Rich snipptes
User intent, also known as search intent or query intent, refers to the underlying goal or purpose behind a user's search query when they use a search engine. It represents what the user is looking to accomplish or find when they enter a specific keyword or phrase into a search engine.
1 views • 8 slides
Maximizing Impact: The Role of Rich Snippets in SERPs"User Intent
User intent, also known as search intent, refers to the underlying goal or purpose a user has when performing an online search. It goes beyond the literal interpretation of keywords and focuses on understanding why a person is searching. Recognizing and catering to user intent is crucial for creatin
3 views • 10 slides
Operating Systems
An operating system is a crucial program that manages all other programs on a computer. It handles tasks like input recognition, file management, and device control. There are different types of operating systems such as single-user, single-task systems, multi-user, multi-task systems, real-time ope
6 views • 11 slides
Understanding King's College School Year Cycle & Intent to Register Process
Explore the school year cycle at King's College, including key events like Intent to Register, registering for Fall/Winter, final exams, and adjudication at the Academic Dean's Office. Learn the benefits of completing your Intent to Register and check program admission requirements. Ensure timely ad
0 views • 18 slides
Revolutionizing Network Management with Intent-Based Networking
Explore the concept and benefits of Intent-Based Networking (IBN) in simplifying network configuration and enhancing efficiency. Learn how IBN automates network operations, aligns with business objectives, improves security, and ensures scalability and reliability. Discover the potential of IBN tool
0 views • 14 slides
The Evolution of Graphical User Interfaces in Computing
Graphical User Interfaces (GUIs) have transformed computing into a more user-friendly and interactive experience, emphasizing the shift from technology-focused to human-centric living. This chapter delves into the various aspects of GUIs, including I/O alternatives, common GUI tasks, programming per
1 views • 32 slides
Understanding Linux User Capabilities and Namespace Management
Linux user namespaces and capabilities play a critical role in managing system security and permissions. Users and groups are assigned unique IDs, and processes are associated with the user's ID. The kernel enforces permission checks based on user IDs and group IDs, allowing root access to bypass ce
0 views • 14 slides
Understanding Criminal Law and Procedure: Greenvisor's Case
A case study involving embezzlement by Joe Greenvisor, the chief accountant of Nobreath Corporation, sheds light on criminal acts, duties, intent, and societal perspectives on crime. Despite Greenvisor's charitable intentions, his actions constituted a crime under the law. The elements of criminal a
0 views • 47 slides
Aids to Interpretation: Understanding the Purpose and Types
Interpretation of statutes involves uncovering legislative intent. Internal aids (such as titles and preambles) and external aids help judges apply statutes accurately. Key factors include short and long titles, preamble statements, and substance over form. Case examples illustrate how titles can sh
0 views • 68 slides
Implementing Alert Messages and User Input Handling in Java
This tutorial guides you through creating alert messages, handling user input, defining functions, calling functions from the `onCreate` method, and creating an XML file for user data entry validation in Java. Learn how to display alerts for empty user credentials and process user actions accordingl
1 views • 6 slides
Strategies for Managing Rural Water Supply and Sanitation Agency (RUWASA) Towards Its Highest Intent
RUWASA, established under the Water Supply and Sanitation Act, has core responsibilities in rural water supply and sanitation projects. Strategies for managing RUWASA focus on achieving its highest intent through functions like planning, construction supervision, and community support. The Director
0 views • 10 slides
Doctrine of Exhaustion of Administrative Remedies in Comparative Administrative Law
The doctrine of exhaustion of administrative remedies requires litigants to pursue all available remedies with administrative authorities before seeking judicial review. Originating from the case of Myers v. Bethlehem Shipbuilding Corp, this doctrine aims to respect congressional intent and promote
1 views • 12 slides
Enhancing Intent Classification with Chain of Thought Prompting
This study explores the use of Chain of Thought Prompting (CoT) for few-shot intent classification using large language models. The approach involves a series of reasoning steps to better understand user intent, leading to improved performance and explainable results compared to traditional promptin
0 views • 37 slides
Unsupervised Clickstream Clustering for User Behavior Analysis
Understanding user behavior in online services is crucial for businesses. This research focuses on utilizing clickstream data to identify natural clusters of user behavior and extract meaningful insights at scale. By analyzing detailed user logs, the study aims to reveal hidden patterns in user inte
0 views • 19 slides
Insights from Fifth ITU Workshop on Network 2030 in Geneva, Switzerland
Key takeaways and conclusions from the Fifth ITU Workshop on Network 2030 in Geneva, Switzerland included discussions on self-driving networks, new technologies, and intent-based networking. Topics such as evolving the management plane, incorporating ML5G work, and the importance of Intent-Based Net
3 views • 9 slides
Efficient User Management System for Health Facilities
Record and manage user details effectively with the new Version 2.0 User Management feature. RNTCP has now registered over 35,000 PHIs, 140,000 Private Health Facilities, 15,000 Private Labs, 31,000 Private Chemists, across 700 Districts and 8,000 TUs in Nikshay. Enhance operations by editing TU pro
0 views • 26 slides
Understanding Criminal Elements and Intentions in State Laws
The prosecution needs to prove all elements of a crime beyond a reasonable doubt, including Mens Rea (mental intent) and Actus Reus (criminal act). Each state has its laws defining specific crime elements, sentences, and degrees of seriousness. Examples include arson, assault with intent, and unlawf
0 views • 17 slides
Understanding Agile User Stories in Software Development
Agile user stories play a crucial role in software development by providing short descriptions of features desired by customers in a language they understand. This method allows for agile planning, efficient documentation, and effective communication between development teams and clients. Extracting
0 views • 30 slides
Enhancing User Experience Through Data Trails and Metrics
Andrea Thompson, a Sr. User Experience Manager at The Home Depot, highlights the importance of measuring and analyzing user experience metrics to understand and improve customer interactions. By investigating data trails from various touchpoints, such as customer sign-ups, interactions with associat
0 views • 17 slides
Comprehensive Overview of Concurrent Enrollment Program at RRCC
Explore the essentials of the Concurrent Enrollment Instructor Program at RRCC, covering topics such as program intent, benefits, class expectations, course alignment, HLC accreditation, and collaboration with RRCC liaisons. Learn about the collective intent of concurrent enrollment, differences in
0 views • 24 slides
Idaho Commission on Aging Town Hall Meetings and Services Overview
The Idaho Commission on Aging is hosting town hall meetings across the state to discuss senior services, funding allocation, legislative intent, and state plan requirements. These meetings aim to engage the public and stakeholders in shaping the future of senior care in Idaho. The four-year state pl
0 views • 47 slides
Understanding Re-Finding Behavior in Yahoo Search Logs
Explore a study on re-finding behavior in Yahoo search logs, focusing on quantifying user re-finding actions, known patterns, methodology, and challenges in inferring re-finding intent. The research sheds light on the commonality and stability of re-finding, emphasizing the significance of identifyi
0 views • 22 slides
Invitation to Apply for New Awards - Essential Dates and Process
An opportunity to apply for new awards through the Department of Health and Human Services for Independent Living Administration Centers. Essential dates to remember include a pre-application meeting on July 7, a notice of intent deadline on July 21, and the application transmittal deadline on Augus
0 views • 34 slides
The Role and Intent of Oil & Gas Recruitment Agencies in International Markets
The Role and Intent of Oil & Gas Recruitment Agencies in International Markets\" covers how agencies provide expert talent and flexible staffing solutions for global oil and gas companies, streamlining recruitment and reducing costs. For more informa
0 views • 4 slides
User Interface Design Principles in Human-Computer Interaction
User interface design principles are crucial in Human-Computer Interaction. This content highlights key principles such as aesthetics, anticipation, autonomy, and color consideration for users with color blindness. It emphasizes the importance of user testing, user autonomy, and providing essential
0 views • 24 slides
Anthony Burgess and the Tremor of Intent: Exploring Espionage and Fiction in the Sixties
Discover the intriguing world of Anthony Burgess as a novelist, his impact on the literary scene of the sixties, and his exploration of espionage in his works. Uncover the cultural context of the era, the growth of popular music, and the significance of Cold War tensions. Delve into Burgess's unique
0 views • 14 slides
Intelligent Mechanism Design for Intent-Based Network Resource Reconfiguration
An exploration of intent-based network resource reconfiguration through intelligent mechanism design, focusing on concepts such as intent setting, abstract views of intent networks, mechanism design, network traffic control examples, system optimization, and underlying optimization strategies. Vario
0 views • 11 slides
Understanding Interaction Design in Human-Computer Interaction
Interaction design focuses on creating interactive products that are easy, effective, and enjoyable to use. It aims to reduce negative user experiences while enhancing positive ones. Designing interactive products requires understanding user activities, interfaces, and device arrangements to support
0 views • 11 slides
Intent to Register for Courses at Western University - Important Information
Ensure you successfully complete your Intent to Register process for courses at Western University from March 1st to April 2nd. Follow steps outlined, review academic requirements, submit online forms by the deadline. Check eligibility, and register for courses via student portal. Learn how to use t
0 views • 31 slides
Admission Process Presentation for Joining upcell Alliance
This PowerPoint document outlines the admission steps for joining the upcell Alliance, focusing on understanding each applicant's core activities, motivations, and potential contributions. Applicants are required to express their intent by filling a letter of intent and presenting their activities i
0 views • 7 slides
Understanding the Objective Intent Test in Contract Law
This content explores the concept of the objective intent test in contract law through legal cases and non-legal examples. It discusses promises, misunderstandings in non-legal situations, and the legal rule surrounding interpreting words and actions as a promise. The analysis of whether a question
0 views • 31 slides
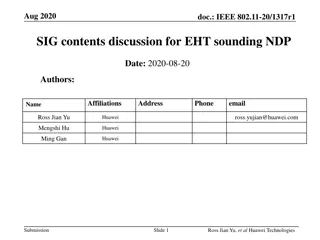
IEEE 802.11-20/1317r1 EHT-SIG Proposal Discussion
The document discusses EHT-SIG for single-user and sounding NDP in IEEE 802.11-20/1317r1, focusing on overflow bits, user fields, CRC, and tail formats. It covers the format details, subfields, and overhead compared to HE sounding, proposing specific bit allocations for different elements. The EHT-S
0 views • 16 slides
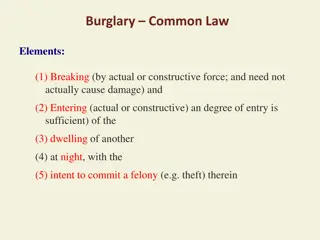
Understanding Burglary and Arson Laws: Common Law vs. Modern Rules
Burglary and arson laws have evolved from common law principles to modern statutes. In common law, burglary involves breaking and entering a dwelling at night with intent to commit a felony, while arson requires malicious burning of another's dwelling. Modern laws may vary, eliminating some elements
0 views • 6 slides
Mastering the Art of Writing a Compelling Letter of Intent
A detailed guide on crafting a persuasive Letter of Intent (LOI) for pharmacy residency applications, featuring insights on the what, why, and how of LOIs along with dos and don'ts. Learn the importance of LOIs, how to showcase your strengths effectively, and avoid common mistakes to make a lasting
0 views • 18 slides
Comprehensive Guide to Due Diligence Review and Letter of Intent
This comprehensive guide delves into the due diligence review process and the intricacies of crafting a letter of intent in the context of oil and gas property acquisitions. It covers the basic framework, goals, what is not covered, a roadmap of the presentation, available forms, the acquisition and
0 views • 42 slides
Administrator Deletes User - User Management System Storyboard
An administrator navigates through a user list, selects a user for deletion, confirms the action, and successfully removes the user from the system. The process involves interacting with user details, confirming the deletion, and updating the user list accordingly in a structured manner.
0 views • 4 slides
Understanding Seattle's Notice of Intent to Sell Ordinance
This informational content covers the amended requirements for the Notice of Intent to Sell (NOIS) ordinance in Seattle, focusing on property owners' obligations regarding affordable housing units. Learn about the background, key differences in the 2015 and 2019 ordinances, notification requirements
0 views • 11 slides
User Interface vs User Experience: Understanding the Essentials
Exploring the distinctions between User Interface (UI) and User Experience (UX) in human-computer interaction design. UI focuses on the space of interaction between humans and machines, while UX encompasses users' behavior, attitude, and emotions towards a product or service. The goal is to create i
0 views • 63 slides
Advanced SEO Techniques for 2025 How to Stay Ahead of the Competition (1)
Stay ahead in the competitive digital landscape with Advanced SEO Techniques for 2025. Focus on user intent, AI-driven strategies, mobile optimization, and enhanced on-page practices to boost rankings and improve user engagement. Learn how to leverag
0 views • 11 slides
Understanding Context Switching and User-Kernel Interaction in Operating Systems
Context switching in operating systems involves a seamless transition between user-level threads without the kernel's awareness. User-level code manages register state and stack pointers, while user-kernel mode switching requires changing processor privilege levels and agreement on information excha
0 views • 25 slides