Apache MINA: High-performance Network Applications Framework
Apache MINA is a robust framework for building high-performance network applications. With features like non-blocking I/O, event-driven architecture, and enhanced scalability, MINA provides a reliable platform for developing multipurpose infrastructure and networked applications. Its strengths lie i
3 views • 13 slides
Modeling and Generation of Realistic Network Activity Using Non-Negative Matrix Factorization
The GHOST project focuses on the challenges of modeling, analyzing, and generating patterns of network activity. By utilizing Non-Negative Matrix Factorization (NMF), realistic network activity patterns can be created and injected into live wireless networks. Understanding and predicting user behavi
4 views • 28 slides
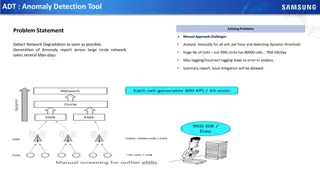
Automated Anomaly Detection Tool for Network Performance Optimization
Anomaly Detection Tool (ADT) aims to automate the detection of network degradation in a mobile communications network, reducing the time and effort required significantly. By utilizing statistical and machine learning models, ADT can generate anomaly reports efficiently across a large circle network
8 views • 7 slides
Revolutionizing Network Management with Intent-Based Networking
Explore the concept and benefits of Intent-Based Networking (IBN) in simplifying network configuration and enhancing efficiency. Learn how IBN automates network operations, aligns with business objectives, improves security, and ensures scalability and reliability. Discover the potential of IBN tool
0 views • 14 slides
Understanding the Components of Tourism for Destination Success
Tourism involves activities of individuals traveling outside their usual environment for leisure, business, or other purposes. The success of tourist destinations relies on Accessibility, Accommodation, Attractions, Amenities, and Activities. Accessibility ensures reachability to destinations via va
1 views • 15 slides
Network Compression Techniques: Overview and Practical Issues
Various network compression techniques such as network pruning, knowledge distillation, and parameter quantization are discussed in this content. The importance of pruning redundant weights and neurons in over-parameterized networks is highlighted. Practical issues like weight pruning and neuron pru
0 views • 37 slides
Network Slicing with OAI 5G CN Workshop Overview
Overview of Network Slicing with OAI 5G CN workshop focusing on the crucial role of network slicing in realizing the service-oriented 5G vision. This workshop covers topics like multiple logical networks creation on shared infrastructure, different types of network slices, preparation and instantiat
1 views • 6 slides
Network Design Challenges and Solutions in Business Data Communications
Issues in designing a Local Area Network (LAN) include needs analysis, technological design, and cost assessment. The traditional approach involves structured systems analysis, but faces challenges due to rapidly changing technology and increasing network traffic. The Building Blocks Approach recomm
1 views • 20 slides
Understanding 5G RAN Network Slicing and Architecture
Explore the intricate world of 5G Radio Access Network (RAN) and Network Slicing, delving into concepts such as SO Service Orchestrator, SDN-C Service Design, and Core Network Elements. Discover the significance of managing and designing mobile slice services, including eMBB, Massive IoT, and Missio
0 views • 26 slides
Understanding Snort: An Open-Source Network Intrusion Detection System
Snort is an open-source Network Intrusion Detection System (NIDS) developed by Cisco, capable of analyzing network packets to identify suspicious activities. It can function as a packet sniffer, packet logger, or a full-fledged intrusion prevention system. By monitoring and matching network activity
0 views • 23 slides
Data Flows and Network Challenges in Particle Physics Infrastructure
This overview delves into the data flows and network challenges faced in particle physics infrastructure, focusing on the JUNO project. It discusses the process of data reception, storage, and replication across various data centers, highlighting the bidirectional nature of data flows. Additionally,
0 views • 24 slides
Progress of Network Architecture Work in FG IMT-2020
In the Network Architecture Group led by Namseok Ko, significant progress has been made in defining the IMT-2020 architecture. The work has involved gap analysis, draft recommendations, and setting framework and requirements. Phase 1 focused on identifying 19 architectural gaps, such as demands for
1 views • 11 slides
Efficient Billion-Scale Label-Constrained Reachability Queries
Graph data sets are prevalent in various domains like social networks and biological networks. Label-Constrained Reachability (LCR) queries aim to determine if a vertex can reach another vertex through specific labeled edges. Existing works utilize exhaustive search or graph indexing techniques, but
0 views • 13 slides
Understanding Internet Routing Protocols
Explore the intricacies of routing protocols in the context of the Internet's large federated network. Delve into the concepts of reachability, message exchange, algorithm design, and the challenges posed by running an autonomous system. Gain insights into the Border Gateway Protocol (BGP) and inter
1 views • 26 slides
Understanding Interconnection Networks Topology
Exploring the topology of interconnection networks helps determine the arrangement of channels and nodes, impacting network cost, performance, latency, energy consumption, and complexity of implementation. Abstract metrics such as degree, hop count, and network diameter play crucial roles in evaluat
1 views • 56 slides
Transportation Network Modeling and Analysis with C.Coupled SE Platform
This content outlines the features and functionalities of the C.Coupled SE Platform (CSET Platform) developed by the Connetics Transportation Group. It covers aspects such as interface design, inputs merging, purposes, platform development using Cube, TAZs merging, and network attributes. The platfo
0 views • 11 slides
Human Disease Symptom Network: Understanding Disease Relationships Through Symptoms and Genes
The Human Disease Symptom Network (HSDN) is constructed using a large-scale medical bibliographic records database to form a network of human diseases based on symptom similarities. By integrating disease-gene associations and protein-protein interaction data, correlations between symptom similarity
0 views • 37 slides
Introduction to Network Analysis Using .NET
This presentation introduces the concept of network analysis using .NET in the humanities classroom. It provides a template for teaching and adapting network analysis tools for educational purposes. The guide explains the relevance of networks in processing and visualizing data, emphasizing the coll
0 views • 20 slides
Meridian: An SDN Platform for Cloud Network Services
Meridian is an SDN platform developed by Mohammad Banikazemi, David Olshefski, Anees Shaikh, John Tracey, and GuohuiWang at IBM T. J. Watson Research Center. The platform focuses on providing cloud network services efficiently. It encompasses an architecture that enables faster and more convenient n
0 views • 21 slides
Tackling Store Buffers in TSO Analysis
The discussion revolves around the management of store buffers in Total Store Ordering (TSO) analysis, contrasting Sequential Consistency (SC) memory model. Different protocols and approaches like Dekker's mutual exclusion and verification techniques for TSO are explored. An innovative method of red
0 views • 21 slides
Undecidability in Rectangular Hybrid Automata Analysis
The undecidability of the reachability analysis in rectangular hybrid automata (RHA) poses challenges for verifying cyber-physical systems. This complexity was demonstrated through a reduction from the Halting problem of two counter machines by Henzinger et al. Additionally, the review of computabil
0 views • 15 slides
Role-based Access Control Policies and Security Properties Overview
This content provides an overview of Role-based Access Control (RBAC) policies, Administrative RBAC (ARBAC) systems, and security properties in the context of access control in large organizations. It discusses the implementation of RBAC in various software systems, the assignment and revocation of
0 views • 18 slides
Enhancing Network Security with Software-Defined Snort and OpenFlow
Explore the implementation of Snort, Barnyard, and PulledPork within a Software-Defined Network framework using OpenFlow technology. Learn how these tools enhance network security through intrusion detection engines, rule management, and network traffic control mechanisms. Dive into the architecture
0 views • 15 slides
Challenges in Establishing a Secure Inter-Domain Routing System
The daunting task of creating a secure and trusted inter-domain routing system poses significant challenges due to the decentralized nature of the internet. Addressing issues such as propagation of false routing information, ensuring correct reachability, and dealing with the lack of a clear truth m
0 views • 15 slides
Understanding Routing Protocols in Network Layer
Routing protocols in the network layer dictate how data packets are routed through a network. This lecture delves into key concepts such as reachability, routing protocol components, and the workings of Distance Vector (DV) algorithms. It explains how updates propagate in networks efficiently with D
0 views • 31 slides
Understanding Network Metrics Through Centrality Analysis
This presentation introduces network metrics as tools to describe network characteristics and answer important questions. Using centrality metrics as an example, participants learn how to identify the most important nodes in a network based on different criteria such as degree centrality and closene
0 views • 15 slides
Understanding Network Analysis: Whole Networks vs. Ego Networks
Explore the differences between Whole Networks and Ego Networks in social network analysis. Whole Networks provide comprehensive information about all nodes and links, enabling the computation of network-level statistics. On the other hand, Ego Networks focus on a sample of nodes, limiting the abili
0 views • 31 slides
Understanding Logic Coverage in Software Testing
Logic coverage in software testing involves deriving predicates from decision statements in programs. Programmers aim to keep predicates simple to ensure effective testing. Applying logic criteria to program source code can be challenging due to reachability and controllability issues. The provided
0 views • 14 slides
Logic Coverage in Software Testing
Logic coverage from source code involves deriving predicates from decision statements in programs, where most predicates have less than four clauses. Wise programmers aim to keep predicates simple, as they affect coverage criteria such as COC, ACC, ICC, and CC, which collapse to predicate coverage (
0 views • 11 slides
Total Order Approach for Reachability Queries in Dynamic Graphs
Explore a total order approach for reachability queries in large dynamic graphs, discussing existing solutions for static graphs and dynamic updates. The Total Order Labeling framework and Butterfly update algorithms are presented as key contributions, focusing on scalability and transitive closure
1 views • 42 slides
Introduction to Generalized Stochastic Petri Nets (GSPN) in Manufacturing Systems
Explore Generalized Stochastic Petri Nets (GSPN) to model manufacturing systems and evaluate steady-state performances. Learn about stochastic Petri nets, inhibitors, priorities, and their applications through examples. Delve into models of unreliable machines, productions systems with priorities, a
0 views • 44 slides
Network Function Virtualization (NFV) Overview
Network Function Virtualization (NFV) focuses on virtualizing network functions to improve efficiency and reduce costs in network infrastructure. The lecture discusses key readings, devices that compose a network, specialization of devices, benefits of one-device-does-anything approach, and the goal
0 views • 21 slides
Enhancing Network Stability with Network Monitoring Systems
Network monitoring is crucial for efficient management and proactive issue detection in a network environment. Factors influencing an effective network system include choosing the best OEM, SLA agreements, and selecting a reliable System Integrator. Reactive monitoring can lead to financial losses a
0 views • 12 slides
Four List Cleaning Methods Related to Reachability to Improve Email Reachability – Benchmark Email
Bulk Mail Masters specializes in efficient, high-impact bulk email marketing services. We help businesses grow by delivering personalized email campaigns at scale, boosting engagement, conversions, and brand visibility. Reach your audience with preci
0 views • 7 slides
Four List Cleaning Methods Related to Reachability to Improve Email Reachability – Benchmark Email
Bulk Mail Masters specializes in efficient, high-impact bulk email marketing services. We help businesses grow by delivering personalized email campaigns at scale, boosting engagement, conversions, and brand visibility. Reach your audience with preci
0 views • 7 slides
Four List Cleaning Methods Related to Reachability to Improve Email Reachability
Bulk Mail Masters specializes in efficient, high-impact bulk email marketing services. We help businesses grow by delivering personalized email campaigns at scale, boosting engagement, conversions, and brand visibility. Reach your audience with preci
0 views • 7 slides
Four List Cleaning Methods Related to Reachability to Improve Email Reachability – Benchmark Email
Bulk Mail Masters specializes in efficient, high-impact bulk email marketing services. We help businesses grow by delivering personalized email campaigns at scale, boosting engagement, conversions, and brand visibility. Reach your audience with preci
0 views • 7 slides
Four List Cleaning Methods Related to Reachability to Improve Email
Bulk Mail Masters specializes in efficient, high-impact bulk email marketing services. We help businesses grow by delivering personalized email campaigns at scale, boosting engagement, conversions, and brand visibility. Reach your audience with preci
5 views • 7 slides
Accelerating Systemic Change Network Inaugural Workshop Summary
The Accelerating Systemic Change Network held its inaugural workshop at Howard Hughes Medical Institute in July 2016 to address the lack of coordination in improving higher education. With a vision to become a professional hub for change researchers in STEM education, the network aims to enhance ind
0 views • 5 slides
University Network Section Overview July 2015 - March 2016
The presentation covers the network team structure, team members, objectives, goals, report outline, network statistics, accomplishments, and future plans of the university network section from July 2015 to March 2016. It highlights efforts to provide stable internet and intranet services, restructu
0 views • 16 slides