Proposed Approach for MAC Address Assignment in IEEE 802.11
IEEE 802.1CQ is working on a mechanism to assign local MAC address blocks to end nodes specifically related to IEEE 802.11 standards. The current draft lacks a pre-association mechanism for IEEE 802.11 stations to obtain a local MAC address before association. The proposed remedy suggests specifying
6 views • 7 slides
Understanding Theories of the Policy Cycle in Policy Analysis
The policy cycle theory describes the evolution of policy issues from inception to evaluation, impacting scientific research and policy formulation. It outlines stages from the 1950s, influenced by Lasswell's seven-stage model, serving as a framework for organizing policy processes. Despite the line
3 views • 30 slides
IEEE 802.11-20/0054r1 MLD MAC Address and WM Address
In the document IEEE 802.11-20/0054r1, the focus is on Multi-Link Framework for MLD address identification and differentiation. It explains the usage of MLD MAC address and STA WM medium address in wireless setups. The document also addresses the need for identifying different MLDs using MAC address
0 views • 16 slides
Proposal for OTA MAC Change in IEEE 802.11-23/268r1
This proposal suggests using separate and unrelated random OTA MAC addresses for Source Address (SA) and Destination Address (DA) to enhance privacy and security in IEEE 802.11 networks. By obscuring the relationship between traffic, it aims to improve transmission privacy for multiple STAs associat
0 views • 14 slides
IEEE Std. 802.11-22/1017r0 Overview and Architecture Presentation
This presentation by Dorothy Stanley from HP Enterprise delves into the utilization of IEEE Std. 802.11-2020 standards focusing on the IEEE Std. 802 overview and architecture. It covers topics such as the use of LLC, MAC address formats, QoS mechanisms, MSDU formats, and various MAC services and pro
0 views • 10 slides
Challenges in Policy Implementation and Lessons Learned
The content discusses the challenges faced in policy implementation, focusing on the gap between policy design and execution. It highlights key steps in policy-making, reasons for implementation failures, and factors influencing successful policy outcomes. Examples from Zambia's National Science and
0 views • 14 slides
Enhancing Privacy with Randomized MAC Addresses in 802.11 Networks
This presentation discusses the use of randomized MAC addresses as a privacy-enhancing measure in 802.11 networks. Passive observation of MAC addresses poses privacy risks, and the proposal suggests assigning random MAC addresses to portable devices to mitigate tracking risks. By periodically changi
0 views • 10 slides
Privacy Issues in IEEE 802.11 Networks: Tracking and MAC Randomization
This presentation delves into the privacy concerns surrounding 802.11 networks, focusing on tracking vulnerabilities and the limitations of MAC randomization in preventing tracking. It discusses the ease of tracking devices, the risk of passive tracking due to MAC addresses being visible in frames,
0 views • 27 slides
IEEE802.15-14-0110-01-0mag MAC Timing Discussion Points for IEEE 802.15.4 Revision
Initial discussion document submitted by Benjamin A. Rolfe from Blind Creek Associates addressing MAC timing issues in the IEEE 802.15.4 standard revision. The document identifies potential problems, provides a list of questions for consideration, and outlines areas for improvement. It includes stat
0 views • 8 slides
Summary of MAC Address Policy Contribution to IEEE 802.11
This document outlines the contribution of MAC address policy to IEEE 802.11, focusing on defining ANQP and Beacon elements to convey information about addressing types supported by the network. It details how specific bits in the ANQP element represent support for various MAC address types includin
0 views • 5 slides
Discussion on IEEE 802.11 Group vs. Individual Epochs
Trigger discussion on differences between group and individual epochs in IEEE 802.11 standards. Group epochs involve simultaneous transitions of MAC parameters by all or selected STAs based on AP trigger, while individual epochs allow each STA to independently change its parameters. Key points inclu
0 views • 4 slides
Proposal for Establishing Epochs in IEEE 802.11-17/2059r1 Network
This proposal by Stephen Rodriguez from Cisco suggests partitioning time into epochs based on network trust levels to determine when clients should change their MAC addresses dynamically. The idea involves rotating MAC addresses at specified intervals depending on the trust level of the network conn
0 views • 5 slides
Implications of IEEE 802.11 State Machine and MAC Randomization
The document discusses the state machine transitions in IEEE 802.11, focusing on MAC address handling and implications for STA connectivity within an ESS. It explains the scenarios where a STA can use different MAC addresses, emphasizing the binding of state to specific address configurations and th
0 views • 11 slides
IEEE 802.11-21/1585r10: Identifiable Random MAC Address Presentation Summary
This presentation discusses the concept of Identifiable Random MAC (IRM) addresses in the IEEE 802.11-21/1585r10 standard. It covers the purpose of IRM addresses in preventing third-party tracking while allowing trusted parties to identify specific devices. The presentation outlines the use of Ident
0 views • 24 slides
How to Record Your Voice: A Comprehensive Guide for Windows, Mac, and Smartphones
Learn how to record your voice for ePoster, MP3, or podcasts using Windows 10, Mac, Android, or iPhone/iPad devices. Find step-by-step instructions for recording on different platforms, including using Windows Voice Recorder on a Windows 10 computer and QuickTime Player on a Mac. Discover tips for a
1 views • 10 slides
Exploring Mac OS & VoiceOver: A Comprehensive Guide with Belinda Rudinger
Dive into the world of Mac OS and VoiceOver with expert Belinda Rudinger in this detailed tutorial. Learn about screen readers, VoiceOver commands, built-in features, interaction tools, customization options, and useful utilities. Discover how to navigate the Mac ecosystem seamlessly using VoiceOver
0 views • 20 slides
Morality in UK Drug Policy: Policy Constellations Analysis
Morality plays a significant role in shaping drug policy in the UK, as revealed by the research conducted by Professor Alex Stevens at the University of Kent. The study investigates the moral commitments underlying different policy positions in UK drug policy debates, highlighting five ethico-politi
0 views • 19 slides
Understanding IP Routing and Switching in Computer Networks
In the world of computer networking, IP routing and switching play crucial roles in ensuring efficient data transmission. Switches make decisions based on MAC addresses, while routers route based on IP information. By managing routing tables and using static or dynamic routing protocols, networks ca
0 views • 13 slides
Industrial Policy: The Old and The New - Insights by Dani Rodrik
Industrial policy, as presented by Dani Rodrik in May 2019, emphasizes the importance of empirical work, the differences between old and new policies, and the targets industrial policy should focus on. The theoretical arguments for industrial policy highlight market imperfections, learning spillover
0 views • 26 slides
Lightweight Cryptography: Key-Reduced Variants and Beyond-Birthday-Bound Security
Lightweight cryptography has emerged as a hot research topic in the past two decades, with over 60 ciphers proposed. This includes examples like PRESENT, GIFT, SIMON/SPECK, and more. Authenticated encryption through CAESAR and NIST LWC plays a vital role, with ASCON and ACORN leading the lightweight
0 views • 25 slides
Parental Control Based on MAC Address in Wi-Fi Routers
The document discusses the implementation of parental control features based on MAC addresses in home-brand wireless routers and enterprise-class access points. It highlights real-world examples and market prevalence of this functionality, emphasizing its presence in various Wi-Fi router brands. The
0 views • 13 slides
The Migration Advisory Committee Review and Findings
The Migration Advisory Committee (MAC) is an independent advisory body formed in 2007 to provide recommendations to the government on migration issues. The MAC does not create or implement policy but advises through research and analysis in various areas like economics, education, and stakeholder en
0 views • 13 slides
Locally-Unique Address Assignment Protocols in IEEE 802 Networks
This content discusses the Local MAC Address Protocol for locally-unique assignment of 48-bit and 64-bit addresses in IEEE 802 networks. It specifies protocols, procedures, and management objects for address assignment in a structured manner. The document also covers peer-to-peer claiming, server mo
0 views • 11 slides
Local MAC Address Assignment Protocol (LAAP) and 802.1CQ
The Local MAC Address Assignment Protocol (LAAP) in conjunction with 802.1CQ specifies protocols and procedures for locally unique assignment of MAC addresses in IEEE 802 networks. LAAP operates in two modes - Server Mode and Peer-to-Peer Mode, ensuring efficient allocation of MAC addresses while av
0 views • 15 slides
Introduction to IEEE 802c SLAP
IEEE 802c defines Local Medium Access Control (MAC) Address Usage, providing structured approaches through the Structured Local Address Plan (SLAP) in different regions of the local MAC address space. Local MAC addresses are not globally unique, and the assignment is within local administration's sc
0 views • 9 slides
Caseous Mitral Valve Calcification (C-MAC) and Stroke: Overview and Management
Caseous Mitral Valve Calcification (C-MAC) is a rare condition characterized by spectrum liquefaction necrosis of the mitral annular calcification (MAC), potentially leading to cardiovascular complications like strokes and emboli. This article discusses the features, diagnostic aspects, and treatmen
0 views • 7 slides
Understanding Policy Formulation: Key Concepts and Approaches
Policy formulation is a crucial step in the policy-making process, involving identifying and crafting policy alternatives to address various issues. This phase requires participants to define policy problems, develop alternatives, and select the most feasible solutions based on criteria such as feas
0 views • 12 slides
Enhancing MAC Header Protection in IEEE 802.11 Networks
This document discusses the need for improved protection of MAC headers in IEEE 802.11 networks to address security concerns related to certain fields that are currently not adequately protected. It emphasizes the importance of safeguarding vital information in MAC headers to prevent potential attac
0 views • 12 slides
IEEE 802.11-22/0424r1 - MAAD MAC Protocol Overview
The document discusses the MAAD MAC protocol, where the AP assigns a MAAD MAC address to the STA during association. Key differences from other schemes are highlighted, emphasizing the use of MAAD MAC addresses as identification. Details on support indication, address allocation, and recognition mec
0 views • 7 slides
IEEE 802.11-22/0955r0 TGbh Pre-association Schemes Exploration
The document explores the pre-association schemes NGID, MAAD, and IRM within the IEEE 802.11-22 standard. It discusses how the schemes operate, comparing RRCM to MAAD and IRM, and addresses the use of Probes and MAC addresses in pre-association scenarios. The presentation clarifies the allocation of
0 views • 15 slides
Understanding Network Security Part 2: Link Layer and ARP
Exploring the vulnerabilities in simple network topologies with hubs and the need for examining the link layer to prevent eavesdropping. Dive into MAC addresses, ARP (Address Resolution Protocol), and how machines translate IP addresses to physical Ethernet addresses. Learn about ARP tables, the tra
0 views • 61 slides
Kookmin University PHY and MAC Proposal for Image Sensor Communication
Kookmin University's proposal focuses on the general architecture of PHY and MAC layers for image sensor communication. The document covers design principles, compatibility features, frame formats, error correction, and various considerations related to supporting commercial cameras, frame rates, sa
0 views • 39 slides
RCM Procedure for Secure Parameter Obfuscation in IEEE 802.11 Networks
The document discusses the RCM procedure within IEEE 802.11 networks, focusing on obfuscating parameters like MAC addresses for enhanced security during CPE Client and CPE AP association. It outlines mechanisms for changing MAC addresses, SN, PN, AID, and TID without connection loss. The proposal su
0 views • 12 slides
Understanding Address Resolution Protocol (ARP) in Computer Networks
Address Resolution Protocol (ARP) is essential for translating IP addresses to MAC addresses in computer networks. ARP facilitates communication between devices on the same network by resolving addresses and enabling efficient data transmission. This protocol involves message exchanges, hardware bro
0 views • 20 slides
Concerns for Longevity of OUI/MAC Address Registry
OUI registry provides company identifiers essential for creating globally unique MAC addresses. With a target of 100-year longevity, concerns arise 40 years into assignments due to accelerating consumption rates. The introduction of Company ID (CID) is explored as a solution for reducing OUI consump
0 views • 5 slides
IEEE 802.11-23/0421r1: Understanding the IRM Scheme for MAC Address Privacy
The document discusses the use of the Same MAC Address (SMA) scheme in IEEE 802.11-23/0421r1 and introduces the Improved Randomized MAC (IRM) scheme as a privacy-enhancing solution. It explores the implementation and benefits of IRM over SMA, addressing issues like privacy requirements, device ident
0 views • 7 slides
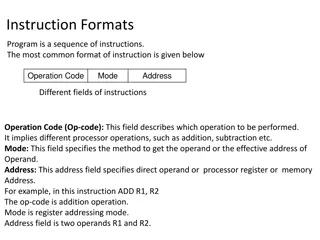
Understanding Different Instruction Formats in Computing
Instruction formats in computing include one-address, two-address, three-address, and zero-address instructions, each with specific ways of specifying operations and operands. One-address instructions utilize an implied accumulator register, while two-address and three-address instructions allow for
0 views • 18 slides
Overview of MAAD MAC Address Designation Scheme for IEEE 802.11-22/1650r4
This document discusses the MAAD (MAC Address Designation) scheme proposed for IEEE 802.11-22/1650r4, focusing on its basics, co-existence with Device ID, probe usage, privacy aspects, spoof AP mitigation, and more. The objective is to clarify the simplicity, security, and applicability of MAAD as a
0 views • 23 slides
Enhancement of Rule-based Random and Changing MAC Proposal in IEEE 802.11-22/1802r0
This document details the enhancements proposed for the Rule-based Random and Changing MAC (RRCM) in IEEE 802.11-22/1802r0. The RRCM concept involves generating Random MAC (RMA) addresses locally to increase security and prevent trackability in wireless networks. Key aspects include RMA generation,
0 views • 12 slides
MAC Address Randomization in IEEE 802.11: Privacy Concerns and Solutions
The document discusses the rise of MAC randomization in IEEE 802.11 networks, addressing motivations, benefits, concerns over privacy implications, and real-life scenarios highlighting the risks associated with passive observation of MAC addresses. It emphasizes the importance of safeguarding privac
0 views • 14 slides