Exploring the Benefits of 192.168.188.1 Admin Setup
Embrace the Benefits of 192.168.188.1 Admin Setup! Seamlessly manage your network settings, enhance connectivity, and elevate user experiences effortlessly.\n\nTo Know more: https:\/\/1921681881.com\/192-168-188-1-admin-setup-how-to-reset-netgear-wifi-range-extender\/
2 views • 2 slides
Enhance Your Wireless Range: 192.168.188.1 Wireless Extender Setup with Top Apps
Are you tired of weak Wi-Fi signals limiting your internet access? Fear not! With the 192.168.188.1 Wireless Extender Setup and some top-notch apps, you can extend your wireless range and enjoy seamless connectivity throughout your home or office.\n\nfor more info: https:\/\/1921681881.com\/192-168-
6 views • 2 slides
What Is Proxy Card Access?
Explore the world of contactless access control. Learn how proxy cards work, their benefits, and common uses. Upgrade your security today!
1 views • 4 slides
NH Management: Your Partner in Successful Business Setup in Dubai
Explore NH Management's comprehensive services for business setup in Dubai. This presentation covers our expertise in company formation, including offshore company formation in Dubai, free zone establishments, and mainland incorporations. Learn how NH Management can streamline your business setup pr
0 views • 8 slides
NH Management: Your Partner in Successful Business Setup in Dubai
Explore NH Management's comprehensive services for business setup in Dubai. This presentation covers our expertise in company formation, including offshore company formation in Dubai, free zone establishments, and mainland incorporations. Learn how NH Management can streamline your business setup pr
4 views • 8 slides
Progress on IEEE 802.11 Multi-link Setup
Significant developments have been made in the multi-link setup within the IEEE 802.11 framework. The focus is on allowing only one STA in the MLD framework, differentiation with STA-level associations, and the rationale behind restricting to one STA. Proposals for defining multi-link devices and re
0 views • 12 slides
Enhanced Type II Testing Setup for NR eMIMO Performance Evaluation
This document outlines the test setup and parameters for conducting enhanced Type II testing to evaluate the performance of NR eMIMO systems. It includes details on the test metrics, test procedures, and performance requirements for different codebooks and scenarios. The testing setup covers aspects
2 views • 14 slides
Comprehensive SEO Workflow Process for Effective Website Optimization
Explore a detailed SEO workflow process comprising off-site setup, initial audits, technical analysis, administrative setup, on-page SEO analysis, ongoing tasks, and more. The journey begins with client goal identification, competitor analysis, keyword research, and website audits in the first month
0 views • 15 slides
Financial Setup and Maintenance Overview
Explore the detailed components of financial setup, including maintenance work codes, price list setup, charging types, currency configuration, VAT/tax setup, and more. Gain insights into the intricate processes involved in managing financial aspects efficiently within the system.
0 views • 18 slides
Business setup in Dubai (5)
The Gateway to Business Setup in Dubai Are you eager to explore the vibrant business landscape of Dubai? Look no further than Dubai Airport Freezone (DAFZ) - your ultimate partner for hassle-free business setup in Dubai. \\u200b
1 views • 7 slides
Optimum Solar Proxy for Long-Term Ionospheric Studies
The search for the best solar proxy for long-term ionospheric studies is ongoing due to the lack of consistent solar radiation data. Various solar proxies have been analyzed, and the use of Mg II for foF2 and F10.7 for foE has shown promising results, describing a high percentage of variance in the
1 views • 10 slides
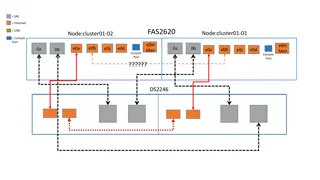
Networking Setup Overview for FAS2620 and FAS2240 Systems
This content provides detailed information about the networking setup for FAS2620 and FAS2240 systems, including connections, ports, and cabling configurations. It includes images and descriptions of the setup for cluster configurations, disk shelves, and switch connections.
0 views • 5 slides
Developing Proxy Indicators for Farm Profitability in Irish Agriculture
This study by Ciara O'Donovan focuses on developing and testing proxy indicators of farm profitability and efficiency measurements for knowledge transfer use on Irish farms. The research aims to identify indicators of farm performance, tailor them based on enterprise, scale, and seasonality, and tes
0 views • 20 slides
Comprehensive Setup and Configuration Guide for Office Management Software
Detailed setup and configuration instructions for your office management software, including customizing company information, tax rates, localization settings, barcode types, stock management, receipts, and invoices. Ensure a seamless setup process by following the step-by-step guidance provided in
0 views • 31 slides
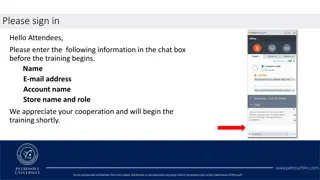
Price Book Setup Refresher Training Agenda
The Price Book Setup Refresher Training Agenda covers essential topics such as correct item setup, parent-child relationships, VAP promotions, and third-party loyalty programs. It also details the necessary units of measure for different tobacco categories and products. This training will help atten
0 views • 44 slides
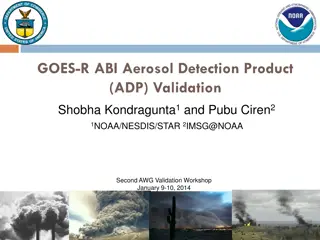
GOES-R ABI Aerosol Detection Product Validation Summary
The GOES-R ABI Aerosol Detection Product (ADP) Validation was conducted by Shobha Kondragunta and Pubu Ciren at the NOAA/NESDIS/STAR workshop in January 2014. The validation process involved testing and validating the ADP product using proxy data at various resolutions for detecting smoke, dust, and
1 views • 21 slides
Proposal for AS Proxy Offer Optimization
This proposal aims to optimize AS proxy offers for TCPA and LCRA to ensure fair market prices without distorting market competition. It includes strategies like Proxy AS Price Floor Proposals and the use of L Factor to determine proxy AS offer prices. The goal is to make AS capacity available to ERC
0 views • 10 slides
Comprehensive Guide for Setting Up WireGuard Securely
This guide covers the setup process of WireGuard with Mamori, a digital identity authentication platform, including pre-requisites, client setup, and portal login steps with multi-factor authentication. Follow step-by-step instructions along with visuals for a seamless setup experience.
1 views • 10 slides
Panasonic KX-NS Step-by-Step Guide: Initial Setup
This step-by-step guide provides detailed instructions for the initial setup of the Panasonic KX-NS PBX system. Covering topics such as installation, default clearing, web maintenance console setup, PT programming, and more, this guide is a valuable resource for users setting up the Panasonic KX-NS
0 views • 30 slides
Understanding Unidirectional Updatable Encryption and Proxy Re-Encryption
Unidirectional updatable encryption and proxy re-encryption are key concepts in secure cryptography deployments. Key management and rotation are essential for secure encryption schemes such as Proxy Re-Encryption (PRE) and Updatable Encryption (UE). PRE allows delegation of decryption abilities, whi
0 views • 16 slides
Experimental Setup at IP5 for Inelastic Events and Particle Detection
Experimental setup at IP5 involves inelastic telescopes for charged particle detection and vertex reconstruction. The setup includes T1 and T2 telescopes, HF and CASTOR detectors, as well as Roman Pots for measuring elastic and diffractive protons. The TOTEM experiment focuses on proton-proton inter
0 views • 27 slides
Importance of Internet Security and Setting Up an Office Proxy Server
Learn how to enhance internet security by setting up an office proxy server to limit staff web surfing. Understand the risks associated with system flaws in Windows, Mac, browsers like Internet Explorer, Firefox, Chrome, and the immediate threat of Zero-Hour Attacks by hackers.
0 views • 28 slides
DarkBox Setup and Testing Overview
This content provides an in-depth overview of the DarkBox setup and testing process conducted by V. Kulikovskiy and others in Napoli. It covers the setup finalization, software installation, extensive data acquisitions, challenges faced, and collaboration with external experts. The content showcases
0 views • 17 slides
Stepping Stone Detection at the Server Side: Real-Time Algorithm
An innovative real-time algorithm is introduced to detect the use of a proxy as a stepping stone from the server's perspective. The solution addresses the limitations of existing methods by focusing on TCP connection initiation. Previous research and vulnerabilities related to proxy servers and step
0 views • 37 slides
German eID and eIDAS: Secure Digital Identification Overview
The German eID system, including eIDAS integration, offers secure digital identification services through government-issued ID cards with embedded chips. It allows citizens and service providers to authenticate each other securely online. The system emphasizes interoperability and privacy protection
0 views • 16 slides
Proxy Access to Medications Implementation Stages
This document outlines the implementation stages for proxy access to medications. It covers agreements with healthcare providers, prerequisites including compliance and data sharing agreements, and systems configuration for access to medical records. The stages include setting up access for care pro
0 views • 7 slides
Proxy Voting in Indian Elections: Developments and Perspectives
India has seen progress in allowing proxy voting for Non-Resident Indians, with recent proposals to extend this privilege to overseas Indians. The initiative aims to enhance voter participation, especially for those residing abroad. While some political parties support proxy voting, concerns exist r
0 views • 35 slides
Enhancing Air Quality Forecasting with TEMPO Retrievals in Proxy Observing System
Improvements in Air Quality Forecast Skill (AQFS) are explored by assimilating TEMPO retrievals in a Proxy Air Quality Observing System (AQOS) using WRF-Chem/DART. The study focuses on benefits identified through a designed OSSE scenario, including application to the Front Range Air Pollution and Ph
0 views • 8 slides
Trust as a Proxy for Certainty in Social Cohesion
Exploring the intricate relationship between trust, security, and social cohesion, this study delves into how trust serves as a proxy for certainty in uncertain environments. By analyzing societal properties and the role of trust in managing risks and insecurities, the Peace Research Institute Oslo
0 views • 16 slides
Updates on GOES-R Aerosol Optical Depth Validation Activities
Generated proxy data algorithm enhancements for post-launch validation activities were discussed at the GOES-R AWG 2nd Validation Workshop in January 2014. The use of MODIS reflectances as a proxy for ABI to retrieve Aerosol Optical Depth (AOD) was emphasized, along with the importance of AERONET gr
0 views • 25 slides
Proxy QoS Management for XR Devices in IEEE 802.11-23/1958r0 - November 2023
This document discusses the challenges faced by XR devices in terms of size, thermal constraints, cost, and power limitations leading to the proposal of Proxy QoS Management to enhance Wi-Fi performance. The aim is to leverage TGbn devices for improving legacy devices' connectivity within a Wi-Fi ne
0 views • 6 slides
Privacy Preservation in Machine Learning Systems via Proxy Use
Proxy use in machine learning systems is crucial for preserving privacy, especially in scenarios where fairness and privacy are at risk. This involves defining influential sub-programs, both qualitatively and quantitatively, to protect sensitive attributes. By utilizing proxies effectively, it enabl
0 views • 15 slides
Achieving Pay Equity Using Proxy Comparison Method in Ontario
Presentation by Doreen Lurie on achieving and maintaining pay equity in Ontario through the proxy method of comparison. Covers an overview of the Pay Equity Act, differences from Employment Standards, purpose of the act, and basic pay equity terms.
0 views • 5 slides
Setting Up a Proxy for Web Time Entry Approvers
Setting up a proxy is essential for Web Time Entry Approvers to ensure seamless approval processes when out of the office. Follow the outlined steps to grant proxy access and maintain security protocols. Remember to remove proxies when necessary and contact Payroll for any assistance.
0 views • 5 slides
Understanding Dynamic Proxy in Java for Type-Safe Proxy Objects
Learn about creating dynamic proxy classes in Java to implement interfaces at runtime without pre-compilation, enabling type-safe proxy object creation for method invocations. This allows for flexible and efficient handling of method calls through uniform interfaces.
0 views • 16 slides
Understanding Web Proxies and Proxy Architectures
Web proxies play a crucial role in networking by facilitating web requests between clients and servers. They come in various types such as forward proxies, reverse proxies, and open forward proxies, each with unique functionalities like content filtering, translation, and load balancing. This articl
0 views • 15 slides
Understanding the Impact of Proxy on Disability and Health Determinants Association
National surveys are evaluating standardized disability identifiers. The Washington Group Short Set and American Community Survey are being compared in the National Health Interview Survey. Limited research exists on these questions in disability research, providing an opportunity for analysis. The
0 views • 15 slides
Understanding Proxy ARP Implementation in IEEE 802.11ax
Proposed in September 2015, the document discusses the implementation of Proxy ARP with 802.11ax Access Points. It explains the Address Resolution Protocol (ARP), detailing how devices in a LAN communicate using MAC and IP addresses. The submission aims to provide comprehensive explanations on Proxy
0 views • 18 slides
Understanding Mobile Proxy Ecosystem: Privacy and Security Implications
The paper delves into the emerging trend of mobile proxy services, specifically focusing on the use of mobile devices as proxy peers. It addresses the security and privacy concerns associated with this practice, highlighting the potential risks posed to end-users. The study offers novel insights int
0 views • 21 slides
Proxy Effects and Fair Adaptation for Dynamic Adaptive Streaming
This study focuses on the implementation of a proxy effect analysis and fair adaptation algorithm for managing multiple competing dynamic adaptive streaming over HTTP clients. By considering factors like client awareness, network structure, and adaptation decisions, the algorithm aims to mitigate ne
0 views • 16 slides