Historical Sources as Evidence
Explore the importance of historical sources as evidence in the Victorian Curriculum History context, focusing on how students analyze, evaluate, and utilize sources to create historical explanations and arguments. Discover the significance of primary and secondary sources, perspectives of historica
1 views • 46 slides
Maximizing Impact: The Role of Rich Snippets in SERPs"User Intent
User intent, also known as search intent, refers to the underlying goal or purpose a user has when performing an online search. It goes beyond the literal interpretation of keywords and focuses on understanding why a person is searching. Recognizing and catering to user intent is crucial for creatin
3 views • 10 slides
Understanding Libyan Civil Law: Sources and Application
Civil law in Libya draws influences from Ottoman, French, Italian, and Egyptian sources, with a move towards a legal system based on Sharia. This article discusses the priority of using Libyan Civil Law sources and emphasizes the importance of laws that cater to the wellbeing of its citizens. The so
1 views • 7 slides
Sources of Drugs and Their Origins
Drugs can be sourced from six major categories: plants, animals, minerals/earth, microbiological sources, semi-synthetic sources, synthetic sources, and recombinant DNA technology. Plant sources, being the oldest, provide various medicinal properties through leaves, flowers, fruits, seeds, roots, ba
0 views • 11 slides
Understanding the Debate on Inexhaustible vs. Nonrenewable Energy Sources
The energy debate revolves around the classification of energy sources into nonrenewable, renewable, and inexhaustible categories. Fossil fuels, such as coal, petroleum, and natural gas, fall under nonrenewable sources due to their finite nature, while wind and tidal energy are examples of inexhaust
0 views • 18 slides
Understanding Information Literacy: A Comprehensive Guide for Students
Information literacy is crucial for academic success. It involves the ability to recognize the need for information, locate relevant sources, evaluate their credibility, and effectively use the information for research and presentations. Primary and secondary sources play a vital role in gathering i
0 views • 19 slides
Understanding Sources of Law in Legal Systems
Exploring the sources of law, this content delves into the concept of formal and material sources categorized by legal scholars. It examines how legal systems differ in recognizing sources such as precedents, legislation, customs, and treaties. The focus shifts to Indian law, highlighting the signif
1 views • 23 slides
Implementing Alert Messages and User Input Handling in Java
This tutorial guides you through creating alert messages, handling user input, defining functions, calling functions from the `onCreate` method, and creating an XML file for user data entry validation in Java. Learn how to display alerts for empty user credentials and process user actions accordingl
1 views • 6 slides
Understanding the Sources of Law: Definitions and Classification
The term "sources of law" refers to the origins from which rules of human conduct derive their legal force and binding character. This concept varies among writers and includes factors like Hindu scriptures, sovereign authority, historical documents, customs, and more. This article explores differen
0 views • 11 slides
Understanding Light Intensity Variation in Different Sources
Explore the correlation between light intensity and efficiency in various light sources through an intriguing experiment. Delve into the theoretical framework and practical applications to grasp the essence of light intensity and its distribution. Uncover the factors influencing the efficiency of li
0 views • 21 slides
Accelerator Technology R&D Targets and Sources Overview
The SnowMass2021 Accelerator Frontier AF7 focuses on Accelerator Technology R&D, exploring targets and sources such as high brightness electron sources, muon sources, and high intensity ion sources. The community planning meeting discussed various Letter of Interest submissions outlining innovative
0 views • 7 slides
Unsupervised Clickstream Clustering for User Behavior Analysis
Understanding user behavior in online services is crucial for businesses. This research focuses on utilizing clickstream data to identify natural clusters of user behavior and extract meaningful insights at scale. By analyzing detailed user logs, the study aims to reveal hidden patterns in user inte
0 views • 19 slides
Efficient User Management System for Health Facilities
Record and manage user details effectively with the new Version 2.0 User Management feature. RNTCP has now registered over 35,000 PHIs, 140,000 Private Health Facilities, 15,000 Private Labs, 31,000 Private Chemists, across 700 Districts and 8,000 TUs in Nikshay. Enhance operations by editing TU pro
0 views • 26 slides
Understanding the Sources for the History of Modern India
The sources for the history of modern India encompass literary sources such as printed books, government documents, newspapers, magazines, pamphlets, historical buildings, biographies, and memoirs. These sources provide insights into the political, social, economical, and cultural developments in In
0 views • 9 slides
Understanding Light: Sources and Properties
Light is a vital form of energy that enables vision and is emitted or reflected by various sources. Learn about natural sources like the sun, moon, fire, lightning, and luminous animals, as well as artificial sources powered by electricity. Discover how light waves travel, illuminating our world and
0 views • 18 slides
Development of Guidelines for Publishing Georeferenced Statistical Data Using Linked Open Data Technologies
Development of guidelines for publishing statistical data as linked open data, merging statistics and geospatial information, with a primary focus on preparing a background for LOD implementation in official statistics. The project aims to identify data sources, harmonize statistical units, transfor
1 views • 31 slides
Understanding Agile User Stories in Software Development
Agile user stories play a crucial role in software development by providing short descriptions of features desired by customers in a language they understand. This method allows for agile planning, efficient documentation, and effective communication between development teams and clients. Extracting
0 views • 30 slides
Enhancing User Experience Through Data Trails and Metrics
Andrea Thompson, a Sr. User Experience Manager at The Home Depot, highlights the importance of measuring and analyzing user experience metrics to understand and improve customer interactions. By investigating data trails from various touchpoints, such as customer sign-ups, interactions with associat
0 views • 17 slides
Understanding Reliable and Unreliable Sources for Research
Recognize reliable and unreliable sources for research. Reliable sources, such as books and peer-reviewed journals, are authored by experts in the field. Unreliable sources like Wikipedia and blogs can be altered by anyone. Learn how to evaluate the credibility of online sites based on their URLs an
0 views • 10 slides
Citing Sources in Research Papers: A Comprehensive Guide
Learn how to correctly cite sources in a research paper through parenthetical citations and creating a Works Cited page. Understand the importance of giving credit to sources to avoid plagiarism. The guide covers the use of quotations to strengthen your arguments, parenthetical citations from specif
0 views • 6 slides
Understanding Primary and Secondary Sources in Research
Primary sources provide firsthand information from the time period being studied, while secondary sources offer interpretations based on primary sources. Examples of primary sources include autobiographies, speeches, historical documents, published firsthand accounts, and sound recordings. Secondary
0 views • 23 slides
Visual Presentation on Federal State and Gateway User Sources
In this visual presentation, various slides showcase images related to federal states, security levels, and gateway user sources. The slides cover topics such as perspectives, federated identities, vision, design, and more. Each image provides a glimpse into different aspects of these subjects, offe
0 views • 31 slides
International Inventory of Musical Sources by RISM
Founded in Paris in 1952, the Répertoire International des Sources Musicales (RISM) comprehensively documents existing music sources worldwide. Recognized as the key entity for cataloging music sources globally, RISM's working groups in over 35 countries catalog manuscripts, printed music, writings
0 views • 17 slides
Disused Sources Working Group Report on National Security Perspective
The Disused Sources Working Group (DSWG) report focuses on managing and disposing of sealed sources to reduce national security risks. Formed in 2011, DSWG developed recommendations to enhance the management of disused sealed sources. The report categorizes sealed sources based on potential harm and
0 views • 15 slides
User Interface Design Principles in Human-Computer Interaction
User interface design principles are crucial in Human-Computer Interaction. This content highlights key principles such as aesthetics, anticipation, autonomy, and color consideration for users with color blindness. It emphasizes the importance of user testing, user autonomy, and providing essential
0 views • 24 slides
Understanding Indoor Air Pollution: Sources, Impacts, and Control Measures
This study explores the sources and influencing factors of indoor air pollution, highlighting the importance of studying indoor air quality due to its critical impact on human health. It discusses the various pollutant categories from different sources such as outdoor elements, indoor sources, furni
0 views • 17 slides
Understanding Archives and Primary Sources in Research
Explore the meaning of archives, examples of archival sources, the distinction between primary and secondary sources, and how researchers locate archival materials. Delve into the significance of primary sources in research and personal life.
0 views • 14 slides
Understanding the Importance of Sources in Psychology
Delve into the significance of differentiating between popular and scholarly sources in psychology to enhance research accuracy and reliability. Learn to discern between credible sources and the importance of referencing original sources for accurate information.
0 views • 18 slides
Understanding Energy: Sources, Generation, and Storage
Explore the fundamentals of energy sources, conversion methods, advantages, and disadvantages of non-renewable and renewable sources. Delve into topics such as coal, oil, gas, biomass, solar, wind, and more. Understand the National Grid, power systems, and considerations when selecting energy source
0 views • 6 slides
Understanding Sources of Light and Reflection
Exploring the concept of light sources and reflection, the article delves into how light is created by various objects like the sun, light bulbs, and fires. It explains the difference between sources of light and objects that reflect light, such as shiny metal surfaces. The reader is encouraged to i
0 views • 14 slides
Understanding Interaction Design in Human-Computer Interaction
Interaction design focuses on creating interactive products that are easy, effective, and enjoyable to use. It aims to reduce negative user experiences while enhancing positive ones. Designing interactive products requires understanding user activities, interfaces, and device arrangements to support
0 views • 11 slides
Vulnerability of Radiological Materials to Theft by Terrorist Groups in US Civilian Entities
The vulnerability of radiological materials stored at US civilian entities to theft by terrorist groups, particularly low-activity sources, remains a significant concern. Security measures primarily focus on high-activity sources, leaving lower activity sources neglected and highly susceptible to ex
0 views • 16 slides
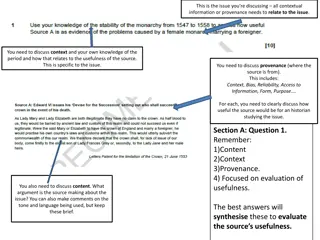
Evaluating Sources on Female Rule in the 1550s
This analysis focuses on assessing the reliability and usefulness of historical sources discussing the issue of female rule in the 1550s. It evaluates the content, provenance, and context of the sources to determine their relevance for historians studying the topic. The sources provide insights into
0 views • 8 slides
Activities, Sectors, and Control Technologies in GAINS Research
The GAINS research by Janusz Cofala and Zbigniew Klimont focuses on aggregation criteria for emission sources, macroeconomic parameters such as population and GDP, aggregation of energy-related sources, transport sources, and process sources. It also covers specific VOC processes/sources like solven
0 views • 13 slides
IEEE 802.11-20/1317r1 EHT-SIG Proposal Discussion
The document discusses EHT-SIG for single-user and sounding NDP in IEEE 802.11-20/1317r1, focusing on overflow bits, user fields, CRC, and tail formats. It covers the format details, subfields, and overhead compared to HE sounding, proposing specific bit allocations for different elements. The EHT-S
0 views • 16 slides
Raw Materials in Industrial Fermentation Processes
Microorganisms utilized in industrial fermentation require essential raw materials such as water, energy sources, carbon, nitrogen, mineral elements, and sometimes vitamins and oxygen. Various raw materials like cane molasses, beet molasses, cereal grains, starch, glucose, and lactose serve as carbo
0 views • 15 slides
Understanding Renewable Energy and its Benefits in 2022
Renewable energy sources like wind, waves, tides, sunlight, geothermal heat, and biomass play a crucial role in combating climate change by reducing greenhouse gas emissions. This task educates about the differences between renewable and non-renewable energy sources, the benefits of renewables, and
0 views • 10 slides
Understanding NUcore User and Account Management System
NUcore is a transaction processing system for core facilities at Northwestern University, comprising key components like Products, Payment Sources, and People roles. The system involves managing user accounts, payment sources, and different system roles such as Global Admins, Core Staff, and Purchas
0 views • 11 slides
Administrator Deletes User - User Management System Storyboard
An administrator navigates through a user list, selects a user for deletion, confirms the action, and successfully removes the user from the system. The process involves interacting with user details, confirming the deletion, and updating the user list accordingly in a structured manner.
0 views • 4 slides
User Interface vs User Experience: Understanding the Essentials
Exploring the distinctions between User Interface (UI) and User Experience (UX) in human-computer interaction design. UI focuses on the space of interaction between humans and machines, while UX encompasses users' behavior, attitude, and emotions towards a product or service. The goal is to create i
0 views • 63 slides