransomware, and more. Malware is often used to steal pe
1 views • 49 slides
Understanding DNS Firewall Architecture at Virginia Tech
Virginia Tech implements Response Policy Zone (RPZ) as a mechanism in the DNS system to protect clients from malicious domains. The RPZ allows recursive resolvers to customize responses for specific zones, enhancing security against malware callbacks. Working with campus partners, the RPZ database a
0 views • 11 slides
Understanding Malware: Types, Impact, and Response Strategies
Malware, a term encompassing various malicious software types like viruses, worms, and ransomware, poses significant threats to cybersecurity. This content delves into the definition, types, kill chain analysis, incident response, and the MITRE ATT&CK framework in mitigating cyber threats.
0 views • 49 slides
Cyber Security Awareness and Best Practices
Enhance your cyber security knowledge with terminology like Social Engineering and Spear Phishing, and learn about common cybercrime activities such as phishing and ransomware attacks. Stay informed to protect yourself and your organization from malicious threats.
0 views • 26 slides
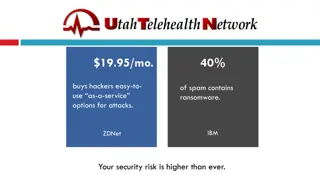
Protecting Your Business from Cybersecurity Threats
In today's digital landscape, the risk of cyber attacks is higher than ever. Hackers offer malicious services for a low cost, increasing the threat of ransomware, phishing, and spam attacks. With statistics showing the rise in ransomware incidents, it's crucial for organizations to prioritize securi
0 views • 24 slides
Financial Management and Cybersecurity: Essential Tips for Treasurers
A comprehensive guide covering topics such as budget development, treasurer's role responsibilities, and cybersecurity basics for treasurers. Learn about financial sustainability, board commitments, and protecting against cybersecurity threats like ransomware and spoofing scams. These insights aim t
0 views • 13 slides
Ensuring Trust and Security in Internet Services: Challenges and Solutions
Measures to enhance trust and security in internet services were discussed by Group 3 in Dhulikhel, Kabhre. Identified problems include hacking, website blocks, ransomware attacks, and more. Lack of trust in ISPs and regulatory bodies due to issues like service quality and consumer rights. Recommend
0 views • 10 slides
Cyber Insurance - Emerging Risks and Threats in Today's Digital Landscape
Explore the evolving landscape of cyber risks and threats, including recent major attacks like the SolarWinds breach and the Colonial Pipeline ransomware incident. Learn about the scope of cyber insurance in mitigating losses from data breaches and cyberattacks for businesses and individuals in the
0 views • 36 slides
Understanding Cybercrime: Types, Signs, and Prevention
Cybercrime involves various criminal activities targeting computers and networks, aiming to generate profit or cause harm. Types include website spoofing, ransomware, malware, IoT hacking, identity theft, and online scams. Signs of identity theft can manifest in credit, tax, child, medical, and crim
0 views • 6 slides
Understanding Malware: Types, Risks, and Prevention
Malware, short for malicious software, is designed to disrupt, damage, or gain unauthorized access to computer systems. Malware includes viruses, worms, trojans, ransomware, adware, spyware, rootkits, keyloggers, and more. They can be spread through various means like malicious links, untrusted down
0 views • 15 slides
Effective DGA Family Classification using Hybrid Inspection Technique on P4 Switches
Attackers utilize Domain Generation Algorithms (DGAs) as dynamic communication methods in malware like botnets and ransomware to evade firewall controls. This study presents a novel approach that combines shallow and deep packet inspection on P4 Programmable Switches for efficient classification of
0 views • 19 slides
Ethics in Cybersecurity: Evolution, Challenges, and Solutions
Explore the evolution of cybersecurity, from the days of firewalls to modern cybersecurity threats like viruses and ransomware. Understand the importance of ethics in cybersecurity, as it plays a vital role in building strong defense mechanisms to secure personal and enterprise data effectively.
0 views • 18 slides