Email Security and Encryption Technologies Overview
Email security is crucial in today's digital world. This content discusses various email security measures, including PGP and S/MIME systems, and their utilization in business and personal communications. It also explores the history of PGP encryption, the role of Philip R. Zimmermann, and the characteristics of secure email transmission. The content further delves into the technical aspects of PGP, such as the algorithms used for encryption and the services it provides. Additionally, it explains authentication through digital signatures and confidentiality measures in email communication, highlighting the encryption processes involved.
Download Presentation

Please find below an Image/Link to download the presentation.
The content on the website is provided AS IS for your information and personal use only. It may not be sold, licensed, or shared on other websites without obtaining consent from the author. Download presentation by click this link. If you encounter any issues during the download, it is possible that the publisher has removed the file from their server.
E N D
Presentation Transcript
Authentication and confidentiality problems Two systems: - PGP (Pretty Good Privacy) - S/MIME (Science Multipurpose Internet Mail Extension). System utilization S/MIME Industrial Standard for business utilization PGB personal electronic mail 2
Philip R. Zimmermann created the first version of PGP encryption in 1991.(freeware) Shortly after its release, PGP encryption found its way outside the United States and in February 1993 Zimmermann became the formal target of a criminal investigation by the US Government for munition export without a license". Cryptosystems using keys larger than 40 bits were then considered munitions within the definition of the US export without a license; PGP has never used keys smaller than 128 bits so it qualified at that time. Penalties for violation, if found guilty, were substantial. After several years, the investigation of Zimmermann was closed without filing criminal charges against him or anyone else. After the Federal criminal investigation ended in 1996, Zimmermann and his team started a company to produce new versions of PGP encryption. 3
Caratteristiche di sicurezza Confidenzialit Autenticazione di chi spedisce Integrit del messaggio Autenticazione del ricevente 4
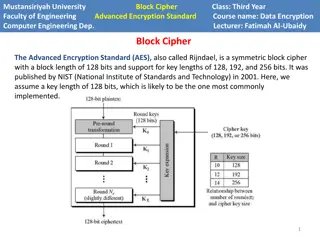
PGP is based on: RSA, DSS, and Diffie- Helman algorithms for public key encryption and CAST-128, IDEA e TDEA algorithms for symmetric key encryption. SHA-1 for hash functions. PGP services: - Authentication - Confidentiality - Compression - E-mail compatibility - Segmentation 5
Authentication (digital signature) 1. The sender creates a message 2. SHA-1 is used to generate a 160 bit hash code of the message 3. The hash code is encrypted with RSA using the sender s private key and the result is prepended to the message. 4. The receiver uses RSA with the sender s public key, to decrypt and recover the hash code. 5. The receiver generates a new hash code for the message and compares it with the decrypted hash code. If the two match, the message is accepted as authentic 6
Confidentiality 1. The sender generates a message and a random 128-bit number to be used as a session key for this message only. (one time key) 2. The message is encrypted, using a symmetric algorithm (CAST-128 or IDEA or 3DES) with the session key 3. The session key is encrypted with RSA, using the recipient s public key, and is prepended to the message 4. The receiver uses RSA with its private key to decrypt and recover the session key 5. The session key is used to decrypt the message. 7
Authentication and Confidentiality The sender - Signs the message with its private key -Encrypts the message with the session key -Encrypts the session key with the public key of the receiver 8
Public key certification The mechanism is different from that of Certification Authority. The PGP public keys may be distributed through a public keys server.When a user submits a public key to one of these servers, the server sends a copy of the key to all the other servers and provides the key to anyone requires the key. A different and very common method of distributing its public key consists in to insert them in the personal web page. 9
Compression A message may be compressed, for storage or transmission using ZIP Email compatibility An encrypted message may be converted to an ASCII string using radix-e conversion Segmentation To accomodate maximum message size limitations, PGP performs segmentation and reassembly 10