How to Resolve QuickBooks Banking Error 9999?
How to Resolve QuickBooks Banking Error 9999?\nStuck with QuickBooks Banking Error 9999? Don't fret! This frustrating error disrupts bank connection in QBO. Fear not! Our guide equips you with solutions. Try waiting, checking credentials, or adjusting firewalls. If those fail, reconnect your bank ac
0 views • 4 slides
How to Resolve QuickBooks Error 1014?
How to Resolve QuickBooks Error 1014?\nStuck with QuickBooks Error 1014? Don't panic! This error disrupts QuickBooks by overloading the company file cache. Fear not! Our guide equips you with solutions. Rebuild the cache, close unnecessary programs, or update QuickBooks. For multi-user issues, try E
0 views • 3 slides
How to Resolve QuickBooks Error 1321?
How to Resolve QuickBooks Error 1321?\nStuck with QuickBooks Error 1321? Don't sweat! This error signals a permission issue. Try a simple retry first. If that fails, consider granting temporary admin rights (use with caution!). For advanced users, editing permissions or using the QBInstall tool can
0 views • 3 slides
Most Comprehensive Guide to Resolve QuickBooks Error 15222
Most Comprehensive Guide to Resolve QuickBooks Error 15222\nFacing the dreaded \"Error downloading updates\" in QuickBooks (Error 15222)? Don't panic! This error often results from digital signature issues. Follow these steps:\n\nRun QuickBooks as Administrator (simple fix).\nVerify the update file'
2 views • 3 slides
Understanding Memory Allocation in Operating Systems
Memory allocation in operating systems involves fair distribution of physical memory among running processes. The memory management subsystem ensures each process gets its fair share. Shared virtual memory and the efficient use of resources like dynamic libraries contribute to better memory utilizat
1 views • 233 slides
Understanding Memory Organization in Computers
The memory unit is crucial in any digital computer for storing programs and data. It comprises main memory, auxiliary memory, and cache memory, each serving different roles in data storage and retrieval. Main memory directly communicates with the CPU, while cache memory enhances processing speed by
1 views • 37 slides
Understanding Memory Organization in Computers
Delve into the intricate world of memory organization within computer systems, exploring the vital role of memory units, cache memory, main memory, auxiliary memory, and the memory hierarchy. Learn about the different types of memory, such as sequential access memory and random access memory, and ho
0 views • 45 slides
Understanding AARCH64 Linux Kernel Memory Management
Explore the confidential and proprietary details of AARCH64 Linux kernel memory mapping, virtual memory layout, variable configurations, DDR memory layout, and memory allocation techniques. Get insights into the allocation of physically contiguous memory using Continuous Memory Allocator (CMA) integ
0 views • 18 slides
Understanding Cache and Virtual Memory in Computer Systems
A computer's memory system is crucial for ensuring fast and uninterrupted access to data by the processor. This system comprises internal processor memories, primary memory, and secondary memory such as hard drives. The utilization of cache memory helps bridge the speed gap between the CPU and main
1 views • 47 slides
Dynamic Memory Allocation in Computer Systems: An Overview
Dynamic memory allocation in computer systems involves the acquisition of virtual memory at runtime for data structures whose size is only known at runtime. This process is managed by dynamic memory allocators, such as malloc, to handle memory invisible to user code, application kernels, and virtual
0 views • 70 slides
Understanding Error Codes in Customs CDS Tariff Training Module 11
This module focuses on interpreting error messages, identifying issues, and correcting errors in Customs CDS Tariff declarations. Learn about error code reference numbers, error descriptions, error locations, and how to fix common issues. Gain insights into cross-validation errors and protective mar
0 views • 13 slides
Understanding Garbage Collection in Java Programming
Garbage collection in Java automates the process of managing memory allocation and deallocation, ensuring efficient memory usage and preventing memory leaks and out-of-memory errors. By automatically identifying and removing unused objects from the heap memory, the garbage collector frees up memory
14 views • 22 slides
Understanding Memory Management in Operating Systems
Dive into the world of memory management in operating systems, covering topics such as virtual memory, page replacement algorithms, memory allocation, and more. Explore concepts like memory partitions, fixed partitions, memory allocation mechanisms, base and limit registers, and the trade-offs betwe
1 views • 110 slides
Efficient Identification of Memory Chip Errors with On-Die ECC
State-of-the-art memory error mitigations face challenges when dealing with on-die Error-Correcting Codes (ECC). "HARP" introduces a Hybrid Active-Reactive Profiling method to address these challenges by analytically studying the effects of on-die ECC and identifying key issues. Through hybrid profi
1 views • 4 slides
Understanding Shared Memory Architectures and Cache Coherence
Shared memory architectures involve multiple CPUs accessing a common memory, leading to challenges like the cache coherence problem. This article delves into different types of shared memory architectures, such as UMA and NUMA, and explores the cache coherence issue and protocols. It also highlights
2 views • 27 slides
Understanding Memory Management and Swapping Techniques
Memory management involves techniques like swapping, memory allocation changes, memory compaction, and memory management with bitmaps. Swapping refers to bringing each process into memory entirely, running it for a while, then putting it back on the disk. Memory allocation can change as processes en
0 views • 17 slides
Effective Error Handling in AUTOSAR: DEM and DET Components
Error handling in AUTOSAR is crucial for developing reliable automotive software. The Diagnostic Event Manager (DEM) and Error Tracer (DET) are key components that manage diagnostic events, error reporting, recovery, and fault diagnosis. By providing standardized frameworks and centralized error man
0 views • 9 slides
Software Security Principles and Practices: Enhancing Program Code Security
Understanding and addressing critical web application security flaws like unvalidated input, cross-site scripting, buffer overflow, injection flaws, and improper error handling is crucial in enhancing the security of program code. The NIST report NISTIR 8151 provides valuable recommendations to redu
2 views • 44 slides
Enhancing Memory and Concentration Techniques for Academic Success
Explore the fascinating world of memory and concentration through various techniques and processes highlighted in the provided images. Discover how sensory memory, short-term memory, and long-term memory function, along with tips on improving concentration, learning strategies, and the interplay bet
1 views • 34 slides
Understanding Memory Encoding and Retention Processes
Memory is the persistence of learning over time, involving encoding, storage, and retrieval of information. Measures of memory retention include recall, recognition, and relearning. Ebbinghaus' retention curve illustrates the relationship between practice and relearning. Psychologists use memory mod
0 views • 22 slides
Magnetization, Decay, and Error Fields in HTS Accelerator Magnets
The research conducted at The Ohio State University focuses on understanding the magnetization, decay, and influence of error fields in high-temperature superconducting (HTS) accelerator magnets. The study explores the impact of different superconducting materials such as Nb3Sn, YBCO, and Bi:2212 on
0 views • 21 slides
Understanding Memory Management in Computer Systems
Memory management in computer systems involves optimizing CPU utilization, managing data in memory before and after processing, allocating memory space efficiently, and keeping track of memory usage. It determines what is in memory, moves data in and out as needed, and involves caching at various le
1 views • 21 slides
Dynamic Memory Management Overview
Understanding dynamic memory management is crucial in programming to efficiently allocate and deallocate memory during runtime. The memory is divided into the stack and the heap, each serving specific purposes in storing local and dynamic data. Dynamic memory allocators organize the heap for efficie
0 views • 31 slides
Understanding Memory Management in C Programming
The discussion covers various aspects of memory management in C programming, including common memory problems and examples. It delves into memory regions, stack and heap management, and static data. The examples illustrate concepts like static storage, heap allocation, and common pitfalls to avoid.
0 views • 24 slides
Understanding Your Memory System: A Guide to Enhancing Recall
Learn about the three components of the memory system - sensory memory, short-term memory, and long-term memory. Discover why we forget and how to improve memory retention through techniques like positive attitude, focus, mnemonic devices, and more. Enhance your memory skills to boost learning effic
0 views • 8 slides
Understanding Memory Basics in Digital Systems
Dive into the world of digital memory systems with a focus on Random Access Memory (RAM), memory capacities, SI prefixes, logical models of memory, and example memory symbols. Learn about word sizes, addresses, data transfer, and capacity calculations to gain a comprehensive understanding of memory
1 views • 12 slides
Understanding Spectre and Meltdown Security Vulnerabilities
Spectre and Meltdown are two critical security vulnerabilities that exploit microarchitectural features to gain unauthorized access to memory. These vulnerabilities enable attackers to read memory that should be inaccessible, targeting branch prediction and exception handling mechanisms. Side channe
0 views • 19 slides
Optimizing Data Center Costs with Heterogeneous-Reliability Memory
Reducing data center costs while meeting availability targets is the focus of this study on memory error vulnerabilities. By employing a heterogeneous-reliability memory approach, storing error-tolerant data in less reliable memory and error-vulnerable data in more reliable memory, significant savin
0 views • 51 slides
Understanding Different Types of Memory Technologies in Computer Systems
Explore the realm of memory technologies with an overview of ROM, RAM, non-volatile memories, and programmable memory options. Delve into the intricacies of read-only memory, volatile vs. non-volatile memory, and the various types of memory dimensions. Gain insights into the workings of ROM, includi
0 views • 45 slides
Understanding Shared Memory, Distributed Memory, and Hybrid Distributed-Shared Memory
Shared memory systems allow multiple processors to access the same memory resources, with changes made by one processor visible to all others. This concept is categorized into Uniform Memory Access (UMA) and Non-Uniform Memory Access (NUMA) architectures. UMA provides equal access times to memory, w
0 views • 22 slides
Understanding Virtual Memory Concepts and Benefits
Virtual Memory, instructed by Shmuel Wimer, separates logical memory from physical memory, enabling efficient utilization of memory resources. By using virtual memory, programs can run partially in memory, reducing constraints imposed by physical memory limitations. This also enhances CPU utilizatio
0 views • 41 slides
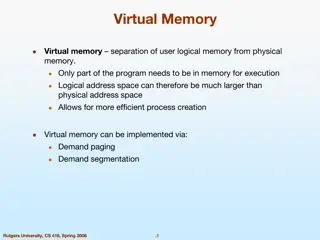
Understanding Virtual Memory and its Implementation
Virtual memory allows for the separation of user logical memory from physical memory, enabling efficient process creation and effective memory management. It helps overcome memory shortage issues by utilizing demand paging and segmentation techniques. Virtual memory mapping ensures only required par
0 views • 20 slides
Understanding Memory: Challenges and Improvement
Delve into the intricacies of memory with discussions on earliest and favorite memories, a memory challenge, how memory works, stages of memory, and tips to enhance memory recall. Explore the significance of memory and practical exercises for memory improvement.
0 views • 16 slides
Understanding Memory Management in Programming
Memory management is a critical aspect of programming to prevent issues like memory leaks, use-after-free bugs, and memory corruption. Proper memory allocation and deallocation techniques can improve performance and avoid security vulnerabilities. Learn about heap storage, garbage collection, smart
0 views • 27 slides
Memory Management Principles in Operating Systems
Memory management in operating systems involves the allocation of memory resources among competing processes to optimize performance with minimal overhead. Techniques such as partitioning, paging, and segmentation are utilized, along with page table management and virtual memory tricks. The concept
0 views • 29 slides
Effective Program Verification for Relaxed Memory Models
Memory model vulnerabilities arise when programmers do not strictly adhere to locking disciplines in performance-critical code, leading to data races that can break on relaxed memory models. This can be challenging to detect and analyze due to the complexities introduced by both compilers and hardwa
0 views • 22 slides
Memory Model Safety of Programs Research
Explore the challenges and vulnerabilities in memory models of programs, emphasizing the importance of maintaining strict locking discipline for performance-critical code. The research discusses issues with relaxed memory models on multicore machines and provides examples of memory model vulnerabili
0 views • 14 slides
Experimental Analysis of Vulnerabilities in MLC NAND Flash Memory Programming
This session at HPCA explores the experimental analysis, exploits, and mitigation techniques related to vulnerabilities in MLC NAND flash memory programming. The presentation delves into the risks associated with NAND flash memory, such as data corruption and errors during read operations. It discus
0 views • 10 slides
Enhancing Memory Bandwidth with Transparent Memory Compression
This research focuses on enabling transparent memory compression for commodity memory systems to address the growing demand for memory bandwidth. By implementing hardware compression without relying on operating system support, the goal is to optimize memory capacity and bandwidth efficiently. The a
0 views • 34 slides
Locality-Aware Caching Policies for Hybrid Memories
Different memory technologies present unique strengths, and a hybrid memory system combining DRAM and PCM aims to leverage the best of both worlds. This research explores the challenge of data placement between these diverse memory devices, highlighting the use of row buffer locality as a key criter
0 views • 34 slides