County Election Board 101
Basic duties and responsibilities of the County Election Board, including voter registration and administration of public elections. It covers the composition of the board, qualifications of its members, officer roles, board minutes, budget estimates, and proxy usage.
142 views • 26 slides
Dell Financial Services
Dell Financial Services offers flexible consumption payment solutions that enable customers to align technology expenses with actual usage. The portfolio includes growth solutions, variable usage options, software financing, and transformational license agreements. Customers can adopt better solutio
3 views • 30 slides
HTPB Usage in NASA and Space Force Flights: Trends and Impacts
Analysis of NASA's projected HTPB usage from 2023 to 2029, focusing on the transition to HTPB boosters, impact on the polymer market, comparison of SLS and BOLE boosters, propellant development details, and HTPB polymer usage in NASA and Space Force flights.
4 views • 6 slides
What Is Proxy Card Access?
Explore the world of contactless access control. Learn how proxy cards work, their benefits, and common uses. Upgrade your security today!
1 views • 4 slides
Gwendolyn Brooks Library Usage Statistics with Springshares LibInsight
Gwendolyn Brooks Library utilizes LibInsight's E-Journals/Databases Dataset to streamline the collection and analysis of usage statistics for reporting to ACRL, IPEDs, and university administration. The tool offers various features such as storing login information, different levels of permissions,
0 views • 7 slides
Understanding Parking Surveys for Urban Planning
Parking surveys play a crucial role in urban planning and traffic management by providing data on parking space availability, usage, and demand. These surveys help in determining effective parking policies, such as pricing strategies and duration limits. Different types of surveys, including parking
0 views • 15 slides
Understanding Energy Usage in the Home
This unit explores energy usage in homes, covering the need for energy in heating, lighting, and appliance operation. It delves into different energy sources such as electricity, gas, and solid fuels, explaining how costs vary based on fuel types and installations. Additionally, it discusses ways to
1 views • 80 slides
Fresh Fruit and Vegetable Program Update Training Session
Fresh Fruit and Vegetable Program Update Training Session took place on November 16, 2018, focusing on program goals, objectives, school eligibility, funding allocation, and usage in Hawaii. The program aims to create a healthier school environment, increase students' produce consumption, and integr
1 views • 24 slides
Understanding Pronouns: Cases, Perspectives, and Usage
Explore the nuances of pronouns including cases, perspectives, and correct usage to enhance your language skills. Learn about subjective, objective, and reflexive pronouns, as well as how to choose the right pronoun based on the context. Enhance your command of standard English grammar and usage wit
0 views • 15 slides
Optimum Solar Proxy for Long-Term Ionospheric Studies
The search for the best solar proxy for long-term ionospheric studies is ongoing due to the lack of consistent solar radiation data. Various solar proxies have been analyzed, and the use of Mg II for foF2 and F10.7 for foE has shown promising results, describing a high percentage of variance in the
1 views • 10 slides
Decoy Routing: A Tool Against Internet Censorship
Modern censorship resistance tools like decoy routing provide a new approach against web censorship at a nation-state level. Decoy routing involves placing a proxy in the middle of paths to hide user packets from detection by adversaries. The use of decoys helps in avoiding the enumeration of censor
0 views • 20 slides
Developing Proxy Indicators for Farm Profitability in Irish Agriculture
This study by Ciara O'Donovan focuses on developing and testing proxy indicators of farm profitability and efficiency measurements for knowledge transfer use on Irish farms. The research aims to identify indicators of farm performance, tailor them based on enterprise, scale, and seasonality, and tes
0 views • 20 slides
Methyl Bromide Usage Recommendations and Reporting Summary
The Methyl Bromide Technical Options Committee (MBTOC) provides final recommendations on the usage of methyl bromide for different sectors and countries based on reported stocks and proposed quantities for various commodities. The recommendations emphasize the importance of justifying the critical n
0 views • 12 slides
GOES-R ABI Aerosol Detection Product Validation Summary
The GOES-R ABI Aerosol Detection Product (ADP) Validation was conducted by Shobha Kondragunta and Pubu Ciren at the NOAA/NESDIS/STAR workshop in January 2014. The validation process involved testing and validating the ADP product using proxy data at various resolutions for detecting smoke, dust, and
1 views • 21 slides
E-book Expenditures and Usage Analysis FY2009-FY2012 at Kean University Library
Analyzing the expenditure and usage trends of e-books from FY2009 to FY2012 at Kean University Library, focusing on purchases, short term loans, and circulation data. The study evaluates the shift towards e-books, comparing costs and usage with print books, presenting findings through graphs and cha
0 views • 18 slides
Proposal for AS Proxy Offer Optimization
This proposal aims to optimize AS proxy offers for TCPA and LCRA to ensure fair market prices without distorting market competition. It includes strategies like Proxy AS Price Floor Proposals and the use of L Factor to determine proxy AS offer prices. The goal is to make AS capacity available to ERC
0 views • 10 slides
Understanding COUNTER Reports for Online Resource Usage
Explore the world of COUNTER reports, a standard for counting online usage of electronic resources. Learn about different types of reports, benefits of using COUNTER data, and key terms like investigations and requests. Discover how COUNTER reports can help make informed decisions, support library s
0 views • 33 slides
Understanding Pesticide Data Collection and Analysis
Pesticide data usage is crucial for accurate assessments and prioritization of areas with high likelihood of usage. Various sources, quality requirements, and data considerations are highlighted, emphasizing the importance of incorporating usage data for informed decision-making.
0 views • 12 slides
Understanding Unidirectional Updatable Encryption and Proxy Re-Encryption
Unidirectional updatable encryption and proxy re-encryption are key concepts in secure cryptography deployments. Key management and rotation are essential for secure encryption schemes such as Proxy Re-Encryption (PRE) and Updatable Encryption (UE). PRE allows delegation of decryption abilities, whi
0 views • 16 slides
Importance of Internet Security and Setting Up an Office Proxy Server
Learn how to enhance internet security by setting up an office proxy server to limit staff web surfing. Understand the risks associated with system flaws in Windows, Mac, browsers like Internet Explorer, Firefox, Chrome, and the immediate threat of Zero-Hour Attacks by hackers.
0 views • 28 slides
Stepping Stone Detection at the Server Side: Real-Time Algorithm
An innovative real-time algorithm is introduced to detect the use of a proxy as a stepping stone from the server's perspective. The solution addresses the limitations of existing methods by focusing on TCP connection initiation. Previous research and vulnerabilities related to proxy servers and step
0 views • 37 slides
German eID and eIDAS: Secure Digital Identification Overview
The German eID system, including eIDAS integration, offers secure digital identification services through government-issued ID cards with embedded chips. It allows citizens and service providers to authenticate each other securely online. The system emphasizes interoperability and privacy protection
0 views • 16 slides
Proxy Access to Medications Implementation Stages
This document outlines the implementation stages for proxy access to medications. It covers agreements with healthcare providers, prerequisites including compliance and data sharing agreements, and systems configuration for access to medical records. The stages include setting up access for care pro
0 views • 7 slides
Analysis of Unique URLs Retrieval Patterns in Web Logs
This analysis delves into the retrieval patterns of unique URLs from web logs, revealing that a significant percentage of URLs are re-presented from different client IP addresses. The study identifies top repeaters and examines instances of potential proxy device usage based on AS locations.
0 views • 15 slides
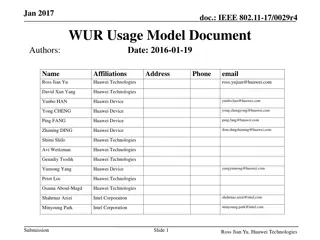
IEEE 802.11-17/0029r4 WUR Usage Model Document
This document, dated January 2017, outlines usage models for wake-up radio WLAN standard. It includes details on various usage models like Smart Home, Warehouse, Outdoor Cattle Farms, Sensor Network Synchronized Wake Up, Wearable Devices, Moving Goods Tracking, and more. The document also explains t
0 views • 20 slides
Proxy Voting in Indian Elections: Developments and Perspectives
India has seen progress in allowing proxy voting for Non-Resident Indians, with recent proposals to extend this privilege to overseas Indians. The initiative aims to enhance voter participation, especially for those residing abroad. While some political parties support proxy voting, concerns exist r
0 views • 35 slides
Enhancing Air Quality Forecasting with TEMPO Retrievals in Proxy Observing System
Improvements in Air Quality Forecast Skill (AQFS) are explored by assimilating TEMPO retrievals in a Proxy Air Quality Observing System (AQOS) using WRF-Chem/DART. The study focuses on benefits identified through a designed OSSE scenario, including application to the Front Range Air Pollution and Ph
0 views • 8 slides
Trust as a Proxy for Certainty in Social Cohesion
Exploring the intricate relationship between trust, security, and social cohesion, this study delves into how trust serves as a proxy for certainty in uncertain environments. By analyzing societal properties and the role of trust in managing risks and insecurities, the Peace Research Institute Oslo
0 views • 16 slides
Updates on GOES-R Aerosol Optical Depth Validation Activities
Generated proxy data algorithm enhancements for post-launch validation activities were discussed at the GOES-R AWG 2nd Validation Workshop in January 2014. The use of MODIS reflectances as a proxy for ABI to retrieve Aerosol Optical Depth (AOD) was emphasized, along with the importance of AERONET gr
0 views • 25 slides
Insights from City of Olathe's Neighborhood Park Usage Study
Explore the comprehensive Neighborhood Park Usage Study conducted by Ed Foley & Paul Krueger in City of Olathe. The study delves into how park resources are managed, the challenges faced in tracking neighborhood park usage, the methodology used for data collection, key findings on growing pains and
0 views • 15 slides
Proxy QoS Management for XR Devices in IEEE 802.11-23/1958r0 - November 2023
This document discusses the challenges faced by XR devices in terms of size, thermal constraints, cost, and power limitations leading to the proposal of Proxy QoS Management to enhance Wi-Fi performance. The aim is to leverage TGbn devices for improving legacy devices' connectivity within a Wi-Fi ne
0 views • 6 slides
Privacy Preservation in Machine Learning Systems via Proxy Use
Proxy use in machine learning systems is crucial for preserving privacy, especially in scenarios where fairness and privacy are at risk. This involves defining influential sub-programs, both qualitatively and quantitatively, to protect sensitive attributes. By utilizing proxies effectively, it enabl
0 views • 15 slides
Achieving Pay Equity Using Proxy Comparison Method in Ontario
Presentation by Doreen Lurie on achieving and maintaining pay equity in Ontario through the proxy method of comparison. Covers an overview of the Pay Equity Act, differences from Employment Standards, purpose of the act, and basic pay equity terms.
0 views • 5 slides
Setting Up a Proxy for Web Time Entry Approvers
Setting up a proxy is essential for Web Time Entry Approvers to ensure seamless approval processes when out of the office. Follow the outlined steps to grant proxy access and maintain security protocols. Remember to remove proxies when necessary and contact Payroll for any assistance.
0 views • 5 slides
Understanding Dynamic Proxy in Java for Type-Safe Proxy Objects
Learn about creating dynamic proxy classes in Java to implement interfaces at runtime without pre-compilation, enabling type-safe proxy object creation for method invocations. This allows for flexible and efficient handling of method calls through uniform interfaces.
0 views • 16 slides
Understanding Web Proxies and Proxy Architectures
Web proxies play a crucial role in networking by facilitating web requests between clients and servers. They come in various types such as forward proxies, reverse proxies, and open forward proxies, each with unique functionalities like content filtering, translation, and load balancing. This articl
0 views • 15 slides
Understanding the Impact of Proxy on Disability and Health Determinants Association
National surveys are evaluating standardized disability identifiers. The Washington Group Short Set and American Community Survey are being compared in the National Health Interview Survey. Limited research exists on these questions in disability research, providing an opportunity for analysis. The
0 views • 15 slides
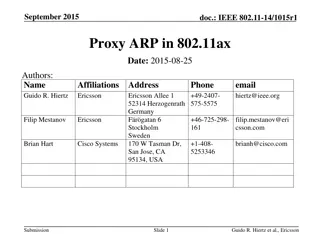
Understanding Proxy ARP Implementation in IEEE 802.11ax
Proposed in September 2015, the document discusses the implementation of Proxy ARP with 802.11ax Access Points. It explains the Address Resolution Protocol (ARP), detailing how devices in a LAN communicate using MAC and IP addresses. The submission aims to provide comprehensive explanations on Proxy
0 views • 18 slides
Understanding Mobile Proxy Ecosystem: Privacy and Security Implications
The paper delves into the emerging trend of mobile proxy services, specifically focusing on the use of mobile devices as proxy peers. It addresses the security and privacy concerns associated with this practice, highlighting the potential risks posed to end-users. The study offers novel insights int
0 views • 21 slides
Proxy Effects and Fair Adaptation for Dynamic Adaptive Streaming
This study focuses on the implementation of a proxy effect analysis and fair adaptation algorithm for managing multiple competing dynamic adaptive streaming over HTTP clients. By considering factors like client awareness, network structure, and adaptation decisions, the algorithm aims to mitigate ne
0 views • 16 slides