Vulnerability: Meaning, Types, and Factors affecting Vulnerability
This article explores the concept of vulnerability, including its meaning, types (physical and social), and factors that contribute to vulnerability. It discusses the impact of hazardous events on communities, infrastructure, and the environment, and highlights the importance of awareness and prepar
26 views • 31 slides
Non Coronary Vascular Stents
Safe scanning of patients with non-coronary vascular stents (NCVS) in MRI settings in NHS Scotland. It covers key questions regarding the safety of patients with NCVS, including risks associated with MRI at different strengths, timing of MRI post-stent implantation, and the safety of various stent m
1 views • 9 slides
Evolution of CT Scan Technology and Terminology
The development of CT scanning technology revolutionized medical imaging. Godfrey Hounsfield introduced computerized axial transverse scanning in 1972, with Allan Cormack's mathematical contributions. Dr. Robert Ledley created the first whole-body CT scanner in 1974. Dr. Willi Kalender further advan
1 views • 121 slides
Enhancing Cybersecurity with Bluedog VAPT Services
Bluedog Security Monitoring offers essential cybersecurity services, including Vulnerability Assessment and Penetration Testing (VAPT). Their automated VAPT combines External Vulnerability Scanning and WebApp Scanning to provide comprehensive testing solutions that help businesses prioritize risks,
0 views • 16 slides
Environmental Scanning Techniques for Business Adaptation
Businesses are integral parts of society and must stay abreast of surrounding changes to thrive. Environmental scanning is crucial for businesses to adapt and evolve effectively.
0 views • 9 slides
Risk Management in Environmental Geography and Disaster Management
Risk management in environmental geography and disaster management involves assessing the potential losses from hazards, evaluating vulnerability and exposure, and implementing strategies to mitigate risks. It includes calculating risk, dealing with risk through acceptance, avoidance, reduction, or
2 views • 10 slides
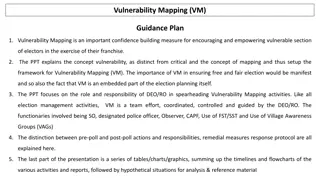
Comprehensive Guide to Vulnerability Mapping in Election Planning
Explore the significance of Vulnerability Mapping (VM) in empowering vulnerable voters, understand the concept, role of DEO/RO, and the objective of identifying and addressing voter vulnerability. The presentation emphasizes pre-poll and post-poll actions, remedial measures, and timelines, providing
3 views • 42 slides
Improve Your Reading Skills: Scanning and Skimming Techniques
Enhance your reading skills by mastering the art of scanning and skimming. Learn how to efficiently search for specific information without reading every word. Discover tips for scanning different types of texts and practice answering questions based on scanned content.
11 views • 12 slides
Vulnerability Mapping (VM).Guidance Plan
Vulnerability Mapping (VM) is crucial in empowering vulnerable voters by identifying and addressing potential threats to their exercise of franchise. This guide explains the concept of vulnerability mapping, its role in ensuring free and fair elections, and the responsibilities of election officials
2 views • 42 slides
Telecom Security Testing: Vulnerability Assessment & Remediation
Telecom security testing is crucial for safeguarding infrastructure against hacks. Learn about vulnerability assessment, common weaknesses, types of vulnerabilities, severity scoring, and automated tools like Nessus and Nexpose. Explore network, web application, and host-based vulnerability testing
0 views • 18 slides
Leveraging Artifact Dependency Graphs for Software Vulnerability Detection
Explore how LLVM-GitBOM utilizes artifact dependency graphs to detect vulnerabilities in software dependencies. The presentation covers the overview of GitBOM, CVE detection, supply chain vulnerabilities, and the importance of precise build tools in vulnerability scanning. Learn about utilizing gito
1 views • 34 slides
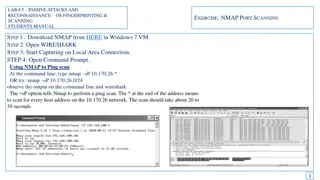
Passive Attacks and Reconnaissance using NMAP for Network Scanning
Learn how to use NMAP for passive attacks and reconnaissance through port scanning techniques like ping scan, TCP port scan, and stealth scan. Understand how to analyze the output in Wireshark to identify open ports and version numbers on target systems.
2 views • 7 slides
Passive Attacks and Reconnaissance in Network Security
Passive attacks involve monitoring target systems through port scanning or other means to locate vulnerabilities. Scanning is the first active action taken against a target network based on information gathered through footprinting, allowing deeper penetration. It includes scanning ports and service
0 views • 24 slides
Environmental Scanning Tool for Strategic Workforce Planning Cycle
In the Compare stage of strategic workforce planning, utilizing the Environmental Scanning Tool can assist in identifying work and workforce scenarios to achieve organizational goals. The tool consists of three templates including Choosing the Right Type of Data, Environmental Scanning Template, and
1 views • 9 slides
The Vulnerability Index for Small Island Developing States
This article discusses the concept of vulnerability in the context of countries, focusing on Small Island Developing States (SIDS). It explores the differences between vulnerability and poverty, the history of vulnerability index development from SIDS to Least Developed Countries (LDCs), and critiqu
8 views • 44 slides
Integrated Vulnerability Assessment and Human Security for Sustainable Livelihoods in the Solomon Islands
The approach to the Solomon Islands Integrated Vulnerability Assessment (SIIVA) and the Integrated Vulnerability and Adaptation Assessment (IVA) are key methodologies to assess climate change risks and prepare nations for adaptation. The objectives include informing national climate change policies,
0 views • 21 slides
Effective Reading Strategies: Skimming and Scanning Techniques
Develop your reading skills with skimming and scanning techniques. Skimming helps you quickly grasp the main ideas of a text, while scanning allows you to find specific information efficiently. Learn how to differentiate between the two methods and when to use each effectively.
0 views • 7 slides
Economic Vulnerability Premium for SIDS - Webinar Insights
Presentation outlines applying Economic Vulnerability Index (EVI) for an Economic Vulnerability Premium in Small Island Developing States (SIDS) during ADF 13 cycle. Details ADF grants availability, grant allocation framework, performance-based allocation system, and modifications needed for SIDS.
0 views • 14 slides
Disaster Recovery and Incident Response Concepts
This content covers the essential concepts of disaster recovery, incident response, penetration testing, vulnerability scanning, and business continuity planning in the context of cybersecurity. It explains the goals and steps involved in penetration testing, vulnerability scanning tasks, business c
2 views • 15 slides
Network Monitoring and Vulnerability Scanning Overview
Kashif Mohammad from the Department of Physics at the University of Oxford provides insights into their setup involving ZEEK, ELK Monitoring, and OpenVas for network monitoring and vulnerability scanning. The team aims to enhance network security through structured classification of nodes based on t
1 views • 10 slides
Gender Considerations in Climate Vulnerability and Risk Assessments for Agriculture
This training workshop explores the intersection of gender, climate vulnerability, and risk assessments in adaptation planning for the agriculture sectors. It delves into how women and men may experience climate change effects differently and discusses ways to ensure gender considerations are includ
0 views • 6 slides
Implementing Barcode Scanning to Reduce Dispensing Errors in Pharmacy
Implementation of barcode scanning in pharmacy departments has been shown to significantly reduce dispensing errors, ensuring greater accuracy in medication dispensation. Despite the generally low error rate among pharmacists, high volumes of dispensing can still lead to a substantial number of erro
1 views • 20 slides
Vulnerability and Capacity Issues in Civil Courts
Exploring vulnerability and capacity issues in civil courts, this content delves into the importance of addressing vulnerabilities of parties and witnesses for ensuring fair participation and quality evidence in legal proceedings. Topics covered include factors contributing to vulnerability, the rol
0 views • 21 slides
Coastal Vulnerability Assessment of Curacao, Netherlands Antilles
Conduct a comprehensive Coastal Vulnerability Audit of Curacao, Netherlands Antilles, using the Coastal Vulnerability Audit Tool (CVAT) to assess physical, human, and engineering infrastructure systems, as well as vulnerability, planning, and resiliency action plans. Consider factors such as climati
0 views • 10 slides
What Are the 5 Benefits of Choosing an Advanced MRI Scanning Centre in Panchkula for Accurate Diagnosis
early diagnosis is equally important in treatment. If you are in Panchkula or the places nearby, it is a very wise decision to opt for a modern MRI scanning centre, for example, Kior Healthcare.
1 views • 3 slides
Breast Ultrasound: Anatomy, Patient Preparation, and Scanning Protocol
This informative content delves into breast ultrasound, covering topics such as breast anatomy, patient preparation and positioning, scanning protocol, required images, and normal sonographic appearances. It provides valuable insights into the structure and composition of the breast, guidelines for
0 views • 8 slides
Mastering Reading Techniques: Skimming, Scanning, and Business Insights
Enhance your reading skills with a focus on skimming, scanning, and understanding business concepts such as commercial vs. retail, B2B vs. B2C, and online shopping trends. Dive into the specifics of general vs. specific information retrieval and learn about dual pricing strategies in the retail sect
0 views • 20 slides
Different Reading Techniques: Skimming and Scanning Explained
Reading involves the process of gaining meaning from text using eyes and brain. Skimming and scanning are two specific types of reading techniques that help readers to quickly grasp the main idea or find specific information in a text. Skimming is like gist reading, where you get a general idea of t
0 views • 17 slides
Reimagining Vulnerability: Rethinking the Body and Human Dignity
The notion of vulnerability is explored within the framework of the human body and dignity, challenging traditional concepts of autonomy and independence. Scholars like Martha Nussbaum and Fineman provide insights on the universal nature of vulnerability and advocate for a shift towards recognizing
0 views • 21 slides
Risks and Vulnerability in Risk Assessment
This module focuses on understanding risks, vulnerability, and conducting risk assessments in disaster risk management. It covers terminologies such as threats, hazards, vulnerability, and exposure, essential for prioritizing risks and initiating risk reduction measures.
0 views • 24 slides
Cybersecurity Footprinting and Scanning Techniques
Learn about the techniques involved in cybersecurity footprinting and scanning to protect against information gathering, target acquisition, and unauthorized access. Explore topics such as network enumeration, DNS interrogation, and scanning methods to identify vulnerabilities and enhance security m
0 views • 8 slides
Gamifying Vulnerability Reporting for Coordinated Disclosure at Microsoft Security Response Center
Christa Anderson, a Senior Security Program Manager at Microsoft's Security Response Center, discusses the importance of gamifying vulnerability report data to encourage coordinated disclosure. The MSRC Top 100, announced at Black Hat USA, plays a crucial role in the public credit strategy by recogn
0 views • 13 slides
Process of Launching an Enterprise: From Scanning Environment to Market Research
The process of launching an enterprise involves scanning the environment, locating business opportunities, converting opportunities into reality, conducting market research, developing a business plan, and managing the entrepreneur. It starts with analyzing the external and internal environment, fol
2 views • 8 slides
Atomic Dimensions: Scanning Probe Microscopy
Delve into the world of nanoscale imaging with Scanning Probe Microscopy (SPM) techniques like Scanning Tunneling Microscopy (STM) and Atomic Force Microscope (AFM). Unlike optical microscopes, SPM methods break the diffraction limit by relying on intermolecular forces and quantum tunneling for unpa
0 views • 26 slides
Enhancing Nuclear Security Through Creative Vulnerability Assessment
Creative and effective vulnerability assessment and testing are essential in nuclear security to identify weaknesses and improve defense systems against intelligent adversaries. The need for in-depth assessment and realistic testing is emphasized to uncover vulnerabilities that adversaries may explo
0 views • 8 slides
Vulnerability in Research Populations
Vulnerability in research populations refers to being exposed to harm without the ability to protect oneself adequately. Factors contributing to vulnerability include intrinsic limitations like decision-making capacity and situational influences such as political or economic circumstances. Different
0 views • 22 slides
Exploring Vulnerability and Power Dynamics in Imperial Rome: Phaedrus' Perspective
Delve into the intricate relationship between constructions of vulnerability in imperial Latin texts and the material reality of vulnerability in ancient Rome. Discover how cultural perceptions of male citizen invulnerability rely on affirming vulnerability in others. Uncover the strengths of vulner
0 views • 10 slides
Advantages of Scanning Lidars in Wind Resource Assessment
Scanning lidars offer a cost-effective and flexible solution for wind resource assessment compared to traditional met masts. They provide multi-point measurements without the need to relocate hardware, reducing uncertainties and risks in wind energy projects. This technology enhances the accuracy of
0 views • 10 slides
Effective Reading Techniques: Skimming, Scanning, and More
Explore different reading techniques like skimming, scanning, extensive reading, and intensive reading. Skimming helps to quickly grasp the main idea, while scanning is useful for finding specific information. Extensive reading is for pleasure, while intensive reading involves deep understanding and
1 views • 6 slides
Enhanced AC Coefficients Compression Techniques
Explore improved methods for compressing AC coefficients in JPEG coding, utilizing alternate adaptive scanning and multi-feature determined context arithmetic coding. The approach involves scanning order determination, entropy coding, and arithmetic coding techniques to enhance compression efficienc
0 views • 10 slides